Late last month, multiple news outlets reported that unspecified law enforcement officials had seized the servers for Leakedsource.com, perhaps the largest online collection of usernames and passwords leaked or stolen in some of the worst data breaches — including billions of credentials for accounts at top sites like LinkedIn and Myspace.
In a development that could turn out to be deeply ironic, it seems that the real-life identity of LeakedSource’s principal owner may have been exposed by many of the same stolen databases he’s been peddling.
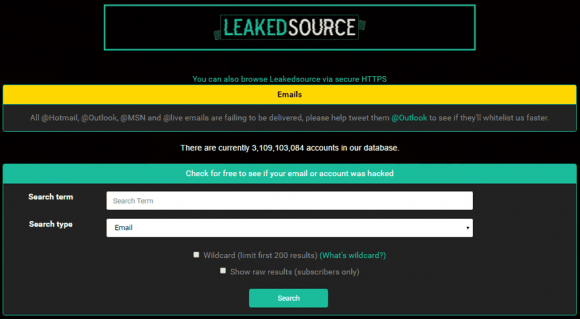
LeakedSource in October 2015 began selling access to passwords stolen in high-profile breaches. Enter any email address on the site’s search page and it would tell you if it had a password corresponding to that address. However, users had to select a payment plan before viewing any passwords.
LeakedSource was a curiosity to many, and for some journalists a potential source of news about new breaches. But unlike services such as BreachAlarm and HaveIBeenPwned.com — which force users to verify that they can access a given account or inbox before the site displays whether it has found a password associated with the account in question — LeakedSource did nothing to validate users. This fact, critics charged, showed that the proprietors of LeakedSource were purely interested in making money and helping others pillage accounts.
I also was curious about LeakedSource, but for a different reason. I wanted to chase down something I’d heard from multiple sources: That one of the administrators of LeakedSource also was the admin of abusewith[dot]us, a site unabashedly dedicated to helping people hack email and online gaming accounts.
Abusewith[dot]us began in September 2013 as a forum for learning and teaching how to hack accounts at Runescape, a massively multiplayer online role-playing game (MMORPG) set in a medieval fantasy realm where players battle for kingdoms and riches.

The currency with which Runescape players buy and sell weapons, potions and other in-game items are virtual gold coins, and many of Abusewith[dot]us’s early members traded in a handful of commodities: Phishing kits and exploits that could be used to steal Runescape usernames and passwords from fellow players; virtual gold plundered from hacked accounts; and databases from hacked forums and Web sites related to Runescape and other online games.
The administrator of Abusewith[dot]us is a hacker who uses the nickname “Xerx3s.” The avatar attached to Xerx3s’s account suggests the name is taken from Xerxes the Great, a Persian king who lived during the fifth century BC.
Xerx3s the hacker appears to be especially good at breaking into discussion forums and accounts dedicated to Runescape and online gaming. Xerx3s also is a major seller of Runescape gold — often sold to other players at steep discounts and presumably harvested from hacked accounts.
I didn’t start looking into who might be responsible for LeakedSource until July 2016, when I sought an interview by reaching out to the email listed on the site (leakedsourceonline@gmail.com). Soon after, I received a Jabber chat invite from the address “leakedsource@chatme.im.”
The entirety of that brief interview is archived here. I wanted to know whether the proprietors of the service believed they were doing anything wrong (we’ll explore more about the legal aspects of LeakedSource’s offerings later in this piece). Also, I wanted to learn whether the rumors of LeakedSource arising out of Abusewith[us] were true.
“After many of the big breaches of 2015, we noticed a common public trend…’Where can I search it to see if I was affected?’,” wrote the anonymous person hiding behind the leakedsource@chatme.im account. “And thus, the idea was born to fill that need, not rising out of anything. We are however going to terminate the interview as it does seem to be more of a witch hunt instead of journalism. Thank you for your time.”
Nearly two weeks after that chat with the LeakedSource administrator, I got a note from a source who keeps fairly close tabs on the major players in the English-speaking cybercrime underground. My source told me he’d recently chatted with Xerx3s using the Jabber address Xerx3s has long used prior to the creation of LeakedSource — xerx3s@chatme.im.
