The process of buying or selling a home can be extremely stressful and complex, but imagine the stress that would boil up if — at settlement — your money was wired to scammers in another country instead of to the settlement firm or escrow company. Here’s the story about a phishing email that cost a couple their home and left them scrambling for months to recover hundreds of thousands in cash that went missing.
It was late November 2016, and Jon and Dorothy Little were all set to close on a $200,000 home in Hendersonville, North Carolina. Just prior to the closing date on Dec. 2 their realtor sent an email to the Little’s and to the law firm handling the closing, asking the settlement firm for instructions on wiring the money to an escrow account.
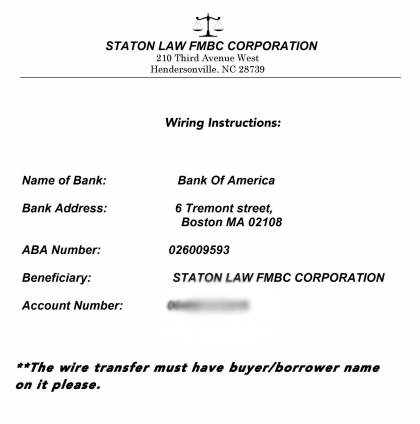
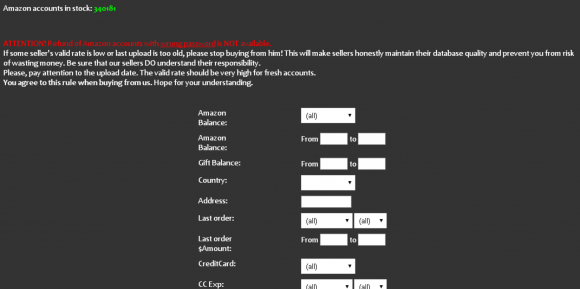
The fraudulent wire instructions apparently sent by the hackers via the settlement law firm.
An attorney with the closing firm responded with wiring instructions as requested, attaching a document that had the law firm’s logo and some bank account information that was represented as the seller’s account number. The Little’s realtor sent the wire on Thursday morning, the day before settlement.
“We went to closing at 1 p.m. on Friday, and after we signed all the papers, we asked the lawyers if we were going to get back the extra money we had sent them, because they hadn’t be able to give us an exact amount in the wiring instructions. At that point they told us they had never gotten the money.”
After some disagreement, both legitimate parties to the transaction agreed that someone’s email had been hacked by the fraudsters, and was used to divert the wired funds to an account the criminals controlled. The hackers had forged a copy of the law firm’s letterhead, and beneath it placed their own Bank of America account information (see screen shot above).
The owner of the Bank of America account appears to have been a willing or unwitting accomplice — also know as a “money mule” — recruited through work-at-home job schemes to receive and forward funds stolen from hacked business accounts. In this case, the money mule wired all but 10 percent of the money (a typical money mule commission) to an account at TD Bank.
Fortunately for the Littles, the FBI succeeded in having the resulting $180,000 wire transfer frozen once it hit the TD Bank account. However, efforts to recover the stolen funds were stymied immediately when the Littles’ credit union refused to give Bank of America a so-called “hold harmless” agreement that the bigger bank wanted as a legal guarantee before agreeing to help.
Charisse Castagnoli, an adjunct professor of law at the John Marshall Law School, said banks have a fiduciary duty to their customers to honor their requests in good faith, and as such they tend to be very nervous legally about colluding with another bank to reverse payment instructions by one of their own customers. The “hold harmless” agreement is usually sought by the bank which received a fraudulent wire transfer, Castagnoli said, and it requires the responding bank to assume any and all liability for costs that the requesting bank may later incur should the owner of account which received the fraudulent wire decide to dispute the payment reversal.
“When it comes to wire fraud cases the banks have to move very quickly because once the wires make it outside the U.S. to foreign banks, the money is usually as good as gone,” Castagnoli said. “The receiver or transferee usually insists on a hold harmless agreement because they’re moving the money on behalf of their own account holder, kind of going against their own client which is a big ‘no-no’ when you’re a fiduciary.”
But in this case, the credit union in which the Littles had invested virtually all of their money for more than 40 years decided it could not in good faith provide that hold harmless agreement, because doing so would stipulate that the credit union affirms the victim (the Littles) hadn’t willingly and knowing initiated the wire, when in fact they had.
“I talked to the wire dept multiple times,” Mr. Little said of the folks at his financial institution, Atlanta, Ga.-based Delta Community Credit Union (DCCU). “They finally put me through to the vice president of loss prevention at the credit union. I’m not sure they even believed all that was going on. They finally came back and told me they couldn’t do it. Their rules would not allow them to send a hold harmless letter because I had asked them to do something and they had done it. They had a big meeting last week with apparently the CEO of the credit union and several other people. Then they called me on Monday again and told me they would not could not do it.” Continue reading




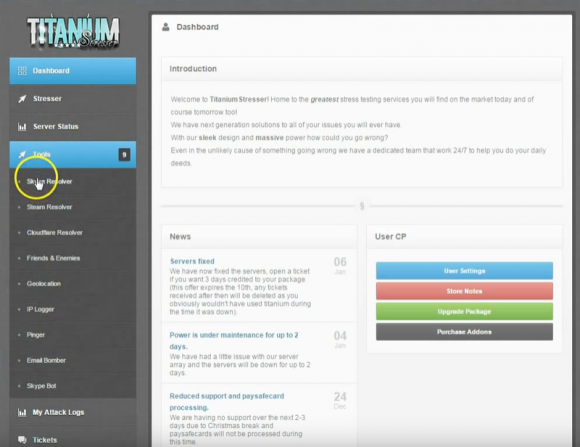

 Your average spam email can contain a great deal of information about the systems used to blast junk email. If you’re lucky, it may even offer insight into the organization that owns the networked resources (computers, mobile devices) which have been hacked for use in sending or relaying junk messages.
Your average spam email can contain a great deal of information about the systems used to blast junk email. If you’re lucky, it may even offer insight into the organization that owns the networked resources (computers, mobile devices) which have been hacked for use in sending or relaying junk messages.

 The biggest change this month for Windows users and specifically for people responsible for maintaining lots of Windows machines is that Microsoft has replaced individual security bulletins for patches with a single “
The biggest change this month for Windows users and specifically for people responsible for maintaining lots of Windows machines is that Microsoft has replaced individual security bulletins for patches with a single “