On Nov. 23, one of the cybercrime underground’s largest bazaars for buying and selling stolen payment card data announced the immediate availability of some four million freshly-hacked debit and credit cards. KrebsOnSecurity has learned this latest batch of cards was siphoned from four different compromised restaurant chains that are most prevalent across the midwest and eastern United States.
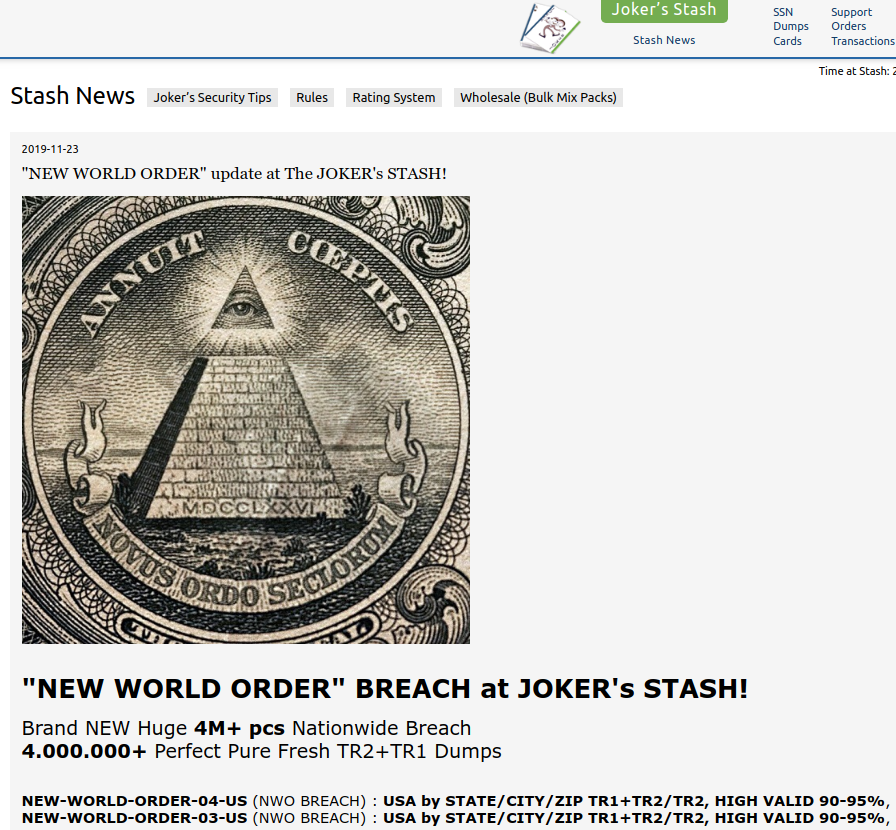
An advertisement on the cybercrime store Joker’s Stash for a new batch of ~4 million credit/debit cards stolen from four different restaurant chains across the midwest and eastern United States.
Two financial industry sources who track payment card fraud and asked to remain anonymous for this story said the four million cards were taken in breaches recently disclosed by restaurant chains Krystal, Moe’s, McAlister’s Deli and Schlotzsky’s. Krystal announced a card breach last month. The other three restaurants are all part of the same parent company and disclosed breaches in August 2019.
KrebsOnSecurity heard the same conclusion from Gemini Advisory, a New York-based fraud intelligence company.
“Gemini found that the four breached restaurants, ranked from most to least affected, were Krystal, Moe’s, McAlister’s and Schlotzsky’s,” Gemini wrote in an analysis of the New World Order batch shared with this author. “Of the 1,750+ locations belonging to these restaurants, nearly 50% were breached and had customer payment card data exposed. These breached locations were concentrated in the central and eastern United States, with the highest exposure in Florida, Georgia, South Carolina, North Carolina, and Alabama.”
