A peer-to-peer (P2P) communications technology built into millions of security cameras and other consumer electronics includes several critical security flaws that expose the devices to eavesdropping, credential theft and remote compromise, new research has found.
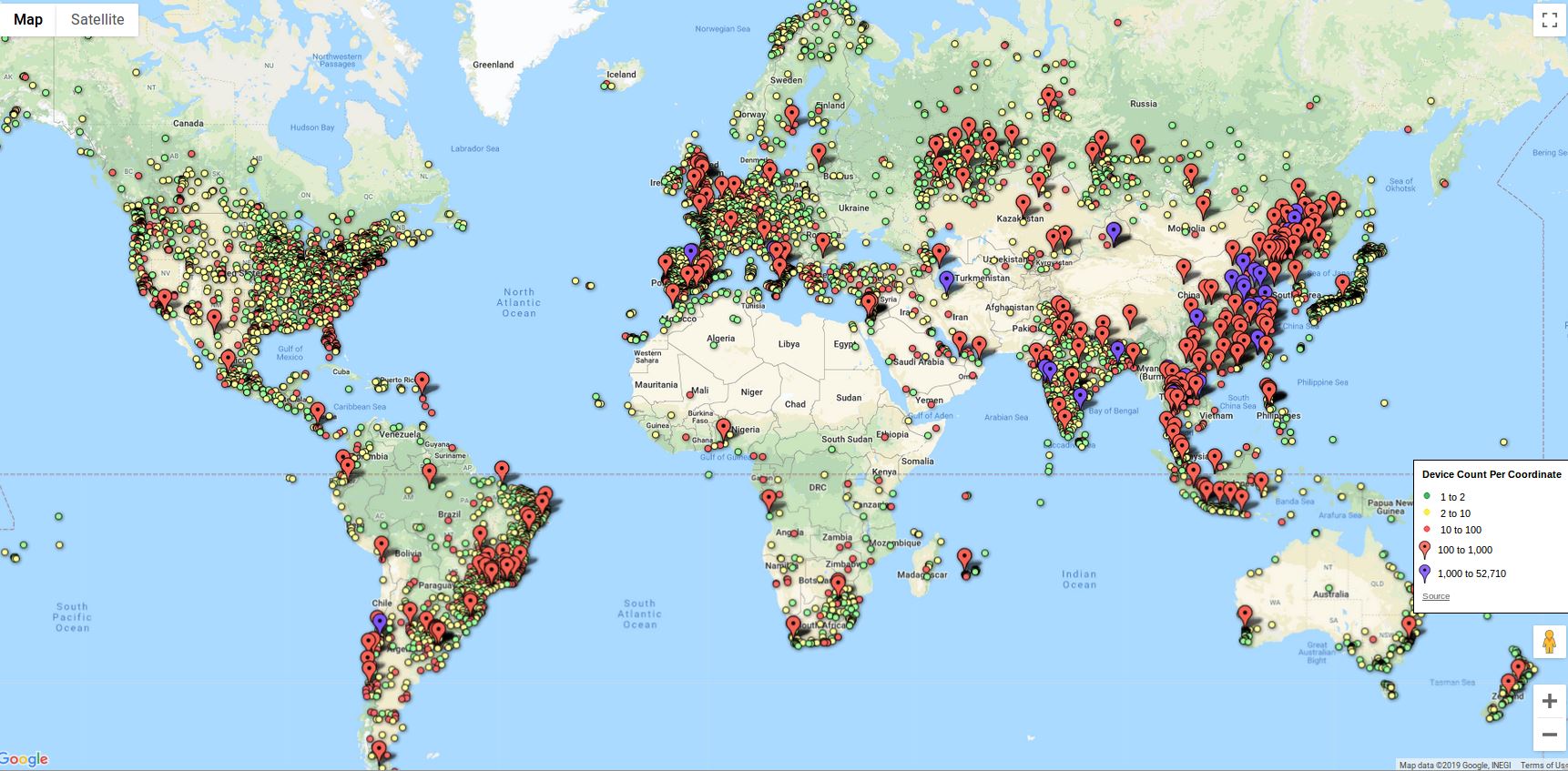
A map showing the distribution of some 2 million iLinkP2P-enabled devices that are vulnerable to eavesdropping, password theft and possibly remote compromise, according to new research.
