We’ve seen an ugly trend recently of tech news stories and cybersecurity firms trumpeting claims of ransomware attacks on companies large and small, apparently based on little more than the say-so of the ransomware gangs themselves. Such coverage is potentially quite harmful and plays deftly into the hands of organized crime.
Often the rationale behind couching these events as newsworthy is that the attacks involve publicly traded companies or recognizable brands, and that investors and the public have a right to know. But absent any additional information from the victim company or their partners who may be affected by the attack, these kinds of stories and blog posts look a great deal like ambulance chasing and sensationalism.

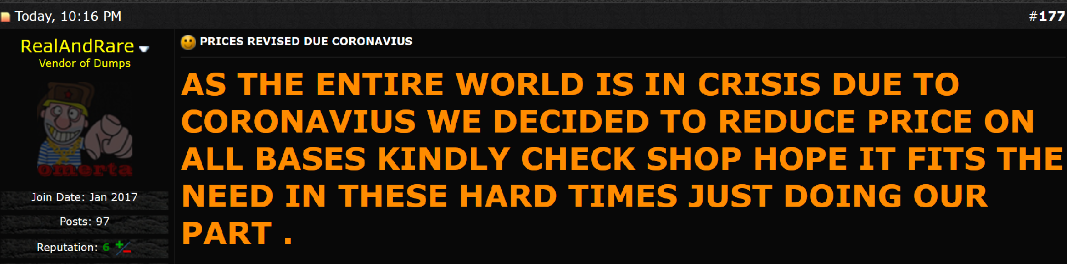
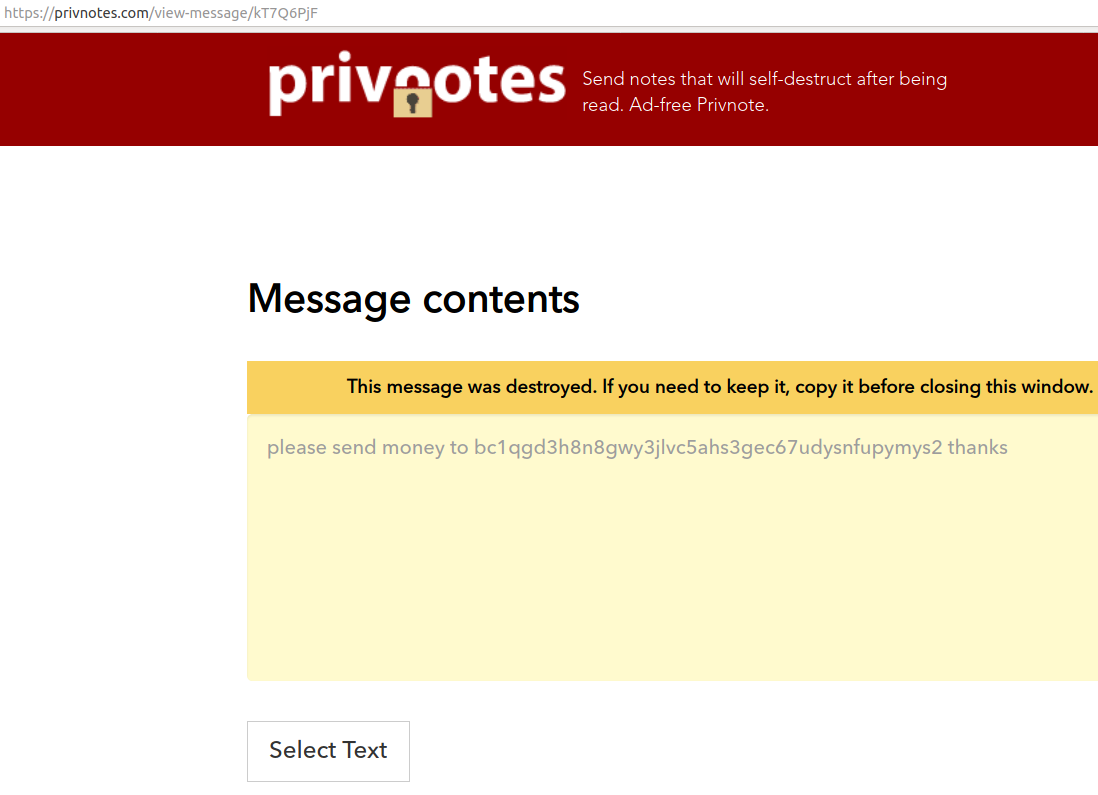
Currently, more than a dozen ransomware crime gangs have erected their own blogs to publish sensitive data from victims. A few of these blogs routinely issue self-serving press releases, some of which gallingly refer to victims as “clients” and cast themselves in a beneficent light. Usually, the blog posts that appear on ransom sites are little more than a teaser — screenshots of claimed access to computers, or a handful of documents that expose proprietary or financial information.
The goal behind the publication of these teasers is clear, and the ransomware gangs make no bones about it: To publicly pressure the victim company into paying up. Those that refuse to be extorted are told to expect that huge amounts of sensitive company data will be published online or sold on the dark web (or both).
Emboldened by their successes, several ransomware gangs recently have started demanding two ransoms: One payment to secure a digital key that can unlock files, folders and directories encrypted by their malware, and a second to avoid having any stolen information published or shared with others.
KrebsOnSecurity has sought to highlight ransomware incidents at companies whose core business involves providing technical services to others — particularly managed service providers that have done an exceptionally poor job communicating about the attack with their customers.
Overall, I’ve tried to use each story to call attention to key failures that frequently give rise to ransomware infections, and to offer information about how other companies can avoid a similar fate.
But simply parroting what professional extortionists have posted on their blog about victims of cybercrime smacks of providing aid and comfort to an enemy that needs and deserves neither.
Maybe you disagree, dear readers? Feel free to sound off in the comments below.









 On June 16, authorities in Michigan arrested 29-year-old Justin Sean Johnson in connection with a 43-count indictment on charges of conspiracy, wire fraud and aggravated identity theft.
On June 16, authorities in Michigan arrested 29-year-old Justin Sean Johnson in connection with a 43-count indictment on charges of conspiracy, wire fraud and aggravated identity theft.
 June marks the fourth month in a row that Microsoft has issued fixes to address more than 100 security flaws in its products. Eleven of the updates address problems Microsoft deems “critical,” meaning they could be exploited by malware or malcontents to seize complete, remote control over vulnerable systems without any help from users.
June marks the fourth month in a row that Microsoft has issued fixes to address more than 100 security flaws in its products. Eleven of the updates address problems Microsoft deems “critical,” meaning they could be exploited by malware or malcontents to seize complete, remote control over vulnerable systems without any help from users.