You can’t make this stuff up: A tech support company based in the United States that outsources its work to India says its brand is being unfairly maligned by — wait for it…..tech support scammers based in India. In an added twist, the U.S.-based tech support firm acknowledges that the trouble may be related to its admittedly false statements about being a Microsoft Certified Partner — the same false statements made by most telephone-based tech support scams.
Tech support scams are, unfortunately, an extremely common scourge. Most such scams are the telephonic equivalent of rogue antivirus attacks, which try to frighten consumers into purchasing worthless security software and services. Both types of scams try to make the consumer believe that the caller is somehow associated with Microsoft or with a security company, and each caller tries to cajole or scare the consumer into giving up control over his or her PC.
Earlier this month, a reader shared a link to a lengthy Youtube video by freelance journalist Carey Holzman, in which Holzman turns the tables on the tech support scammers. During the video, Holzman plays along and gives the scammer remote control access to a test computer he’s set up specifically for this video. The scammer, who speaks with a strong Indian accent but calls himself “Steve Wilson” from the “Microsoft technical department,” tries to convince Holzman that he works for a company that is a legitimate Microsoft support partner.
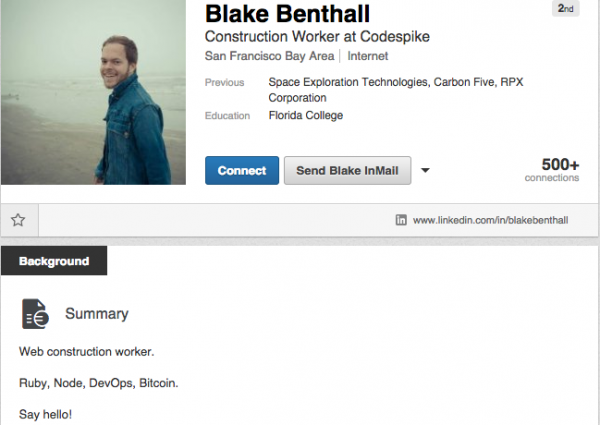
“Let me show you who we are,” the scammer says, opening up Google.com and typing SB3 Inc. Clicking on the first result brings up sb3inc[dot]com, which proudly displays an icon in the upper right corner of its home page stating that it is a Microsoft Certified Partner. “This is our mother company. Can you see that we are a Microsoft certified partner?”
When Holzman replies that this means nothing and that anyone can just put a logo on their site saying they’re associated with Microsoft, the scammer runs a search on Microsoft.com for SB3. The scammer shows true chutzpah when he points to the first result, which — if clicked — leads to a page on Microsoft’s community site where members try to warn the poster away from SB3 as a scam.
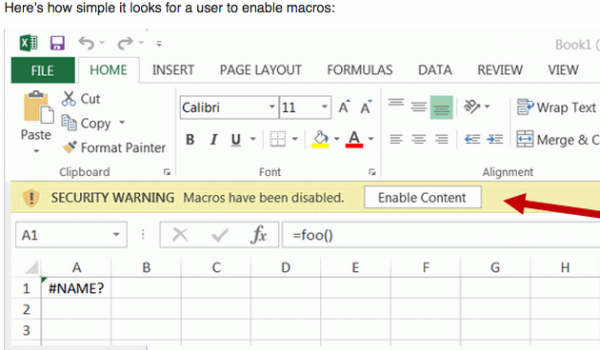
When Holzman tries to get the scammer to let him load the actual search result link about SB3 on Microsoft.com, the caller closes the browser window and proceeds to enable the SysKey utility on Windows, which allows the scammer to set a secret master password that must be entered before the computer will boot into Windows (effectively an attempt at locking Holzman out of his test computer if he tries to reboot).
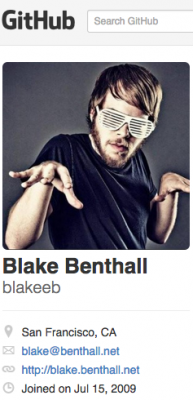
The video goes on for some time more, but I decided to look more closely at SB3. The Web site registration records for the company state that it is based in New Jersey, and it took less than a minute to find the Facebook page of the company’s owner — a Suvajit “Steve” Basu in Ridgewood, NJ. Basu’s Facebook feed has him traveling the world, visiting the World Cup in Brazil in 2014, the Ryder Cup in 2012, and more recently taking delivery on a brand new Porsche. Continue reading