The security flaws involve iLnkP2P, software developed by China-based Shenzhen Yunni Technology. iLnkP2p is bundled with millions of Internet of Things (IoT) devices, including security cameras and Webcams, baby monitors, smart doorbells, and digital video recorders.
iLnkP2P is designed to allow users of these devices to quickly and easily access them remotely from anywhere in the world, without having to tinker with one’s firewall: Users simply download a mobile app, scan a barcode or enter the six-digit ID stamped onto the bottom of the device, and the P2P software handles the rest.
But according to an in-depth analysis shared with KrebsOnSecurity by security researcher Paul Marrapese, iLnkP2P devices offer no authentication or encryption and can be easily enumerated, allowing potential attackers to establish a direct connection to these devices while bypassing any firewall restrictions.
Marrapese said a proof-of-concept script he built identified more than two million vulnerable devices around the globe (see map above). He found that 39 percent of the vulnerable IoT things were in China; another 19 percent are located in Europe; seven percent of them are in use in the United States.
Although it may seem impossible to enumerate more than a million devices with just a six-digit ID, Marrapese notes that each ID begins with a unique alphabetic prefix that identifies which manufacturer produced the device, and there are dozens of companies that white-label the iLnkP2P software.
For example, HiChip — a Chinese IoT vendor that Marrapese said accounts for nearly half of the vulnerable devices — uses the prefixes FFFF, GGGG, HHHH, IIII, MMMM, ZZZZ.
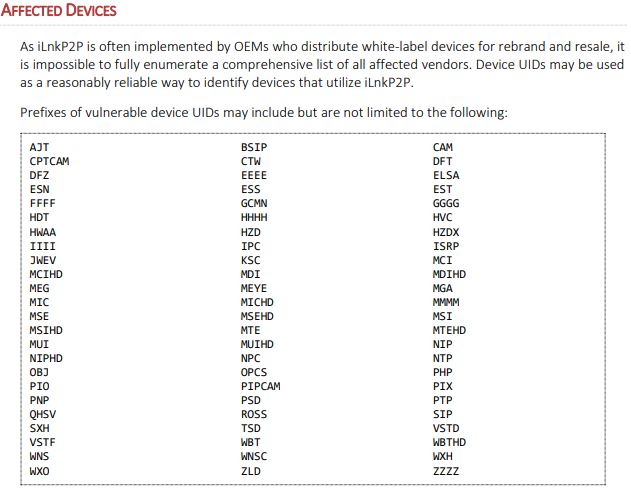
These prefixes identify different product lines and vendors that use iLnkP2P. If the code stamped on your IoT device begins with one of these, it is vulnerable.
“In theory, this allows them to support nearly 6 million devices for these prefixes alone,” Marrapese said. “In reality, enumeration of these prefixes has shown that the number of online devices was ~1,517,260 in March 2019. By enumerating all of the other vendor prefixes, that pushes the number toward 2 million.”
Marrapese said he also built a proof-of-concept attack that can steal passwords from devices by abusing their built-in “heartbeat” feature. Upon being connected to a network, iLnkP2P devices will regularly send a heartbeat or “here I am” message to their preconfigured P2P servers and await further instructions.
“A P2P server will direct connection requests to the origin of the most recently-received heartbeat message,” Marrapese said. “Simply by knowing a valid device UID, it is possible for an attacker to issue fraudulent heartbeat messages that will supersede any issued by the genuine device. Upon connecting, most clients will immediately attempt to authenticate as an administrative user in plaintext, allowing an attacker to obtain the credentials to the device.”
To make matters worse, even if an attacker doesn’t want to bother intercepting device passwords, a great many of them will be running in their factory-default state with the factory-default password. The IoT malware Mirai proved this conclusively, as it rapidly spread to millions of devices using nothing more than the default credentials for IoT devices made by dozens of manufacturers.
What’s more, as we saw with Mirai the firmware and software built into these IoT devices is often based on computer code that is many years old and replete with security vulnerabilities, meaning that anyone able to communicate directly with them is also likely to be able to remotely compromise them with malicious software.
Marrapese said despite attempts to notify China’s CERT, iLnk and a half dozen major vendors whose products make up the bulk of the affected devices, none of them have responded to his reports — even though he first started reaching out to them more than four months ago. Neither HiChip nor iLnk responded to requests for comment sent by KrebsOnSecurity.
