Several sources in the financial industry say they are seeing a spike in fraud on customer cards used at ATMs in Mexico. The reason behind that apparent increase hopefully will be fodder for another story. In this post, we’ll take a closer look at a pair of ATM skimming devices that were found this month attached to a cash machine in Puerto Vallarta — a popular tourist destination on Mexico’s Pacific coast.
On Saturday, July 18, 2015, municipal police in Puerto Vallara arrested a man who had just replaced the battery in a pair of skimming devices he or an associate had installed at an ATM in a busy spot of the town. This skimming kit targeted certain models of cash machines made by Korean ATM manufacturer Hyosung, and included a card skimming device as well as a hidden camera to record the victim’s ATM card PIN.
Here’s a look at the hidden camera installed over the compromised card reader. Would you have noticed anything amiss here?

The tiny pinhole camera was hidden in a molded plastic fascia designed to fit over top of the area directly above the PIN pad. The only clue that something is wrong here is a gap of about one millimeter between the PIN capture device and the actual ATM. Check out the backside of the false front:
The left side of the false fascia (as seen from the front, installed) contains the battery units that power the video camera:
The device used to record data from the magnetic stripe as the customer inserts his ATM card into the machine is nothing special, but it does blend in pretty well as we can see here:
Have a gander at the electronics that power this badboy:
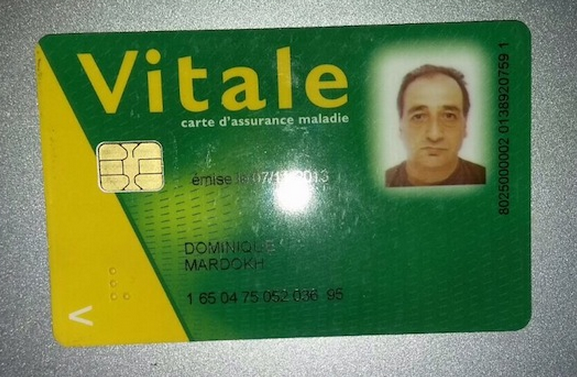
According to a local news clipping about the skimming incident, the fraudster caught red-handed was found in possession of a Carte Vitale card, a health insurance card of the national health care system in France.
The man gave his name as Dominique Mardokh, the same name on the insurance card. Also, the picture on the insurance card matched his appearance in real life; here’s a picture of Mardokh in the back of a police car.
According to the news site Noticiaspv.com, the suspect was apprehended by police as he fled the scene in a vehicle with license plates from Quintana Roo, a state nearly 2,500 km away on the Atlantic side of Mexico that is the home of another very popular tourist destination: Cancún.
Ironically, the healthcare card that identified this skimmer scammer is far more secure than the bank cards he was allegedly stealing with the help of the skimming devices. That’s because the healthcare card stores data about its owner on a small computer chip which makes the card difficult for thieves to duplicate.
Virtually all European banks and most non-US financial institutions issue chip-and-PIN cards (also called Europay, Mastercard and Visa or EMV), but unfortunately chip cards have been slow to catch on in the United States. Most US-based cards still store account data in plain text on a magnetic stripe, which can be easily copied by skimming devices and encoded onto new cards.
For reasons of backward compatibility with ATMs that aren’t yet in line with EMV, many EMV-compliant cards issued by European banks also include a plain old magnetic stripe. The weakness here, of course, is that thieves can still steal card data from Europeans using skimmers on European ATMs, but they need not fabricate chip-and-PIN cards to withdrawal cash from the stolen accounts: They simply send the card data to co-conspirators in the United States who use it to fabricate new cards and to pull cash out of ATMs here, where the EMV standard is not yet in force.
This skimmers found in Mexico (where most credit cards also are identified by microchip) abuse that same dynamic: Undoubtedly, the thieves in this scheme compromised ATMs at popular tourist destinations because they knew these places were overrun with American tourists.
In October 2015, U.S. merchants that have not yet installed card readers which accept more secure chip-based cards will assume responsibility for the cost of fraud from counterfeit cards. While most experts believe it may be years after that deadline before most merchants have switched entirely to chip-based card readers (and many U.S. banks are only now thinking about issuing chip-based cards to customers). Unfortunately, that liability shift doesn’t apply to ATMs in the U.S. until October 2017.
