Lance Ealy, an Ohio man who fled home confinement last year just prior to his conviction on charges of filing phony tax refund requests on more than 150 Americans, was apprehended in a pre-dawn raid by federal marshals in Atlanta on Wednesday.
Ealy, 28, of Dayton, Ohio, was the subject of no fewer than three previous posts on this blog. Ealy reached out to me in February 2014, after being arrested by the U.S. Secret Service for using his email account to purchase Social Security numbers and other personal information from an online identity theft service run by a guy named Hieu Minh Ngo.
Ngo is a Vietnamese national who, for several years, ran an online identity theft service called Superget.info. Shortly after my 2011 initial story about his service, Ngo tauntingly renamed his site to findget.me. The Secret Service took him up on that challenge, and succeeded in luring him out of Vietnam into Guam, where he was arrested and brought to New Hampshire for trial. He pleaded guilty last year to running the ID theft service, and the government has been working on rounding up his customers ever since.
Mr. Ealy was one of several individuals found guilty of identity theft charges after buying from Ngo’s service, which relied in part on data obtained through a company owned by big-three credit bureau Experian.
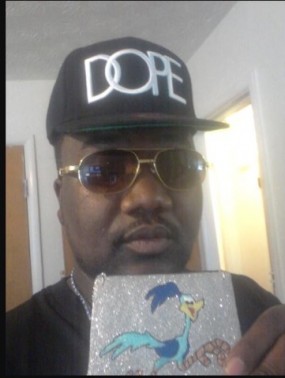
After being indicted on 46 counts of fraudulent activity, Ealy fired his attorney and chose to represent himself in court. In mid-November 2014 — just days before the jury in his trial was to issue its guilty verdict — Ealy slipped his ankle monitor and skipped town, but not before posting a taunting selfie to his Twitter account.
In the four months since his disappearance, investigators caught glimpses of Ealy jumping online as he made his way south to Atlanta. Incredibly, Ealy took time to file several lengthy pro se legal arguments (PDF) stating why the judge in the case was not impartial and that he deserved a retrial. When federal officials prosecuting his case responded (PDF) incredulously to his request, Ealy took it upon himself to file a response (PDF) to their motion for dismissal — all while on the lam.
Investigators close to the case say Ealy continued filing false tax refund requests while on the run from the law. But instead of turning to an underground identity theft service as he did previously, investigators say Ealy appears to have paid numerous inmates serving time in Ohio prisons for permission to file tax refund requests on their behalf with the Internal Revenue Service (IRS) — topping up the inmates’ commissary funds to the tune of $100 per filing while pocketing the rest of the fraudulent refunds.
According to whio.com, Ealy remains in the Northern District of Georgia until he can be extradited.