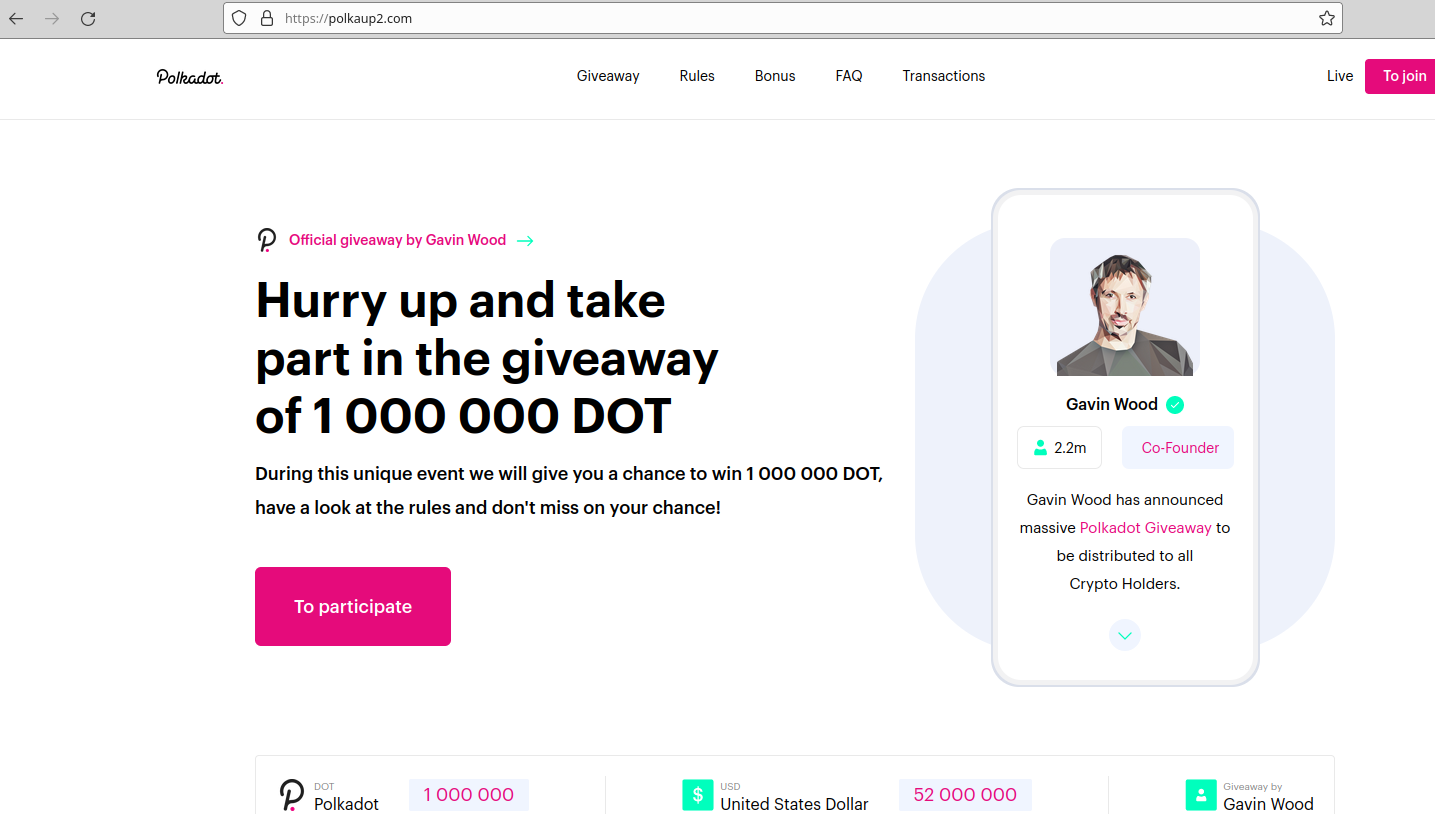
KrebsOnSecurity recently reviewed a copy of the private chat messages between members of the LAPSUS$ cybercrime group in the week leading up to the arrest of its most active members last month. The logs show LAPSUS$ breached T-Mobile multiple times in March, stealing source code for a range of company projects. T-Mobile says no customer or government information was stolen in the intrusion.