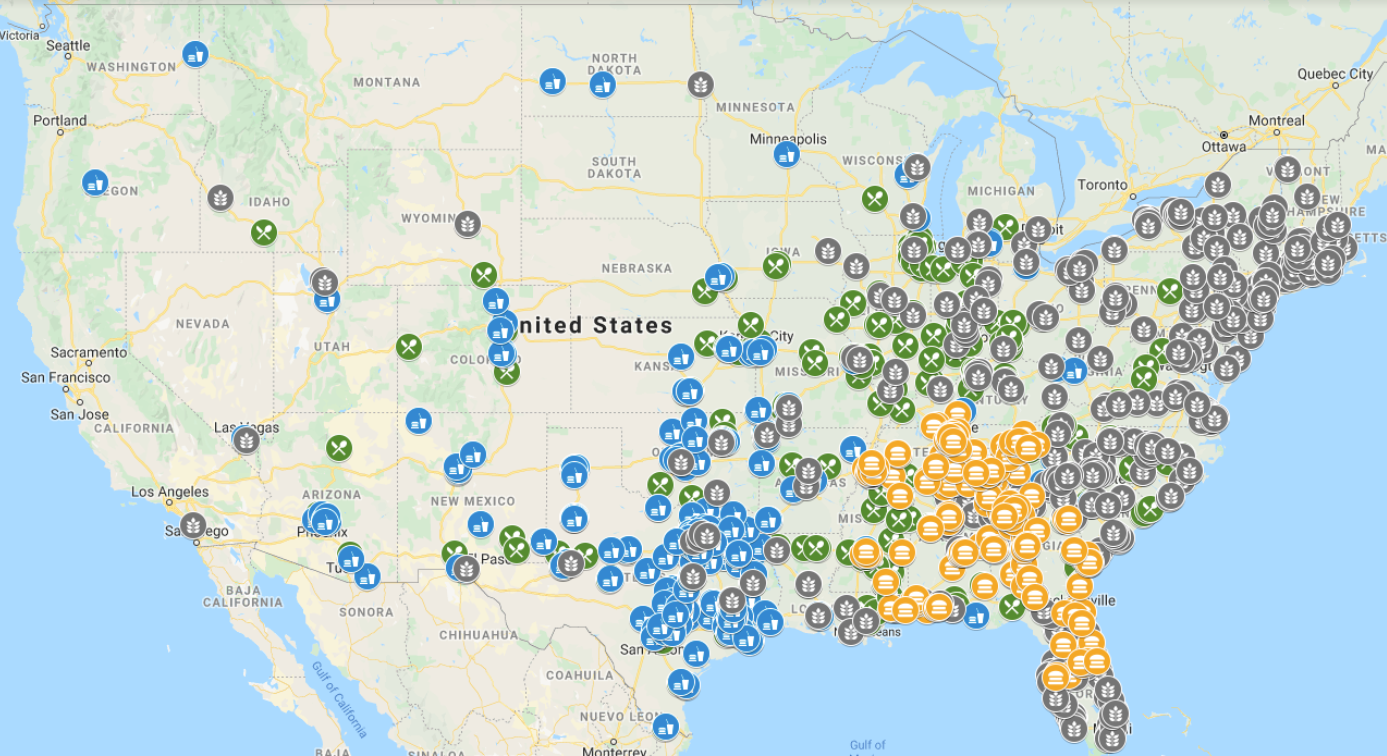
McAlister’s (green), Schlotzsky’s (blue), Moe’s (gray), and Krystal (orange) locations across the United States. There is an additional Moe’s location in Hawaii that is not depicted. Image: Gemini Advisory.
Focus Brands (which owns Moe’s, McAlister’s, and Schlotzsky’s) was breached between April and July 2019, and publicly disclosed this on August 23. Krystal claims to have been breached between July and September 2019, and disclosed this in late October.
The stolen cards went up for sale at the infamous Joker’s Stash carding bazaar. The most recent big breach marketed on Joker’s Stash was dubbed “Solar Energy,” and included more than five million cards stolen from restaurants, fuel pumps and drive-through coffee shops operated by Hy-Vee, a supermarket chain based in Iowa.
