The Web site for Fortune 500 real estate title insurance giant First American Financial Corp. [NYSE:FAF] leaked hundreds of millions of documents related to mortgage deals going back to 2003, until notified this week by KrebsOnSecurity. The digitized records — including bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images — were available without authentication to anyone with a Web browser.

First American Financial Corp. Image: Linkedin.
Santa Ana, Calif.-based First American is a leading provider of title insurance and settlement services to the real estate and mortgage industries. It employs some 18,000 people and brought in more than $5.7 billion in 2018.
Earlier this week, KrebsOnSecurity was contacted by a real estate developer in Washington state who said he’d had little luck getting a response from the company about what he found, which was that a portion of its Web site (firstam.com) was leaking tens if not hundreds of millions of records. He said anyone who knew the URL for a valid document at the Web site could view other documents just by modifying a single digit in the link.
And this would potentially include anyone who’s ever been sent a document link via email by First American.
KrebsOnSecurity confirmed the real estate developer’s findings, which indicate that First American’s Web site exposed approximately 885 million files, the earliest dating back more than 16 years. No authentication was required to read the documents.
Many of the exposed files are records of wire transactions with bank account numbers and other information from home or property buyers and sellers. Ben Shoval, the developer who notified KrebsOnSecurity about the data exposure, said that’s because First American is one of the most widely-used companies for real estate title insurance and for closing real estate deals — where both parties to the sale meet in a room and sign stacks of legal documents.
“Closing agencies are supposed to be the only neutral party that doesn’t represent someone else’s interest, and you’re required to have title insurance if you have any kind of mortgage,” Shoval said.
“The title insurance agency collects all kinds of documents from both the buyer and seller, including Social Security numbers, drivers licenses, account statements, and even internal corporate documents if you’re a small business. You give them all kinds of private information and you expect that to stay private.”
Shoval shared a document link he’d been given by First American from a recent transaction, which referenced a record number that was nine digits long and dated April 2019. Modifying the document number in his link by numbers in either direction yielded other peoples’ records before or after the same date and time, indicating the document numbers may have been issued sequentially.
The earliest document number available on the site – 000000075 — referenced a real estate transaction from 2003. From there, the dates on the documents get closer to real time with each forward increment in the record number.
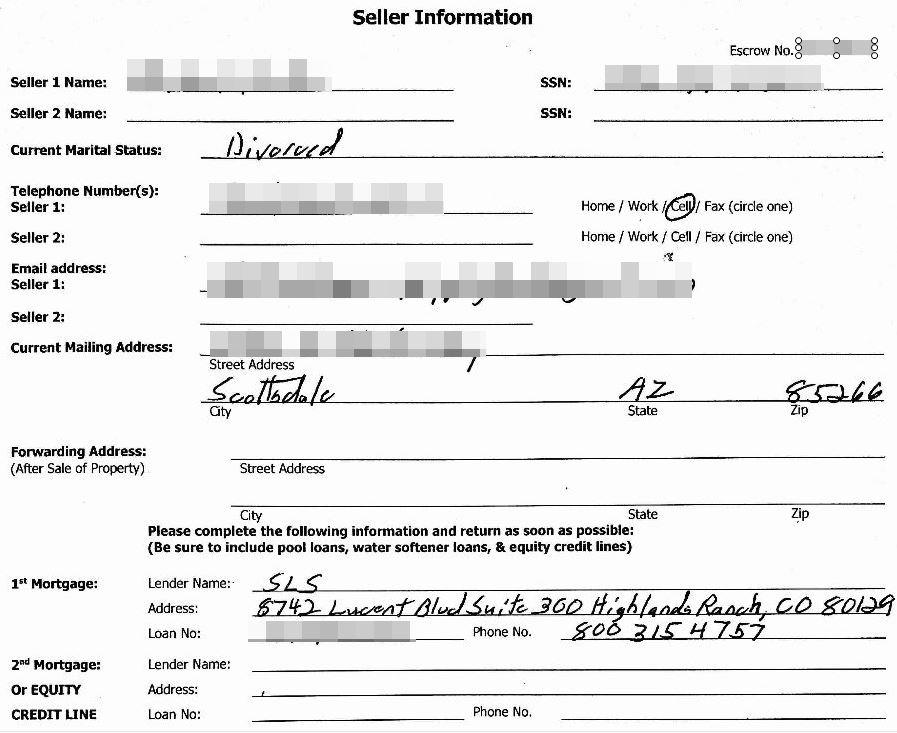
A redacted screenshot of one of many millions of sensitive records exposed by First American’s Web site.
