Last week, LifeLock and several other identity theft protection firms erroneously alerted their customers to a breach at cloud storage giant Dropbox.com — an incident that reportedly exposed some 73 million usernames and passwords. The only problem with that notification was that Dropbox didn’t have a breach; the data appears instead to have come from another breach revealed this week at social network Tumblr.
Today’s post examines some of the missteps that preceded this embarrassing and potentially brand-damaging “oops.” We’ll also explore the limits of automated threat intelligence gathering in an era of megabreaches like the ones revealed over the past week that exposed more than a half billion usernames and passwords stolen from Tumblr, MySpace and LinkedIn.
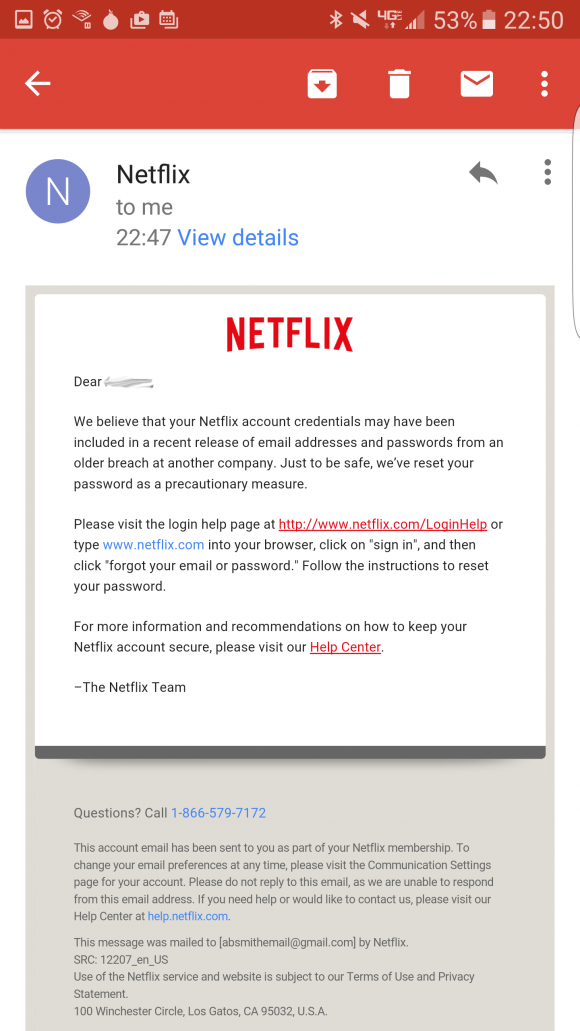
The credentials leaked in connection with breaches at those social networking sites were stolen years ago, but the full extent of the intrusions only became clear recently — when several huge archives of email addresses and hashed passwords from each service were posted to the dark web and to file-sharing sites.
Last week, a reader referred me to a post by a guy named Andrew on the dropbox.com help forum. Andrew said he’d just received alerts blasted out by two different credit monitoring firms that his dropbox credentials had been compromised and were found online (see screenshot below).
A user on the dropbox forum complains of receiving alerts from separate companies warning of a huge password breach at dropbox.com.
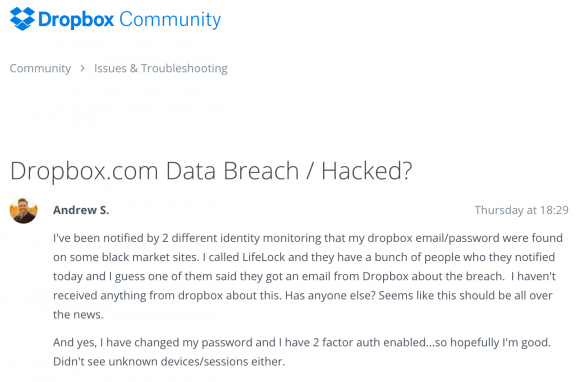
Here’s what LifeLock sent out on May 23, 2016 to many customers who pay for the company’s credential recovery services:
Alert Date: 05-23-2016
Alert Type: Monitoring
Alert Category: Internet-Black Market Website
**Member has received a File Sharing Network alert Email: *****
Password: ****************************************
Where your data was found: social media
Type of Compromise: breach
Breached Sector: business
Breached Site: www.dropbox.com
Breached Record Count: 73361477
Password Status: hashed
Severity: red|email,password
Site: www.dropbox.com
LifeLock said it got the alert data via an information sharing agreement with a third party threat intelligence service, but it declined to name the service that sent the false positive alert.