LAPSUS$ is known for stealing data and then demanding a ransom not to publish or sell it. But the leaked chats indicate this mercenary activity was of little interest to the tyrannical teenage leader of LAPSUS$, whose obsession with stealing and leaking proprietary computer source code from the world’s largest tech companies ultimately led to the group’s undoing.
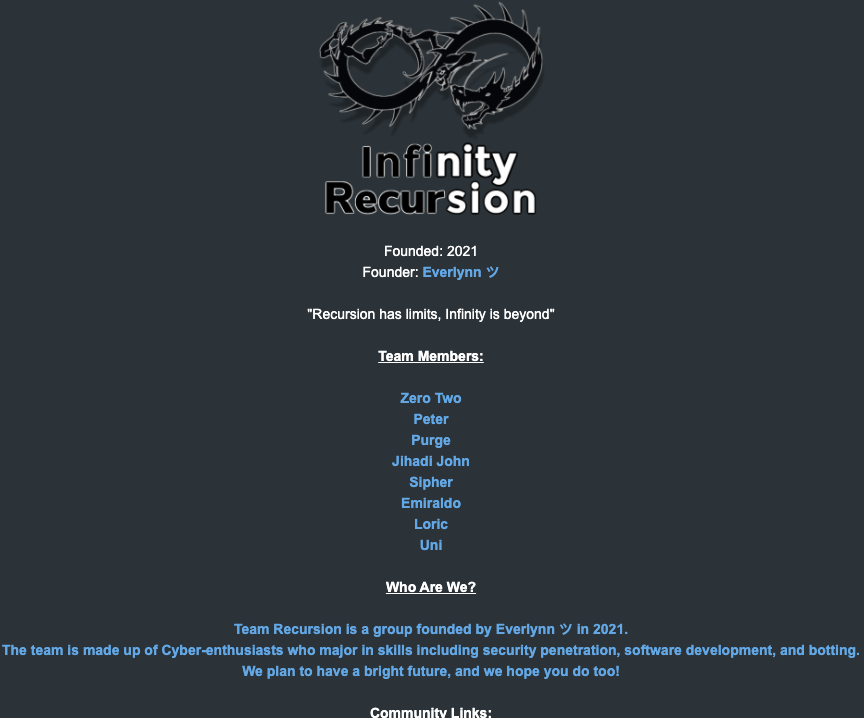
From its inception in December 2021 until its implosion late last month, LAPSUS$ operated openly on its Telegram chat channel, which quickly grew to more than 40,000 followers after the group started using it to leak huge volumes of sensitive data stolen from victim corporations.
But LAPSUS$ also used private Telegram channels that were restricted to the core seven members of the group. KrebsOnSecurity recently received a week’s worth of these private conversations between LAPSUS$ members as they plotted their final attacks late last month.
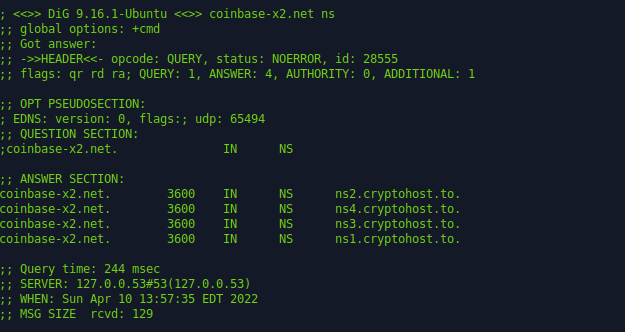
The candid conversations show LAPSUS$ frequently obtained the initial access to targeted organizations by purchasing it from sites like Russian Market, which sell access to remotely compromised systems, as well as any credentials stored on those systems.