As of the morning of May 24, firstam.com was returning documents up to the present day (885,000,000+), including many PDFs and post-dated forms for upcoming real estate closings. By 2 p.m. ET Friday, the company had disabled the site that served the records. It’s not yet clear how long the site remained in its promiscuous state, but archive.org shows documents available from the site dating back to at least March 2017.
First American wouldn’t comment on the overall number of records potentially exposed via their site, or how long those records were publicly available. But a spokesperson for the company did share the following statement:
“First American has learned of a design defect in an application that made possible unauthorized access to customer data. At First American, security, privacy and confidentiality are of the highest priority and we are committed to protecting our customers’ information. The company took immediate action to address the situation and shut down external access to the application. We are currently evaluating what effect, if any, this had on the security of customer information. We will have no further comment until our internal review is completed.”
I should emphasize that these documents were merely available from First American’s Web site; I do not have any information on whether this fact was known to fraudsters previously, nor do I have any information to suggest the documents were somehow mass-harvested (although a low-and-slow or distributed indexing of this data would not have been difficult for even a novice attacker).
Nevertheless, the information exposed by First American would be a virtual gold mine for phishers and scammers involved in so-called Business Email Compromise (BEC) scams, which often impersonate real estate agents, closing agencies, title and escrow firms in a bid to trick property buyers into wiring funds to fraudsters. According to the FBI, BEC scams are the most costly form of cybercrime today.
Armed with a single link to a First American document, BEC scammers would have an endless supply of very convincing phishing templates to use. A database like this also would give fraudsters a constant feed of new information about upcoming real estate financial transactions — including the email addresses, names and phone numbers of the closing agents and buyers.
As noted in past stories here, these types of data exposures are some of the most common yet preventable. In December 2018, the parent company of Kay Jewelers and Jared Jewelers fixed a weakness in their site that exposed the order information for all of their online customers.
In August 2018, financial industry giant Fiserv Inc. fixed a bug reported by KrebsOnSecurity that exposed personal and financial details of countless customers across hundreds of bank Web sites.
In July 2018, identity theft protection service LifeLock corrected an information disclosure flaw that exposed the email address of millions of subscribers. And in April 2018, PaneraBread.com remedied a weakness exposing millions of customer names, email and physical addresses, birthdays and partial credit card numbers.




They said, “privacy and confidentiality are of the highest priority” and I wonder ¿what kind of clowns are they? Because they are not the funny ones. This kind of sh*t should ensue a class-action without further ado. They were totally irresponsible. Plus, if they say it’s their “highest priority” and they failed about that, imagine how good they are at the rest of the things they do.
+1.
It’s indeed interesting to note how nearly every big business which has experienced some major data leak, breach, etc. etc. on which Brian has reported – always come up with the same, meaningless, worn-out PR line(s) about how important their customers’ privacy, etc. is to them.
Yet, it is all too obvious they aren’t very proactive about such things – only reactive……and THEN…only when someone like Brian can get through to them to make them “see the light” so-to-speak!
They certainly didn’t pay attention to one of their own customers who first reported the problem to them!
Stupid crap like this what happens when you hire people into your IT department with little experience developing sophisticated systems in order to lower the cost of labor.
This type of stuff happens in most companies. What you get is junk that often needs to be re-designed and re-developed.
Why pay X when you can pay .5X? Because in the long run, the mess they produce will cost you 3X in customer complaints, federal fines, technical maintenance and overpaid consultants to fix the mess.
I’m thinking that unless they offshores their it and cyber security, then it is even money at least that someone reported this or similar risks to their board. The board probably has someone review their cyber policy and decided they were covered if they got breached, so stfu about this please mr. it person. Board math doesn’t even worry about pii protection or consequences of them letting that get breached – that is something silly proles worry about, not your big co. betters.
