When your credit card gets stolen because a merchant you did business with got hacked, it’s often quite easy for investigators to figure out which company was victimized. The process of divining the provenance of stolen healthcare records, however, is far trickier because these records typically are processed or handled by a gauntlet of third party firms, most of which have no direct relationship with the patient or customer ultimately harmed by the breach.
I was reminded of this last month, after receiving a tip from a source at a cyber intelligence firm based in California who asked to remain anonymous. My source had discovered a seller on the darknet marketplace AlphaBay who was posting stolen healthcare data into a subsection of the market called “Random DB ripoffs,” (“DB,” of course, is short for “database”).
Eventually, this same fraudster leaked a large text file titled, “Tenet Health Hilton Medical Center,” which contained the name, address, Social Security number and other sensitive information on dozens of physicians across the country.
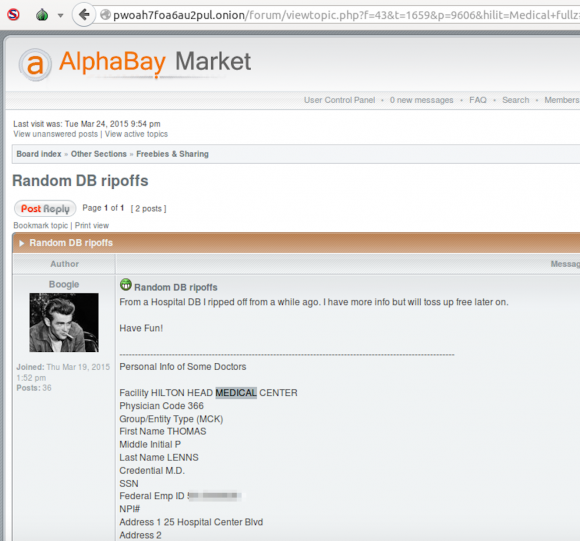 Contacted by KrebsOnSecurity, Tenet Health officials said the data was not stolen from its databases, but rather from a company called InCompass Healthcare. Turns out, InCompass disclosed a breach in August 2014, which reportedly occurred after a subcontractor of one of the company’s service providers failed to secure a computer server containing account information. The affected company was 24 ON Physicians, an affiliate of InCompass Healthcare.
Contacted by KrebsOnSecurity, Tenet Health officials said the data was not stolen from its databases, but rather from a company called InCompass Healthcare. Turns out, InCompass disclosed a breach in August 2014, which reportedly occurred after a subcontractor of one of the company’s service providers failed to secure a computer server containing account information. The affected company was 24 ON Physicians, an affiliate of InCompass Healthcare.
“The breach affected approximately 10,000 patients treated at 29 facilities throughout the U.S. and approximately 40 employed physicians,” wrote Rebecca Kirkham, a spokeswoman for InCompass.
“As a result, a limited amount of personal information may have been exposed to the Internet between December 1, 2013 and April 17, 2014, Kirkham wrote in an emailed statement. Information that may have been exposed included patient names, invoice numbers, procedure codes, dates of service, charge amounts, balance due, policy numbers, and billing-related status comments. Patient social security number, home address, telephone number and date of birth were not in the files that were subject to possible exposure. Additionally, no patient medical records or bank account information were put at risk. The physician information that may have been exposed included physician name, facility, provider number and social security number.”
Kirkham said up until being contacted by this reporter, InCompass “had received no indication that personal information has been acquired or used maliciously.”
So who was the subcontractor that leaked the data? According to PHIprivacy.net (and now confirmed by InCompass), the subcontractor responsible was PST Services, a McKesson subsidiary providing medical billing services, which left more than 10,000 patients’ information exposed via Google search for over four months.
As this incident shows, a breach at one service provider or healthcare billing company can have a broad impact across the healthcare system, but can be quite challenging to piece together. Continue reading