Canadian authorities have arrested and charged a 27-year-old Ontario man for allegedly selling billions of stolen passwords online through the now-defunct service Leakedsource.com.
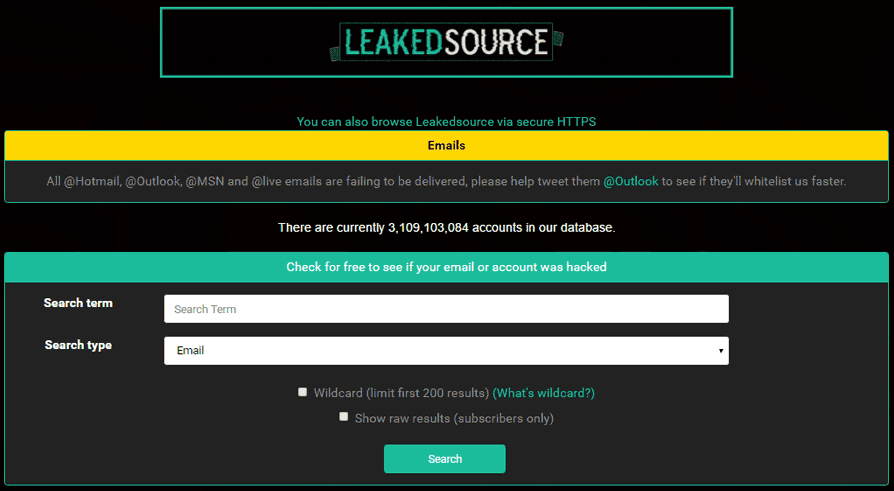
The now-defunct Leakedsource service.
On Dec. 22, 2017, the Royal Canadian Mounted Police (RCMP) charged Jordan Evan Bloom of Thornhill, Ontario for trafficking in identity information, unauthorized use of a computer, mischief to data, and possession of property obtained by crime. Bloom is expected to make his first court appearance today.
According to a statement from the RCMP, “Project Adoration” began in 2016 when the RCMP learned that LeakedSource.com was being hosted by servers located in Quebec.
“This investigation is related to claims about a website operator alleged to have made hundreds of thousands of dollars selling personal information,” said Rafael Alvarado, the officer in charge of the RCMP Cybercrime Investigative Team. “The RCMP will continue to work diligently with our domestic and international law enforcement partners to prosecute online criminality.”
In January 2017, multiple news outlets reported that unspecified law enforcement officials had seized the servers for Leakedsource.com, perhaps the largest online collection of usernames and passwords leaked or stolen in some of the worst data breaches — including three billion credentials for accounts at top sites like LinkedIn and Myspace.

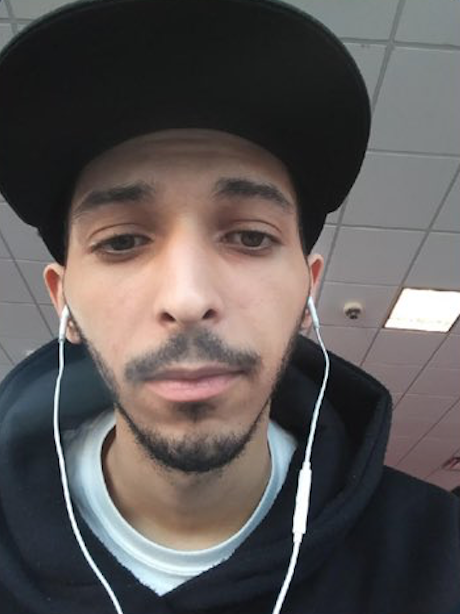
Jordan Evan Bloom. Photo: RCMP.
LeakedSource in October 2015 began selling access to passwords stolen in high-profile breaches. Enter any email address on the site’s search page and it would tell you if it had a password corresponding to that address. However, users had to select a payment plan before viewing any passwords.
The RCMP alleges that Jordan Evan Bloom was responsible for administering the LeakedSource.com website, and earned approximately $247,000 from trafficking identity information.