I’m guessing that this used to be an internal document management system that some bright boy decided would be a good idea to expose to the web for convenience of document sharing.
Sadly, protection of personal information is a high priority for these companies – but not as high as 480 other things that drive margins and revenue, since it is a cost center, not a revenue center, cyber security is just not something the big dogs, and little dogs for that matter, care to invest in.
This only gets fixed if they suffer financially and those who failed get incarcerated for their negligence. Make no mistake, this was sheer negligence, and the board in all likelihood knows it. I think board minutes are publicly available for publicly traded companies, so a little digging may be in order.
People have been raising such concerns for years. For many, it’s the last time they ever receive work or even hear from the company. The message is clear: keep your mouth shut or you will be blacklisted.
DJ – source on that please? Not arguing but I’d like to know how you know that people have been reporting this for years and told to go sit in a corner.
Experience.
I’ve been a notary public and a signing agent. One specific title company stopped talking to me after mentioning their similar practice. Another plainly told me that there was no security or privacy concerns and then took 5 months to send me the money they owed me for a signing. Before that I would get paid within a month. I was also quietly dropped from an index of signing agents run by a different title company right after. That same index sold their list of agents to spammers and I’m still getting spam from fake signing agent lists (and I found out who it was because someone didn’t know about editing or BCC:.)
Side note: The docs were typically either unsigned PDFs or Word docs that could be altered by anyone. Also, smtp or ftp were used for transfers. No encryption at all.
This was completely preventable and reeks of gross negligence
and you know this how?
Because any developer with 1/10th of a functioning brain knows you can’t protect anything using sequential numeric IDs. Resource enumeration is one of the oldest and easiest attacks that exists. Ideally there would be authentication required to view these documents, but at the very least, the identifiers should be UUIDs that can’t be guessed, not just every sequential number between 75 and 999999999.
It’s lacking the most basic user authentication and authorization. You don’t mess up this bad unless security was not considered in the design at all.
My guess: Their IT people had experience with using closed networks such as CompuServe, Tymnet, etc., which were (are???) still in existence and where private or unpublished services were easy to hide, and presumed that the internet was the same thing.
Also, any competent QA person who does web testing and knows the slightest bit about security would immediately notice what appeared to be a simple number in a querystring parameter and try modifying that number by one digit to see if they got another document.
If it was ‘secure by design’ they never would have used a simple indexable ID in the first place.
If they had a competent QA team that knew anything about security, even if the developers coded it this way, bugs would have been filed to fix it before release.
If they had a competent security team, THEY could have noticed this during audits and testing by that team.
This isn’t rocket science, There’s a couple of terms for it “Insecure Direct Object Reference is the more technical.. “ID Spoofing” the more friendly way of putting it. This is not, not some obscure convoluted attack that would require a sophisticated person to find.. Once you see how your document is being found, it’s literally a 5 second task to alter the URL ever so slightly and press enter and see if you are shown something you ought not see. .
This is how a college student who’s had no exposure to security concepts would code things, NOT a seasoned professional who understands how to make things secure by design.
In addition, consider that someone was trying to report this to them and they were NOT paying any attention to them. That person had to rope in Krebs, and then they finally took it seriously (and we’ve no idea how many people Krebs had to go through before someone was found that would listen.
NOT a seasoned professional who understands how to make things secure by design.
That’s an industry problem for even seasoned coders because secure coding are elective classes and not just taught out the gate throughout all coding classes.
There is quite the lengthy discussion about this very topic over at Hackernews’s comments on this story
https://news.ycombinator.com/item?id=20005230
Who found it?
Ben Shoval.. ahh
A like of new incompetent CISOs is already forming outside the HR office.
Wouldn’t even the most elementary PEN test find this?
Not only a pen test but an application security test (hack). You want to see what’s exposed on the web pages for anonymous and regular users; for the latter, you also want see if a regular user can easily see things he or she shouldn’t (e.g., vertical/horizontal security attack). It’s do-able but assume an app is hackable. You don’t want to make it easy and have enough mitigating security controls to limit the damage.