Interestingly, iLnk’s Web site (p1.i-lnk[.]com) currently appears to be non-functional, and a review of its HTML source code indicates the site is currently compromised by an obfuscated script that tries to redirect visitors to a Chinese gaming Web site.
Despite the widespread impact of these vulnerabilities, Marrapese’s research suggests that remediation from vendors is unlikely – and in fact, unfeasible.
“The nature of these vulnerabilities makes them extremely difficult to remediate for several reasons,” Marrapese wrote. “Software-based remediation is unlikely due to the infeasibility of changing device UIDs, which are permanently assigned during the manufacturing process. Furthermore, even if software patches were issued, the likelihood of most users updating their device firmware is low. Physical device recalls are unlikely as well because of considerable logistical challenges. Shenzhen Yunni Technology is an upstream vendor with inestimable sub-vendors due to the practice of white-labeling and reselling.”
Marrapese said there is no practical way to turn off the P2P functionality on the affected devices. Many IoT devices can punch holes in firewalls using a feature built into hardware-based routers called Universal Plug and Play (UPnP). But simply turning off UPnP on one’s router won’t prevent the devices from establishing a P2P connection as they rely on a different communications technique called “UDP hole punching.”
Marrapese said it should be possible to block vulnerable devices from communicating with any P2P servers by setting up firewall rules that block traffic destined for UDP port 32100.
However, a much safer idea would be to simply avoid purchasing or using IoT devices that advertise any P2P capabilities. Previous research has unearthed similar vulnerabilities in the P2P functionality built into other IoT systems. For examples of this, see This is Why People Fear the Internet of Things, and Researchers Find Fresh Fodder for IoT Attack Cannons.
Marrapese documented his findings in more detail here. The enumeration vulnerability has been assigned CVE-2019-11219, and the man-in-the-middle vulnerability has been assigned CVE-2019-11220.
Additional reading: Some Basic Rules for Securing your IoT Stuff.





This is the reason we have avoided all security cameras even though we’d like them. Do you know of any articles that rate security cams including their known vulnerabilities?
The security used with The Ring was vetted by Steve Gibson of GRC.com and he’s gone on record to say that they’ve done it right. There was one instance of a flaw that was reported to them (before Amazon bought them out) and they responded quickly and fixed the flaw.
Excellent. Wish they were as affordable as the cheap china stuff.
You get what you pay for I guess?
Security vs. Privacy
Google, Amazon, Apple… all have great security.
But if ever they decide it is profitable to use your home automation data… beware. Even if they don’t have access to your actual video content… the metadata is still valuable to them.
Gmail is very secure, but Google reads your emails for profiling.
Amazon Echo is secure, but it’s been revealed that humans are listening to audio samples.
We may not hear of a major security flaw from the big companies, but we may hear of privacy abuse.
I wonder from whom Amazon bought their Web Cam – they don’t provide any security information on it – who knows how many vulns it has
Cloud Cam, not “Web” Cam
IMO, that just means Ring’s vulnerabilities/backdoors haven’t been disclosed yet.
Btw, Steve’s actual words were “I mean, Ring is an example of, in my opinion, doing this as right as it can be done.”
The latter part of the quote is rather significant.
Btw, he recommends running all IoT devices on your guest network with no access to your home/business network, which should give you some indication as to his level of trust regarding their inherently insecure nature.
If you have to isolate your IoT devices from your primary network to protect that network from attacks, do you really trust those devices not to leak the data (video, etc) they’re collecting?
All (and I mean all) hardware and software and processes used are designed and built by humans and so therefor has undiscovered bugs. Some have more, but they all have bugs. Some people make a living discovering those bugs, and then sell them to the highest bidder or responsibly report them to the vendor. Why is that fact so hard to grasp?
I’d be very skeptical of any “vetting” that is done by Leo Laporte and his Security Now show. You must realize that Ring is the sponsor of that podcast, so any real “vetting” is highly improbable. As for the Gibson fellow, his version of “vetting” is just reading the press release and “trusting” the vendor/sponsor.
Any real vetting should be done by trusted security researchers that actual reverse engineer the code and look for vulnerabilities.
Perhaps you should find out more about S.G. & Leo for that matter.
@Dennis – here’s a pretty good example of Steve’s skillz:
http://www.crime-research.org/library/grcdos.pdf
You might want to rethink your comments.
