We don’t yet know the root cause(s) that forced Marriott this week to disclose a four-year-long breach involving the personal and financial information of 500 million guests of its Starwood hotel properties. But anytime we see such a colossal intrusion go undetected for so long, the ultimate cause is usually a failure to adopt the most important principle in cybersecurity defense that applies to both corporations and consumers: Assume you are compromised.
TO COMPANIES
For companies, this principle means accepting the notion that it is no longer possible to keep the bad guys out of your networks entirely. This doesn’t mean abandoning all tenets of traditional defense, such as quickly applying software patches and using technologies to block or at least detect malware infections.
It means accepting that despite how many resources you expend trying to keep malware and miscreants out, all of this can be undone in a flash when users click on malicious links or fall for phishing attacks. Or a previously unknown security flaw gets exploited before it can be patched. Or any one of a myriad other ways attackers can win just by being right once, when defenders need to be right 100 percent of the time.
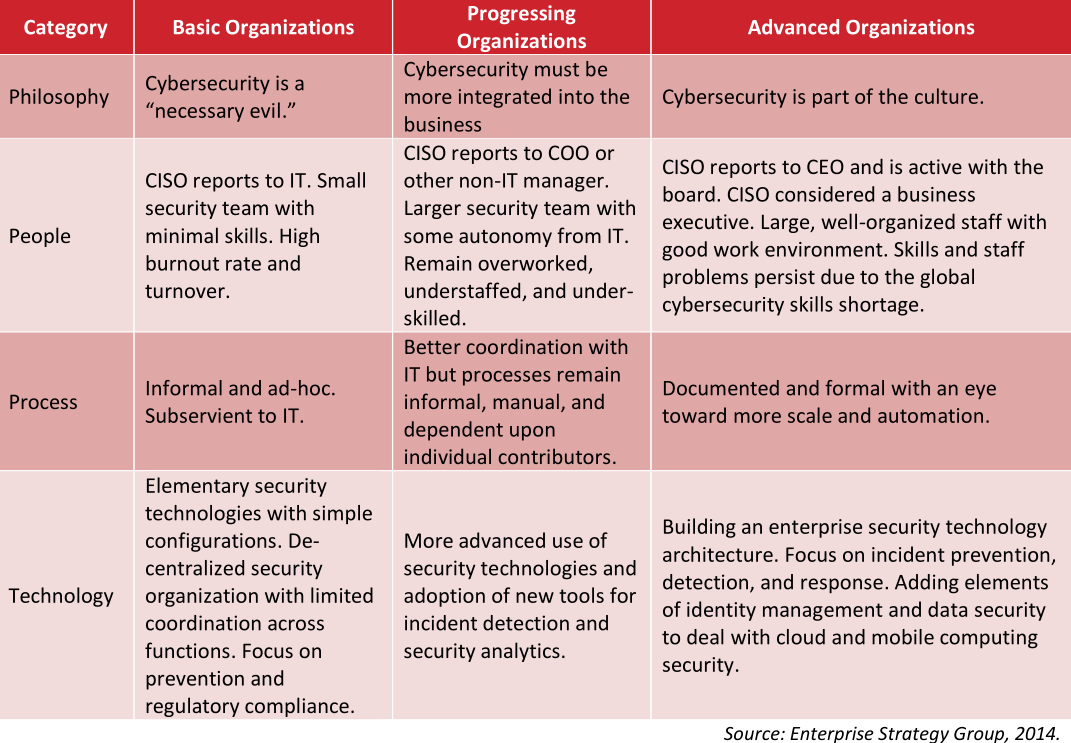
The companies run by leaders and corporate board members with advanced security maturity are investing in ways to attract and retain more cybersecurity talent, and arranging those defenders in a posture that assumes the bad guys will get in.
This involves not only focusing on breach prevention, but at least equally on intrusion detection and response. It starts with the assumption that failing to respond quickly when an adversary gains an initial foothold is like allowing a tiny cancer cell to metastasize into a much bigger illness that — left undetected for days, months or years — can cost the entire organism dearly.
The companies with the most clueful leaders are paying threat hunters to look for signs of new intrusions. They’re reshuffling the organizational chart so that people in charge of security report to the board, the CEO, and/or chief risk officer — anyone but the Chief Technology Officer.
They’re constantly testing their own networks and employees for weaknesses, and regularly drilling their breach response preparedness (much like a fire drill). And, apropos of the Marriott breach, they are finding creative ways to cut down on the volume of sensitive data that they need to store and protect.
TO INDIVIDUALS
Likewise for individuals, it pays to accept two unfortunate and harsh realities:
Reality #1: Bad guys already have access to personal data points that you may believe should be secret but which nevertheless aren’t, including your credit card information, Social Security number, mother’s maiden name, date of birth, address, previous addresses, phone number, and yes — even your credit file.
Reality #2: Any data point you share with a company will in all likelihood eventually be hacked, lost, leaked, stolen or sold — usually through no fault of your own. And if you’re an American, it means (at least for the time being) your recourse to do anything about that when it does happen is limited or nil.
