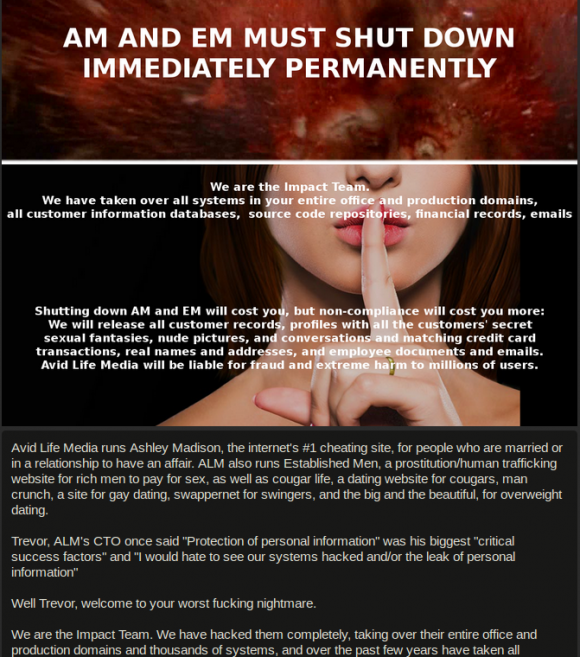
AshleyMadison.com, a site that helps married people cheat and whose slogan is “Life is Short, have an Affair,” recently put up a half million (Canadian) dollar bounty for information leading to the arrest and prosecution of the Impact Team — the name chosen by the hacker(s) who recently leaked data on more than 30 million Ashley Madison users. Here is the first of likely several posts examining individuals who appear to be closely connected to this attack.
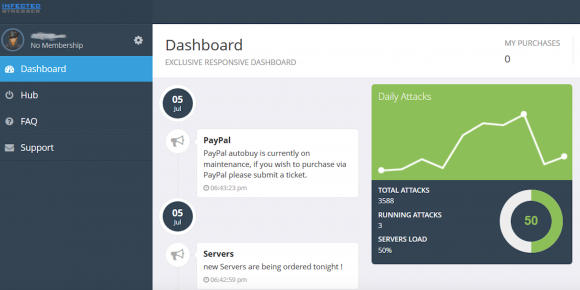
 It was just past midnight on July 20, a few hours after I’d published an exclusive story about hackers breaking into AshleyMadison.com. I was getting ready to turn in for the evening when I spotted a re-tweet from a Twitter user named Thadeus Zu (@deuszu) who’d just posted a link to the same cache of data that had been confidentially shared with me by the Impact Team via the contact form on my site just hours earlier: It was a link to the proprietary source code for Ashley Madison’s service.
It was just past midnight on July 20, a few hours after I’d published an exclusive story about hackers breaking into AshleyMadison.com. I was getting ready to turn in for the evening when I spotted a re-tweet from a Twitter user named Thadeus Zu (@deuszu) who’d just posted a link to the same cache of data that had been confidentially shared with me by the Impact Team via the contact form on my site just hours earlier: It was a link to the proprietary source code for Ashley Madison’s service.
Initially, that tweet startled me because I couldn’t find any other sites online that were actually linking to that source code cache. I began looking through his past tweets and noticed some interesting messages, but soon enough other news events took precedence and I forgot about the tweet.
I revisited Zu’s tweet stream again this week after watching a press conference held by the Toronto Police (where Avid Life Media, the parent company of Ashley Madison, is based). The Toronto cops mostly recapped the timeline of known events in the hack, but they did add one new wrinkle: They said Avid Life employees first learned about the breach on July 12 (seven days before my initial story) when they came into work, turned on their computers and saw a threatening message from the Impact Team accompanied by the anthem “Thunderstruck” by Australian rock band AC/DC playing in the background.
After writing up a piece on the bounty offer, I went back and downloaded all five years’ worth of tweets from Thadeus Zu, a massively prolific Twitter user who typically tweets hundreds if not thousands of messages per month. Zu’s early years on Twitter are a catalog of simple hacks — commandeering unsecured routers, wireless cameras and printers — as well as many, many Web site defacements.
On the defacement front, Zu focused heavily on government Web sites in Asia, Europe and the United States, and in several cases even taunted his targets. On Aug. 4, 2012, he tweeted to KPN-CERT, a computer security incident response team in the Netherlands, to alert the group that he’d hacked their site. “Next time, it will be Thunderstruck. #ACDC” Zu wrote.
The day before, he’d compromised the Web site for the Australian Parliament, taunting lawmakers there with the tweet: “Parliament of Australia bit.ly/NPQdsP Oi! Oi! Oi!….T.N.T. Dynamite! Listen to ACDC here.”