Whether or not your card has a chip in it, one way to defeat skimmers that rely on hidden cameras (and that’s most of them) is to simply cover the PIN pad with your hand when entering your PIN: That way, if even if the thieves somehow skim your card, there is less chance that they will be able to snag your PIN as well. You’d be amazed at how many people fail to take this basic precaution. Yes, there is still a chance that thieves could use a PIN-pad overlay device to capture your PIN, but in my experience these are far less common than hidden cameras (and quite a bit more costly for thieves who aren’t making their own skimmers).
Are you as fascinated by ATM skimmers as I am? Check out my series on this topic, All About Skimmers.
Update, July 28, 8:54 a.m. ET: ATM maker NCR has just released an advisory also warning about a spike in ATM skimming tied to Mexico. See the alert here (PDF).








I was myself a victim in Mexico city.
My american Citibank card still does not have chip, so I use it seldomly per month. (I’m an avid reader of this blog, I typically take precautions when using my debit card)
However, one day I withdrew money from a local branch of Citibank (banamex), the day after at 6am I got withdraws totaling 1500 USD in London, UK.
Fortunately I got my money back…
How is that even possible?! In UK we have used chip and PIN for years, I doubt there’s a single ATM here that does not read chips…
Someone mind explaining this?
The victims card didn’t have a chip on it. That’s it. Card details were recorded, sent to UK where details copied onto a blank standard card, off they went.
Just because chip is standard on the card, dosent mean the ATM’s will only read chip based cards, theyre backwards compatible.
No, not all ATMs have chip readers installed. Europe region – yes, probably 99,8% of them are EMV ready. As for the Mexico, from what I see (i’m in issuing business) – split is 25% EMV and 75% non-EMV ATMs. So you can freely use skimmed chip card in those ATMs.
A lot of EMV-ready ATMs swallow the whole card, so could still be fitted with a mag stripe skimmer while the cardholder relaxes in the assumption that their card is safe. The issue isn’t really the ATM – as long as cards have the mag stripe, and it is accepted somewhere, there will still be a risk of skimming.
Many of the ATM that I frequently use have on one of first screen (after selecting language) “do not use this ATM if it looks different than on this photo” when waiting on card authorization (or something); I wonder why it is not more widespread.
If necessary, and not cost prohibitive, these thieves will reproduce it.
While such a screen could be somewhat helpful in the short term, it won’t really benefit that much.
Skimmers can even reproduce the green glow / rounding image.
This attack surface will only be resolved once EMV is fully deployed.
>> “do not use this ATM if it looks different than on this photo” when waiting on card authorization
I know you said “(or something)” but can’t resist pointing out that if you’ve already inserted your card and entered the PIN, which has to be real-time authorized … it’s too late!
Also, I doubt the average person pays much attention to the screen except for entering their PIN and selecting how much money they want. Even if they did, I doubt the photo would give them enough information to make a good decision.
Furthermore, such photos would serve as a guideline for crooks to “match” as closely as possible. They absolutely would exploit any ambiguities.
Brian, can you get a picture where you point out the hole for the camera?
Exactly. I do not see any camera hole either.
That’s the point. You can’t see it from the front. If you could, it would be near the center of the panel to the right of the PIN pad.
Brian, I realized it could not be seen from the front.
That is why I asked if you could obtain a picture (which is taken from a different angle, of course) that does show the location. A shot taken, for example, directed upward into the PIN pad enclosure.
From what your reply says I would conclude it is built into the side panel of the enclosure.
This is important, because I usually shield the PIN pad directly above, but if holes for the camera are put into the side panels I will have to fashion some kind of a curved shield that covers view not only from the top, but also from the sides.
George,
Many hidden cams record from the side. See:
http://krebsonsecurity.com/wp-content/uploads/2010/08/wouldyou-300×217.jpg
http://krebsonsecurity.com/2010/11/all-in-one-skimmers/
http://krebsonsecurity.com/2011/12/pro-grade-3d-printer-made-atm-skimmer/
http://krebsonsecurity.com/2012/04/skimtacular-all-in-one-atm-skimmer/
Thanks ‘
Anyways, I didn’t take the pictures, and I don’t have any others, so….