Marriott is offering affected consumers a year’s worth of service from a company owned by security firm Kroll that advertises the ability to scour cybercrime underground markets for your data. Should you take them up on this offer? It probably can’t hurt as long as you’re not expecting it to prevent some kind of bad outcome. But once you’ve accepted Realities #1 and #2 above it becomes clear there is nothing such services could tell you that you don’t already know.
Once you’ve owned both of these realities, you realize that expecting another company to safeguard your security is a fool’s errand, and that it makes far more sense to focus instead on doing everything you can to proactively prevent identity thieves, malicious hackers or other ne’er-do-wells from abusing access to said data.
This includes assuming that any passwords you use at one site will eventually get hacked and leaked or sold online (see Reality #2), and that as a result it is an extremely bad idea to re-use passwords across multiple Web sites. For example, if you used your Starwood password anywhere else, that other account you used it at is now at a much higher risk of getting compromised.
By the way, if you are the type of person who likes to re-use passwords, then you definitely need to be using a password manager, which helps you pick and remember strong passwords/passphrases and essentially lets you use the same strong master password/passphrase across all Web sites.
The “assume you’re compromised” philosophy involves freezing your credit files with the major credit bureaus, and regularly ordering free copies of your credit file from annualcreditreport.com to make sure nobody is monkeying with your credit (except you).
It means planting your flag at various online services before fraudsters do it for you, such as at the Social Security Administration, U.S. Postal Service, Internal Revenue Service, your mobile provider, and your Internet service provider (ISP).
Assuming compromise means placing very little trust or confidence in anything that comes to you via email. In the context of this Marriott/Starwood breach, for example, consider all the data points that attackers may now have to make a phishing or malware attack more likely to be successful: Your Starwood account number, your address, phone number, email address, passport number, dates and times of your reservations, and credit card information.
How hard would it be for someone to craft an email that warns of a problem with a recent reservation or with your Starwood account, urging you to click a booby trapped link or attachment to learn more? Now imagine that such targeted emails can come from any brand with whom you’ve done business (for a refresher, see Reality #2 above).
Assuming you’re compromised means beefing up your passwords by adopting more robust multi-factor authentication — and perhaps even transitioning away from SMS/text messages for multifactor toward more secure app- or key-based options.
TOUGH TRADE-OFFS
If the advice above sounds inconvenient, unfair and expensive for all involved, congratulations: You are well on your way to internalizing Realities #1 and #2. For better or worse, being a savvy consumer means constantly having to make difficult trade-offs between security, privacy, and convenience.
Oh, and you generally only get to pick two out of three of these qualities. Same goes for the trio of high-speed, high-quality, and low-cost. Or good, fast, and cheap. Again, pick two. You get the idea.
Unfortunately, these transactions become even more lopsided and difficult to weigh when one party to them always selects the same trade-off (e.g., fast, low-cost, and convenient). Right now, it sure seems like there aren’t a lot of consequences when huge companies that ought to know better screw up massively on security, leaving consumers and their paying customers to clean up the mess.
I don’t know how many more big-time privacy and security debacles we need to convince our nation’s leaders that perhaps we should enshrine in law some basic standards of care for how companies handle and secure consumer data, and what rights and expectations consumers should have when companies fail to meet those standards. Because it’s clear that unless and until this happens, some subset of businesses out there will continue to make the most expedient and short-sighted trade-offs available to them, regardless of the impact to their customers and the public at large.
On this point, as with many others related to Internet security and privacy, I found it hard to argue with the opinion of my home state Senator Mark Warner (D-Va.), who observed:
“It seems like every other day we learn about a new mega-breach affecting the personal data of millions of Americans. Rather than accepting this trend as the new normal, this latest incident should strengthen Congress’ resolve. We must pass laws that require data minimization, ensuring companies do not keep sensitive data that they no longer need. And it is past time we enact data security laws that ensure companies account for security costs rather than making their consumers shoulder the burden and harms resulting from these lapses.”




Until there is a real bite behind the teeth of a law, no company is going to take any of this seriously.
I agree entirely, but civil penalties are what is required. With the scale of these breaches, a liquidated damages penalty of $10,000 per person whose file is breached would get the attention of the empty suits who run these companies.
Right now, there is no reason to do anything because they are not the ones that get hurt, their customers do.
Why in the &(**(&( do they allow heating contractors, etc, access to the financial side of their business. One net for this sort of stuff and another entirely for financial data should be the minimum requirement!
I have to politely disagree with you. Companies do pay a lot of money in fines, penalties and reputational damage. A Level 1 merchant such as Marriott has to undergo an annual PCI assessment. They must hire an external QSA that has to certify and scrutinize their compliance . This in itself is expensive. Marriott will need to increase their security posture and will likely lose some of their transactional discount with their acquiring bank. For instance if they pay 2 cents per transaction, it could increase to 4 cents. While a couple of cents sounds like nothing, when you do millions of transactions, it can become quite hefty.