Now how would a simple pen test find it, if the necessary step was a valid URL generated from a legit account? LOL …
Yes and no. Sequential likely not but that no auth or User1 can view User2 likely. Was a pentest performed? Was it black box and what was scope? Many pentests are scoped to try not let testers find things rather just check a box that one was performed.
External Pen test performs a routine of tests for known and well documented vulnerabilities from the *OUTSIDE*!
How can a typical Pen test discover this vulnerability that is specific only to First American ?!. The pen test would require a FA customer user/id and a provided URL!
So the answer is NO, a simple Pen test won’t discover this!
“You give them all kinds of private information and you expect that to stay private.”
This statement doesn’t go far enough. Not only do we give our private information, but we HAVE to give it. If we don’t, we can’t make the purchase. It’s like this throughout all industries.
It’s not enough to do business with them. I understand trading information and money for goods, so each party feels comfortable with the business deal. These companies take it further by gleaning our information to sell to others, who then hound us incessantly, and put us more at risk to fraud.
Then if you show concern for YOUR information, they are happy to sell you services to keep you “safe”. I’m specifically thinking of the credit bureaus with this one. Want to freeze your credit? Pay us. This is one time where I think the government did the right thing in making it illegal for them to charge you for it, but I’m sure they’ll find some loophole.
@JS: Actually the recent amendment to the Fair Credit Reporting Act giving a free credit freeze applies ONLY to nationwide credit reporting agencies.
So Equifax, Experian and TransUnion only.
Not ChexSystems, Innovis, National Consumer Telecom & Utilities Exchange, The Work Number etc.
A start, but not great.
This has been an issue since at least 2011, if not before. Citibank exposed 200K+ accounts because user could diddle their own account numbers and see someone else’s account information. Have we learned nothing in the ensuing years?
https://consumerist.com/2011/06/how-hackers-stole-200000-citi-accounts-by-exploiting-basic-browser-vulnerability.html
I have a suggestion for First American and any or all present or past customer who have utilized their service, if you suspect any fraudulent activity with your financial or other relevant personal information that may have been exposed, First American should make available (to those that their financial information is in jeopardy) to pay for at a minimum one year credit monitoring service.
Free credit monitoring is the standard reflex offer in these cases. It really is a joke.
No, 1ooo per exposed record. Until thte cost of non compliance greatly exceeds the cost of compliance nothing will ever change.
1000 years might be too much. But only one year sounds like it could fall short
This is where regulations like GDPR in the EU and CCPA in California should help. The fines under GDPR are the greater of €20m (just over $20m) or 4% of global annual revenue. That make these sorts of leeks worth preventing, as you say Rick, until the fines out strip the cost of implementation what’s the insentive?
Exactly. So much negligent and even criminal behavior continues because it’s cheaper to pay the fine than stop the bad behaviors. Those bad behaviors are profitable, and since the fines are only a fraction of the profits… these bad actions continue. Of course, you and I are held to different standards, if I steal something, I’m paying way more in penalties than whatever it is I stole. If I defraud someone, I’m taken to the cleaners. Heck, if I post something that offends sensibilities of a tiny demographic, I can have my livelihood taken away via deplatforming or demonetizing my content on YouTube. It really is a bizarre system, and completely not an accident.
The first thing I saw the California state flag on the front page. Next, I read “Santa Ana, Calif.-based First American KrebsOnSecurity confirmed the real estate developer’s findings, which indicate that First American’s Web site exposed approximately 885 million files, the earliest dating back more than 16 years.,,, No authentication was required to read the documents… title insurance agency collects all kinds of documents from both the buyer and seller, including Social Security numbers, drivers licenses, account statements, and even internal corporate documents if you’re a small business… “-Brian Krebs
Gad, that is the whole Cookie Jar for personal Information.
Title companies do collect very accurate and sensitive data on real estate transactions from not only California buyers and seller but US buyers and sell and possibly European buyers and sellers.