Old school h@x0r.
@AL: Thank you. I haven’t laughed this hard for a while.
PS. Definitely a paper written in 2001 by Steve Gibson proves Steve Gibson’s incredible skills as a security researcher.
Do inform us of your skills.
He ran LOIC once.
And the most technical part of that http://www.crime-research.org/library/grcdos.pdf document seems to be the use of netstat.
btw… this is a different Joe here. Most of the comments below are mine. And not the one defending S.G. or Leo.
Thank you average Joe.
I like open source standards, so I suggest Axis. They just bought 2N, but I would hold off on 2N products until they have been Axis products for a while. Axis is an ONVIF member.
Regarding RING, never use WiFi for security. Crooks use jammers. Yes I am serious.
Another tip is to buy cameras that use surface mount IR LEDs rather than through hole. Also avoid bullet cameras if there is another choice. The crooks literally lasso those bullet cameras.
Axis makes terrific cameras, but they’re also about 10-20x as expensive as most of the products discussed in this article.
No argument Axis gear is expensive. I still have the ISC West app on my phone. I have 87 vendors under IP cameras. You can burn a lot of time figuring out who makes gear on par with Axis. It is kind of buying IBM back in the day.
You could probably cut it down to less than two dozen camera vendors if you stick to ONVIF members, depending on the profile.
For individual security cams and security cams by Common Vulnerabilities and Exposures (CVE), do a do search by vendor name at CVE and CERT databases.
I bought one of these a couple years ago to use as a baby monitor. Unfortunately I wasn’t able to use it locally after blocking its MAC address on my firewall so into a drawer it went.
The larger problem that many people fail to take into account is the idea of using anything that is connected to a central controller. Sorry, but I am not a fan of Ring, Google, or Amazon as if any of them ever get hacked the hackers have potential access to EVERYONE’s data.
There are safer alternatives. Setup everything on your home network and VPN in to get access. It is not as easy as logging into a cloud URL, but it is safer IMO.
This is great advice that I tell many people. Get a good router, setup DDNS, and use a VPN to connect to IOT devices that are otherwise blocked from the Internet.
Of course, this requires a decent router which not everyone will want to buy. And the VPN solution doesn’t work for any IOT device that needs to alert in real-time. So no doorbells, cameras that you want to trigger on motion, or anything that needs to send outbound traffic unsolicited by the user.
I disable ALL P2P – on individual devices, and at the Firewall.
Really, if necessary? Port forwarding with translation is not that hard.
To boot – who exactly knows WHAT “secret wormholes” P2P establishes?
Is your firewall/router disable “P2P” option only for recognized application layer protocols? Some router makers simply group known P2P protocols like torrent, etc. But it doesn’t actually block UDP hole punching.
UDP hole punching takes advantage of UDP’s connectionless nature, and as long as the keep-alive beacons are flowing outbound, the state table will allow inbound from the same IP/port pair. It doesn’t really consider it a Peer 2 Peer type Layer 7 protocol.
Port Forwarding is nice, in a sense that the user knows exactly what ports are open. But really, the user still doesn’t know what traffic is flowing through it.
For IP cameras and other IOT devices where consumers want to connect clients from anywhere… there still needs to be a rendezvous server that tells those clients what IP/ports to connect home.
Which means this security is still in the hands of that unknown cloud server. And if they protect it with a simple/guessable UID and default/weak password… then it is the same threat, regardless of whether or not the home device used UDP hole punching, UPnP, PMP-Nat, or required manual port forwarding.
The better solution is to get rid of the rendezvous servers and use DDNS to give your home network a unique name that resides on DNS servers. Then manually set up the clients with the DNS name the port.
This way, the cloud provider doesn’t even need to know where you are at… and less risk of them compromising that info.
Don’t like the idea of port forwarding. Bad guys can scan for open ports and compromise rdp if I’m not mistaken.
To Andrew’s point, it is way safer to find devices that DO NOT need the internet to work, and then setup all of it premise at your home, then VPN in to get access.
The problem with this is that, most DIY security cameras require planning, IT setup, wire runs, drilling, time, and additional tools. And most home owners DO NOT want to do that.
If you have these devices, the best thing to do is to set them up, place them on there own subnet/VLAN, and firewall/PiHole them.