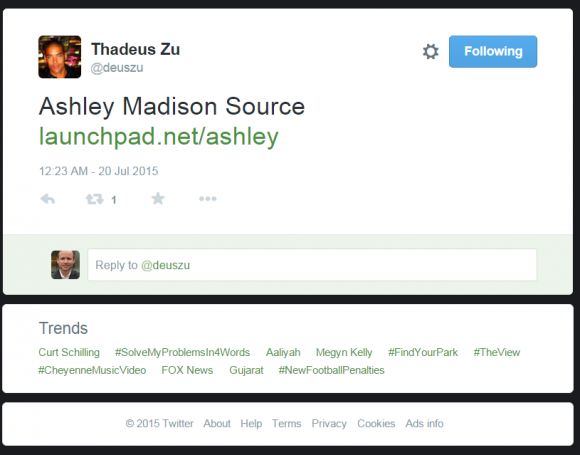
I began to get very curious about whether there were any signs on or before July 19, 2015 that Zu was tweeting about ACDC in relation to the Ashley Madison hack. Sure enough: At 9:40 a.m., July 19, 2015 — nearly 12 hours before I would first be contacted by the Impact Team — we can see Zu is feverishly tweeting to several people about setting up “replication servers” to “get the show started.” Can you spot what’s interesting in the tabs on his browser in the screenshot he tweeted that morning?
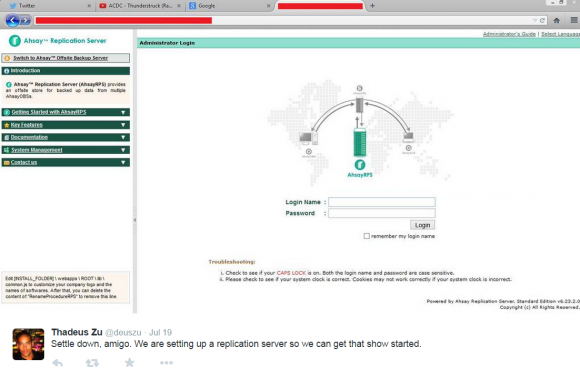
Twitter user ThadeusZu tweets about setting up replication servers. Did you spot the Youtube video he’s playing when he took this screenshot?
Ten points if you noticed the Youtube.com tab showing that he’s listening to AC/DC’s “Thunderstruck.”
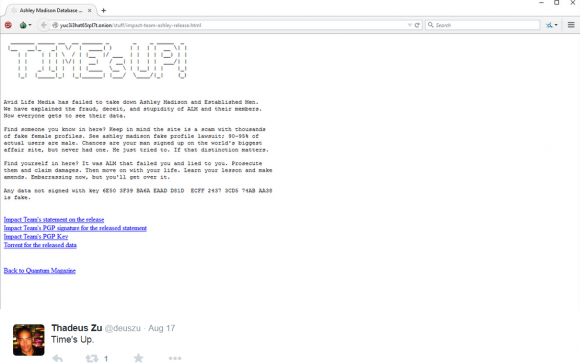
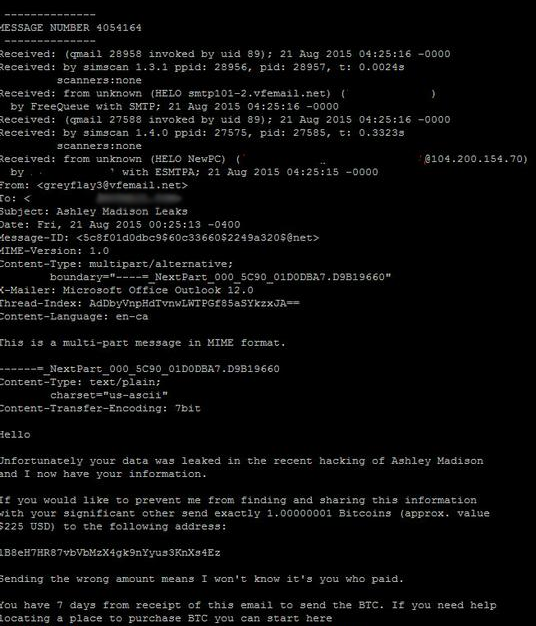
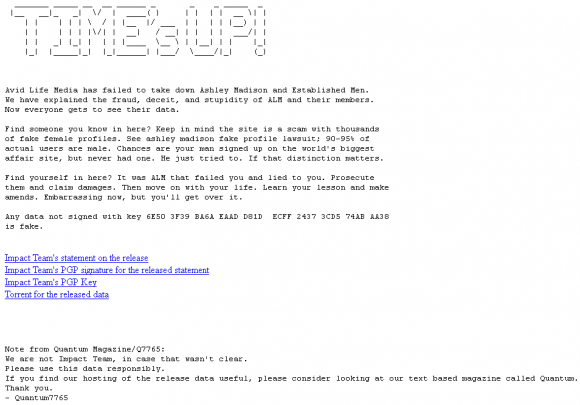
A week ago, the news media pounced on the Ashley Madison story once again, roughly 24 hours after the hackers made good on their threat to release the Ashley Madison user database. I went back and examined Zu’s tweet stream around that time and found he beat Wired.com, ArsTechnica.com and every other news media outlet by more than 24 hours with the Aug. 17 tweet, “Times up,” which linked to the Impact Team’s now infamous post listing the sites where anyone could download the stolen Ashley Madison user database.