According to Gemini, Joker’s Stash likely delayed the debut of the New World Order cards to keep from flooding the market with too much stolen card data all at once, which can have the effect of lowering prices for stolen cards across the board.
“Joker’s Stash first announced their breach on November 11, 2019 and published the data on November 22,” Gemini found. “This delay between breaches occurring as early as July and data being offered in the dark web in November appears to be an effort to avoid oversaturating the dark web market with an excess of stolen payment records.”
Most card breaches at restaurants and other brick-and-mortar stores occur when cybercriminals manage to remotely install malicious software on the retailer’s card-processing systems, often by compromising third-party firms that help manage these systems. This type of point-of-sale malware is capable of copying data stored on a credit or debit card’s magnetic stripe when those cards are swiped at compromised payment terminals, and that data can then be used to create counterfeit copies of the cards.
The United States is embarrassingly the last of the G20 nations to make the shift to more secure chip-based cards, which are far more expensive and difficult for criminals to counterfeit. Unfortunately, many merchants have not yet shifted to using chip-based card readers and still swipe their customers’ cards.
According to stats released in September by Visa, 80 percent of U.S. storefronts now accept chip cards. Visa says for merchants who have completed the chip upgrade, counterfeit fraud dollars dropped 87 percent in March 2019 compared to September 2015. This may help explain why card thieves increasingly are shifting their attention to compromising e-commerce merchants, a trend seen in virtually every country that has already made the transition to chip-based cards.
Companies that accept, store, process and transmit credit and debit card payments are required to implement so-called Payment Card Industry (PCI) security standards, but not all entities are required to prove that they have met them. While the PCI standards are widely considered a baseline for merchants that accept payment cards, many security experts advise companies to put in place protections that go well beyond these standards.
Even so, the 2019 Payment Security Report from Verizon indicates the number of companies that maintain full compliance with PCI standards decreased for the second year in a row to just 36.7 percent worldwide.
As noted in previous stories here, the organized cyberthieves involved in stealing card data from main street merchants have gradually moved down the food chain from big box retailers like Target and Home Depot to smaller but far more plentiful and probably less secure merchants (either by choice or because the larger stores became a harder target).
It’s really not worth worrying about where your card number may have been breached, since it’s almost always impossible to say for sure and because it’s common for the same card to be breached at multiple establishments during the same time period.
Just remember that while consumers are not liable for fraudulent charges, it may still fall to you the consumer to spot and report any suspicious charges. So keep a close eye on your statements, and consider signing up for text message notifications of new charges if your card issuer offers this service. Most of these services also can be set to alert you if you’re about to miss an upcoming payment, so they can also be handy for avoiding late fees and other costly charges.




Even if consumers are not liable for fraudulent charges, they may well, as a whole, end up paying for the financial institutions’ losses from these breaches as the FIs spread their cost of doing business among their customer base. But exactly how much these breaches are costing you and me, it is impossible to tell.
As we calculate the cost, consider that we’ve been paying between 1.5% and 3.5% for every credit card transaction our entire lifetimes. That’s a baseline — or right off the top, depending on your perspective.
To be more specific, MERCHANTS taking credit cards have been paying between approx. 1.5% and 3.5% for every credit card transaction.
To be more clear, merchants charge their customers a price for their products and services that covers credit card swipe/dip fees, even if those customers aren’t using a credit card.
To be more complete, not every merchant can afford to do this, especially small businesses for whom 1.5-3.5% can be the difference between buying a product from them or going to Amazon.
Just to be through, this makes it clear that using cash at stores and is safer, even if it is less efficient. Credit Card use should be saved for online transations, as they are slightly more defended.
It is not clear at all that cash is safer.
Safer from online fraud, yeah, but much more dangerous for getting mugged.
You get mugged, you don’t get cash back under any circumstances, unless the police find the mugger which they usually don’t. And even if they do, good luck with the legal process to recoup the cash.
It is much safer not to carry too much cash on your person. This is common wisdom.