Xerx3s told my source in great detail about my conversation with the Leakedsource administrator, suggesting that either Xerx3s was the same person I spoke with in my brief interview with LeakedSource, or that the LeakedSource admin had shared a transcript of our chat with Xerx3s.
Although his username on Abusewith[dot]us was Xerx3s, many of Xerx3s’s closest associates on the forum referred to him as “Wade” in their forum postings. This is in reference to a pseudonym Xerx3s frequently used, “Jeremy Wade.”
![An associate of Xerx3s tells another abusewith[dot]us user that Xerx3s is the owner of LeakedSource. That comment was later deleted from the discussion thread pictured here.](https://krebsonsecurity.com/wp-content/uploads/2017/02/xerownsit-580x252.png)
An associate of Xerx3s tells another abusewith[dot]us user that Xerx3s is the owner of LeakedSource. That comment was later deleted from the discussion thread pictured here.
The “Jeremy Wade” pseudonym shows up in a number of hacked forum databases that were posted to both Abusewith[dot]us and LeakedSource, including several other sites related to hacking and password abuse.
For example, the user database stolen and leaked from the DDoS-for-hire service “panic-stresser[dot]xyz” shows that a PayPal account tied to the email address eadeh_andrew@yahoo.com paid $5 to cover a subscription for a user named “jeremywade;” The leaked Panicstresser database shows the Jeremywade account was tied to the email address xdavros@gmail.com, and that the account was created in July 2012.
The leaked Panicstresser database also showed that the first login for that Jeremywade account came from the Internet address 68.41.238.208, which is a dynamic Internet address assigned to residential customers of Comcast Communications in Michigan.
According to a large number of forum postings, it appears that whoever used the xdavros@gmail.com address also created several variations on that address, including alexdavros@gmail.com, davrosalex3@yahoo.com, davrosalex4@yahoo.com, as well as themarketsales@gmail.com.
The Gmail account xdavros@gmail.com was used to register at least four domain names almost six years ago in 2011. Two of those domains — daily-streaming.com and tiny-chats.com — were originally registered to a “Nick Davros” at 3757 Dunes Parkway, Muskegon, Mich. The other two were registered to a Nick or Alex Davros at 868 W. Hile Rd., Muskegon, Mich. All four domain registration records included the phone number +12313430295.
I took that 68.41.238.208 Internet address that the leaked Panicstresser database said was tied to the account xdavros@gmail.com and ran an Internet search on it. The address turned up in yet another compromised hacker forum database — this time in the leaked user database for sinister[dot]ly, ironically another site where users frequently post databases plundered from other sites and forums.
The leaked sinister[dot]ly forum database shows that a user by the name of “Jwade” who registered under the email address trpkisaiah@gmailcom first logged into the forum from the same Comcast Internet address tied to the xdavros@gmail.com account at Panicstresser.
I also checked that Michigan Comcast address with Farsight Security, a security firm which runs a paid service that tracks the historic linkages between Internet addresses and domain names. Farsight reported that between 2012 and 2014, the Internet address 68.41.238.208 was tied to no-ip.biz, popular “dynamic IP” service.
No-ip.biz and other dynamic IP address services are usually free services that allow users to have Web sites hosted on servers that frequently change their Internet addresses. This type of service is useful for people who want to host a Web site on a home-based Internet address that may change from time to time, because services like No-ip.biz can be used to easily map the domain name to the user’s new Internet address whenever it happens to change.
Unfortunately, these dynamic IP providers are extremely popular in the attacker community, because they allow bad guys to keep their malware and scam sites up even when researchers manage to track the attacking IP address and convince the ISP responsible for that address to disconnect the malefactor. In such cases, dynamic IP services allow the owner of the attacking domain to simply re-route the attack site to another Internet address that he controls.
Farsight reports that the address 68.41.238.208 maps back to three different dynamic IP domains, including “jwade69.no-ip.biz,” “wadewon.no-ip.biz,” and “jrat6969.zapto.org.” That first dynamic address — jwade69.no-ip.biz — was included among several hundred others in a list published by the Federal Bureau of Investigation as tied to the distribution of Blackshades, a popular malware strain that was used as a password-stealing trojan by hundreds of paying customers prior to May 2014.