On a different topic:
Data thieves are gathering up tons of data on people, often without them knowing it. Because the contracts you “agree to” online are more and more outrageous.
Is there a way to find out who has data on you?
Is there are way to post a Do Not Use flag on personal data, etc.? As in, the “Right of Publicity,” etc..
Chinese crap.
It’s not bad enough that they polluted their own air and water so bad that companies are moving out of Beijing just because they can’t even breath. Now the jackasses have to totally pollute the Internet with their crap also. How is this not different from melamine in Chinese milk or lead in Chinese children’s toys? Where is the FTC, which should be protecting us from harmful foreign imported products?
So what are the real life dangers of this? Somebody somewhere can see my living room. And?
They could potentially upload malware to your device that is behind your firewall. From there they could attack any system on your network, or worse. Or, they could use your device and network to proxy malicious activity online, such as credential stuffing attacks, account takeovers and other types of cybercrime.
https://krebsonsecurity.com/2016/10/iot-devices-as-proxies-for-cybercrime/
The biggest risk is that these P2P weaknesses will allow some bad guy(s) to a create a truly monster botnet, just like they did with Mirai. If you’re unfamiliar with Mirai, it’s been involved in launching some of the biggest DDoS attacks the Internet has ever seen.
>. Or, they could use your device and network to proxy malicious activity online,
At the individual level, this is a bigger concern than a massive botnet. Imagine dealing with the 6AM knock at the door based on a warrant for distribution of child pornography because they subverted a web cam to host the content.
A good investigator could sort this out quickly. An untrained investigator would tie you up in the system for years.
That’s certainly what worries me the most. For the other stuff, anyone spying on me will die of boredom, guaranteed.
It’s certainly valid to say one does not have much of significance to spy on or steal…
But let’s be careful not to extend that to “therefore I don’t care if everyone is constantly spied upon or everything everyone has is stolen…” for if one truly doesn’t care about keeping any of their stuff, they might as well put it all in the garbage, and have no stuff. or if they truly don’t care about keeping anything private, they might as well remove all doors, curtains, clothes, etc, and publish all their bank details and passwords publicly, etc… (no, don’t do any of this, I’m just cautioning against absurdity by describing it…)
We are a startup that built our Guard Dog product specifically to product home automation/smart home devices. Our strategy is IIPP. Isolate the devices onto their own subnet, Identify them, Profile their behavior and protect the home by blocked unwanted and unexpected traffic.
We are on kickstarter here if you are interested:
https://www.kickstarter.com/projects/199226421/guard-dog-protecting-your-smart-home
I read P2P and it reminds me of file sharing services with illicit torrent junk and dark web criminals. For that reason alone, I’d never use such devices.
This article mirrors similar information as the one in October 2018, and earlier articles. Repeatedly, KOS points out that these Chinese-made IOT devices are flawed.
I disagree; these are not flaws. These devices are intentionally designed by the Chinese for spying and it’s not an accident.
https://krebsonsecurity.com/2018/10/naming-shaming-web-polluters-xiongmai/#comment-474917
I’ve instituted the finest security you could imagine. I have nothing worth stealing….. even my identity is worthless. Oh wait , I guess if you could use my Arduino or Raspberry Pi to steal my Social Security , well you’d still be starving. Neither the Russians nor The Chinese need my data when they already have pwn’d our President. As any Battlestar Galactica fan knows no network is ever safe.
KrebsOnSecurity is full of articles that explain numerous times how criminals DO value your identity, email, IOT, etc… even if you cannot fathom how it may be valuable.
If you don’t value your stuff, please get rid of it, so that the rest of us are not constantly attacked by it….
Ah, yes. Internet connected cameras and microphones purchased to place in ones home in order to accomplish absolutely trivial things that could be done with a smart phone or PC. Brilliant.
Brian
Great insights —
What do you make of products like OpenDNS that claim to address these issues?
Thanks
Charles
If a device chooses to use an IP address w/o DNS, OpenDNS won’t help you…
The right approaches are:
1. Pay for decent products w/ actual support and firmware updates
2. Set up a separate network for I[di]oT devices
3. Make sure that your router can severely restrict traffic to-and-from such devices. Preferably w/ notifications for changes in traffic behavior.
Chinese Internet enabled devices are a risk.