Of course many will say, carry a bit, and just use the ATM when needed. But you should see how that again, opens up another can of worms. Or carry only enough for a day or two… and keep the rest in your house. Then we need to open that can of worms about home burglary.
Bottom line, do what you can. But anywhere you keep your money, will be a target. Whether in a wallet, home, bank, etc… criminals will intently follow the money.
yes, but the cost of accepting cash is still greater…
Not sure on that one. All depends upon the average transaction for the merchant.
The consumer is paying for all losses and expenses of the merchant.
This is nothing new. And taking checks is even worse for the merchant. Absolutely no chargeback rights on that form of payment. With fraudulent activity, if the merchant did things right – then the bank picks up the tab for fraud.
Am so glad i live in the UK. Even though we’re not immune to Card fraud, its much harder here with chip and pin for transactions under £30. Still possible on pos terminals in restaurants and the like, but much so less than the States where you run the risk of massive debt problems even if its not your fault as the banking system there puts the responsibilities mostly on the consumer and give very little redress rights to the consumer. In the UK, as soon as your spot the fraudulent transactions the bank here will be on your side, cos.. well, legally mandated that they have to be 🙂
So much for land of the free eh?
MFA only protects you when the transaction is being processed. Most retail establishments in the USA now have EMV chip readers. Your credit card number temporarily sits on server that is managed by the restaurant chain. You better hope its encrypted. Oh, and when you hand your credit card to the waiter and he is out of sight do you think he/she is not copying down your info? Go back to cash
Not true as a whole! Had my identity stolen twice and the credit card company took care of it both times! I now have a chip in my cards which makes the information harder to steal! I always pay down my debt instead of paying interest so I don’t know if they increased my interest or not!
And to be extra safe you use lots of exclamation marks!
Don’t know what you’re on about; the Fair Credit Billing Act does the same thing for Americans. I myself have been fraudulently hit twice, and had no problems getting the charges reversed.
Sounds more like you’re trying to peddle a myth than accurately comment on the matter.
I’m sorry…..with all due respect, however; how can you make such a blatant comment without having direct knowledge on how the banking system operates in the U.S? All the large banks ARE on the consumers’ side. I’ve had my accounts compromised at 3 a.m. and Chase customer service has contacted me within minutes to inform me of fraudulent activity. They immediately reimburse me my money. I’ve had my accounts (3 different banks) compromised 3 times in the last 10 years and believe me my banks have always been on my side….The CONSUMER! You, my friend, have been misinformed.
Now that’s what I call the land of the free, Eh
You are incorrect about how credit card fraud is handled in the US. IF the consumer handles the reporting properly, the risk is 100% on the vendor or the card provider depending on where the transaction was when cancelled. In most cases, absolutely zero payments come out of the consumer’s account. Debit Cards on the other hand, are another matter where your PIN and that card are tied to an active account and you can be on the hook for whatever your daily limit is. I would never use a debit card for anything outside of an ATM transaction for cash.
US has the chip and PIN and if you dispute within 60 days you get your money back, the merchant gets a charge back.
I wish you would do your research as you are completely wrong on all counts.
1. Consumers have 60 DAYS past their last statement to notify the bank of any unauthorized transactions.
2. The bank picks up the fraud losses – not the consumer.
3. All of this is specified in Regulation E.
Yes, we are the land of the free.
Cheers,
yes…the U.K is a wonderful place where people are polite and create problems (brexit) where none need exist; while reminding you how lucky they are….an anagram for tawt
The issue is specific to fast food restaurants and automated gas dispensers in the USA who still utilize magnetic card readers. Pretty much everyone else has shifted to EMV readers by now.
The 3.5% surcharged added to every CC transaction goes to covering this fraud expense, doesn’t it? In other countries, with Chip-n-pin, if the correct pin is entered, then the customer (individual) eats the loss.
Or am I wrong?
The 3.5% first goes to PROFIT. A small percentage goes to cover losses.
