Change Healthcare says it has notified approximately 100 million Americans that their personal, financial and healthcare records may have been stolen in a February 2024 ransomware attack that caused the largest ever known data breach of protected health information.
Image: Tamer Tuncay, Shutterstock.com.
A ransomware attack at Change Healthcare in the third week of February quickly spawned disruptions across the U.S. healthcare system that reverberated for months, thanks to the company’s central role in processing payments and prescriptions on behalf of thousands of organizations.
In April, Change estimated the breach would affect a “substantial proportion of people in America.” On Oct 22, the healthcare giant notified the U.S. Department of Health and Human Resources (HHS) that “approximately 100 million notices have been sent regarding this breach.”
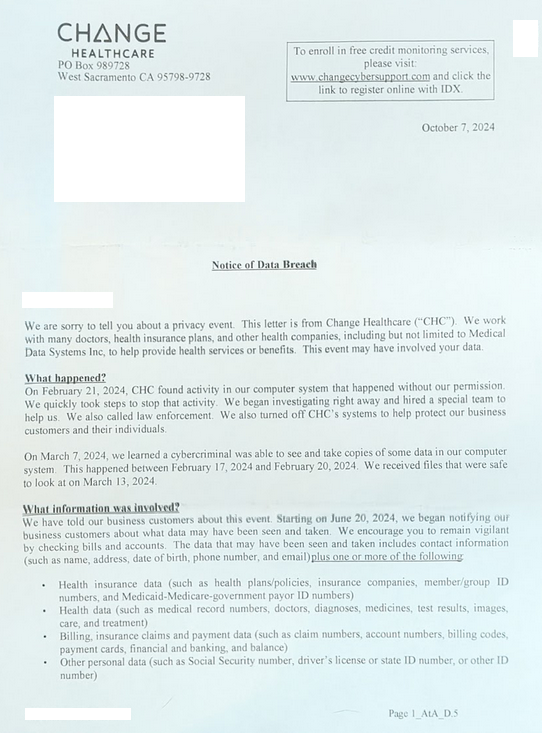
A notification letter from Change Healthcare said the breach involved the theft of:
-Health Data: Medical record #s, doctors, diagnoses, medicines, test results, images, care and treatment;
-Billing Records: Records including payment cards, financial and banking records;
-Personal Data: Social Security number; driver’s license or state ID number;
-Insurance Data: Health plans/policies, insurance companies, member/group ID numbers, and Medicaid-Medicare-government payor ID numbers.
The HIPAA Journal reports that in the nine months ending on September 30, 2024, Change’s parent firm United Health Group had incurred $1.521 billion in direct breach response costs, and $2.457 billion in total cyberattack impacts.
Those costs include $22 million the company admitted to paying their extortionists — a ransomware group known as BlackCat and ALPHV — in exchange for a promise to destroy the stolen healthcare data.
That ransom payment went sideways when the affiliate who gave BlackCat access to Change’s network said the crime gang had cheated them out of their share of the ransom. The entire BlackCat ransomware operation shut down after that, absconding with all of the money still owed to affiliates who were hired to install their ransomware.
A few days after BlackCat imploded, the same stolen healthcare data was offered for sale by a competing ransomware affiliate group called RansomHub.
“Affected insurance providers can contact us to prevent leaking of their own data and [remove it] from the sale,” RansomHub’s victim shaming blog announced on April 16. “Change Health and United Health processing of sensitive data for all of these companies is just something unbelievable. For most US individuals out there doubting us, we probably have your personal data.”
It remains unclear if RansomHub ever sold the stolen healthcare data. The chief information security officer for a large academic healthcare system affected by the breach told KrebsOnSecurity they participated in a call with the FBI and were told a third party partner managed to recover at least four terabytes of data that was exfiltrated from Change by the cybercriminal group. The FBI declined to comment.
Change Healthcare’s breach notification letter offers recipients two years of credit monitoring and identity theft protection services from a company called IDX. In the section of the missive titled “Why did this happen?,” Change shared only that “a cybercriminal accessed our computer system without our permission.”
But in June 2024 testimony to the Senate Finance Committee, it emerged that the intruders had stolen or purchased credentials for a Citrix portal used for remote access, and that no multi-factor authentication was required for that account.
Last month, Sens. Mark Warner (D-Va.) and Ron Wyden (D-Ore.) introduced a bill that would require HHS to develop and enforce a set of tough minimum cybersecurity standards for healthcare providers, health plans, clearinghouses and businesses associates. The measure also would remove the existing cap on fines under the Health Insurance Portability and Accountability Act, which severely limits the financial penalties HHS can issue against providers.