I but them on their own VLAN and SSID where feasible, and always blocks them from gaining Internet access no matter what VLAN they are on.
I am still aware, that there is a risk that the devices will switch IP/MAC and do a heartbeat once in a while to contact the chinese government C&C server. I see them all as trojans.
Maybe it is not a problem for me if the chinese takes control of my outdoor IP cams (from respectable brands like Dahua and HikVision), but I see them as a risk to the rest of the network they can see, and to national infrastructure.
It doesn’t matter that they’re isolated to a separate or guest network. Once infected, they will consume resources that should have gone to your main or home network. And they will get infected, as designed.
If you pay for a big data plan or extra broadband speeds, you may never notice the leaking pipe until your ISP sends you a disconnection notice for excessive usage. If your plan is more modest, the data loss will be noticeable, but you’ll be powerless to stop it.
Either way, you’re tempting fate to kick you in the knees.
The best bet is to get IOT devices designed for security, or forgo them entirely.
There is no need for most IOT devices that cannot be met through CCTV, ADT (or similar service), or a good neighbor.
HikVision is hardly reputable. There is a reason those cameras are banned for use by federal government. If you have them, replace them.
I have the Nest doorbell camera and (not yet installed) Nest cameras. Does anyone have any knowledge of their security vulns, resources with info on them, etc…? Greatly appreciated. Thank you.
The primary vulnerability is that you’re a target for violence by anyone who notices you’ve installed a device that gives Google a 24/7 view of your neighbors. It marks you as the sort of person who deserves to be encouraged to move away.
If you are determined to let Google spy on you and your neighbors, shame on you. Here is additional information about Nest vulnerabilities:
https://dynamarksecurityrichmond.com/vulnerabilities-of-nest-security-cameras/
These device-specific vulnerabilities are one reason why it is valuable to put IoT devices behind an IoT gateway application. Ideally such an app would run on the home/local network router or broadband modem (assuming the modem has router/firewall capability), and be able to manage firewall settings. Mozilla’s open source WebThings Gateway application (iot.mozilla.org) is being integrated into OpenWrt, so that it can run on a router. Then consumers don’t need to configure all these firewall rules themselves — Mozilla’s IoT team will help implement the protections consumers need and deserve, and with the support of security experts like this article points out, keep them as safe as possible.
Any info on the “Blink” products? Not to mention Alexa stuff…… sigh.
I have a couple of Ubiquiti cameras at my home. They are controlled by an on prem controller but made available to the internet via video.ubnt.com.
Ubiquiti seems to be really on top of problems and updates firmware regularly. They certainly don’t use P2P.
I feel like it is a quality brand both hardware and software wise. Like Axis, they are not the cheapest hardware but having something maintained long term costs money.
Spyware in the IoT is quite possibly the most troubling new cyberthreat, given the mass adoption of “smart everything”… smart toys (for our kids), smart homes, smart wearables.
More on the topic here: https://www.informationsecuritybuzz.com/articles/spyware-in-the-iot-this-years-biggest-security-threat/
Brian, not necessarily the only solution is to avoid purchasing or using IoT devices that advertise any P2P capabilities. A real-time proactive cybersecurity solution for IoT devices can solve this issue.
I’d love your thoughts about our blog post on P2P Hole punching in Home IoT and what can be done to ensure the privacy and security of the users. check it out here –
https://firedome.io/blog/p2p-hole-punching-in-home-iot/
I am qxiang, the developer of iLnkP2P.how can i voice out my words
we are a small company, we provide the communication components (iLnkP2P) to let the device can easy access, but as you known, a device solution is combined by much components, a communication component can not be reponsable for the device whole security, any questions please contact us, not just say other say,please,we are fallen a big problem but can not voice out our views
I think your response is typical for products made in China. It is great that hundreds of manufacturers like yourself have driven down costs. But the lack of security awareness is evident in your comment.
The communications component, as you call it, is critical to security of the whole system. And just because you didn’t develop it yourself, but rather selected it as a standard, doesn’t absolve you of due diligence. The security is still your responsibility.
If that means you spend a bit more on supply chain security, or develop better mitigating controls to make up for the obvious gaps in the protocol, then that is your responsibility.
Vendors like yourself seem to give no thought to the security of the 3rd party components or even try to develop a way to patch after the inevitable flaw is discovered. And that is why you deserve the reputation you get for poor security.