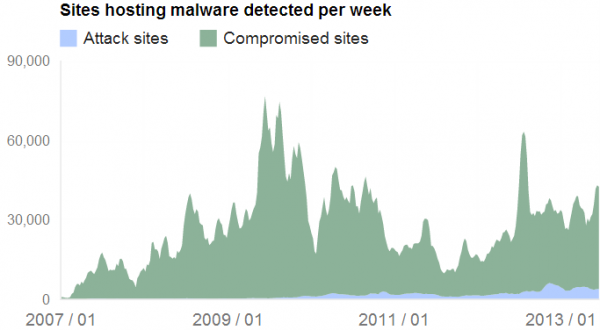
An increasing number of malware samples in the wild are using host systems to secretly mine bitcoins. In this post, I’ll look at an affiliate program that pays people for the mass installation of programs that turns host machines into bitcoin mining bots.
Bitcoin is a decentralized, virtual currency, and bitcoins are created by large numbers of CPU-intensive cryptographic calculations. As Wikipedia explains, the processing of Bitcoin transactions is secured by servers called bitcoin miners. These servers communicate over an internet-based network and confirm transactions by adding them to a ledger which is updated and archived periodically using peer-to-peerfilesharing technology. In addition to archiving transactions, each new ledger update creates some newly minted bitcoins.
Earlier this week, I learned of a Russian-language affiliate program called FeodalCash which pays its members to distribute a bitcoin mining bot that forces host PCs to process bitcoin transactions (hat tip to security researcher Xylitol). FeodalCash opened its doors in May 2013, and has been recruiting new members who can demonstrate that they have control over enough Internet traffic to guarantee at least several hundred installs of the bitcoin mining malware each day.
The FeodalCash administrator claims his mining program isn’t malware, although he cautions all affiliates against submitting the installer program to multi-antivirus scanners such as Virustotal; sending the program that installs bitcoin mining bot to Virustotal “greatly complicates the work with antivirus” on host PCs. Translation: Because services like Virustotal share information about new malware samples with all participating antivirus vendors, scanning the installer will make it more likely that antivirus products on host PCs will flag the program as malicious. Rather, the administrator urged users who want to check the files for antivirus detection to use a criminal friendly service like scan4u[dot]net or chk4me[dot]com, which likewise scan submitted files with dozens of different antivirus tools but block those tools from reporting home about new and unidentified malware variants.
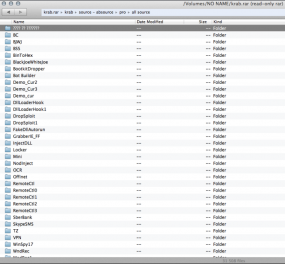
I gained access to an affiliate account and was able to grab a copy of the mining program. I promptly submitted the file to Virustotal and found it was flagged as a trojan horse program by at least two antivirus products. This analysis at automated malware scanning site malwr.com shows that the mining program installer ads a Windows registry key so that the miner starts each time Windows boots up. It also indicates that the program beacons out to pastebin.com (perhaps to deposit a note about each new installation).
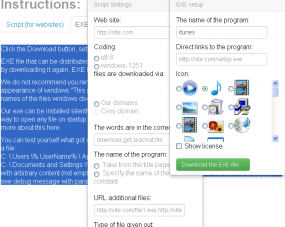
The FeodalCash administrator also claims that his affiliates are not permitted to distribute the installer file in any way that violates the law, but of course it’s unclear which national laws he might be talking about. At the same time, the affiliate program’s Web site includes a graphical tool that helps affiliates create a custom installer program that can install silently and be disguised with a variety of program icons that are similar to familiar Windows icons.
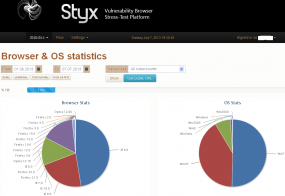
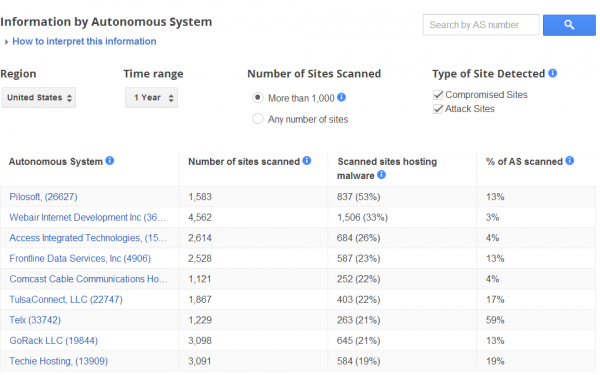
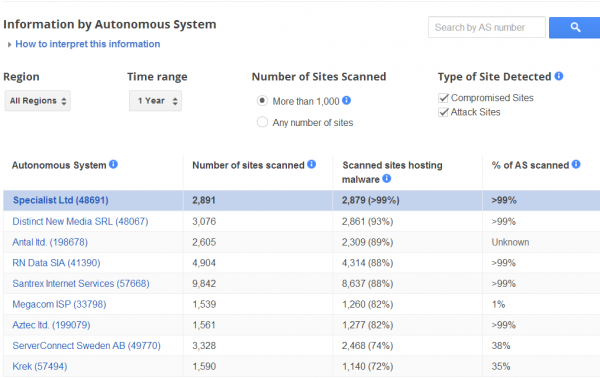
Also, the administrator demands that new users demonstrate the ability to garner hundreds to thousands of installs per day. This is a rather high install rate, and it appears many if not all affiliates are installing the mining program by bundling it with other executable programs distributed by so-called pay-per-install (PPI) programs. This was apparent because a source managed to gain administrative-level access to the back-end database for the FeodalCash program, which includes hundreds of messages between affiliates and the administrator; most of those messages are from new registrants sending the administrator screenshots of their traffic and installs statistics at various PPI affiliate programs.