Trend Micro’s Rik Ferguson posted a good piece on Thursday about a major shortcoming in credit card security programs maintained by MasterCard and Visa. Although the loophole that Ferguson highlighted may be unsettling to some, fraudsters who specialize in stealing and using stolen credit cards online have been exploiting it for years.
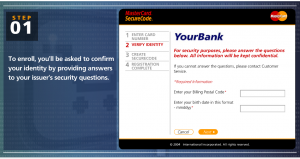 At issue is a security protocol called “3 Domain Secure,” (3DS), a program designed to reduce card fraud and shift liability for fraud from online merchants to the card issuing banks. Visa introduced the program in 2001, branding it “Verified by Visa,” and MasterCard has a similar program in place called “SecureCode.”
At issue is a security protocol called “3 Domain Secure,” (3DS), a program designed to reduce card fraud and shift liability for fraud from online merchants to the card issuing banks. Visa introduced the program in 2001, branding it “Verified by Visa,” and MasterCard has a similar program in place called “SecureCode.”
Cardholders who chose to participate in the programs can register their card by entering the card number, filling in their ZIP code and birth date, and picking a passcode. When a cardholder makes a purchase at a site that uses 3DS, he enters the code, which is verified by the issuing bank and is never shared with the merchant site.
But as Ferguson notes, people are human and tend to forget things, especially passcodes and passwords, and it is the password reset function that eliminates any security provided by Verified by Visa or SecureCode. From his blog:
“What would a criminal do if they access to your card details but not your password? Of course, there’s that handy “I forgot my password” link. Let’s see how well protected that is.”
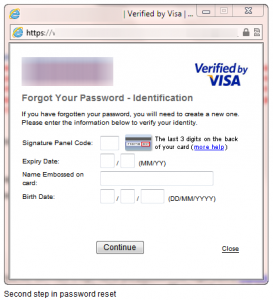 The first step in the password reset procedure is to enter your card number, obviously to ensure you are resetting the password for the correct account. Once that number is entered the system now requires some corroborating data to be sure that you are the legitimate account holder, let’s have a look at that “Identification” phase.”
The first step in the password reset procedure is to enter your card number, obviously to ensure you are resetting the password for the correct account. Once that number is entered the system now requires some corroborating data to be sure that you are the legitimate account holder, let’s have a look at that “Identification” phase.”
“Oh noes, this doesn’t look good at all! Three out of four of the items of information used to verify my identity are all contained in the credit card data itself, embossed or printed on the card and contained in the magnetic stripe data. Wouldn’t the criminal already have access to this? So what remains? One piece of information that is not included on the card. Trouble is, it’s information that is not only widely shared on social networks, surveys, sign-up forms and a myriad of other places, but also freely available in public records. We cannot and should not consider our date of birth to be a secret.”
“Having entered the required information all that remains is to enter a new password of your choosing and your transaction is authorised. Worse still, no email notification is sent to alert the cardholder that their account has been accessed or modified. The cardholder need never know until they check their statements.”
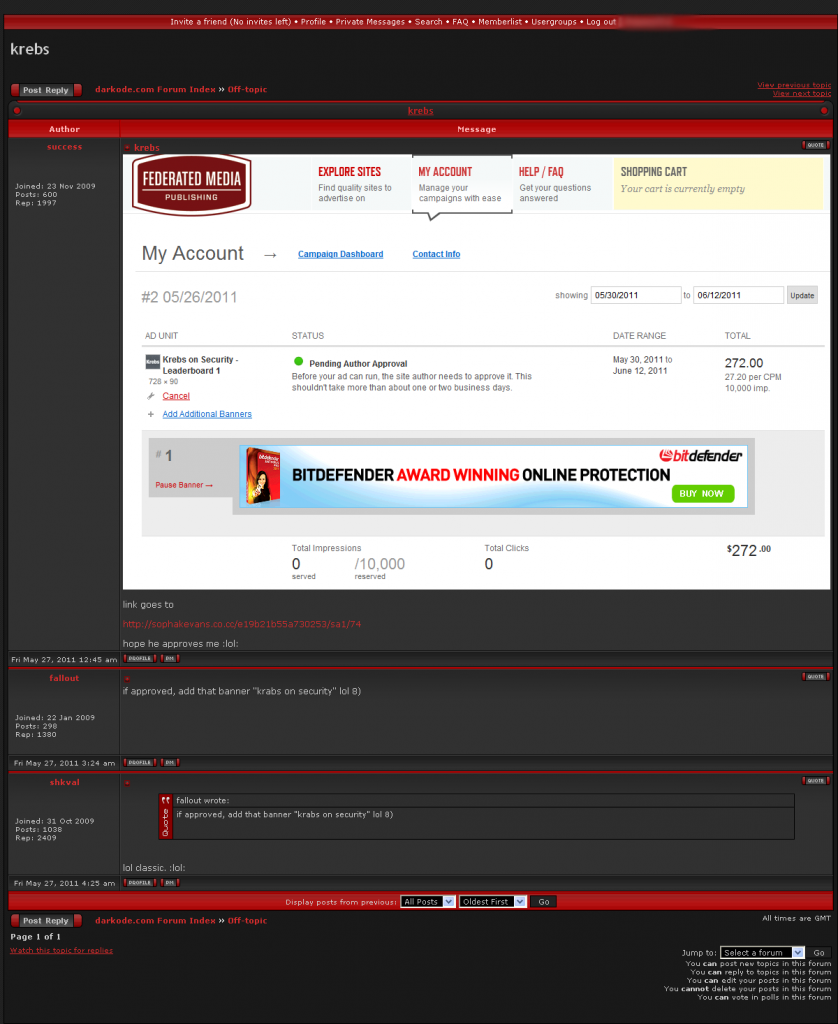
This would all be very shocking if it wasn’t already painfully obvious to today’s cyber crooks. When I read the Trend blog post, I began searching for several screen shots I had taken of a discussion on an underground carding forum more than two years ago, which explained very clearly how to get around this added level of card security. The tutorial in the screen shot below was posted by an administrator from the carding forum carder.pro on Halloween, 2009: