The recent zero-day vulnerability in Internet Explorer caused many (present company included) to urge Internet users to consider surfing the Web with a different browser until Microsoft issued a patch. Microsoft did so last month, but not before experts who ought to have known better began downplaying such advice, pointing out that other browser makers have more vulnerabilities and just as much exposure to zero-day flaws.
This post examines hard data that shows why such reasoning is more emotional than factual. Unlike Google Chrome and Mozilla Firefox users, IE users were exposed to active attacks against unpatched, critical vulnerabilities for months at a time over the past year and a half.
Attackers exploited zero-day holes in Internet Explorer for at least 89 days over the past 19 months.
The all-browsers-are-equally-exposed argument was most recently waged by Trend Micro‘s Rik Ferguson. Ferguson charges that it’s unfair and unrealistic to expect IE users to switch — however briefly — to experiencing the Web with an alternative browser. After all, he says, the data show that other browsers are similarly dogged by flaws, and switching offers no additional security benefits. To quote Ferguson:
“According to this blog post, in 2011 Google’s Chrome had an all time high of 275 new vulnerabilities reported, the current peak of an upward trend since its day of release. Mozilla Firefox, while currently trending down from its 2009 high, still had a reported 97 vulnerabilities. Microsoft’s Internet Explorer has been trending gradually down for the past five years and 2011 saw only 45 new vulnerabilities, less than any other browser except Apple’s Safari, which also had 45. Of course raw numbers of vulnerabilities are almost meaningless unless we consider the respective severity, but there again, of the ‘big three’ the statistics favour Internet Explorer. If zero-day vulnerabilities have to be taken into consideration too, they don’t really do much to change the balance, Google Chrome 6, Microsoft Internet Explorer 6 and Mozilla Firefox 4. Of course different sources offer completely different statistics, and simple vulnerability counts are no measure of relative (in)security of browsers, particularly in isolation. However, it cannot be ignored that vulnerabilities exist in every browser.”
Looking closer, we find that this assessment does not hold water. For one thing, while Ferguson acknowledges that attempting to rate the relative security of similar software products by merely comparing vulnerabilities is not very useful, he doesn’t offer much more perspective. He focuses on unpatched, publicly-highlighted vulnerabilities, but he forgets to ask and answer a crucial question: How do browser makers rate in terms of unpatched vulnerabilities that are actively being exploited?
Part of the problem here is that many security pundits rank vulnerabilities as “zero-day” as long as they are both publicly identified and unfixed. Whether there is evidence that anyone is actually attacking these vulnerabilities seems beside the point for this camp. But I would argue active exploitation is the most important qualifier of a true zero-day, and that the software flaws most worthy of worry and action by users are those that are plainly being exploited by attackers.
To that end, I looked back at the vulnerabilities fixed since January 2011 by Google, Microsoft and Mozilla, with an eye toward identifying true zero-day flaws that were identified publicly as being exploited before the vendor issued a software patch. I also queried both Mozilla and Google to find out if I had missed anything in my research.
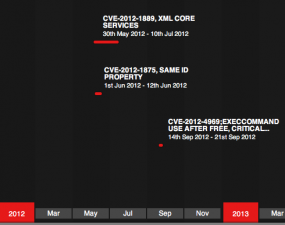
As Ferguson mentioned, all browser makers had examples over the past 19 months of working or proof-of-concept exploit code available for unpatched flaws in their products. However, both my own investigation and the public record show that of the three browsers, Internet Explorer was the only one that had critical, unpatched vulnerabilities that were demonstrably exploited by attackers before patches were made available. According to Microsoft’s own account, there were at least six zero-days actively exploited in the past 18 months in IE. All but one of them earned Microsoft’s most dire “critical” rating, leaving IE users under zero-day attack for at least 152 days since the beginning of 2011.
If we count just the critical zero-days, there were at least 89 non-overlapping days (about three months) between the beginning of 2011 and Sept. 2012 in which IE zero-day vulnerabilities were actively being exploited. That number is almost certainly conservative, because I could find no data on the window of vulnerability for CVE-2011-0094, a critical zero-day flaw fixed in MS11-018 that Microsoft said was being attacked prior to releasing a patch for it. This analysis also does not include CVE-2011-1345, a vulnerability demonstrated at the Pwn2Pwn contest in 2011.