When it’s time to book a vacation or a quick getaway, many of us turn to travel reservation sites like Expedia, Travelocity and other comparison services. But there’s a cybercrime-friendly booking service that is not well-known. When cyber crooks want to get away — with a crime — increasingly they are turning to underground online booking services that make it easy for crooks to rent hacked PCs that can help them ply their trade anonymously.
We often hear about hacked, remote-controlled PCs or “bots” being used to send spam or to host malicious Web sites, but seldom do security researchers delve into the mechanics behind one of the most basic uses for a bot: To serve as a node in an anonymization service that allows paying customers to proxy their Internet connections through one or more compromised systems.
 As I noted in a Washington Post column in 2008, “this type of service is especially appealing to criminals looking to fleece bank accounts at institutions that conduct rudimentary Internet address checks to ensure that the person accessing an account is indeed logged on from the legitimate customer’s geographic region, as opposed to say, Odessa, Ukraine.” Scammers have been using proxies forever it seems, but it’s interesting that it is so easy to find victims, once you are a user of the anonymization service.
As I noted in a Washington Post column in 2008, “this type of service is especially appealing to criminals looking to fleece bank accounts at institutions that conduct rudimentary Internet address checks to ensure that the person accessing an account is indeed logged on from the legitimate customer’s geographic region, as opposed to say, Odessa, Ukraine.” Scammers have been using proxies forever it seems, but it’s interesting that it is so easy to find victims, once you are a user of the anonymization service.
Here’s an overview of one of the more advanced anonymity networks on the market, an invite-only subscription service marketed on several key underground cyber crime forums.
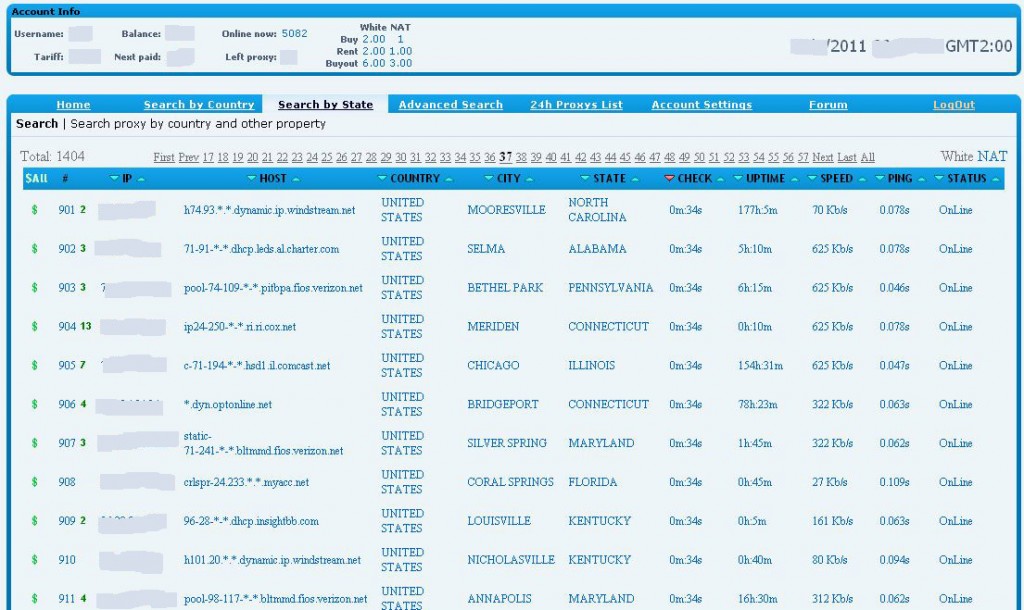
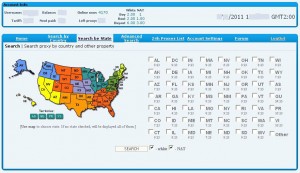
When I tested this service, it had more than 4,100 bot proxies available in 75 countries, although the bulk of the hacked PCs being sold or rented were in the United States and the United Kingdom. Also, the number of available proxies fluctuates daily, peaking during normal business hours in the United States. Drilling down into the U.S. map (see image above), users can select proxies by state, or use the “advanced search” box, which allows customers to select bots based on city, IP range, Internet provider, and connection speed. This service also includes a fairly active Russian-language customer support forum. Customers can use the service after paying a one-time $150 registration fee (security deposit?) via a virtual currency such as WebMoney or Liberty Reserve. After that, individual botted systems can be rented for about a dollar a day, or “purchased” for exclusive use for slightly more.
I tried to locate some owners of the hacked machines being rented via this service. Initially this presented a challenge because the majority of the proxies listed are compromised PCs hooked up to home or small business cable modem or DSL connections. As you can see from the screenshot below, the only identifying information for these systems was the IP address and host name. And although so-called “geo-location” services can plot the approximate location of an Internet address, these services are not exact and are sometimes way off.
I started poking through the listings for proxies that had meaningful host names, such as the domain name of a business. It wasn’t long before I stumbled upon the Web site for The Securities Group LLC, a Memphis, Tenn. based privately held broker/dealer firm specializing in healthcare partnerships with physicians. According to the company’s site, “TSG has raised over $100,000,000 having syndicated over 200 healthcare projects including whole hospital exemptions, ambulatory surgery centers, surgical hospitals, PET Imaging facilities, CATH labs and a prostate cancer supplement LLC with up to 400 physician investors.” The proxy being sold by the anonymization service was tied to the Internet address of TSG’s email server, and to the Web site for the Kirby Pines Retirement Community, also in Memphis.