September featured two stories on a phony tech investor named John Bernard, a pseudonym used by a convicted thief named John Clifton Davies who’s fleeced dozens of technology companies out of an estimated $30 million with the promise of lucrative investments. Those stories prompted a flood of tips from Davies’ victims that paints a much clearer picture of this serial con man and his cohorts, including allegations of hacking, smuggling, bank fraud and murder.
KrebsOnSecurity interviewed more than a dozen of Davies’ victims over the past five years, none of whom wished to be quoted here out of fear of reprisals from a man they say runs with mercenaries and has connections to organized crime.
As described in Part II of this series, John Bernard is in fact John Clifton Davies, a 59-year-old U.K. citizen who absconded from justice before being convicted on multiple counts of fraud in 2015. Prior to his conviction, Davies served 16 months in jail before being cleared of murdering his third wife on their honeymoon in India.

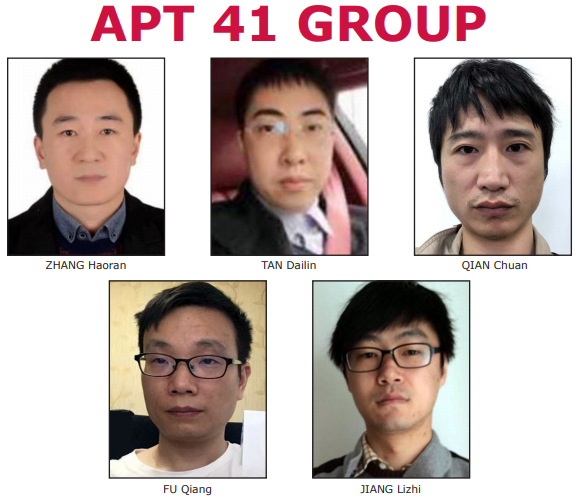
The scam artist John Bernard (left) in a recent Zoom call, and a photo of John Clifton Davies from 2015.
After eluding justice in the U.K., Davies reinvented himself as The Private Office of John Bernard, pretending to a be billionaire Swiss investor who made his fortunes in the dot-com boom 20 years ago and who was seeking investment opportunities.
In case after case, Bernard would promise to invest millions in tech startups, and then insist that companies pay tens of thousands of dollars worth of due diligence fees up front. However, the due diligence company he insisted on using — another Swiss firm called Inside Knowledge — also was secretly owned by Bernard, who would invariably pull out of the deal after receiving the due diligence money.
Bernard found a constant stream of new marks by offering extraordinarily generous finders fees to investment brokers who could introduce him to companies seeking an infusion of cash. When it came time for companies to sign legal documents, Bernard’s victims interacted with a 40-something Inside Knowledge employee named “Katherine Miller,” who claimed to be his lawyer.
It turns out that Katherine Miller is a onetime Moldovan attorney who was previously known as Ecaterina “Katya” Dudorenko. She is listed as a Romanian lawyer in the U.K. Companies House records for several companies tied to John Bernard, including Inside Knowledge Solutions Ltd., Docklands Enterprise Ltd., and Secure Swiss Data Ltd (more on Secure Swiss data in a moment).
Another of Bernard’s associates listed as a director at Docklands Enterprise Ltd. is Sergey Valentinov Pankov. This is notable because in 2018, Pankov and Dudorenko were convicted of cigarette smuggling in the United Kingdom.

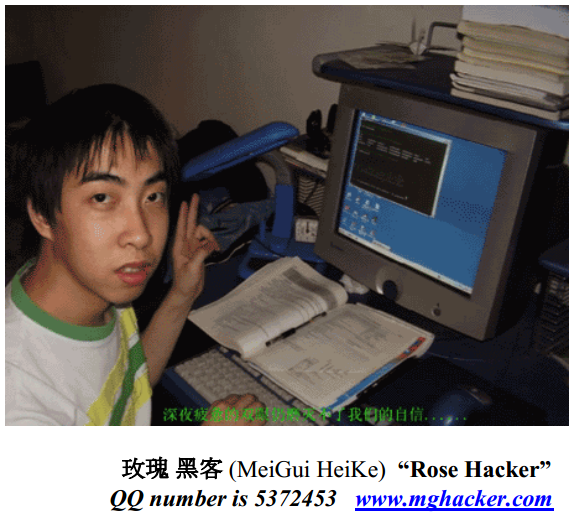
Sergey Pankov and Ecaterina Dudorenco, in undated photos. Source: Mynewsdesk.com
According to the Organized Crime and Corruption Reporting Project, “illicit trafficking of tobacco is a multibillion-dollar business today, fueling organized crime and corruption [and] robbing governments of needed tax money. So profitable is the trade that tobacco is the world’s most widely smuggled legal substance. This booming business now stretches from counterfeiters in China and renegade factories in Russia to Indian reservations in New York and warlords in Pakistan and North Africa.”
Like their erstwhile boss Mr. Davies, both Pankov and Dudorenko disappeared before their convictions in the U.K. They were sentenced in absentia to two and a half years in prison.
Incidentally, Davies was detained by Ukrainian authorities in 2018, although he is not mentioned by name in this story from the Ukrainian daily Pravda. The story notes that the suspect moved to Kiev in 2014 and lived in a rented apartment with his Ukrainian wife. Continue reading