Federal prosecutors in California have filed criminal charges against four employees of Adconion Direct, an email advertising firm, alleging they unlawfully hijacked vast swaths of Internet addresses and used them in large-scale spam campaigns. KrebsOnSecurity has learned that the charges are likely just the opening salvo in a much larger, ongoing federal investigation into the company’s commercial email practices.

Prior to its acquisition, Adconion offered digital advertising solutions to some of the world’s biggest companies, including Adidas, AT&T, Fidelity, Honda, Kohl’s and T-Mobile. Amobee, the Redwood City, Calif. online ad firm that acquired Adconion in 2014, bills itself as the world’s leading independent advertising platform. The CEO of Amobee is Kim Perell, formerly CEO of Adconion.
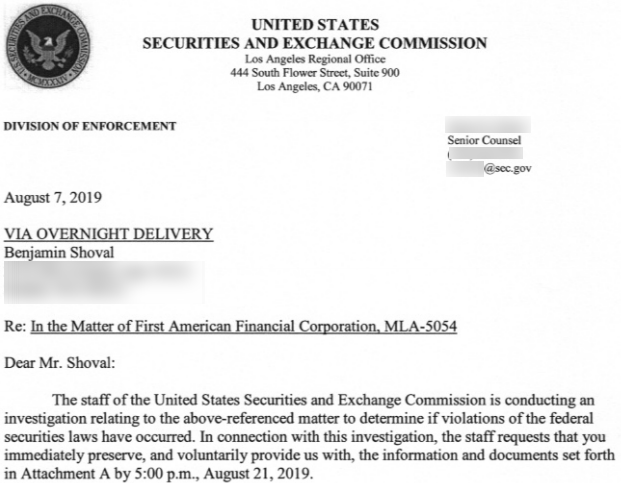
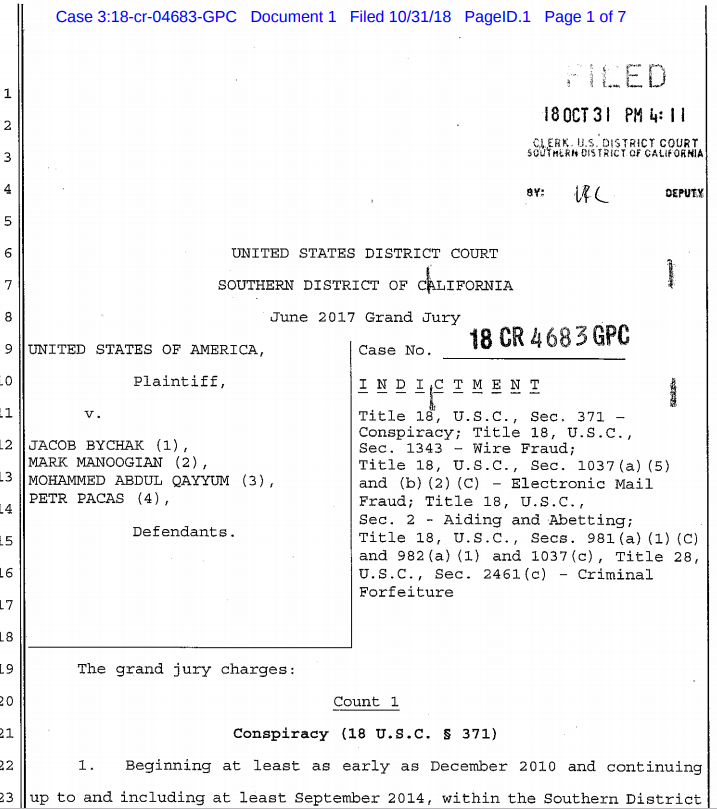
In October 2018, prosecutors in the Southern District of California named four Adconion employees — Jacob Bychak, Mark Manoogian, Petr Pacas, and Mohammed Abdul Qayyum — in a ten-count indictment on charges of conspiracy, wire fraud, and electronic mail fraud. All four men have pleaded not guilty to the charges, which stem from a grand jury indictment handed down in June 2017.