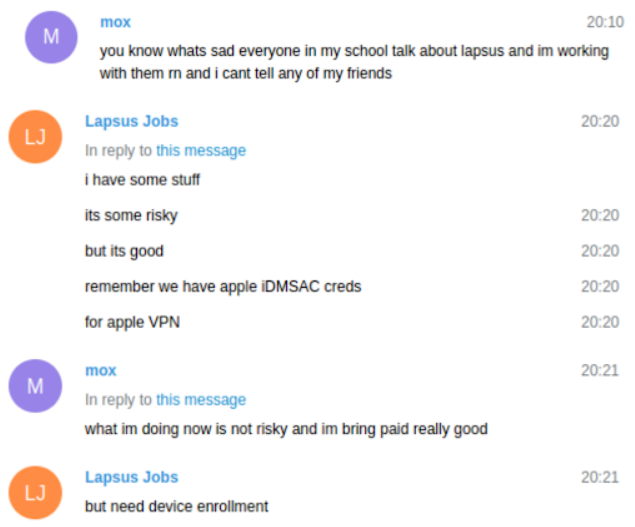
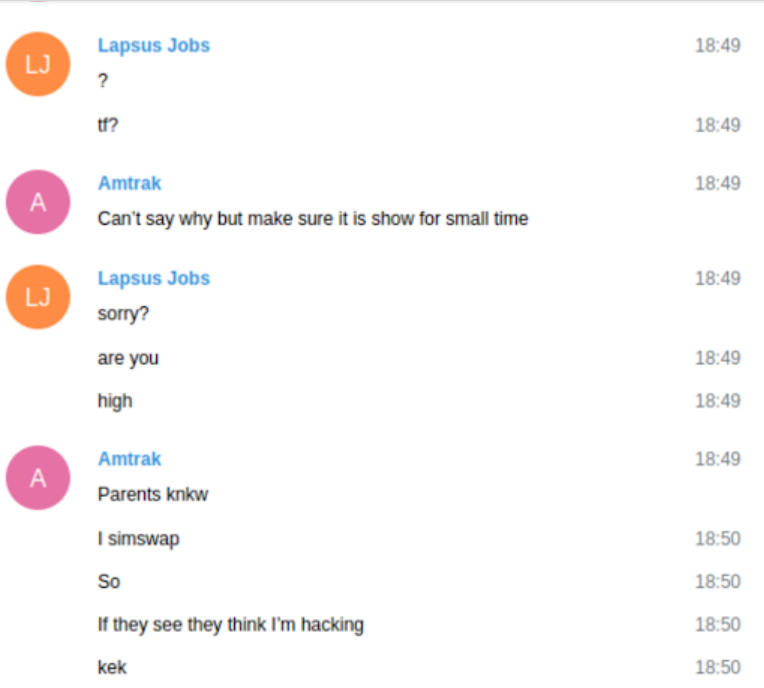
The logs indicate LAPSUS$ had exactly zero problems buying, stealing or sweet-talking their way into employee accounts at companies they wanted to hack. The bigger challenge for LAPSUS$ was the subject mentioned by “Lapsus Jobs” in the screenshot above: Device enrollment. In most cases, this involved social engineering employees at the targeted firm into adding one of their computers or mobiles to the list of devices allowed to authenticate with the company’s virtual private network (VPN).
The messages show LAPSUS$ members continuously targeted T-Mobile employees, whose access to internal company tools could give them everything they needed to conduct hassle-free “SIM swaps” — reassigning a target’s mobile phone number to a device they controlled. These unauthorized sim swaps allow an attacker to intercept a target’s text messages and phone calls, including any links sent via SMS for password resets, or one-time codes sent for multi-factor authentication.