According to the HIPAA Journal, the biggest penalty imposed to date for a HIPAA violation was the paltry $16 million fine against the insurer Anthem Inc., which suffered a data breach in 2015 affecting 78.8 million individuals. Anthem reported revenues of around $80 billion in 2015.

A post about the Change breach from RansomHub on April 8, 2024. Image: Darkbeast, ke-la.com.
There is little that victims of this breach can do about the compromise of their healthcare records. However, because the data exposed includes more than enough information for identity thieves to do their thing, it would be prudent to place a security freeze on your credit file and on that of your family members if you haven’t already.
The best mechanism for preventing identity thieves from creating new accounts in your name is to freeze your credit file with Equifax, Experian, and TransUnion. This process is now free for all Americans, and simply blocks potential creditors from viewing your credit file. Parents and guardians can now also freeze the credit files for their children or dependents.
Since very few creditors are willing to grant new lines of credit without being able to determine how risky it is to do so, freezing your credit file with the Big Three is a great way to stymie all sorts of ID theft shenanigans. Having a freeze in place does nothing to prevent you from using existing lines of credit you may already have, such as credit cards, mortgage and bank accounts. When and if you ever do need to allow access to your credit file — such as when applying for a loan or new credit card — you will need to lift or temporarily thaw the freeze in advance with one or more of the bureaus.
All three bureaus allow users to place a freeze electronically after creating an account, but all of them try to steer consumers away from enacting a freeze. Instead, the bureaus are hoping consumers will opt for their confusingly named “credit lock” services, which accomplish the same result but allow the bureaus to continue selling access to your file to select partners.
If you haven’t done so in a while, now would be an excellent time to review your credit file for any mischief or errors. By law, everyone is entitled to one free credit report every 12 months from each of the three credit reporting agencies. But the Federal Trade Commission notes that the big three bureaus have permanently extended a program enacted in 2020 that lets you check your credit report at each of the agencies once a week for free.




Wasn’t this caused by an employee using their personal account on a work computer, thus syncing their data across devices and their personal device was compromised?
Or was that another breach that happened this year?
I would say the bigger risk here is not credit fraud but extortion/blackmail using threat of public disclosure of personal medical history/records. I’m sure that is extremely sensitive information for a lot of people and something not many would want to have exposed to friends/family/coworkers.
Agree, and think of the chilling effect this could have on people’s willingness to seek therapy, counseling,etc. due to the perfectly reasonable fear that the medical system can’t keep their records safe.
I received a letter for each member of my family. I didn’t know until this article that United Health Care was the company behind the leak. I had no idea who Change Healthcare was.
Thanks Brian for this update.
Sadly, the most that will happen is a slap on the wrist.
If you go to https://www.annualcreditreport.com/index.action, it says this:
—
Free weekly online credit reports are available from Equifax, Experian and TransUnion. Credit reports play an important role in your financial life and we encourage you to regularly check your credit history.
—
Is that actually true? Free WEEKLY credit reports?
Yes, as the article above says, that is actually true:
https://consumer.ftc.gov/consumer-alerts/2023/10/you-now-have-permanent-access-free-weekly-credit-reports
Credit Karma offers free Real Time credit reporting. NFCU offers free Real Time FICO scores.
What does NFCU refer to?
There are actually four reporting credit agency’s. Innovis is the 4th and few realize this.
Actually, Brain knows this. It must be an oversight.
10 yrs of federal prison are needed for the entire BoD and C-Suite people who allowed this to be possible. Probably 50+ people need to be tried and put into jail. Otherwise “industry standard security practices” will continue, which is clearly NOT SUFFICIENT.
The thought of appropriate legal recourse, and following through on any type of punishment for actions of large corporations doing damage and death to victims is not ever forthcoming. Just give PG&E headquarters a call, they’re still laughing about killing thousands of people due to their negligence and disregard for human life. They even made their customers pay the fines due to excessive rate increases, so there is no such thing as big corps paying any kind of penalty.
its so maddening sometimes…
Yep, here are regular criminals and regular heroes, then there are super criminals,, and no superheroes.
Better yet, maybe BlackCat, ALPHV and RansomHub need a visit from Delta Force or Seal Team 6 or the entire 82nd Airborne Division to announce new rules for ransomware attacks.
Hear, hear! The sooner the better!
I got a letter from them that my info was part of the breech – and I have no idea how I’m part of their network!
A little transparency as to how providers are related would be really nice.