XERX3S HACKED?
In January 2017, when news of the alleged raid on LeakedSource began circulating in the media, I began going through my notes and emails searching for key accounts known to be tied to Xerx3s and the administrator of Abusewith[dot]us.
Somehow, in the previous three months I’d managed to overlook an anonymous message I received in mid-September from a reader who claimed to have hacked the email account themarketsales@gmail.com, one of several addresses my research suggested was tied to Xerx3s.
The anonymous source didn’t say exactly how he hacked this account, but judging from the passwords tied to Xerx3s’s other known accounts that were included in the various forum database leaks listed above it may well have been because Xerx3s in some cases re-used the same password across multiple accounts.
My anonymous source shared almost a dozen screenshots of his access to themarketsales@gmail.com, which indicate the name attached to the account was “Alex Davros.” The screenshots also show this user received thousands of dollars in Paypal payments from Leakedsource.com over a fairly short period in 2015.
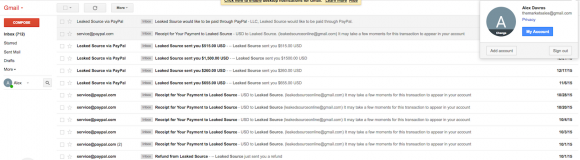
The screenshots also showed that themarketsales@gmail.com was tied to a PayPal account assigned to a Secured Gaming LLC. Recall that this is the same company name included in the Web site registration records back in 2011 for daily-streaming.com and tiny-chats.com.
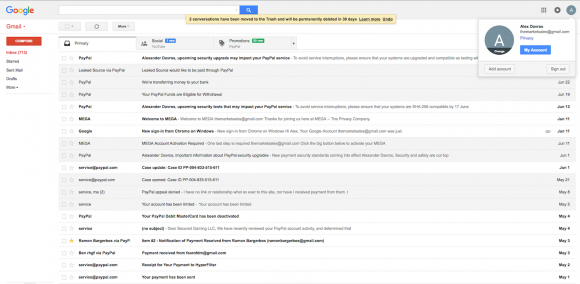
A screenshot shared with me in Sept. 2016 by an anonymous source who said he’d hacked the Gmail address “themarketsales@gmail.com”.
In addition, the screenshot above and others shared by my source indicate that the same Paypal account tied to themarketsales@gmail.com was habitually used to pay a monthly bill from Hyperfilter.com, a company that provides DDoS protection and hosting and which has long been the provider used by Abusewith[dot]us.
Finally, the anonymous hacker shared screenshots suggesting he had also hacked into the email account desiparker18@gmail.com, an account apparently connected to a young lady in Michigan named Desi Parker. The screenshots for Ms. Parker suggest her hacked Gmail account was tied to an Apple iTunes account billed to a MasterCard ending in 7055 and issued to an Alexander Davros at 868 W. Hile, Muskegon, Mich.
The screenshots show the desiparker18@gmail.com address is associated with an Instagram account for a woman by the same name from Muskegon, Mich. (note that the address given in the WHOIS records for Alex Davros’s daily-streaming.com and tiny-chats.com also was Muskegon, Mich).
Desi Parker’s Instagram lists her “spouse” as Alex Davros, and says her phone number is 231-343-0295. Recall that this is the same phone number included in the Alex Davros domain registration records for daily-streaming.com and tiny-chats.com. That phone number is currently not in service.
Desi Parker’s Facebook account indeed says she is currently in a relationship with Alexander Marcus Davros, and the page links to this Facebook account for Alex Davros.
Alex’s Facebook profile is fairly sparse (at least the public version of it), but there is a singular notation in his entire profile that stands out: Beneath the “Other Names” heading under the “Details about Alexander” tab, Alex lists “TheKing.” Parker’s Instagram account includes a photo of an illustration she made including her beau’s first name with a crown on top.
Interestingly, two email addresses connected to domains associated with the Jeremy Wade alias — matt96sk@yahoo.com and skythekiddy@yahoo.com — are tied to Facebook accounts for Michigan residents who both list Alex Davros among their Facebook friends.