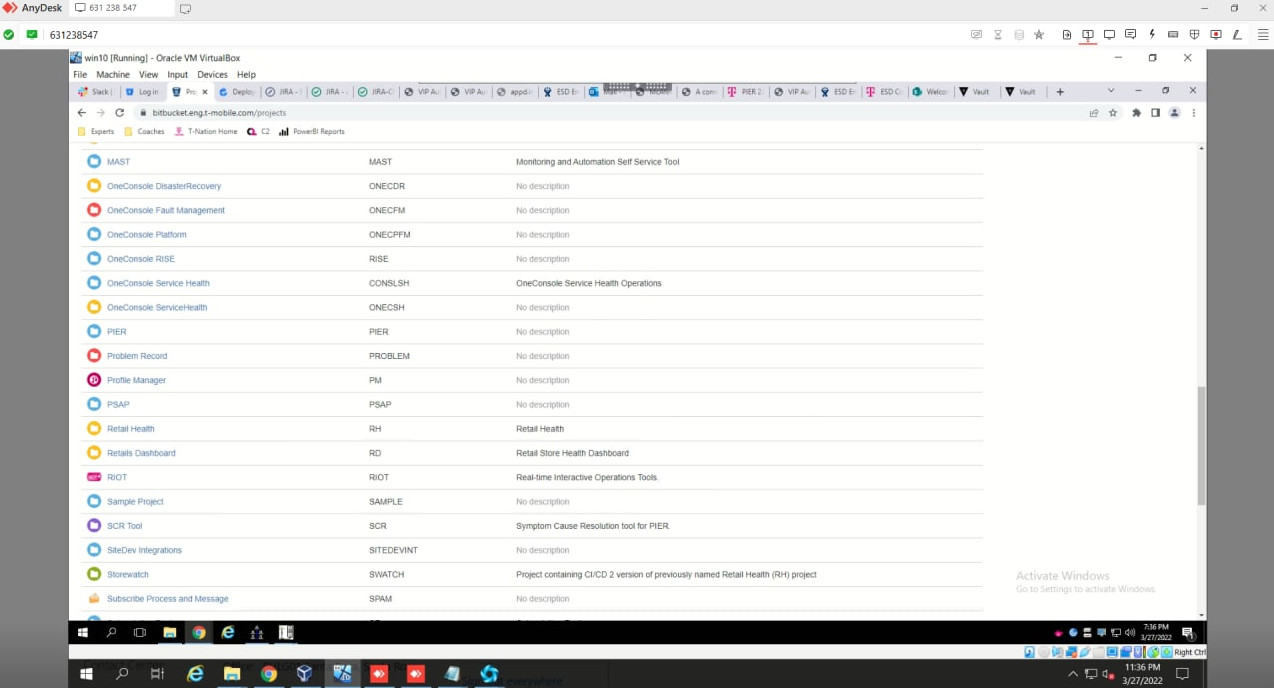
The LAPSUS$ group had a laugh at this screenshot posted by their leader, White, which shows him reading a T-Mobile news alert about their hack into Samsung. White is viewing the page via a T-Mobile employee’s virtual machine.
In one chat, the LAPSUS$ leader — a 17-year-old from the U.K. who goes by the nicknames “White,” “WhiteDoxbin” and “Oklaqq” — is sharing his screen with another LAPSUS$ member who used the handles “Amtrak” and “Asyntax.”
The two were exploring T-Mobile’s internal systems, and Amtrak asked White to obscure the T-Mobile logo on his screen. In these chats, the user “Lapsus Jobs” is White. Amtrak explains this odd request by saying their parents are aware Amtrak was previously involved in SIM swapping.
“Parents know I simswap,” Amtrak said. “So, if they see [that] they think I’m hacking.”
The messages reveal that each time LAPSUS$ was cut off from a T-Mobile employee’s account — either because the employee tried to log in or change their password — they would just find or buy another set of T-Mobile VPN credentials. T-Mobile currently has approximately 75,000 employees worldwide.
On March 19, 2022, the logs and accompanying screenshots show LAPSUS$ had gained access to Atlas, a powerful internal T-Mobile tool for managing customer accounts.