“We can confirm that we recently notified a small segment of LifeLock members that a version of their dropbox.com credentials were detected on the internet,” LifeLock said in a written statement provided to KrebsOnSecurity. “When we are notified about this type of information from a partner, it is usually a “list” that is being given away, traded or sold on the dark web. The safety and security of our members’ data is our highest priority. We are continuing to monitor for any activity within our source network. At this time, we recommend that these LifeLock members change their Dropbox password(s) as a precautionary measure.”
Dropbox says it didn’t have a breach, and if it had the company would be seeing huge amounts of account checking activity and other oddities going on right now. And that’s just not happening, they say.
“We have learned that LifeLock and MyIdCare.com are reporting that Dropbox account details of some of their customers are potentially compromised,” said Patrick Heim, head of trust and security at Dropbox. “An initial investigation into these reports has found no evidence of Dropbox accounts being impacted. We’re continuing to look into this issue and will update our users if we find evidence that Dropbox accounts have been impacted.” Continue reading →
 The latest update brings Flash to v. 22.0.0.192 for Windows and Mac users alike. If you have Flash installed, you should update, hobble or remove Flash as soon as possible.
The latest update brings Flash to v. 22.0.0.192 for Windows and Mac users alike. If you have Flash installed, you should update, hobble or remove Flash as soon as possible.



 According to
According to  FBI Special Agent Timothy J. Wilkins wrote that investigators also subpoenaed and got access to that michaelp77x@gmail.com account, and found emails between Persaud and at least four affiliate programs that hire spammers to send junk email campaigns.
FBI Special Agent Timothy J. Wilkins wrote that investigators also subpoenaed and got access to that michaelp77x@gmail.com account, and found emails between Persaud and at least four affiliate programs that hire spammers to send junk email campaigns. Yes, that’s right it’s once again Patch Tuesday, better known to mere mortals as the second Tuesday of each month. Microsoft isn’t kidding around this particular Tuesday — pushing out
Yes, that’s right it’s once again Patch Tuesday, better known to mere mortals as the second Tuesday of each month. Microsoft isn’t kidding around this particular Tuesday — pushing out  During the height of tax-filing season in 2015, KrebsOnSecurity
During the height of tax-filing season in 2015, KrebsOnSecurity  On January 27, 2016, this publication was the first
On January 27, 2016, this publication was the first 
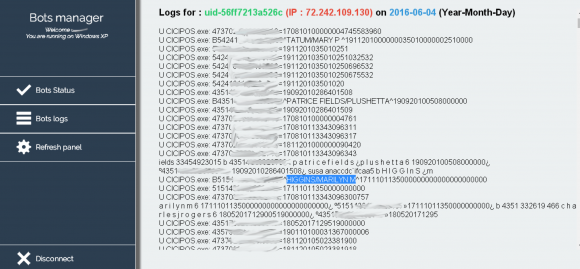
 Over the past two months, KrebsOnSecurity has received inquiries from fraud fighters at more than a half-dozen financial institutions in the United States — all asking if I had any information about a possible credit card breach at CiCi’s. Every one of these banking industry sources said the same thing: They’d detected a pattern of fraud on cards that all had all been used in the last few months at various CiCi’s Pizza locations.
Over the past two months, KrebsOnSecurity has received inquiries from fraud fighters at more than a half-dozen financial institutions in the United States — all asking if I had any information about a possible credit card breach at CiCi’s. Every one of these banking industry sources said the same thing: They’d detected a pattern of fraud on cards that all had all been used in the last few months at various CiCi’s Pizza locations.