‘COMPANY A’
The indictment and other court filings in this case refer to the employer of the four men only as “Company A.” However, LinkedIn profiles under the names of three of the accused show they each work(ed) for Adconion and/or Amobee.
Mark Manoogian is an attorney whose LinkedIn profile states that he is director of legal and business affairs at Amobee, and formerly was senior business development manager at Adconion Direct; Bychak is listed as director of operations at Adconion Direct; Quayyum’s LinkedIn page lists him as manager of technical operations at Adconion. A statement of facts filed by the government indicates Petr Pacas was at one point director of operations at Company A (Adconion).
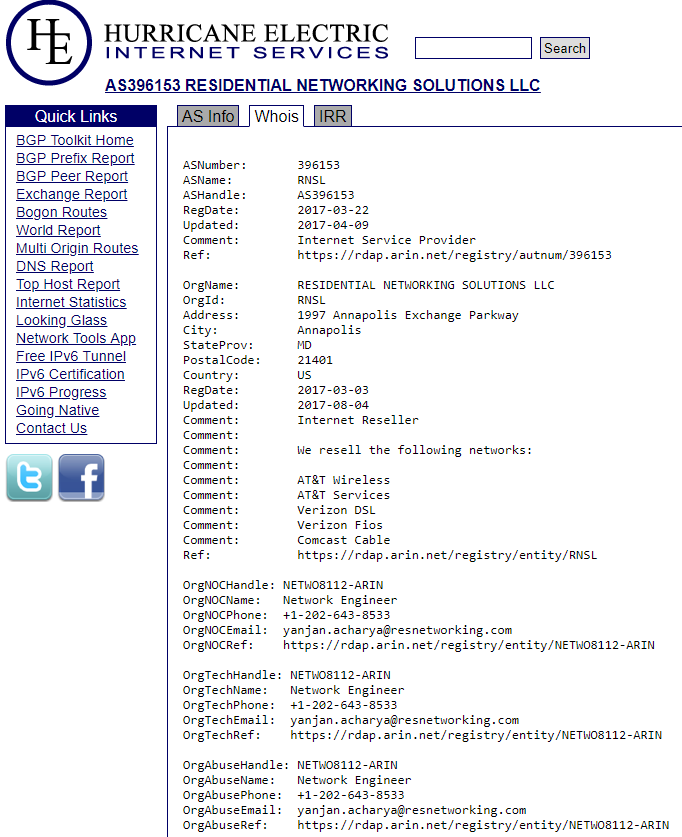
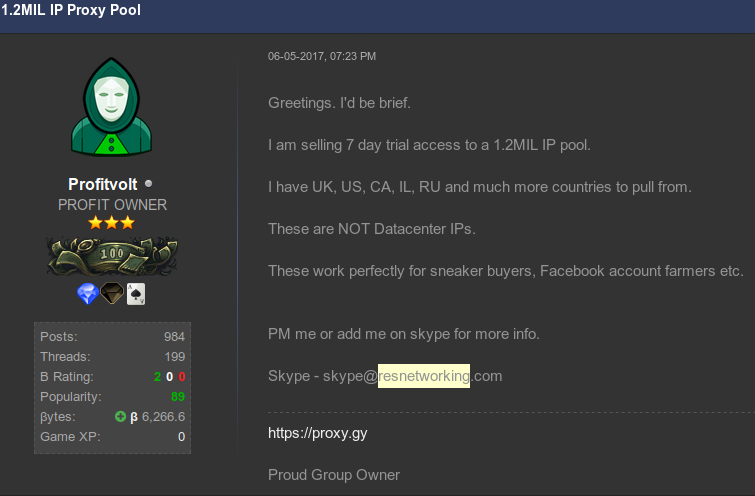
According to the indictment, between December 2010 and September 2014 the defendants engaged in a conspiracy to identify or pay to identify blocks of Internet Protocol (IP) addresses that were registered to others but which were otherwise inactive.
The government alleges the men sent forged letters to an Internet hosting firm claiming they had been authorized by the registrants of the inactive IP addresses to use that space for their own purposes.