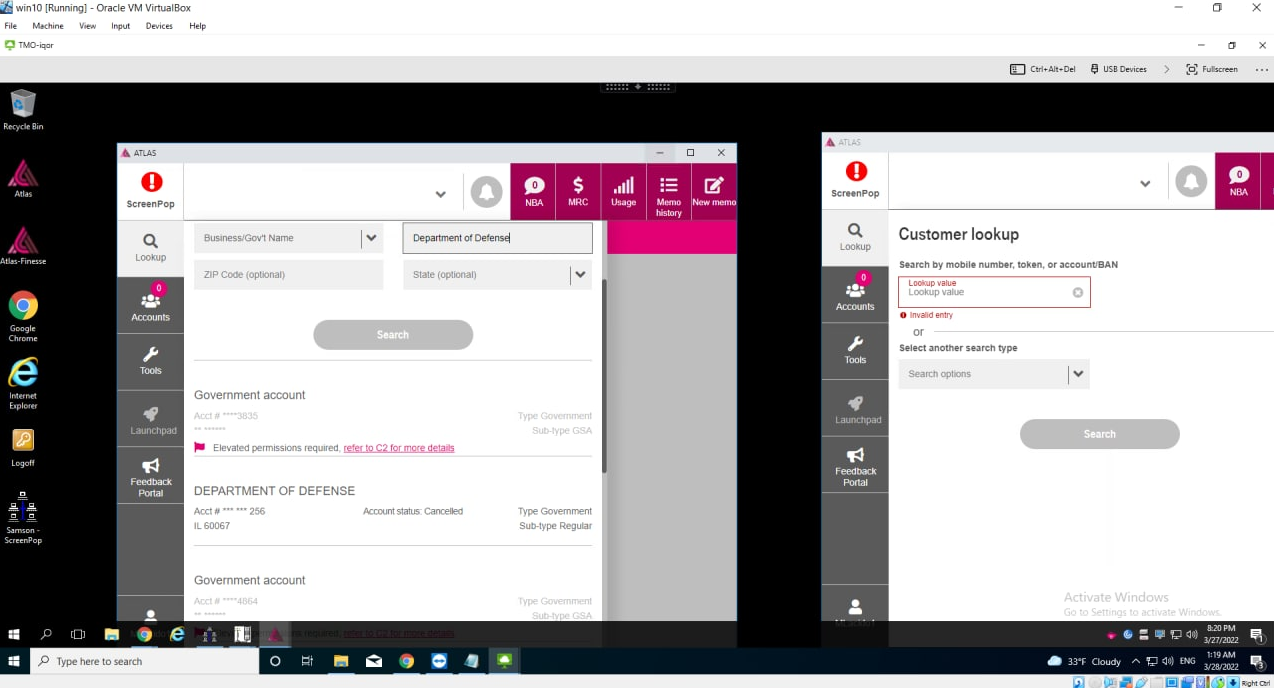
LAPSUS$ leader White/Lapsus Jobs looking up the Department of Defense in T-Mobile’s internal Atlas system.
After gaining access to Atlas, White proceeded to look up T-Mobile accounts associated with the FBI and Department of Defense (see image above). Fortunately, those accounts were listed as requiring additional verification procedures before any changes could be processed.
Faced with increasingly vocal pleadings from other LAPSUS$ members not to burn their access to Atlas and other tools by trying to SIM swap government accounts, White unilaterally decided to terminate the VPN connection permitting access to T-Mobile’s network.
The other LAPSUS$ members desperately wanted to SIM swap some wealthy targets for money. Amtrak throws a fit, saying “I worked really hard for this!” White calls the Atlas access trash and then kills the VPN connection anyway, saying he wanted to focus on using their illicit T-Mobile access to steal source code.
Perhaps to mollify his furious teammates, White changed the subject and told them he’d gained access to T-Mobile’s Slack and Bitbucket accounts. He said he’d figured out how to upload files to the virtual machine he had access to at T-Mobile. Continue reading