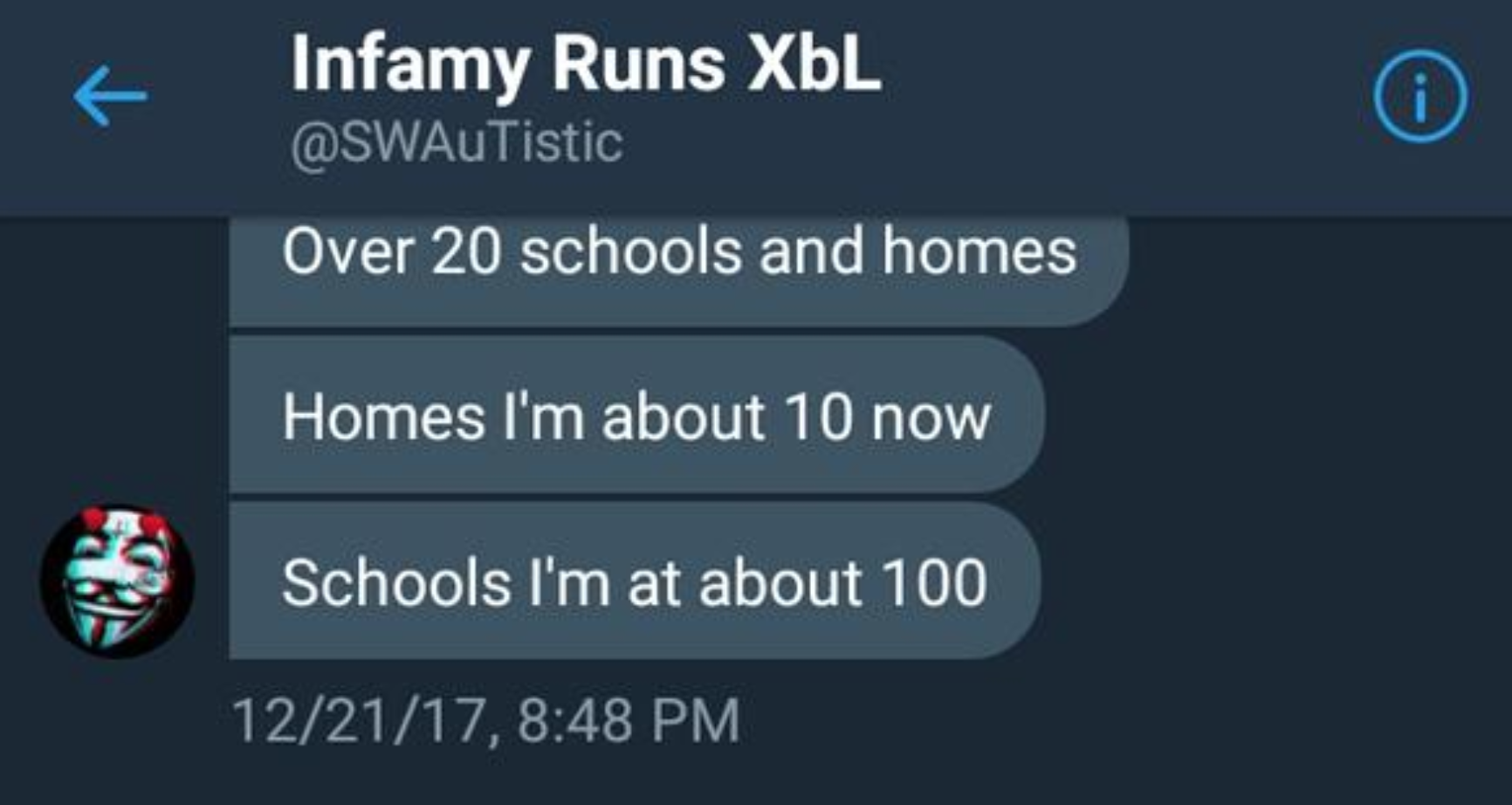
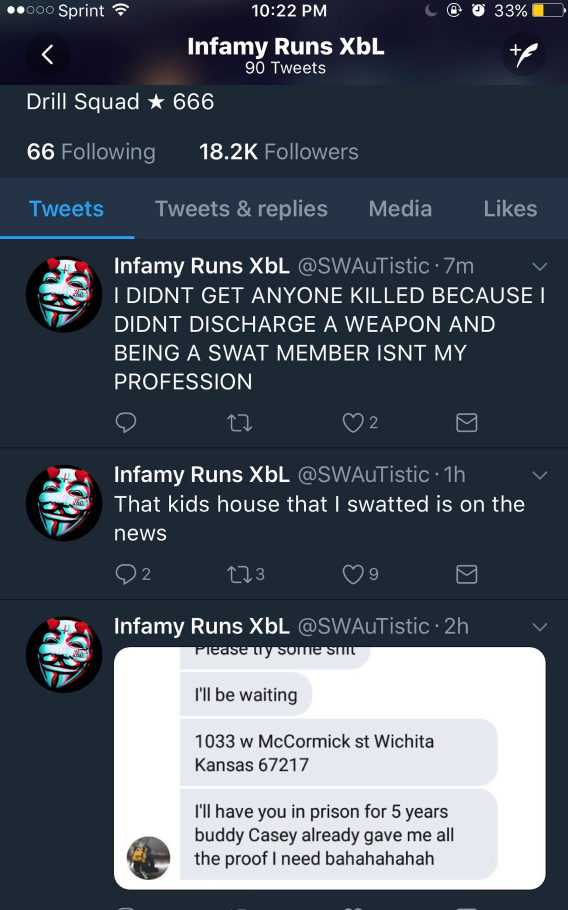
A February 2017 story here at KrebsOnSecurity examined clues that LeakedSource was administered by an individual in the United States. Multiple sources suggested that one of the administrators of LeakedSource also was the admin of abusewith[dot]us, a site unabashedly dedicated to helping people hack email and online gaming accounts. Continue reading




 Last week’s story,
Last week’s story, 
 This past year KrebsOnSecurity published nearly 160 stories, generating more than 11,000 reader comments. The pace of publications here slowed down in 2017, but then again I have been trying to focus on quality over quantity, and many of these stories took weeks or months to report and write.
This past year KrebsOnSecurity published nearly 160 stories, generating more than 11,000 reader comments. The pace of publications here slowed down in 2017, but then again I have been trying to focus on quality over quantity, and many of these stories took weeks or months to report and write.