It is easy to be upset with the company, but you need to understand that for every stride a company makes with enhancing their security posture, it just takes one malicious hacker to do severe damage.
If you want to see some numbers around what a breach costs, google “security Metrics, cost of a breach”.
While civil penalties will do more to encourage companies to take Cyber Security seriously, that’s not entirely the issue.
The issue is, and remains to be, draconian security practices, that assume you can keep the bad guys “out.” In reality, you cannot. You must assume your user network is compromised all the time. Network segregation and detection are key components to any cyber security program. The time it takes many cyber criminals to exfiltrate data after initial compromise is actually growing for non-targetted attacks. That means, you can be compromised, detect the comprimise, and react before criminals even exfiltrate data.
However, if they’re in your network for weeks, months, or even years, the likelihood of your data not being compromised quickly approaches nil.
“Why in the &(**(&( do they allow heating contractors, etc, access to the financial side of their business.”
If youre referring to the Target breach, they didnt give their contractor access to financial data or systems, not in any way. Their contractor had access to their network via a secure login portal, with very limited access. The contractor got phished, a keylogger was installed and the hackers stole their login credentials for Target vendor portal. Once on the vendor portal with normal, low level user access, they were able to use a privilege escalation vulnerability to gain admin access to the vendor portal and the server it resided on. From there they were able to pivot and steal more credentials until finally they found the POS system. IIRC they then reverse engineered the POS system, built their own custom firmware, loaded it on to the POS machines and began skimming customer payment card data. It was a pretty sophisticated hack, not some script kiddie who found a backdoor in the vendor portal which then immediately gave them access to financial systems. It took months to pull off.
Until international law provides penalties for such crimes, nothing will happen to cyber criminals that are based in and protected by third world countries. They get away with it without their governments trying to stop them. The country you live in is not likely where the criminals are based. So, no bite is there to be had.
Snap! You mean the GDPR.
On the basis that confession early and often is good for the soul, the most interesting question of all is: precisely *when* did they first learn that they *might* be in a data breach scenario? Because that is the key question mitigating or aggravating fines and class action awards…
(My own commercial and legal work seems increasing shifting toward M&A GDPR risk… – which is almost completely distinct from data breach risk)
When I need to connect to some public wifi, and they ask me to provide any data, I use fake emails. If possible I don’t provide any real information, and I am using nordvpn on top. It does not change my user experience and I am not getting any random newsletters or ads.
Re:
“Until there is a real bite behind the teeth of a law, no company is going to take any of this seriously.”
DING DING DING! WINNING COMMENT!
Thumbs up / agree!
Hire and invest in security professionals in your organization OR PAY BIG FINES and that should include JAIL TIME for executives caught being negligent.
THESE ARE THINGS THAT COMPANIES UNDERSTAND PERIOD.
“they are finding creative ways to cut down on the volume of sensitive data that they need to store and protect”.
This point doesn’t seem to be emphasized enough. Whenever I read about a large breach, I wonder *why* the records for million accounts are even in a location or form that could be exploited from the public internet?
The short answer is “because there’s virtually nothing useful that isn’t at least tangentially reachable from the public internet”.
The only exceptions are:
1. milnet (various countries)
2. rare scientific laboratories (which are still accessible via sneakernet, c.f. stuxnet)
3. standalone computers used by old-fashioned accountants
4. typewriters used by old-fashioned authors
So, once you’re past the “why is it reachable” question, we should focus on the “why is it held” question.
Sometimes the answer is “to make it more convenient for the customer”. When you order an item from a company, do you like filling in all the fields?* If you answer “yes”, you’re lying. One of the many problem with filling in fields is that it increases the chance of error. Each time you, I, or anyone else has to fill in a field/form, we increase the chance of making a mistake. If I ask someone to bill me to the same address where I was successfully billed before, the odds are better that it will work again than if I enter it again by hand. Similarly, if we ask to have something delivered to the same address where we’ve successfully received an item before, the odds are better that it’ll arrive at the right place**.
Oh, you use a form filler (Chrome, Firefox, Edge, Safari) so you don’t care about entering information in repeatedly? Well, some vendors are annoying (meet IBM*) and prevent form filling, forcing us all to enter things by hand. Plus, one reasonably good hint that a site is legitimate is that it has all the information we’ve previously entered. A phishing site in general shouldn’t have all of our account information***.
That said, the real reason anyone keeps information is to build profiles so they can monetize their customers. If I buy the same product each visit, and they learn that I can be tempted to buy another product, being able to remember that and use it to entice me to buy that second product is valuable. This is “Know Your Customer”, and any business that doesn’t do this doesn’t really deserve to remain in business.