Banks are losing money too on a lot of transactions. The interchange is less than the expenses to process the transaction. Only banks that get 3-5% are American Express and Discover. All the rest of the banks earn << <<3%.
Sorry, you are wrong. Even with a pin transaction, the bank is going to eat the fraud.
From securityweek (dot) com on November 25, 2019
Church’s Chicken Restaurants Hit by Payment Card Breach
“At least 160 Church’s Chicken restaurants across 11 U.S. states are impacted by a data breach that involved unauthorized access to payment processing systems.
Cajun Operating Company, which owns and operates Church’s Chicken, revealed last week that it had become aware of unauthorized access to payment processing systems in late October.
Atlanta-based Church’s Chicken is a quick service restaurant chain that has over 1,500 locations across 23 countries. There are nearly 1,000 locations across 29 states in the U.S., but a majority are franchised rather than company-operated.
The company claims the recent data breach has only impacted the restaurants it operates itself — no franchised locations appears to have been hit — and customers who made orders through delivery apps such as Uber Eats and DoorDash are not affected.
Church’s Chicken has launched an investigation into the incident and it has so far determined that the payment processing systems used by roughly 160 of its restaurants are impacted. However, tens of new locations have been added in the past few days so the number might increase until the investigation is completed.
Affected restaurants are located across 11 states, including Alabama, Arkansas, Florida, Georgia, Illinois, Louisiana, Mississippi, Missouri, South Carolina, Tennessee and Texas.”
It seems like the fraud, shake-downs and stealing gets worse by the day. It makes me wonder if the olden days of phone calls (not email, messaging, etc.) typewriters and white-out, US mail, copying machines (not scanners), and using physical money had some major advantages that we didn’t appreciate until our current problems became reality. Technological advances also lead to more complex problems perhaps.
It might explain why the rate of crimes on persons, has slowly gone down in the last decade. It doesn’t pay to physically rob someone personally with a hold up, when you can do it electronically with so little risk to the criminal.
Of course there are always the desperate drug addicts that don’t have such skills – so the old fashion hold up still happens, too often.
Technological advances also offer protections that weren’t available back in the day. For example, physical cash: If I’m robbed of that, I’m screwed unless the police catch the robber. If I’m robbed of a card, I just cancel it. If charges are made on that card without my approval, I dispute them and get them removed. I’m not aware of any card issuer in the US that doesn’t have a zero liability vs fraud policy in place.
Cash is literally riskier. If it’s stolen, it’s gone. Not the case with credit cards.
I totally agree.
Cash counterfeiting was a huge problem back then. Yes, a lot of credit goes to watermarking, holograms, foil, etc… but some credit should be given to how there are fewer cash only businesses which are easy targets for counterfeiters to spend.
Back when everyone paid cash, a lot of businesses would have to take extra time to inspect large bills. Criminals don’t waste time on forging small bills. Now, cash payments are rare, so large bills can be inspected and scrutinized.
Also, check fraud was a HUGE problem. Now, not nearly as much.
The move away from cash and check has made it easier for a new digital criminal, but has also made the old paper and ink criminal all but obsolete.
Actually criminals do forge small bills, more often than large bills these days. The last time there was reports of phoney money being passed off at stores around here, it was fake 10’s. Much easier to pass than 100’s since most places still check large bills, they dont even blink when its a 10.
That’s precisely my point. That criminals are being forced to work harder for less payout.
Fewer and fewer businesses are dealing primarily in cash, and that gives tellers a higher chance of suspicion when they do get handed cash.
It isn’t as much of a problem as it used to be, with large transactions. Before, high quality bills were forged and released in bulk… now, its more like students with ink jet printers buying pizza.
It may “seem” like it is worse, since it may be more bills with more transactions… but the dollar amount is less.
Naw, fast food restaurants just need to get with the program and start using EMVs instead of magnetic readers. Because their own individual transactions involve pretty small amounts they are willing to take the chargeback risk. However, their actions are a weak link in the overall chain and they need to correct them.
How about the State of California’s CalFresh debit cards? No chip there yet!
