The FBI today said it has determined that the North Korean government is responsible for the devastating recent hack attack against Sony Pictures Entertainment. Here’s a brief look the FBI’s statement, what experts are learning about North Korea’s cyberattack capabilities, and what this incident means for other corporations going forward.
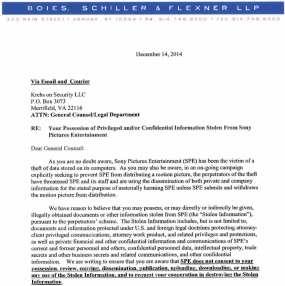
In a statement released early Friday afternoon, the FBI said that its investigation — along with information shared by Sony and other U.S. government departments and agencies — found that the North Korean government was responsible.
The FBI said it couldn’t disclose all of its sources and methods, but that the conclusion was based, in part, on the following:
-“Technical analysis of the data deletion malware used in this attack revealed links to other malware that the FBI knows North Korean actors previously developed. For example, there were similarities in specific lines of code, encryption algorithms, data deletion methods, and compromised networks.”
-“The FBI also observed significant overlap between the infrastructure used in this attack and other malicious cyber activity the U.S. government has previously linked directly to North Korea. For example, the FBI discovered that several Internet protocol (IP) addresses associated with known North Korean infrastructure communicated with IP addresses that were hardcoded into the data deletion malware used in this attack.”
-“Separately, the tools used in the SPE attack have similarities to a cyber attack in March of last year against South Korean banks and media outlets, which was carried out by North Korea.”
The agency added that it was “deeply concerned” about the destructive nature of this attack on a private sector entity and the ordinary citizens who work there, and that the FBI stands ready to assist any U.S. company that is the victim of a destructive cyber attack or breach of confidential information.
“Further, North Korea’s attack on SPE reaffirms that cyber threats pose one of the gravest national security dangers to the United States,” the FBI said. “Though the FBI has seen a wide variety and increasing number of cyber intrusions, the destructive nature of this attack, coupled with its coercive nature, sets it apart. North Korea’s actions were intended to inflict significant harm on a U.S. business and suppress the right of American citizens to express themselves. Such acts of intimidation fall outside the bounds of acceptable state behavior. The FBI takes seriously any attempt—whether through cyber-enabled means, threats of violence, or otherwise—to undermine the economic and social prosperity of our citizens.”
SPE was hit with a strain of malware designed to wipe all computer hard drives within the company’s network. The attackers then began releasing huge troves of sensitive SPE internal documents, and, more recently, started threatening physical violence against anyone who viewed the Sony movie “The Interview,” a comedy that involves a plot to assassinate North Korean leader Kim Jong Un. Not long after a number of top movie theater chains said they would not show the film, Sony announced that it would cancel the movie’s theatrical release.
Apparently emboldened by Sony’s capitulation, the attackers are now making even more demands. According to CNN, Sony executives on Thursday received an email apparently from the attackers said they would no longer release additional stolen Sony Pictures data if the company announced that it would also cancel any plans to release the movie on DVD, Netflix or elsewhere. The attackers also reportedly demanded that any teasers and trailers about The Interview online be removed from the Internet.
A ‘MAGIC WEAPON’
Little is publicly known about North Korea’s cyber warfare and hacking capabilities, but experts say North Korean leaders view cyber warfare capabilities as an important asymmetric asset in the face of its perceived enemies — the United States and South Korea. An in-depth report (PDF) released earlier this year by HP Security Research notes that in November 2013, North Korea’s “dear leader” Kim Jong Un referred to cyber warfare capabilities as a “magic weapon” in conjunction with nuclear weapons and missiles.
“Although North Korea’s limited online presence makes a thorough analysis of their cyber warfare capabilities a difficult task, it must be noted that what is known of those capabilities closely mirrors their kinetic warfare tactics,” HP notes. “Cyber warfare is simply the modern chapter in North Korea’s long history of asymmetrical warfare. North Korea has used various unconventional tactics in the past, such as guerilla warfare, strategic use of terrain, and psychological operations. The regime also aspires to create viable nuclear weapons.”
Sources familiar with the investigation tell KrebsOnSecurity that the investigators believe there may have been as many as several dozen individuals involved in the attack, the bulk of whom hail from North Korea. Nearly a dozen of them are believed to reside in Japan.
According to HP, a group of ethnic North Koreans residing in Japan known as the Chongryon are critical to North Korea’s cyber and intelligence programs, and help generate hard currency for the regime. The report quotes Japanese intelligence officials stating that “the Chongryon are vital to North Korea’s military budget, raising funds via weapons trafficking, drug trafficking, and other black market activities.” HP today published much more detail about specific North Korean hacking groups that may have played a key role in the Sony incident given previous such attacks. Continue reading