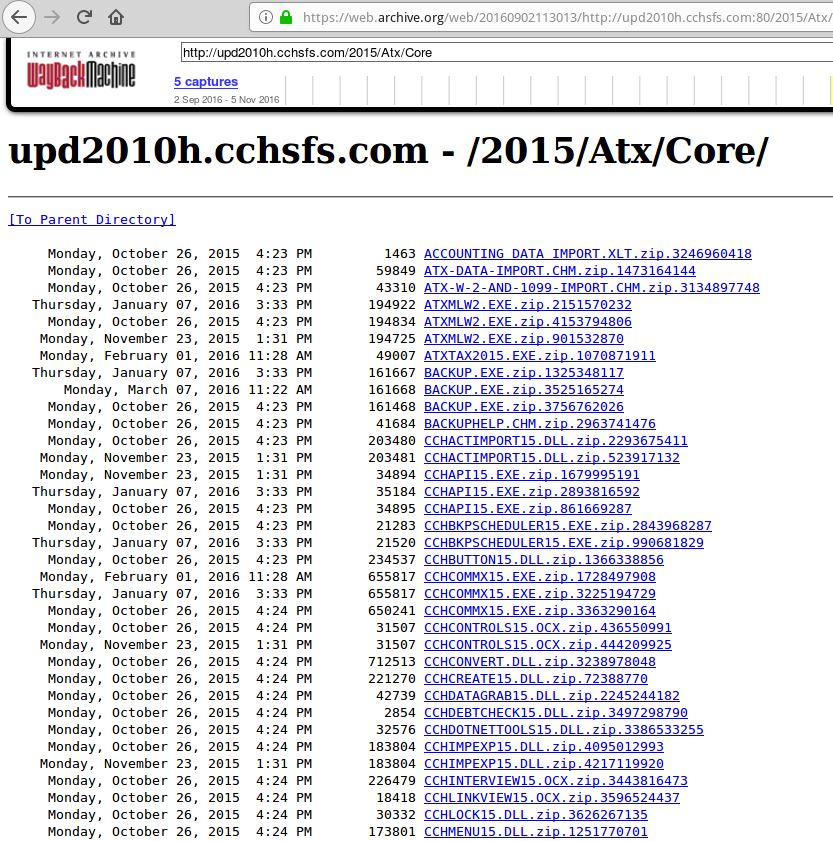
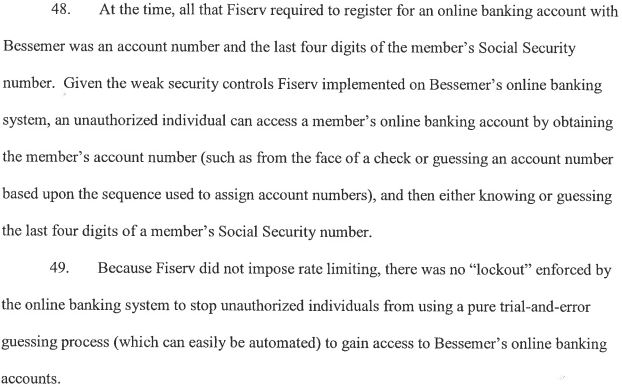
In the early days of the Internet, there was a period when Internet Protocol version 4 (IPv4) addresses (e.g. 4.4.4.4) were given out like cotton candy to anyone who asked. But these days companies are queuing up to obtain new IP space from the various regional registries that periodically dole out the prized digits. With the value of a single IP hovering between $15-$25, those registries are now fighting a wave of shady brokers who specialize in securing new IP address blocks under false pretenses and then reselling to spammers. Here’s the story of one broker who fought back in the courts, and lost spectacularly.

On May 14, South Carolina U.S. Attorney Sherri Lydon filed criminal wire fraud charges against Amir Golestan, alleging he and his Charleston, S.C. based company Micfo LLC orchestrated an elaborate network of phony companies and aliases to secure more than 735,000 IPs from the American Registry for Internet Numbers (ARIN), a nonprofit which oversees IP addresses assigned to entities in the U.S., Canada, and parts of the Caribbean.
Interestingly, Micfo itself set this process in motion late last year when it sued ARIN. In December 2018, Micfo’s attorneys asked a federal court in Virginia to issue a temporary restraining order against ARIN, which had already told the company about its discovery of the phony front companies and was threatening to revoke some 735,000 IP addresses. That is, unless Micfo agreed to provide more information about its operations and customers.
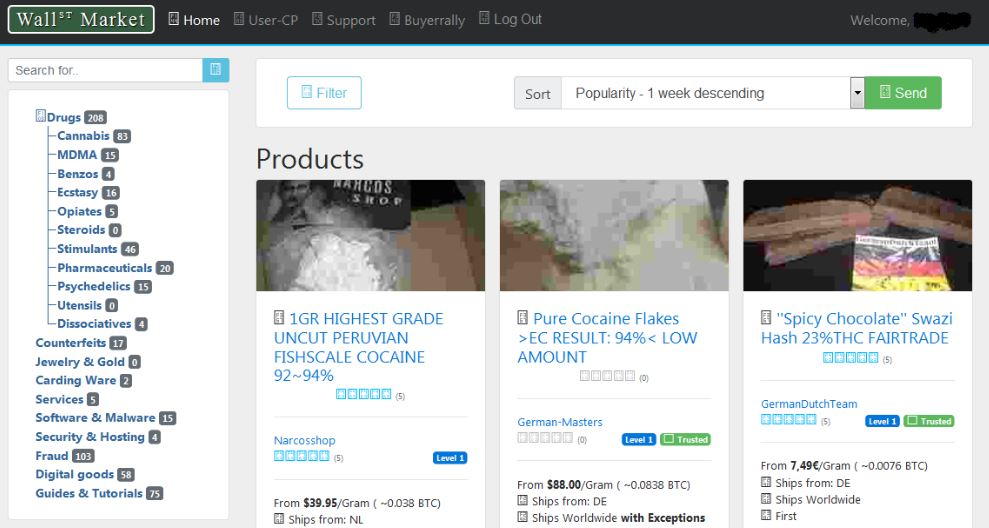
At the time, many of the IP address blocks assigned to Micfo had been freshly resold to spammers. Micfo ultimately declined to provide ARIN the requested information, and as a result the court denied Micfo’s request (the transcript of that hearing is instructive and amusing).
But by virtue of the contract Micfo signed with ARIN, any further dispute had to be settled via arbitration. On May 13, that arbitration panel ordered Micfo to pay $350,000 for ARIN’s legal fees and to cough up any of those 735,000 IPs the company hadn’t already sold.
According to the criminal indictment in South Carolina, in 2017 and 2018 Golestan sold IP addresses using a third party broker:
“Golestan sold 65,536 IPv4 addresses for $13 each, for a total of $851,896,” the indictment alleges. “Golestan also organized a second transaction for another 65,536 IP addresses, for another approximately $1 million. During this same time period, Golestan had a contract to sell 327,680 IP addresses at $19 per address, for a total of $6.22 million” [this last transaction would be blocked.] Continue reading