(And don’t ask about their IT security/customer help with those issues on their lottery site…)
For a state that has so many people, it never hired enough civil service/social sevices employees so they could say “Look at the surplus!”
Politics as usual.
California hires plenty of people in the government, more than any other state. The problem is they implement almost exclusive diversity hiring. So rather than hiring the most qualified candidate, they’re required to go out and find an Intuit American or something and hire them regardless of the qualifications.
Sounds racist.
It doesn’t sound like you understand diversity programs, but instead are just making the same stereotypical argument against affirmative action that has been debunked decades ago. It is based on a fake narrative propagated by conservative radio.
California is, by far, the most populous state. So of course they have more government employees. If you take 6 red states equaling the population of California, they would have more government employees.
California’s EBT SNAP food benefits cards dont have chips however, they do require a pin number that is set by the owner. This however can be changed by phone with the SSN. That would be really messed up to steal from people who are really struggling. And all they could buy with the data is….food
The cards are sold for cash at a lower value, so figure selling them for fifty cents on the dollar.
Is the merchant not liable for the charges? I thought when the chip system went in that the bank would be liable for fraud against the chip and merchant would be liable for fraud where the magnetic stripe was used. This was to encourage chip adoption. Is this not the case?
We have two Visa cards with chip . Both cards were cloned and used at fake locations (Was is a former business, the other does not exist) about two hours away from anywhere we have ever used our cards at the same time we used our cards. We were told that the cards could not be hacked or duplicated due to the chip. I was finally able to prove that the cards had been in fact duplicated (chip and all). Its just so frustrating!
They didn’t clone the chip. They cloned the magnetic stripe. All US-issued chip cards still have the stupid stripe, which stores the data in plain text. And as long as that’s the case and there are still merchants that force you to swipe, this problem will continue.
And BTW that’s unlikely to change anytime soon: Most US ATMs still require the stripe because it’s an integral part of the way the the card acceptance slot on the machines work. Without the stripe, most of these machines can’t grab the card when you insert it into an ATM.
When chips fail to read in the machine (damaged chip) the machine will ask you to swipe the card (the stripe) If both would fail you would have to manually key in the numbers which results in a even higher fee to process for the merchant accepting the card.
You should do an article on ACH fraud and maybe the recent Macy’s breach.
Most ATMs now accept the chips. Banks are learning quickly that they get to eat the loss if a card which is chip enabled gets used at their ATM which is not chip enabled.
Losses goto the holder of least security. We saw this at a friendly bank which did not have their atms chip enabled. That got changed in a heartbeat.
Their ATM was drained in a weekend as the bad guys literally sat the entire night at the atm pulling cash from multiple cards.
The key is that the merchant is only liable for fraudulent transactions made at THEIR OWN establishment, not for all the transactions made at other establishments by cards who were stolen through their systems.
Therefore, fast food restaurants like the ones mentioned by the breach are not in a hurry to upgrade to EMV as their own losses from these breaches are actually pretty small. It’s other merchants (usually non-POS ones where a physical card is not presented) which suffer due to the restaurants’ carelessness.
Mr jocker stash is well known provider.
I Think Mr jocker stash is number one seller.
But I really think carding is over!
Time for crypto, bye bye carding
Doing some spam today are we?
crypto, lay off the meth little guy
Just 2 words to the wise:
Apple Pay
Android Pay
Never be bothered by an inconvenient card replacement again.
Unfortunately, neither of those can be used everywhere a card can be used. For example, at a local BBQ restaurant last night, they brought the chip-enabled card reader to the table but the restaurant doesn’t accept NFC-based payments, so I had to use my card.
BTW, my local McAllister’s still swipes cards after the breach.
Apple Pay and Android Pay are good choices. They do not process with the real account # but a token instead. Significantly less fraud with those methods.
Adding another layer of abstraction can prevent this kind of fraud. But does add a new middleman that is potentially compromised.