Below is a rough mind map I created which attempts to show the connections between the various aliases, email addresses, phone numbers and Internet addresses mentioned above. At a minimum, they strongly indicate that Xerx3s is indeed an administrator of LeakedSource.
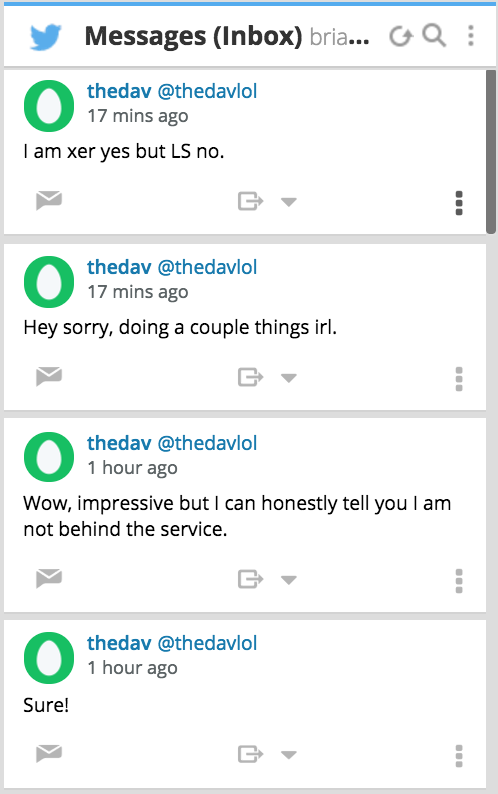 I managed to reach Davros through Twitter, and asked him to follow me so that we could exchange direct messages. Within maybe 60 seconds of my sending that tweet, Davros followed me on Twitter and politely requested via direct message that I remove my public Twitter messages asking him to follow me.
I managed to reach Davros through Twitter, and asked him to follow me so that we could exchange direct messages. Within maybe 60 seconds of my sending that tweet, Davros followed me on Twitter and politely requested via direct message that I remove my public Twitter messages asking him to follow me.
After I did as requested, Davros’s only response initially was, “Wow, impressive but I can honestly tell you I am not behind the service.” However, when pressed to be more specific, he admitted to being Xerx3s but claimed he had no involvement in LeakedSource.
“I am xer yes but LS no,” Davros said. He stopped answering my questions after that, saying he was busy “doing a couple things IRL.” IRL is Internet slang for “in real life.” Presumably these other things he was doing while I was firing off more questions had nothing to do with activities like deleting profiles or contacting an attorney.
Even if Davros is telling the truth, the preponderance of clues here and the myriad connections between them suggest that he at least has close ties to some of those who are involved in running LeakedSource.
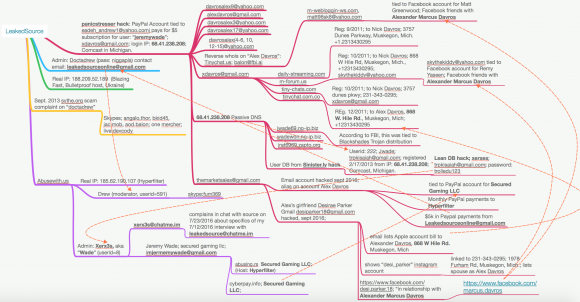
A “mind map” I created to illustrate the apparent relationships between various addresses and pseudonyms referenced in this story.
THE LEGALITY OF LEAKEDSOURCE
On the surface, the rationale that LeakedSource’s proprietors have used to justify their service may seem somewhat reasonable: The service merely catalogs information that is already stolen from companies and that has been leaked in some form online.
But legal experts I spoke with saw things differently, saying LeakedSource’s owners could face criminal charges if prosecutors could show LeakedSource intended for the passwords that are for sale on the site to be used in the furtherance of a crime.
Orin Kerr, director of the Cybersecurity Law Initiative at The George Washington University, said trafficking in passwords is clearly a crime under the Computer Fraud and Abuse Act (CFAA).
Specifically, Section A6 of the CFAA, which makes it a crime to “knowingly and with intent to defraud traffic in any password or similar information through which a computer may be accessed without authorization, if…such trafficking affects interstate or foreign commerce.”