Brian, many thanks for posting these news. Helps a lot to educate my collegues and law enforcement. Cheers!
Brian,
Great article, I am seeing massive spikes in ATM fraud in both Mexico as well as Italy.
Love seeing the real them.
Thanks again.
Curtis
I’ve received a couple of updated credit cards with chips, but according to the bank FAQs, no PIN is possible. Many European checkout clerks are confused about the American mag-stripe cards, not knowing how to swipe them, or confused about the lack of PIN.
Ironically, I had cards with chips in them years ago, but the banks dropped it and substituted RFID (which I’ve never had the ability to use). Brain, you haven’t come across RFID skimmers?
There are two kinds of RFIDs:
1. Static beacons.
2. Active programs.
A credit card with a magstripe is like a static beacon, the information on the strip doesn’t change.
It doesn’t technically have to be this way, a couple of groups have come out with fancy [1] “credit cards” that let you have them change their personality. But it generally is static.
The information in the credit card strip is basically: card issuer, account number, client name, static-validation-code (this is what’s called a “shared secret” in the security community). It’s similar to the sort of information that was used before magnetic strips were added to cards, when carbon imprints were taken of the raised numbers. The numeric information on the card didn’t change between transactions.
EMV, and EMV-RFID work in the second manner. Instead of sending *all* the information the card has, the “reader” sends the card information about the transaction it wants to process. The card then “signs” that transaction and sends back a signature. The reader then uses this signature (e.g. by sending it to the card issuer for verification) to decide to accept the transaction. This “signature” system is more or less the same system that browsers use for secure connections to web sites (@Brian: HSTS, please?), it’s called “Public Key Cryptography” [2].
A short and very inaccurate example for how it works:
Imagine that your secret is “102938317” and for simplicity that I, your credit issuer also know this secret. I could have you include that secret with each transaction, but if I do that, then each merchant will also have our secret, which would mean they could make their own transactions (or a thief could). Instead, imagine that I issue instructions for your card to take the 3rd, 7th, and 9th digits, as a set (237) along with your card’s transaction counter (this was your 5th transaction) and use that as part of a mathematical operation (roughly a hash) of the transaction your card is making. If the merchant is evil, and the next time the card needs to use the 3rd, 6th, and 10th digits, the merchant doesn’t have the information necessary to produce the signature. And, if the merchant/thief tries to sign a second transaction claiming it’s transaction #5, I, your issuer will reject it. The system is more complicated than this — the issuer shouldn’t know the secret on the card, just a secret it can use to verify that you have it (there is cool math here), and there’s more data involved in the process. But the key is that your card never tells the reader everything it knows, and the information it provides isn’t sufficient for anyone to impersonate it for most other future transactions (there are some sucky edges for network-unavailable transactions, and poor implementations).
[1] http://www.cnet.com/how-to/smart-credit-cards-swyp-plastc-stratos-coin/
[2] https://en.wikipedia.org/wiki/Public-key_cryptography
When I use a bank ATM , I always check out the area around the card insert slot before putting in my card. Now and days you can’t trust banks to protect their customers with outside ATM machines.
I now have three credit cards with E.M.V. and use that feature anytime I’m using a P.O.S.
I have also been victim of ATM fraud in Mexico, beware if visiting from waiters in restaurants, gas station clerks and others who you might give your card too, don’t let it leave your sight they are sometimes scanned or photographed and used for online purchases. Yes, I’ve been a victim also.
They’re now adding RFID chips into credit/bank cards. 1 step forward, 2 steps back.
Not really, the RFID doesn’t simply give away the account details, it’s a tokenised handshake of some kind to authorise a payment of upto £20/$30, with the merchant choosing whether out not to bear the slim risk in return for the convenience and lower cash handling costs. I use it all the time, it’s incredibly handy to pay for a 99p coffee with a tap of a card whilst still collecting air miles!
