Multiple stories published here over the past few weeks have examined the disruptive power of hacked “Internet of Things” (IoT) devices such as routers, IP cameras and digital video recorders. This post looks at how crooks are using hacked IoT devices as proxies to hide their true location online as they engage in a variety of other types of cybercriminal activity — from frequenting underground forums to credit card and tax refund fraud.
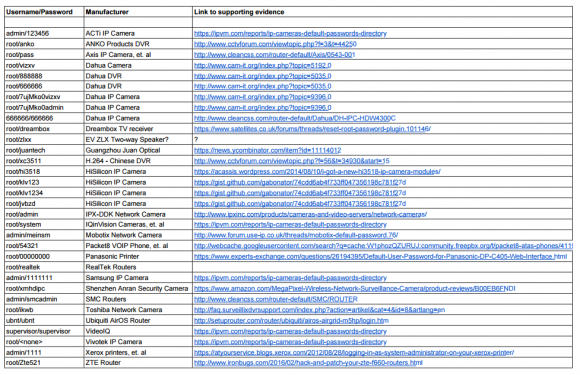
 Recently, I heard from a cybersecurity researcher who’d created a virtual “honeypot” environment designed to simulate hackable IoT devices. The source, who asked to remain anonymous, said his honeypot soon began seeing traffic destined for Asus and Linksys routers running default credentials. When he examined what that traffic was designed to do, he found his honeypot systems were being told to download a piece of malware from a destination on the Web.
Recently, I heard from a cybersecurity researcher who’d created a virtual “honeypot” environment designed to simulate hackable IoT devices. The source, who asked to remain anonymous, said his honeypot soon began seeing traffic destined for Asus and Linksys routers running default credentials. When he examined what that traffic was designed to do, he found his honeypot systems were being told to download a piece of malware from a destination on the Web.
My source grabbed a copy of the malware, analyzed it, and discovered it had two basic functions: To announce to a set of Internet addresses hard-coded in the malware a registration “I’m here” beacon; and to listen for incoming commands, such as scanning for new vulnerable hosts or running additional malware. He then wrote a script to simulate the hourly “I’m here” beacons, interpret any “download” commands, and then execute the download and “run” commands.
The researcher found that the malware being pushed to his honeypot system was designed to turn his faux infected router into a “SOCKS proxy server,” essentially a host designed to route traffic between a client and a server. Most often, SOCKS proxies are used to anonymize communications because they can help obfuscate the true origin of the client that is using the SOCKS server.
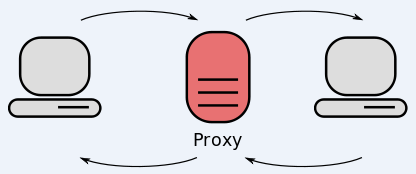
When he realized how his system was being used, my source fired up several more virtual honeypots, and repeated the process. Employing a custom tool that allows the user to intercept (a.k.a. “man-in-the-middle”) encrypted SSL traffic, the researcher was able to collect the underlying encrypted data passing through his SOCKS servers and decrypt it.
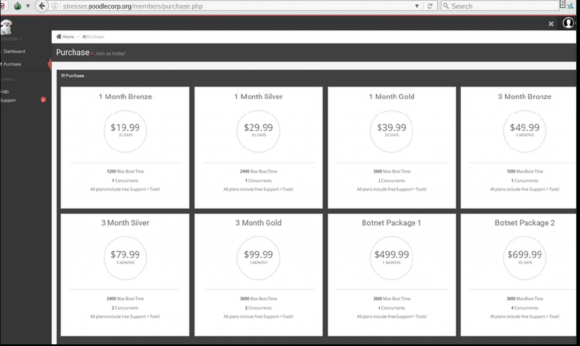
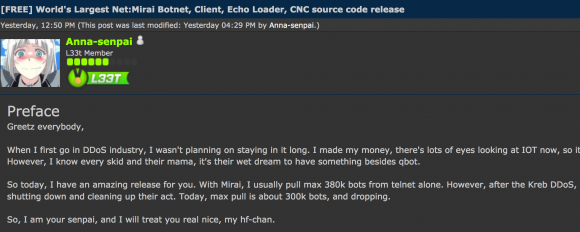
What he observed was that all of the systems were being used for a variety of badness, from proxying Web traffic destined for cybercrime forums to testing stolen credit cards at merchant Web sites. Further study of the malware files and the traffic beacons emanating from the honeypot systems indicated his honeypots were being marketed on a Web-based criminal service that sells access to SOCKS proxies in exchange for Bitcoin.
Unfortunately, this type of criminal proxying is hardly new. Crooks have been using hacked PCs to proxy their traffic for eons. KrebsOnSecurity has featured numerous stories about cybercrime services that sell access to hacked computers as a means of helping thieves anonymize their nefarious activities online. Continue reading


 Zero-day vulnerabilities describe flaws that even the makers of the targeted software don’t know about before they start seeing the flaws exploited in the wild, meaning the vendor has “zero days” to fix the bugs.
Zero-day vulnerabilities describe flaws that even the makers of the targeted software don’t know about before they start seeing the flaws exploited in the wild, meaning the vendor has “zero days” to fix the bugs. According to
According to