“CFAA quite clearly punishes password trafficking,” Kerr said. “The statute says the [accused] must be trafficking in passwords knowingly and with intent to defraud, or trying to further unauthorized access.”
Judith Germano, a senior fellow at the Center on Law and Security at New York University’s School of Law, said LeakedSource might have a veneer of legitimacy if it made an effort to check whether users already have access to the accounts for which they’re seeking passwords.
“If they’re not properly verifying that when the user goes to the site to get passwords then I think that’s where their mask of credibility falls,” Germano said.
LeakedSource may be culpable also because at one point the site offered to crack hashed or encrypted passwords for a fee. In addition, it seems clear that the people who ran the service also advocated the use of stolen passwords for financial gain.





Real good article , very informative.
Wow Brian, As always, impressed by your ability to synthesize a list of disparate clues, and build a strong case. Keep doing what you do!
Amazing work. Thank you for keeping the Internet safe.
Stellar work as usual. Given the volume of evidence gathered here, is there any possibility that law enforcement can use this against the accused? I’d like to think that this work isn’t in vain.
Brian Krebs is the best. Keep going!
~Inspector Didi
Another nice bit of investigation, Brian.
I shudder to think of bad actors who might be using similar techniques for less altruistic purposes.
OpSec is indeed tough but vital.
Very nice bit of sleuthing!
This is ridiculous. There are legitimate security uses for users other than those who were compromised to acquire leaked passwords (or hashes).
What about pen testing firms who want to check if their client is reusing a password that has been compromised? Or what about security teams for businesses who want to check if their high value employees are reusing passwords that have been dumped online?
While I don’t doubt LeakedSource had some shadiness, proclaiming that *the* issue was lack of vetting of who was requesting the info is ridiculous and negatively impacts legitimate security uses of the data.
Ran into you site by accident a couple of months ago, cool articles (especially considering how long it must take to gather all the data).
Rock on!
1. The phone number had a seeming callerID of “Alex”.
2. The 6-digit prefix of the number vaguely (in the digital age) cross-references to Grant, MI, 20 miles east of Muskegon.
Nice article, Brian.
Thanks Brian for boldly researching and maintaining your own credibility along the way. Truth will only emerge as long as people like you continue to represent best interests of honest people.
More and more, our trusted sources of mainstream journalism are subverted by immoral financial interest, or things that become cloaked under edicts of ‘national security’.
I refer your work & website to anyone that will pay attention in my sphere of influence. All the best to you.
“our trusted sources of mainstream journalism”
There is no such thing.
Courage and integrity are in short supply. That’s one of the reasons why we consider Brian Krebs a national treasure.
Two questions.
1: What software do you use to make mind maps?
2: Does the IRS CID ever try to recruit you?
Follow the money. “screenshots also show this user received thousands of dollars in Paypal payments from Leakedsource.com”
The IRS Tax Fraud Hotline is 1-800-829-0433. Or download Form 3949-A. The IRS will have no trouble tracing the Paypal payments. You may be eligible for reward money.
Brian: spelling. See “mange”. Feel free to delete the comment.
Thanks for the article.
His place of residence is about a 5-10 minute drive from my home. I drive through that area regularly and am somewhat familiar with the high school that his banner picture seems to indicate he attended. I didn’t think I’d see my home area featured in a story like this – great work, Brian!
Regarding the phone number, if it’s a cell phone it doesn’t mean much these days other than the fact that he asked for a 231 area code, which encompasses most of Muskegon county. For instance, if you were to look up my cell number it would tell you that the number originates in a town about 45 minutes south of where I first obtained the number.
I am an inside source.
Xerx3s is innocent. He’s been elaborately framed by a collective of his three of his largest competitors for stealing RS GP on Abusewith.us, two users named “Haci” and “Brun0” (Brun0 AKA “saulaab”, Karl Gaffney from the UK irl), as well as the administrator of a former competitor site, “Toil” (aka @Megamansec kiddo named Joshua Rogers [same one who found an sqli for PTV and got arrested for reporting it] of Melbourne, who can be reached at +61-3-9822-5004).
I know this because I was the fourth member who was working with them while plotting this framing, logging skype and xmpp chats as I went.
