Tag Archives: TransUnion
Experian, You Have Some Explaining to Do
Twice in the past month KrebsOnSecurity has heard from readers who’ve had their accounts at big-three credit bureau Experian hacked and updated with a new email address that wasn’t theirs. In both cases the readers used password managers to select strong, unique passwords for their Experian accounts. Research suggests identity thieves were able to hijack the accounts simply by signing up for new accounts at Experian using the victim’s personal information and a different email address.
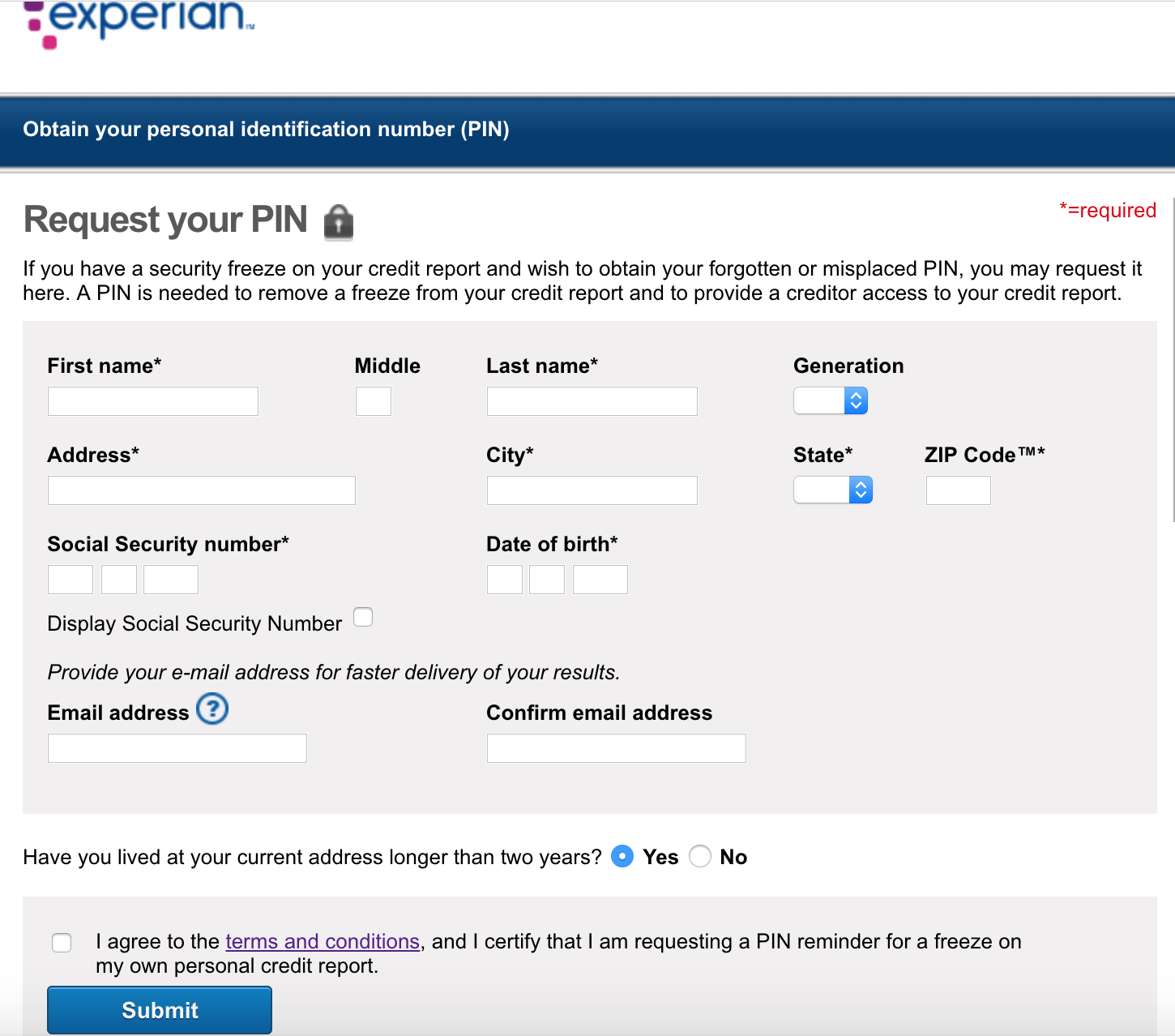
Experian’s Credit Freeze Security is Still a Joke
In 2017, KrebsOnSecurity showed how easy it is for identity thieves to undo a consumer’s request to freeze their credit file at Experian, one of the big three consumer credit bureaus in the United States. Last week, KrebsOnSecurity heard from a reader who had his freeze thawed without authorization through Experian’s website, and it reminded me of how truly broken authentication and security remains in the credit bureau space.
Equifax Has Chosen Experian. Wait, What?
A year after offering free credit monitoring to all Americans on account of its massive data breach that exposed the personal information of nearly 148 million people, Equifax now says it has chosen to extend the offer by turning to a credit monitoring service offered by a top competitor — Experian. And to do that, it will soon be sharing with Experian contact information that affected consumers gave to Equifax in order to sign up for the service.
Credit Freezes are Free: Let the Ice Age Begin
It is now free in every U.S. state to freeze and unfreeze your credit file and that of your dependents, a process that blocks identity thieves and others from looking at private details in your consumer credit history. If you’ve been holding out because you’re not particularly worried about ID theft, here’s another reason to reconsider: The credit bureaus profit from selling copies of your file to others, so freezing your file also lets you deny these dinosaurs a valuable revenue stream.
In a Few Days, Credit Freezes Will Be Fee-Free
Later this month, all of the three major consumer credit bureaus will be required to offer free credit freezes to all Americans and their dependents. Maybe you’ve been holding off freezing your credit file because your home state currently charges a fee for placing or thawing a credit freeze, or because you believe it’s just not worth the hassle. If that accurately describes your views on the matter, this post may well change your mind.
Checked Your Credit Since the Equifax Hack?
A recent consumer survey suggests that half of all Americans still haven’t checked their credit report since the Equifax breach last year exposed the Social Security numbers, dates of birth, addresses and other personal information on nearly 150 million people. If you’re in that fifty percent, please make an effort to remedy that soon.
Credit reports from the three major bureaus — Equifax, Experian and Trans Union — can be obtained online for free at annualcreditreport.com — the only Web site mandated by Congress to serve each American a free credit report every year.
Equifax Breach: Setting the Record Straight
Bloomberg published a story this week citing three unnamed sources who told the publication that Equifax experienced a breach earlier this year which predated the intrusion that the big-three credit bureau announced on Sept. 7. To be clear, this earlier breach at Equifax is not a new finding and has been a matter of public record for months. Furthermore, it was first reported on this Web site in May 2017.
Are Credit Monitoring Services Worth It?
In the wake of one data breach after another, millions of Americans each year are offered credit monitoring services that promise to shield them from identity thieves. Although these services can help true victims step out from beneath the shadow of ID theft, the sad truth is that most services offer little in the way of real preventative protection against the fastest-growing crime in America.
Credit Reports Sold for Cheap in the Underweb
Following the online publication of Social Security numbers and other sensitive data on high-profile Americans, the three major credit reporting bureaus say they’ve uncovered cases where hackers gained access to users’ information, Bloomberg reports. The disclosure, while probably discomforting for many, offers but a glimpse of the sensitive data available to denizens of the cybercrime underworld, which hosts several storefronts that sell cheap, illegal access to consumer credit reports.