Can the data be encrypted so that hackers can’t use it? Not practically. Data could be encrypted so that it’s only accessible when you log in (a salt + your password to encrypt a per user encryption key), but that’s not actually protection, if the database is stolen, then an offline attack could be mounted against each password (it would have been mounted anyway, because the hackers want your passwords to attack your other accounts elsewhere). At best, that buys you time. But, a vendor wants to be able to reach out to you without you logging in, e.g. we have account representatives who call us to ask questions, if they can’t access the data on us (see KYC), then they can’t do their job. And what happens when someone “forgets their password”? The answer would be that all the data would be useless and would have to be deleted. Sure, companies could put in backup systems, but those would just weaken the security, and hackers would target that instead — security is *only* as good as the weakest link (see social engineering).
* There’s this one form that I get to fill in quarterly for IBM which has around 20 mandatory fields — it has iirc 2 optional fields: fax number and “address 2”.
** There’s someone up my street who either has bad handwriting or corrupts digits, I keep getting important snail mail for them from various entities.
*** Yes, if a hacker has breached the real site, they will have all the information, or if they’re performing a clever MITM attack, but on average, to date, they won’t, and for the time being, there’s still some value in this protection.
I think your opening sentence: “We don’t yet know the root cause(s) that forced Marriott this week to disclose a four-year-long breach involving the personal and financial information of 500 million guests of its Starwood hotel properties.” is telling.
The root cause of the security breach is one thing. There’s lots of good material on this on your site and others.
The root cause of why Marriott had to finally disclose the breach is probably because they understood that the breach was finally going to be made public in a BIG way. Corps aren’t pro-active at trying to heal minor (in their eyes) problems. They only become motivated when the shareholders, and less so regulators, might impact their executive payments.
Root solution: make the shareholders and executive-level decision makers accountable. Keep 10-30% in escrow for 3-5 years until their performance on their watch has been impeccable.
Oh, wait. I was in a day dream. Not living in the US.
It just never stops. I’ve been recommending for almost 10 years now that all these data sellers need to be indexed and licensed. In other words, get a license with stipulations that the type of data and the markets sold to are updated as they change so we know who they are? To me that makes sense if we are going to do any lawmaking is to first identify the “who”. There are thousands of companies all of us have never heard of that do the same thing, and use APIs t connect to other data bases, as an example, until the breach, nobody ever heard of Exactis either.
At least with licensing the players get identified and fines could be levied easy enough and licenses could be suspended with those found out of compliance. Of course law making goes beyond this step one but heck how in the world do we at least know who’s tossing out all the One Trick Algos out there? The hackers know much better than we do on who has the data outside the obvious big guns.
I’ll just keep mentioning it I guess and maybe one day it might hit the right area to get some attention. I agree, there’s absolutely no teeth in any type of regulation here. Jaron Lanier recently said that companies have to trick us in order to get our data that they want as well, and they do.
http://ducknetweb.blogspot.com/2017/04/one-trick-algo-world-needs-to-be.html
We should at least have a system that requires licensing for this as shoot my hair dresser has to get a license and she represents far less risk than this data stealing game. Everybody has an index of who all the hair dressers are practicing in this country:)
Most people don’t care about these breaches until their personal information is stolen or it cost them financially.
Then they panic because they didn’t take the necessary steps to start with when it comes to their personal information security
Some people do not care even if a breach involves them.
i have heard “I do not have to pay the false charges, so why should I be careful?”
The answer should be “because these incompetent data-brokers can’t keep their data clean, they will have incorrect information, and one day someone will be breached with incorrect, but embarrassing information seemingly about you”. A fictitious example occurred in The Net (TV Series) [1], but Brian has lots of coverage of examples for credit reports and there are plenty of people who can speak to cases where their email address was added w/o authorization to embarrassing systems.
i.e. it isn’t just that harmless truthful information about you will be leaked.
The other classic example is Target’s baby prediction [2] (you can search for the Forbes article if you aren’t an NYT subscriber).
There are dozens of examples of privacy breaches where infections are disclosed [3]. In theory, some of those diagnoses/analyses could be false positives, and one day your friend could be in that category.
Protecting data is important. And no one does a particularly good job at it.
[1] https://www.imdb.com/title/tt0658901/plotsummary?ref_=tt_ov_pl
[2] https://www.nytimes.com/2012/02/19/magazine/shopping-habits.html?pagewanted=9&_r=1&hp
[3] https://www.npr.org/sections/health-shots/2018/01/17/572312972/aetna-agrees-to-pay-17-million-in-hiv-privacy-breach
If corporations want to be people then the death penalty for such massive screw ups should be an option. Make it so anytime they lose peoples information then they are responsible for fixing any problems relating to that screw up for the life of the person. That would bankrupt most corporations.
I’m not opposed to a corporate death penalty, but it has to be a toxic tainting corporate death penalty. It has to prevent all board members from being able to sit on boards for life. It has to impact major investors/shareholders. It has to taint through shell corporations. It has to impact affiliated lenders (DB and Volvo should both have received this penalty a long time ago, and should have been eligible a number of times).
Otherwise, they’ll dice their way around the problem.