If you want to get in touch me Brian, I can be reached at robertcalifornia@exploit.im, though I will exclusively be using OTR messaging and will not talk with you unless you do the same.
Fellow AWU member 😉
This is why i love the internet. these dank memes
I wonder who could be behind this post?
http://abusewith.us/showthread.php?tid=7601
“Some people here like me, then there’s Haci and Saulaab (Brun0)”
Hmm..
Seems legit!
Even if it is, I doubt the dude will be squeaky clean enough to survive a forensics team digging through his stuff.
Way to follow the breadcrumbs!
Always a pleasure to take in the results of your work.
Actually, if the leak is not considered sensitive by HaveIBeenPwned, anybody can ask if a given email was in a leak (rate-limited).
The major difference is that HaveIBeenPwned doesn’t store passwords nor hashes – it actually stores *only* email and in which leak(s) it was.
Alex Davros is also @dirtydav23 on Instagram
Really nice Brian.
I can’t help but notice, many of the miscreants out there started off by cheating in video games, and messing with other players.
Just not good people from the start.
missxrunescape@gmail.com is another email used , used same password and same ip range (68.41.238.208)
Some other alias’s used
Peach imjeremywade@gmail.com 68.41.238.208
jamesjay missxrunescape@gmail.com trolledu123 68.41.238.208
Wade imjeremywade@gmail.com bigreds23 68.41.238.208
Peach imjeremywade@gmail.com 68.41.238.208
Jwade imjeremywade@gmail.com bangbang
HlTS imjeremywade@gmail.com soccerman 68.41.59.109
JeremyWade imjeremywade@gmail.com trolledu123
alex imjeremywade@gmail.com baseball11 68.9.215.208
Loki v2 xdavros@gmail.com buck12 199.59.162.151
gameaddict xdavros@gmail.com soccerman 24.11.86.183
PartyPopper xdavros@gmail.com soccerman 98.250.82.137
alex xdavros@gmail.com soccerdude101 24.11.217.137
xdavros@gmail.com socc3rman
napalms missxrunescape@gmail.com 174.48.246.10
The Loki missxrunescape@gmail.com buck12 199.59.162.151
jamesjay missxrunescape@gmail.com trolledu123 68.41.238.208
Le loki missxrunescape@gmail.com 50.124.245.23
Le loki missxrunescape@gmail.com trolledu123 68.41.238.208
sparc mac skythekiddy@yahoo.com74.103.246.227
Its all organised by illuminati illuminati is behind all the organised crime and also cybetcrime.
People in cardimg business use the same symbols
Numbers and even numbers like masons do it.
Rember guys illuminati favorite color is blue and yellow.
Moslty blue color.
People who start fighing against the system thei are the ones
Who end up working for the system.
Like the same force who you fight against is the same force they help. Welcome to the roman empire hermes zeus and all nice
Accient mytologia guys. Lets add Atticus and we have full complect lol.
Anyways if i say this is anyone even can undestood??
I guess you have no idea what i saying here.
Wow now u guys think its Utopia..
have I been pwned does not seem to require verification for me. I just checked the emails of my family members without issue.
Yes it’s wrong in the article.
haveibeenpwned.com doesn’t require a verification. It only requires a verification if you want to check for sensitive breaches (like Ashley Madison).
Btw I don’t like that everybody can check my emailadresses there. At least you can opt-out on this.
Awesome, I didn’t know you could opt out. Just did that.
Good idea. And even if you opt-out of public search, if you verify your e-mail you still can check these accounts.
Nice, more’s coming. Getting popcorn. Great work Brian.
nice work, Brian!
Thank you for all you do, Brian. I’ve learned a lot from you. You have set a new, high bar for investigative reporting.
have i been pwned is useful, but i’d particularly like to know if the hashes found in these dumps have been ‘easily’ cracked, or had positive hits across known rainbow tables, and if so then listing the password (for verified, or even paid customers). This would be the ultimate
As this is the expected MO of hackers who use these dumps. They’ll put the effort into finding the passwords if they can automate the process using the tools available; the same tools ‘haveibeenpwned’ uses for publishing the leaks. So why not go the equal length and provide a reverse of?
Brian you are awesome! Keep doing what you do! 🙂