You have your money in a bank, which works with a credit card provider like VISA, MC, etc… and they now work with 3rd parties like Google, Apple, Paypal, etc…
So it is good that there is another layer of security… but there is also another layer of risk.
So it may move from physical card skimmers, to more virtual card skimmers (javascript on hijacked sites), and more demand for account takeovers of Apple and Google.
“That’s where the money is!” is the primary target. It makes no sense to risk showing up in person to rob a bank or even mug a person in the street, if access to the money flows through so many providers.
Cyber crimes are lethal to the point of people feeling without any hope, outcast ( depending on the unlawfully seizures magnitude via bank cyber linking) & eventually death & sickness through worry & stress..Its not just stupid cr cards. its grand LARCENY, UNLAWFUL HOME ESTATE SEIZURE, CBBER TRAFFICKING CYBER THIS CYBER THAT. SOurce them & end them. Is that clear enough??
After the target hack, which I read about in detail through Krebs, I thought to myself. This won’t happen again!
I was working at Wells Fargo as a Phone banker all the time so I got daily reminders of the hack as customers would call in. But, it just…keeps…happening.
At what point, are companies going to take the securities of their customer’s private network information seriously? When are we going to hold them accountable?
They are being held accountable. Any merchant/ATM which takes a chip enabled card for a mag swipe is responsible for the fraudulent transactions.
Bank of America just sent me a new credit card saying that it might have been compromised. I didn’t eat at any of the restaurants though. So you have to figure your card number is never secure.
Also, for some reason I read the comments in the voice of Robin Leach. Quite entertaining.
Same here.
It all started with a notice of a fraudulent transaction that properly tagged. Glad they did that and allowed me to dispute the transaction.
Thanks for the article, @Brian!
I KNOW FOR SURE BRIAN KREBS IS WORKING WITH THIS JOKER AND ALL OTHER CYBER CRIMINALS TO STEAL OUR CREDIT CARD DATA HOW DOES BRIAN KREBS MAKE HIS MONEY DOING THIS JOURNALISM I THINK THIS IS SUBLIMINAL ADVERTISING FOR HIS SITES I FOUND ONE SITE NAMED AFTER HIM WITH HIS PICTURE HE OWNS THOSE DARKNET SITES
Yes, you figured me out. I’m simultaneously trying to expose these turkeys and at the same time run a few decent card shops. Thanks for the laugh.
Let’s not forget those CP, Drugs and Weapons sites you also run that you don’t tell us about, Brian, while we’re at it… [ROTFL emoticon]
Interesting. Good write-up. Disparage cash? Come on, what do you tip with? Pay the Uber with? Or use during a power outage? Keep some cash available.
I tell you what they do with it , they go to some desolate giftshop , where noone goes , by some high end stuff , using these cards and then resell them at much lower prices , try googling for carded products and you will know about the big market which thrives and lives right now , you could get an iPhone for as little as 100dollars and an Xbox for even less . Now you decide.
This is the reason I get charge alerts via my phone on all my cards. BTW, since Kansas is the center of the US, according to the map shown there were not that many hacks in the ACTUAL mid-west. Just sayin
Dinner in Palm Desert at a popular Mexican restaurant led to subsequent charges made in Kansas City.
Watch your bank statements for several months if dining out in the Palm Springs area
Look at the map of activity in California. It is no joke.
Palm Springs (Palm Desert, Rancho Mirage) is a hot bed of this activity. Check the map. Watch you bank statements for this activity for some time after dining out there. A charge will show up somewhere across the country several weeks later.
I monitor card data and fraud across the US and Canada. There is far less fraud to Canadian consumers. Their debit system, Interac, seems very secure. And they are used to using PIN and chip. In the US we are behind many other countries in securing credit card data and those costs are passed on one way or another. We are still swiping all over the place, especially at gas stations which are not even required to update the technology to chip for another year.
Virtually every developed nation’s banking system is ahead of the US. Canada had a huge head start on debit cards as well. And, most of Europe hasn’t seen a check in 50 years, yet, the US still writes them…
The US economy is also significantly larger than all of those you reference.