The dicing can be seen in Australia’s *twelve* rounds of trying to protect its lottery from a guy who bought all possible combinations when the jackpot made it a financially viable proposition. Afterwards, he did the same thing in Virginia [1].
From Planet Money[2]’s report on how that worked:
«… They changed the laws. First, they passed a law that said no one person can buy every combination of lottery tickets (laughter).
… It’s just a, literally, do not do that again law. And so then he broke it up into fifty different people who each bought one-fiftieth of the numbers. And so he keeps winning, and eventually they make enough sufficient laws that prevent him from doing it again.»
We already see criminal enterprises that when caught, simply close their business name and reopen with another. One of the private military contractors did that, as did Cambridge Analytics. So, it really isn’t sufficient to have a corporate death penalty, it has to be tainting and has to be able to survive shell corporations/pass-through’s/minority holders.
[1] https://www.nytimes.com/1992/02/25/us/group-invests-5-million-to-hedge-bets-in-lottery.html
[2] https://www.npr.org/templates/transcript/transcript.php?storyId=462982983
I’m misunderstanding, Is the lottery a government sponsored illegal enterprise, or is taking advantage of it an illegal enterprise?
There is another way to approach maintenance of the integrity of data that is used by internet actors: design a database that is controlled by the individual where they can hand out keys to access on a one-time limited basis.
Thus instead of a database keeping reference numbers of passports, social security, addresses, and other unique identifiers for a single person, it would, say, keep a one-time receipt number for accessing whichever of those items it used to get its business with that individual done at that particular transaction. The certificate will again become a very important number, and I’m really pleased about the takeup of Let’s Encrypt as a precursor to taking back control of security.
The Solid startup with Berners-Lee riding along initially
https://solid.inrupt.com/
is a way for many web users to manage access to their own data.
One would still run with Krebs’ propositions 1 and 2, but for a person who’d like to seize back access control, the Solid idea appeals; anyone wanting access to any vital data would have to ask for the keys from me. Those of us with the will to learn server log maintenance can run with their own Pod. Those without the time or ability can go for a Pod service provider.
Those without the wherewithal to run a Pod at all could at least be informed of the possibility as a way for keepers of databases to sort of vouchsafe their own integrity of approach. A person can dream, no?
Right now, many sites accept personal credentials held by Ggle and Fcebk.
I’d rather run my own Pod on my own server – or at least hire a Pod from a company that runs open source software that can in theory be much better overseen than any of those private firms who often have a distant relationship with the truth.
How to get Solid made acceptable in govt and business?
Nothing’s done without some sweat. I’m playing around with my own Pod service and will be corresponding with my local member of parliament on the whole topic of leaving data on large unaccountable services – including government ones.
You have to make a start somewhere and I don’t believe that regulatory carrots and sticks will have any traction any sooner than a complete rethink of the kind that the Solid idea points to.
TL;DR
As of June 2013, a Congressional report found there were over 50 statutes relevant to cybersecurity compliance.
Here’s hoping that in another 5 years the conversation has actually changed somewhat
Underscores the need for rigorous Security due diligence in an acquisition. Marriott never saw it coming.
All due respect to Sen. Warren, “data minimization” and “cost remuneration” aren’t enough. What we really need is legislation that expands on the controls requirements under SOX 404, requiring all firms operating in the US or having access to personal data of US persons (not just public companies) to collect and report in-depth cyber risk controls and incident information on the same cadence as earnings. The current SEC guidance excludes non-public firms and, frankly, doesn’t do nearly enough to encourage or mandate accurate and complete reporting of the true cyber risk posture of enterprises – certainly not sufficient for making either investment or consumer decisions.
There’s a reason Target stock bounced back and consumers never abandoned the brand – it’s the lack of actual understanding of cyber risk impact by the market and marketplace. And why is that? Simple: Moral hazard and economics.
Moral hazard, as in the offloading of breach risk from companies to consumers or from banks to the federal government. Economics, as in the failure of the consumer to understand that the near-term indemnification of their immediate loss results in higher costs being passed onto them down the line. We tend to focus on the near-term risk at the exclusion of the long-term effects. Thus, having a fraudulent charge reversed by the bank is all an individual consumer cares about. It’s not catastrophic enough, and the drip-drip-drip of added costs is nearly imperceptible.
The tragedy of the cyber commons is the name of this game.
Although regulation is among my least favorite strategies, at some point the collective harm to “the commons” has to be addressed – or we need to accept our new “assured breach” reality as the cost of living in the digital world, the price of convenience if you will.
Either way, the choice should be made. Avoiding the decision, unfortunately, also constitutes a decision.
Im surprised… Is people still work with carding??
I done catding before too but now i think there is not money in anymore the cards security is too tough.
But now i do bitcoin business and its much more profitable and good business and no risk.
As many old carders have started bitcoin investment business
A simple law: Each organization that looses PII, PCI or HIPAA data should indemnify each victim at a rate of $1 per day from the beginning of the breach until it has been fixed and the victims notified.
~500 million victims over 1200 days at $1 per day would make a serious cybersecurity program look like a good investment or provide a lot of people with a nice holiday gift.