“Members of the conspiracy would use the fraudulently acquired IP addresses to send commercial email (‘spam’) messages,” the government charged.
HOSTING IN THE WIND
Prosecutors say the accused were able to spam from the purloined IP address blocks after tricking the owner of Hostwinds, an Oklahoma-based Internet hosting firm, into routing the fraudulently obtained IP addresses on their behalf.
Hostwinds owner Peter Holden was the subject of a 2015 KrebsOnSecurity story titled, “Like Cutting Off a Limb to Save the Body,” which described how he’d initially built a lucrative business catering mainly to spammers, only to later have a change of heart and aggressively work to keep spammers off of his network.
That a case of such potential import for the digital marketing industry has escaped any media attention for so long is unusual but not surprising given what’s at stake for the companies involved and for the government’s ongoing investigations.
Adconion’s parent Amobee manages ad campaigns for some of the world’s top brands, and has every reason not to call attention to charges that some of its key employees may have been involved in criminal activity.
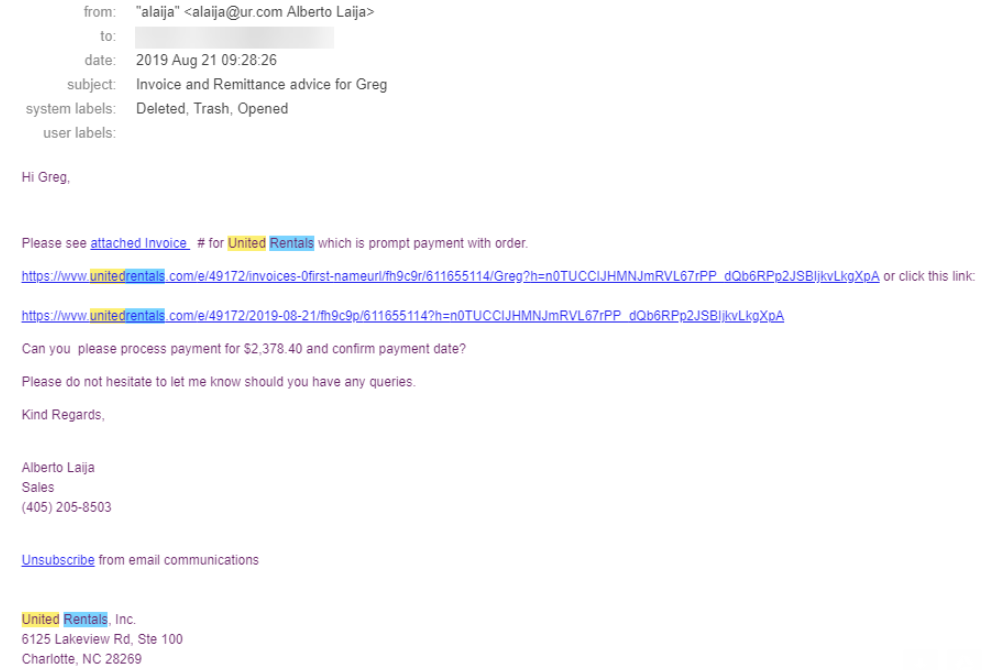
Meanwhile, prosecutors are busy following up on evidence supplied by several cooperating witnesses in this and a related grand jury investigation, including a confidential informant who received information from an Adconion employee about the company’s internal operations. Continue reading





 Okay, maybe a trip to the dentist’s office is still preferable. In any case, today is the second Tuesday of the month, which means it’s once again Patch Tuesday (or — depending on your setup and when you’re reading this post — Reboot Wednesday). Microsoft today released patches to fix some 93 vulnerabilities in Windows and related software, 35 of which affect various Server versions of Windows, and another 70 that apply to the Windows 10 operating system.
Okay, maybe a trip to the dentist’s office is still preferable. In any case, today is the second Tuesday of the month, which means it’s once again Patch Tuesday (or — depending on your setup and when you’re reading this post — Reboot Wednesday). Microsoft today released patches to fix some 93 vulnerabilities in Windows and related software, 35 of which affect various Server versions of Windows, and another 70 that apply to the Windows 10 operating system.