Brian – I suggest you add a link to your ‘Why & Where You Should Plant Your Flag’ posting every time you post about a data breach such as this one. https://krebsonsecurity.com/2020/08/why-where-you-should-you-plant-your-flag/
I worked as a general IT guy for a behavioral health/addiction clinic. I started as a consultant but finally moved to part-time on call worker so I could be protected by their liability insurance rather than having to cover myself. Plus I was worried if there was a breach I would be inside the corporate wall rather than outside.
I had big problems with vendors. The first EMR company we had, I broke down and yelled at them for the first time in my career. I saw a note asking the receptionist to gather up everyone’s password so the vendor could update their client software. When I told them that was a violation of basic network security nevermind HIPAA regulations, they said “well it’s just easier that way”. I told my boss and I finally decided to quit when I realized the clinic needed that software more than they needed me. I wasn’t around enough to keep tabs on them and I didn’t want to deal with any fallout from their shoddy security practices. Other vendors were either asking to install software on our network or open ports in the firewall so they could remotely access their devices.
That was a small practice without even a full time IT person, these big companies that can afford good cybersecurity teams and equipment have no excuse.
One thing that shocks me is how many people claim to be security conscious, but do not encrypt their e-mail whenever and wherever available. Also, they never digitally sign their e-mail.
Other than my own e-mails between computers, in the past thirty years, the only times I have ever received digitally signed e-mail was on a certain, now-defunct anti-spam list and the only time I have ever received encrypted e-mails were more out of testing than anything else.
For my own e-mail, my various servers send certain logs to my ProtonMail account. Often, but not right now, I encrypt the e-mails with the logs.
Until I see people encrypting and digitally signing their e-mail, I’m not going to take their claims seriously of them being above average in their security consciousness.
The most interesting part, at least to me, was about an affiliate providing them access and then getting stiffed on their “share” of the payout. In other words, they are promising to pay employees or affiliates for giving them their access to the network? That would likely make it really tough to defend against.
I wonder if a hardware key might help against such methods. If the attacker had to have a physical access device to get in, the crooked affiliate should be limited unless he was wiling to give up his access permanently.
I am shocked that you’re missing the elephants in the room. HIPAA and PCI regulations require this data to be encrypted for just this reason. Was it or was it not? I’ve been trying to find out for weeks and this company refuses to respond. And frankly you’re making this out to mainly be the problem for the consumer not the incredible dereliction of duty by this vendor. Do you have the slightest idea the level of effort to even partially protect yourself against this disaster? And all they are offering is minor compensation? Why not urge a class action lawsuit, calling your congress critters, or anything else to hold these people responsible? Or are you afraid to drop some uncomfortable truths on these malefactors?
There’s a very simple reason why your congressional representatives doesn’t give one wit about your opinion on this. You simply don’t make big enough, “Bribes” to him,or her,for you to matter.
The data might be encrypted (at rest). Or encrypted within the database. It doesn’t matter. If a bad actor gets at an account that has access to the data (think admin), then they can leverage tools to use that account to get access to all the data. The data will be unencrypted in order to present it to the account.
Brian Krebs “afraid to drop some uncomfortable truths on these malefactors?” You’re joking right?
In general, the targets of these attackers end up getting compromised so thoroughly in most cases that the bad guys can touch, delete etc data backups, and other security mechanisms. Also, if I own your machine with malware, and you have the ability to decrypt data or view it unencrypted, guess what? So do I.
So, was the sensitive data encrypted or just stored in plain text?
I am genuinely curious.
The people selling the data posted numerous documents and screenshots they stole. So if it was encrypted, it doesn’t appear to have been when it was stolen.
Knowing a little about UHG (former employee), this is no surprise. UHG upper management has some real scumbags, to bad they won’t be the ones to suffer even the slightest bit. Pay the ransom to support other criminals due to their shorting IT budget because a few thousand bucks might hurt their millions of dollars in bonuses after fleecing their own customers. Health insurance is a very lucrative skimming operation, skimming between you and your health care and the main reason health care is more expensive than it should be. bah, nothing anyone can do about it.
I invested in a fake cryptocurrency scheme and lost thousands. I was fearful of being scammed again, but HACKXTECHN’s credibility and trustworthiness shone through. They ( @hackxtechn@gmailcom ) met my expectations and provided excellent service. Don’t trust everything you see online
These types of “recovery experts” appear on Reddit, all of which are scammers themselves. Get fooled once, shame on them. Get fooled twice?
Aubrielle, what happened to Briana?
My business was targeted by ransomware attackers. We had to pay to get our data back. I was hesitant to hire a hacker, but my experience with @hackxtechnwas exceptional. They ( @hackxtechn@gmailcom )exceeded my expectations and recovered my lost data quickly. Protect your systems, people!
These types of “recovery experts” appear on Reddit, all of which are scammers themselves. Get fooled once, shame on them. Get fooled twice?