No, I don’t believe we will ever see a law like that.
In an IT career that stated as a systems analyst in the mid-1970s and formally ended 30 plus years later at the IT director/VP level, one thing was always a constant. Top management made it abundantly clear that they deeply resented the need to spend the company’s money on staff, hardware, and software for the IT dept. It was always a struggle to convince the “powers that be” that a request was essential, and the larger the sum the greater the struggle. Perhaps the old attitudes have changed now that there is almost total dependency on technology to run just about any business today. However, even though a completely new and younger set of senior managers, for the most part, is in control today there is still resentment, push back and struggle when it comes to approving expenditures for cyber security defense. In the “old days” management threw ROI requirements that were frequently unrealistic at IT leaders in an effort to hold down “un-necessary” expenditures. They say things change but remain the same, (whoever they actually are). Today the push back seems to be focused on controlling expenses related to cyber security measures by a generation of corporate whores who really don’t give a fiddlers damn about the security of customer data.
This incident is due to a flaw in the acquisition strategy. The desired end result is to get the acquired company on Marriott systems and decommission as much of the legacy IT infrastructure in the acquired company as possible. During this time, there is minimal connectivity between the two, and the legacy IT infrastructure at Starwood is not under the scope of management at Marriott, it continues as it were, with the pre-existing team (Accenture) managing the infrastructure. (A separate Accenture team also now manages Marriott IT infrastructure as of May this year). The risk created is it takes a really long time to complete this transition (many years), and during this time the legacy IT infrastructure in the acquired company is a ticking time bomb.
It should not be a surprise that the teams managing the legacy IT infrastructure are in custodian mode. There was also a significant amount of neglect due to Starwood was shopping itself around for a while and the investments in IT were minimal.
This isn’t exclusive to Marriott, although it is an extreme case due to the size, scope and time required to complete the acquisition. I was talking to someone at another company, and they have the same problem. As soon as an acquisition is announced, the acquired company is targeted by threat actors. It’s an easy foothold to achieve.
C-Suits only care about one thing: profit margin. I would like to see a combination of something like the GDPR and Sarbanes-Oxley to make the C-Suits more personally liable. It has always irked me when a company goes through financial woes (bankruptcy, lay-offs, loss of 401K/pensions, etc…) but the C-Suits and board all still get their money after running the company into the ground with bad decisions.
It would help companies didn’t keep asking for the same security responses, such as mother’s maiden name. I understand why: the customer knows the response off the cuff. But the security is risible. Of course the mother’s maiden name can be any alpha sequence when submitting it in the first place, but unfortunately a lot of people think the response needs to be the truthful one.
I worke it for a company with ~150 employees. security was always treated like it was a hindrance to profit. we got aquired by a forturn 300 company and things changes. I spent most of this year patching and complying with the security scans. then they replaced all of our netowork with Cisco so they could centrally manage it. we had to move our web server into the DMZ.
we went for security is nice to have to security is required and we will audit you .
I like the change.
This is why I believe all Privacy Shield Framework should be withdrawn from by Europe.
And we should _force_ US companies either to run separate business in Europe within European legislation, or work with limited access to information.
With a U.S. population of 325 million as of 2017
( internet search ), it would appear that we are all pretty much exposed already. I wish all internet sites utilized two-factor authentication such as Yubikey, but most don’t. I’ve followed advise from Brian as to cell phone verification techniques by utilizing a Google Voice account as discussed in https://krebsonsecurity.com/tag/google-voice/
Everyday dealing with banks, insurance, medical etc. I’m asked for at least the last 4 of SSN, if not the complete number. In addition many are requiring date of birth, mothers maiden name, phone and address. Even if there were no data breaches I feel exposed already.
Maybe someday we will be able to utilize DNA for identification and a usb device can confirm who you are by a simple touch. Even DNA could be faked, but would be harder.
+1
I signed up for the monitoring service (all you need is an email address, there’s no authentication process).
Kroll solicits additional PII like birthdate, SSN, mailing address, phone, credit card number, passport, but this is all optional. I note that the Kroll site does not offer 2FA options, it is only password protected. I also signed up my minor son. The email address you provide receives a confirmation message (full text at the end of this message), but no action is needed to confirm the account or email address. All this seems sloppy for a data security company, although they assure users that the data you provide will be encrypted.
Their privacy policy indicates that the information you provide can be (will be) provided to third parties and used for things including marketing (“In order for us to provide you with our identity monitoring, consultation, and restoration services, Kroll and/or its agents may share your personal information with its affiliated companies, with third party service providers retained by Kroll to provide services on its behalf (such as data hosting, marketing, analytics, identity monitoring, and customer service) or with others, such as credit bureaus or institutions with which you have a relationship (for instance, in order to provide you with your credit reporting history, or to discuss an issue you have with your account) or as required by law, legal process, and/or regulation.”)
Full text of email received after signing up:
Welcome to Kroll’s Web Watcher Monitoring Service! Let’s get started.