I lived in mainland China from 2001 to 2006. All banks there issued chip cards.
When I came back to the USA in 2007, cards in my state were still mag strip; no chips. It wasn’t until about 2015 they started issuing them.
Pretty sad when a Communist country more than 15 years back was issuing them, yet in the USA, it took forever.
But although transparency is a necessity for the whole company, its presence is even more important at the top where strategies are planned and decisions are made.
Is tap to pay more safe? is apple pay more safe?
Safer, for now. Different type of criminal, and requires more sophistication. But criminals adapt.
Adding another layer of abstraction can prevent this kind of carder fraud. But it does add a new middleman that is potentially compromised.
You have your money in a bank, which works with a credit card provider like VISA, MC, etc… and they now work with 3rd parties like Google, Apple, Paypal, etc… then there is the security of your mobile phone…
So it is good that there is another layer of security… but there is also another layer of risk.
So it may move from physical card skimmers, to more virtual card skimmers (javascript on hijacked sites), and more demand for account takeovers of Apple and Google. And any malware running on your phone.
“That’s where the money is!” is the primary target. It makes no sense to risk showing up in person to rob a bank or even mug a person in the street, if access to the money flows through so many providers.
If by ‘tap to pay’ you mean tapping the card (ie. contactless scheme like payWave) then yes that’s as safe as it gets.
Tapping the card isn’t safer than inserting into a Chip and PIN reader.
Wireless is very convenient, but opens up a new attack.
There is an app for Android called Credit Card Reader, and it can quickly and easily, get the card data for cloning… just by tapping.
Criminals can bump you in a crowded area, and possibly get your card data through your wallet.
This is a non-threat. So tired of companies pitching various products to protect against this as if it were a real concern. There is a dynamic CVV added to every contactless transaction, and this dynamic CVV is only good for that one transaction, and I believe it also has time limits on how soon it has to be used. I.e., this attack does not scale and it has severe practical limitations. There are much easier ways to steal credit card details that do scale (like skimming ATMs, skimming ecommerce sites, and gas pumps).
It is not a huge threat, true.
*misspoke: not for cloning but rather risk of bumping and making an immediate/one-time transaction.
Limits on scale may be important for those looking at the big picture (i.e. reporters).
But victims don’t care if they are the rare occurrence.
Yes, there are easier ways to steal credit card data. But we have to also think about the future. When the most prevalent method of skimming becomes untenable, due to requiring Chip and PIN / depreciating mag stripe…. then criminals will focus on the next thing, Tap and Pay cards.
There is also a non-security privacy risk. Some cards keep a transaction history that is available when tapped. Not sure vendors should have access to that.
Also, the products you allude to, such as RF blocking wallets, also protect the multitude of static RFID/MiFare/NFC cards that many people have to carry around. Easily clonable (no crypto challenge/response done on card) static information is still in use and very common. Tourists are targeted for their hotel room keys all the time.
Whether Chip & PIN or magnetic stripe card readers are used when processing payment cards is more or less irrelevant for security. The key issue is whether end-to-end encryption technology is used.
In end-to-end encrypting solutions, the POS system and payment terminal are separated. The Merchant’s systems never see cardholder data and even if hacked, it will not result in a cardholder data breach. The payment terminal is a dedicated payment security device, provided by a company dedicated to payment security. The Merchant has no access to the encryption keys or to any configuration of the payment terminal. I have yet to hear of a single cardholder data breach with a proper end-to-end encrypting solution.
99% of the breaches we read about in the news have one common denominator – a Merchant processing cardholder data in their own systems. Bottom line is that a Merchant or any organisation whose core business is NOT payment security, will never be able to keep up the level of security required to protect cardholder data.
My local Tijuana Flats (Moe’s competitor) has had EMV POS terminals installed at each register for about a year now (with Do Not Use stickers on them) but only recently activated them. After these breaches I’m guessing they got warnings from their card processors that they better get them activated or their processing fees would go up.