I hope you are taking it out of a rfd wallet. To tap it. Prior to 2000, there were articles written as proof of concept on rfd readers being installed in grocery stores in the US to record inventory. The sa me year, a university in Oregon published a paper how to hack the then popular rfd key, used for gas pitches while sitting in a vehicle out of sight of the stores parking lot camera. That was fifty foot away. With today’s readers, an article in the news, 2010, I believe, was reading rfd in a briefcase reader while walking down wall street. Where is rfd safer from computing power? Better readers, further away, maybe, just not enough interest yet. Gas purchases are usually limited to 100 dollars. Wider acceptance could be a downfall.
Nice article! You always do a great job on this topic, thanks for the details and great photo examples. I use these to help train folks on what to watch out for at the ATM. It really opens their eyes to see the actual devices and how they are hidden.
Also, was nice to see they gave you credit for the AM story on comedy central’s @midnight show.
Thanks for caring about Mexico, Brian! You have loyal readers down here, and we appreciate the alert!
I was in the UK a year or so ago, and nobody seemed at all confused about cards that required a signature instead of a PIN. But since I knew it was a chip card, I just stuck it directly in the slot instead of handing it to the clerk or anything.
You were pretty much out of luck if you wanted to use an automated kiosk however -say to rent a bike. At the time, those machines pretty much required the PIN.
I have yet to see an RFID credit card, and I do test them with various tools and look for the little logo.
It takes but a few minutes to have your bank/credit union prepare a credit card for a secondary account in which you have a balance of maybe $10.00 with no overdraft. Before going out to wine and dine for an evening, or before going to withdraw funds, use you computer/phone to transfer the amount you intend spending or withdrawing from your main account into this secondary account. Withdraw the same amount or pay for your evening with this card. The balance would now revert to the original balance of $10.00. Only a suggestion . . . . .
Calum,
a good idea.
However, you talk about a credit card, yet it sounds like you meant ATM/debit card.
Whilst there may be card skimming occurring in Mexico, it certainly doesn’t appear that it is Mexicans that are doing it!
As an expat living in Mexico, I recall as similar arrest in Puerto Vallarta a few years back, and the suspects were Eastern European, same as this guy.
Based on my limited knowledge of this ‘business’, it appears that there is a certain ethnic group that has cornered most of the market worldwide.
Hi Brian,
For privacy reasons, you may want to blur out the number on the Carte Vitale screenshot : it is the (french) SSN of the cardholder which contains various info, such as gender, DOB and birth place.
kind regards,
The information (including that photo) was taken from another news publication
http://www.noticiaspv.com/capturaron-a-clonador-de-tarjetas-bancarias/
I am sorry, but I don’t buy the argument that “somebody else did it, so can I”. I agree that the information will still be available on the Internet, but there is no need to give it more exposure.
Your article shows up way before the Mexican one when we search for this guy. And, as I replied to Peter (below in the thread), we have no guarantee that this number really belong to this guy.
Should that be a US SSN, I am not sure you would have published is so bluntly.
+1 to @FrenchGuy
French SSN are a powrful tool, and sould not be disclosed.
I think a simpler way is to do what banks in India have started what they call as One Time Passdword or OTP as it’s known colloquially.
The idea being the bank sends you a text with an OTP for A SPECIFIC transaction.
It isn’t foolsafe as well because if hackers are into your phone, then too you’re toast!
I see absolutely nothing amiss in the two exterior shots of the ATMs. An arrow or something would be helpful.
@FrenchGuy:
Really? This guy’s part of a skimming scam and you’re concerrned about protecting his privacy? Yes, I know he hasn’t been convicted yet, but it sound’s like there’s pretty convincing evidence. Also, that info might not legitimately belong to him, right?
@Peter:
Really. Like you said, he is not convicted yet. So until proven guilty, he is innocent and should treated accordingly. We don’t know all the story since it only based so far on 2-3 news articles.
And as you said (again), that info might not legitimately belong to him. That could mean he may be using a genuine SSN from another person (fraudulent Carte Vitale do exist in France), and publishing it could harm this other perso,
As a security practitioner, I always tell people that sometimes the simplest precautions are often the best. Placing you hand over the Pin Pad just makes sense, so do it dumb dumb.
At one of the locations of one of the credit unions I belong to, the drive-up ATM has the Pin Pad mounted on a vertical surface that is located several inches to the right of the touch screen display and the card insertion slot. This makes it very difficult to somehow mount an undetected camera on the ATM to record the PIN being entered. However, there is a problem with this particular installation.