Log in to your account now to explore Kroll’s Web Watcher Monitoring Service. Here’s what to expect:
Complete your account by adding your identity information to be monitored.
We’ll notify you by email if we find a match to your monitored information.
Review the details of any notifications you receive in your secure portal.
If you have any questions, please contact our Support Team by email at incidentsupport@kroll.com.
Sincerely,
Kroll’s Web Watcher Monitoring Service
Regret: You outlined the reasons I did not enroll with Kroll. Plus their terms require you to release them from liability for their wrongs and require you to pay them for any costs that can be traced to your computer somehow. That plus their having complete freedom to use your identity information for any purposes including selling it to a 3rd party was way too much to stomach. But it’s “Free”, right? Then I remembered, when it’s free, you are the product.
I see everyone wants a law to punish the victim. No mention of making laws more stringent on hackers. Imagine getting mugged and then paying a fine or getting arrested because you walked into a dangerous neighborhood.
Mark,
Let’s use email as an example:
You’ve hit on an aspect that is very touchy for the vast majority of people in the United States.
For example: Yubikey (FIDO) 2FA. It’s free. It’s no longer owning a moderately secure email account. It is “highly” secure email accounts.
But people, users of email, do not want to hear this. Yubi—- what they say? FIDO is a dog, yes??
Then there is the other side of the equation, which is: how is, for example, something like Gmail+Yubikey so much more wildly secure than our most sensitive financial & health info held at the vast majority of institutions in the USA??
The vast gulf between these two islands is what the U.S. is today. Bewildering is an understatement. Inexcusable is more accurate. A recipe for disaster. Something we are seeing more and more every day.
When others talk about fines & punishment, for either individuals and/or corporations who are struggling in this vacuum, they are missing the forest for the trees.
The topic has shifted to ‘major’ societal behavior changes with respect to this digital century. Until that happens, we all will keep whistling past the graveyards of breaches that get more and more massive as times goes on.
This is war that will never end. And we all have to start realizing and accepting this.
Just my 2c…..
(not a real email address, btw)
What happens if the Yubikey gets lost or stolen?
I don’t think this is correct.
All 50 states and the Federal Government already have laws that make hacking illegal. Aside from the difficulty in investigating these crimes, some (many?) perpetrators are hacking from outside the U.S. making it expensive or futile to persue.
I also didn’t see comments from people who want to punish “the victim” (who are the people whose data may be misused). Commenters are rightly upset that the “target” of these type of hacks often have few consequences for poor data security practices and are discussing alternatives to that problem.
I once saw a Microsoft General Counsel tell a parliamentary committee that the solution to their software being hacked wasn’t their security-free-zone in general or their insecurity-by-default in particular, it was 20-year jail sentences for the hackers. Fortunately the committee, with exquisite politeness, treated him as the idiot he was.
I dont want to get into a flame war about Microsoft’s perceived lack of security, but there have been plenty of vulnerabilities found in Linux – based code: Heartbleed, DirtyCOW, Rekoobe, PorkExplosion, any number of “cool” sounding hacks.
The simple fact is, almost all software (and now hardware) has a bug which can be exploited (rowhammer). The bug in the ZigBee stack that allows hackers to take over Philips Hue light bulbs from a drone isn’t even part of an operating system.
The only solution is to stop these big corporations holding on to our data (and trawling for more, so they can advertise at us and “share with carefully chosen third parties”).
GDPR should start having an impact soon, the £500,000 fines handed out to Farcebook and Equifax were derisory because the breaches took place before GDPR day.
Next time it will hurt big time.
And, yes, courts need to stop treating hackers like naughty kids, and giving a slap on the wrist. The sentence should reflect the seriousness of the crime – be it physical harm, or financial loss (and that financial loss should include the fine handed out to the company).
Good to see the Californian Swatter is facing 20 years, and he didn’t even pull the trigger.
A better analogy is this: You pay a package delivery service to deliver your package. They load it along with others onto their truck. They then make no effort whatsoever to protect those packages. They park in a bad neighborhood and leave the truck unlocked overnight.
Laws more stringent on hackers? It is already illegal with tough sentences.
Deterrence only goes so far. No hacker is going to say, “I am willing to accept the meager prison time for this hack”.
Also, criminal prosecution as a deterrence doesn’t work very well for hacking because the risk of getting caught is so low. They can easily be out of the jurisdiction too.
So the “mugging” example is convenient since that is clearly someone way more likely to face criminal judgement. And there is no precedent for negligence based on being in a neighborhood.
Companies are getting paid for their business, and thus have expectations for which they could be found negligent if they don’t take due care.
Congressional failure to act covers so many different areas we can just make that quote a MadLib.
