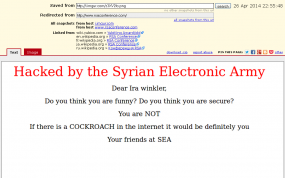
The Internet of Things is coming….to a highway sign near you? In the latest reminder that much of our nation’s “critical infrastructure” is held together with the Internet equivalent of spit and glue, authorities in several U.S. states are reporting that a hacker has once again broken into and defaced electronic road signs over highways in several U.S. states.
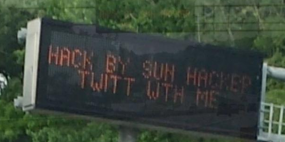
Earlier this week, news media in North Carolina reported that at least three highway signs there had apparently been compromised and re-worded to read “Hack by Sun Hacker.” Similar incidents were reported between May 27 and June 2, 2014 in two other states, which spotted variations on that message left by the perpetrator, (including an invitation to chat with him on Twitter).
The attack was reminiscent of a series of incidents beginning two years ago in which various electronic message signs were changed to read “Warning, Zombies Ahead”.
While at least those attacks were chuckle-worthy, messing with traffic signs is no laughing matter: As a report by the Multi-State Information Sharing and Analysis Center (MS-ISAC) points out, changes to road signs create a public safety issue because instead of directing drivers through road hazards, they often result in drivers slowing or stopping to view the signs or take pictures.
That same MS-ISAC notice, obtained by KrebsOnSecurity and published here (PDF), points out that these incidents appear to be encouraged by sloppy security on the part of those responsible for maintaining these signs.
“Investigators in one state believe the compromise may be in part due to the use of weak Simple Network Management Protocol (SNMP) community strings. Investigators in another state believe the malicious actor used Telnet port 23 and a simple password cracker to gain remote access. In one state the malicious actor changed the modem passwords, forcing technicians to restore to factory default settings to regain access.”