This week, nationwide beauty products chain Sally Beauty disclosed that, for the second time in a year, it was investigating reports that hackers had broken into its networks and stolen customer credit card data. That investigation is ongoing, but I recently had an opportunity to interview a former Sally Beauty IT technician who provided a first-hand look at how the first breach in 2014 went down.
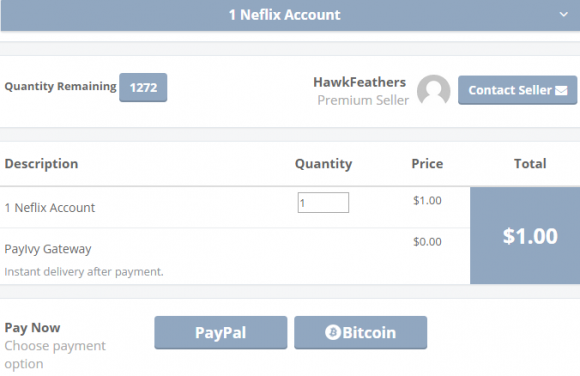
 On March 14, 2014, KrebsOnSecurity broke the news that some 260,000 credit cards stolen from Sally Beauty stores had gone up for sale on Rescator[dot]cc, the same shop that first debuted cards stolen in the Home Depot and Target breaches. The company said thieves made off with just 25,000 customer cards. But the shop selling the cards listed each by the ZIP code of the Sally Beauty store from which the card data had been stolen, exactly like this same shop did with Home Depot and Target. An exhaustive analysis of the ZIP codes represented in the cards for sale on the fraud shop indicated that the hackers had hit virtually all 2,600 Sally Beauty locations nationwide.
On March 14, 2014, KrebsOnSecurity broke the news that some 260,000 credit cards stolen from Sally Beauty stores had gone up for sale on Rescator[dot]cc, the same shop that first debuted cards stolen in the Home Depot and Target breaches. The company said thieves made off with just 25,000 customer cards. But the shop selling the cards listed each by the ZIP code of the Sally Beauty store from which the card data had been stolen, exactly like this same shop did with Home Depot and Target. An exhaustive analysis of the ZIP codes represented in the cards for sale on the fraud shop indicated that the hackers had hit virtually all 2,600 Sally Beauty locations nationwide.
The company never disclosed additional details about the breach itself or how it happened. But earlier this week I spoke with Blake Curlovic, until recently an application support analyst at Sally Beauty who was among the first to respond when virtual alarm bells starting going off last year about a possible intrusion. Curlovic said that at the time, Sally Beauty was running exactly one enterprise solution for security — Tripwire (full disclosure: Tripwire is an advertiser on this blog). Tripwire’s core product monitors key operating system and application files for any changes, which then triggers alerts.
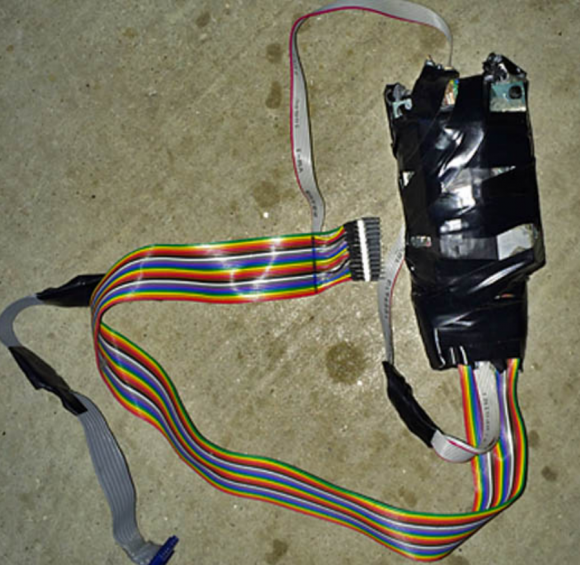
Tripwire fired a warning when the intruders planted a new file on point-of-sale systems within Sally Beauty’s vast network of cash registers. The file was a program designed to steal card numbers as they were being swiped through the registers, and the attackers had named their malware after a legitimate program running on all Sally Beauty registers. They also used a utility called Timestomp to change the date and time stamp on their malware to match the legitimate file, but that apparently didn’t fool Tripwire.
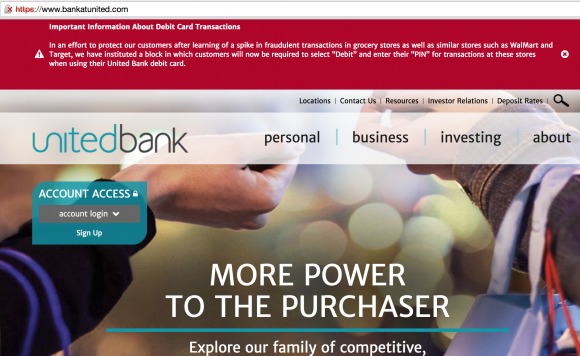
According to Curlovic, the intruders gained access through a Citrix remote access portal set up for use by employees who needed access to company systems while on the road.
“The attackers somehow had login credentials of a district manager,” Curlovic said. “This guy was not exactly security savvy. When we got his laptop back in, we saw that it had his username and password taped to the front of it.”
Once inside the Sally Beauty corporate network, the attackers scanned and mapped out the entire thing, located all shared drives and scoured those for Visual Basic (VB) scripts. Network administrators in charge of managing thousands or tens of thousands of systems often will write VB scripts to automate certain tasks across all of those systems, and very often those scripts will contain usernames and passwords that can be quite useful to attackers.
Curlovic said the intruders located a VB script on Sally Beauty’s network that contained the username and password of a network administrator at the company.
“That allowed them to basically copy files to the cash registers,” he said. “They used a simple batch file loop, put in all the [cash] register Internet addresses they found while scanning the network, looped through there and copied [the malware] to all of the point-of-sale devices — roughly 6,000 of them. They were in the network for like a week prior to that planning the attack.”