In order to be able to use your free hand to cover the hand that is entering your PIN, you would have to stop your vehicle lined up with the touch screen display and card slot, insert your card, drive your vehicle forward to line up with the Pin Pad, enter your PIN and then drive your vehicle backwards back to the touch screen to perform your transaction. If you aren’t worried about someone seeing you enter your PIN, you can reach the Pin Pad from the touch screen without moving your vehicle forward.
Needless to say, I don’t use that ATM. Oh, and next door to the drive-up ATM is a day care center parking lot. It is perfect cover for someone in a vehicle to observe someone entering their PIN on the Pin Pad.
Brian,
A minor correction. The EMV liability shift for ATMs in the US is October 2016 for MasterCard and 2017 for Visa. The reality is though since almost all ATMs in the U.S. accept both brands, the ATM owner would like do the upgrade to meet the 2016 deadline.
If I were in that line of work (skimming and scamming), I’d add a little generator powered by the card being pushed through. Then I wouldn’t have to change the batteries.
I disagree with the statement that most US banks dont use chip and pin. I have three different banks i work with and in the past year and a half, as they have replaced my ATM and credit cards, all have had the chip/pin security.
Otherwise, the article is another scary reminder that its still easier to steal than to make money legitimately. I propose we change laws in the US so that theft sentencing is based on every US dollar stolen, a day in prison is applied (Mexico could adjust it for their own currency or equate it ). On the flip side, for every dollar returned or confiscated, a half day is taken off the sentence. If you steal 100k, then it will take 200k to set you free. The conviction stays on your record even if you pay it off. Every time you are convicted of theft(separate instances/dates), the return rate lowers by 1%, so instead of 50%, you can only get back 49% the second time. 48% the third time.
Course after the money is returned, then the gains are for funding prisons…
Brent, you are sure they are chip/pin and not chip/sign, which is what I thought most US banks were going to? Your banks have asked you to setup (or sent you a separate) pin in order to be able to use your card as a credit card? If so, I’d like to know which banks because I’d like to get at least one chip/pin card. So far, I’ve only gotten a chip/sign card, and none of my regular merchants are ready to accept it as an EMV card yet.
mexican people are rapes, narcotrafic deals, theft and now this: gadget with hardware tricks.
We had two members who were on vacation in Mexico. They went to use the ATM outside of the Cafe where they were told that the ATM was out of service, and “helpfully” shown to the closest ATM.
Both had unauthorized ATM Withdrawals within two days.
Needless to say, be very leery of an ATM suggested by anyone you don’t know.
It depends on the city I would think. I live in Mexico and all the ATM’s I’ve seen not only have chip readers but some also have a plastic piece to hide the keyboard when you’re typing.
However, I would suggest anyone, not only in Mexico, because this happens everywhere, rather use ATMs who are inside banks and not the ones on malls or convenience stores. Usually ATMs in bank sites are harder to compromise and events are recorded.
The man was simply try to living make. Stop judging!
This happened to me in Honduras in March. This is live and well in Central America and Mexico
In Mexico the 100% of the ATM are EMV capable since is a standar; some are incapable of reading magnetic stripes (all cards issued here start having chips over a deacade ago) and since a magnetic stripe info is less valuable if the card do have EMV. skimming is not a big issue here as the article title may imply.
Obviosly is targeted at cards from Banks that fail at the most basic modern security meassures… and no one is from here. The incident happend at very specific target in mind but that could (and do ) happend anywhere in the world. Blame the Bank issuing crap cards in first place as culprits.
Dishonor employes are more of an issue that skimming but then again blame correcttly, never lose the sight of your card or do not complain of the consecuences
Interesting story on atm skimming. Regarding your story about the married dating website; I met a man who claimed he paid for accounts on a couple of these websites using stolen credit cards not only to avoid paying as much but also to avoid identification in case the site was hacked. I am curious, if the ‘Impact team’ publishes the credit card information for Madison accounts, and this guy is telling the truth and is not unique, is there an estimate of the number of people who are going to be blindslided with their stolen identities used on this site? He claimed he made it easy for people to show their credit cards used at the website had been stolen, though I doubt that will be very useful once the information is published.