Get a clue please. Nobody is falling for your BS.
A few months ago when ‘hackxtechn’ spam started appearing I found warnings of their activity on some anti scammer forums. The only physical location I could find for them was an anonymous mailbox service on Friedrichstraße, Berlin, Germany. They now have a Github account that is 3 weeks old with no activity and they also have a nicely polished listing on sortlist[.]com that advertises their services with plenty of 5 star reviews. Guess what their new address is? A suite at 350 5th Ave New York, NY 10118. That is the Empire State Building! ROFLMAO! I think we can all safley assume it is crock of sh*te and to avoid them like the plague.
Also a reverse image search of the face of ‘hackx-techn’ posted here;
https://www.sortlist.com/agency/hackx-techn#
is also the face of a customer testamonial of hormone replacement therapy clinic supposedly based out Harlingen, Texas, here;
https://harlingen.hgha.space/
Be aware however, both sites are considered safe by VirusTotal.com but the second site does contain trackers from yandex.ru. Why would a Texan HRT clinic have connections to Russia?
Good question.
It seems to me that perhaps we are not prepared to host all of this information on computers. This is yet another breach of trust with OUR information. With people’s information, real world people that exist. For too long there have been no real consequences to losing other people’s data.
What if these people were to stop allowing their info to be stored electronically. It appears that is the only way to protect ones information. Even then, I realize things can be stolen, but you can’t steal it from hundreds or thousands of miles away from the comfort of your own living room.
We are obviously losing the cat and mouse game of Good guy protecting info and Bad guy trying to steal information. Is society actually better off having all of their information stored electronically? Or is there a better way?
Nobody has commented on: “Change Healthcare’s breach notification letter offers recipients two years of credit monitoring and identity theft protection services from a company called IDX.”
Wasn’t this company also breached? I get the credit freeze, but having a legitimate company watch your back (possibly IDX???) is also a good idea. Just like having a security guard is good, but having a security guard with a dog is better.
IDX is a total joke. I tried to sign up for the “free monitoring” I got due to the Change Healthcare fiasco. The signup bombed out with “general error…contact support”. It has been like that for months now. No response from support email, and the voice line support staff can do nothing but tell me to email support. Trustpilot rates them as LOW, and the Better Business Bureau does too. There is not real help here, and Change chose the cheapest (i.e. useless) route to cover their ass.
Your experience with IDX mirrors mine. I at least got an account, which can’t seem to monitor my credit report. Support is non-responsive. I guess they know they are just a checkbox company and the people who’s credit they are supposed to be monitoring won’t renew anyway, so why bother with any sort of service.
(Admittedly, I do have my credit reports frozen, so that could interfere with IDX being able to monitor them, but they should at least warn me about that.)
United needs to be broken up into 5 separate companies. They pay the fines then continue on.
United needs to be broken up into 5+ separate companies. They pay the fines then continue on.
Could the government make it illegal to pay cyber ransoms (a felony charge against the decision-makers)? If this could be enforced, it would shut down the motive for stealing the data.
In MY OPINION, at this point, it behooves EVERYONE to just put a freeze on their report with all three. Even if one’s data wasn’t leaked in this particular breach, there’s been so many big breaches of so many companies I think it’s a REEEEEAAAALLLLY slim chance that your name/ssn/etc. is not already out there anyway.
I’m really curious—was the sensitive data encrypted, or was it just saved in plain text?
Be aware! https://paymydoctors[.]online/ is a potentially malicious website. See VirusTotal analysis below;
https://www.virustotal.com/gui/url/939544078e2572af3ece6727e6588548ba0830a6e6a66482bdc874a04a9e38ac/detection
Yes, luck us, people are increasingly concerned about tech companies collecting health data through devices like smartwatches. Privacy and data security are major worries in the digital age.
They should be shut down and out of Business. Sued royally.
I received a Change Heathecare letter stating what happened on February 21, 2024, and the activity CHC found in their computer system. Im not sure if I am to trust contacting IDX or not. Beacause over the past years I have been a victim of identity theft, data breaches, financial and business ccounts open, EIN # being applied for that I had no idea of, stealing my gmail accounts, taking over my IP address, networks, and devices, etc….You name it. Still ongoing and I can’t seem to get any answers having a hard time to trust anyone that I talk to because my calls, text and whatever else has been getting monitered by the hackers. Please Help Me.
> Im not sure if I am to trust contacting IDX or not.
I have first-hand experience with IDX. It’s less a trust issue and more a “don’t waste your time issue”. Look further up in the comments. They are useless. The free account with Experian I made to freeze my credit report gives me better monitoring and info than my IDX account does.