“It seems like every other day we learn about a new [mass shooting/environmental disaster/mega-breach affecting the personal data of millions of Americans/financial scam perpetrated by the finance industry/______]. Rather than accepting this trend as the new normal, this latest incident should strengthen Congress’ resolve. We must pass laws that require [safer guns (e.g. biometric controls) and more controls over gun sales/more stringent regulation and inspection of environmental impacts/more stringent regulation and inspection of financial risks/data minimization, ensuring companies do not keep sensitive data that they no longer need/________]. And it is past time we enact laws that ensure [gun sellers and owners are liable for what is done with guns they provide/ executives are subject to liability and criminal sanctions for corporate malfeasance on their watch/ companies account for security costs/___________] rather than making their consumers shoulder the burden and harms resulting from these lapses.
Our thoughts and prayers are with the victims and their families who have been harmed by this latest [atrocity/environmental disaster/financial catastrophe/security breach/_______], and we in Congress will establish a blue ribbon commission that will make recommendations that we will decide are politically untenable because they will upset our corporate donors.
[Sen. / Rep.] ____________ [(D)/(R)] ___(State)____
1) Pass a law that says if you tell a company to purge ALL of the data you gave them as well as passed on to a separate company in 24 hours.
2) Pass a law that says a company has to disclose every time they pass your data on.
Next time there’s an attack, they’ll get flooded with demands to purge, which will eventually put them out of business since their saleable items (YOUR information) will drop to nothing.
And the company will tell you to provide all of your information, so they can search their databases for it.
Then they’ll keep your request on file, to prove to government and courts that they received and honored your request.
It’s trading one file for another.
Look for Google’s data “transparency” reports, regarding deletion of URLs in their results under the “right to be forgotten.” The URLs still exist.
Since this will be their global database, I can’t imagine they have a domestic US one and another for the rest of the world, but right now I bet they wish they did and it was hidden somewhere on Europe. Why, because right now they are holding the smoking gun of what may well be the largest GDPR penalty handed out outside of Europe. This is going to wake a lot of organisations up. If it involves a contractor breach like Target then companies will be asking what they might have to do to secure their supply chains. This might be the thin edge of the wedge. If US airlines and other US travel organisations see the problem with what GDPR might really cause them as well the flow on should be significant enough to see some real changes. Time to go warm up the popcorn this might get interesting
Planting your flag at USPS doesn’t protect your mail from being scanned by someone else. Multiple persons (or organizations) can order the service, sent to anywhere. The recently-added step of snailmail confirmation helps but isn’t a panacea.
I don’t think separating security from technology makes sense these days, that feels like pretty old-school advice. In the context of modern environments and automated CI/CD pipelines, security (and, thus, security folks) needs to be deeply embedded into the systems development process as much as possible, and as “left” as possible, rather than exist process that happens discretely/”somewhere else”. Doing embedded security while the security org is separate/up a separate reporting line does not work. And nevermind that Audit already plays a “3rd line”/independent checker role in most large orgs.
Companies need to practice reasonable cybersecurity. No doubt about that. The FTC publishes good information on what that means. At the same time, cyber-attackers need to be held accountable for their crimes. Who has a great idea for how to do that?
Unfortunately, holding cyber-criminals responsible is an easier-said-than-done scenario.
Many times, cyber criminals pivot off of stolen resources. For example, website owners don’t know their site is compromised until they receive an abuse report from their ISP or web-hosting company. On top of that, many of them are foreign, in jurisdictions without any sort of ability to extradite or prosecute for cyber crimes. While many tout “hack back” as a means of bringing consequences, this kind of policy approach guarantees more damage to innocent bystanders – it’s very easy to make an attack look like it is coming from somewhere else.
The only solution remains to be “good security” – something no one really seems to be good at.
I don’t see legislation helping this issue, unfortunately. It’s a basic tenant of cybersecurity that compliance is not security. Let’s not fall into the old trap of assuming we will “get it right” with the next round of laws.
Change is going to have to be driven by market share and consumers are going to have to accept less convenience to achieve any measure of safety. When you figure out how to sell that package, let me know!
@Jeff Strubberg
The NEXT round of laws ONLY needs a few things to be effective:
1.) MASSIVE FINES <–Big business speaks only the language of money
2.) JAIL TIME and TAKE THE PERSONAL ASSETS of CEOs and executives <–No place to hide or run or golden parachute to – no point having employees take ethics training every year when negligent criminals at the top have no conscious, no morals and no punishment – ACTUAL security like everything else in the corporate world needs to start at the top period.
I would be curious to hear your thoughts on what meaningful legislation would look like. I agree that this likely won’t change until meaningful legislation is put in place and enforced, but considering that best practices and threat types seem to change very rapidly, how would congress enact some law that would remain relevant in the long term?
That meaningful legislation would probably have to be something that required extreme data minimization without being requested to do so, e.g., requiring the deletion of personal data immediately after a transaction has been processed.
Even under GDPR, the number of deletion requests are a tiny, tiny fraction of an overall customer population. That results in massive data sets like Starwood hotels had.
But that legislation will never be passed – not even in Europe.
For me, “assuming you’re compromised” means using a Chromebook for reading web email, so clicking on a booby trapped link does nothing.