I took a quick look at California privacy laws in Wikipedia:
“Companies that become victims of data theft or other data security breaches can be ordered in civil class action lawsuits to pay statutory damages between $100 to $750 per California resident and incident, or actual damages, whichever is greater…” – California Consumer Privacy Act, Wikipedia.
ht tps://en.wikipedia[.]org
/wiki/California_Consumer_Privacy_Act
[link fractured for safety]
Talking about web crawlers and web scrappers all of the big web firms from Face book, Google, Twitter, and even down to. Acxiom, military contractors, DHS, TSA. greasy data brokers and so on.
All of First America’s data could end up on the dark quite quickly.
This is horrible. After reading “Legal Threats Make Powerful Phishing Lures” I wonder who will be the first con-artist to say “Hi, your house has been forclosed…” I am sure First America has good lawyers but I am not so sure they will win in the long run.
The only way this garbage ends is if there is a federal law that fines them $10,000 for every record which is exposed. When computer insecurity costs money then everyone will pay more attention. Plus the programmers must be personally responsible for some percentage of it and sign off on its security.
Make that fine association a nonlinear one, e.g. $10,000^n, where n=number of records exposed. THAT will get everyone’s attention, PDQ.
A few years ago, I had an interview with their IT department. Needless to say, their IT management displayed pure incompetence from the beginning. This is the kind of quality, or lack thereof, that permeates First American.
I take it from your post that you weren’t hired ?! 😉
The company is comprised of several subsidiaries. One division’s IT department could be quite different (with it’s own policies and prosecuted) from another.
Nice, first a huge layoff right before Christmas and then this kind of irresponsibility. Pathetic.
I will not be using FA for any title insurance needs.
Tell em
I’m so tired of this total ignorance on security and the lies in company statements. Call it what it is – criminal negligence. Throw some people in jail and sue them to oblivion.
Seems like you can’t trust nobody anymore everything in the world is being exposed it’s a damn shame that we can’t keep anything private next to be wondering what we’re doing in the bathroom
It’s anybody not nobody. Just an FYI before you leave a comment make sure your grammar is correct!
Hey grammar nazi,
Learn to use commas.
Krebs, could you please also contact archive.org and ask them to take down their cache of these private documents?
Do it yourself, if you care about it. Brian has other things to do, don’t you think? Like ferreting out the NEXT moronic breach.
And while you’re at it, ask Google really nicely to delete all of their cached copies of these documents too. (Yes, there is a small mountain of them cached already by Google too.)
As a general rule, this is a task that the web site owner (i.e. First American) should perform.
It’s pretty simple, just some changes to robots.txt [1]. They can reach out by email to the archive for help…
[1] http://www2.sims.berkeley.edu/research/conferences/aps/removal-policy.html
I recently did a transaction with FirstAm and I asked them specifically and repeatedly about how they planned to keep my data secure. I was uncomfortable with all the personally invasive information they wanted – they ask for a lot. Let me tell you what the escrow officer told me:
Except for the Settlement Statement and sales contracts signed by multiple parties, the forms we fill out and send to FirstAm are completely private to us individually. All the affected parties can see those.
Completed forms are all encrypted, scanned, and the hardcopies are thrown away.
After the transaction is done, FirstAm has nothing left afterwards except the last 4 digits of a customer’s SSN.
However FirstAm maintains encrypted copies for 7 years for audit purposes. FirstAm employees cannot decrypt or access the encrypted copy, only the auditor can.
Well, I guess she forgot to say, “FirstAm employees cannot access the encrypted copy, but everyone else on the internet can.”
I am investigating this issue. If you are willing to discuss further, please call me. Thanks.
I seriously doubt that escrow officer’s satement. For one thing, they have to keep most if not all the paper for at least the life of the mortgage, whether it’s been scanned, filmed, photocopied, whatever. Documents are scanned but also transferred to an archive site after a time. Businesses really wish they could just destroy the paper once it’s been scanned but they would be in legally treacherous waters and they know it.
As Chief Executive Officer at FIRST AMERICAN FINANCIAL CP, Dennis J. Gilmore made $8,402,957 in total compensation.
Maybe they should drop the comp $1M or so and hire some security folks that know what they are doing to protect customer data.
Or, maybe it’s easier to do what Ford did in the Pinto days, and not fix the problem but rather pay the lawsuits because it’s cheaper.
Severe financial penalties must be levied, and not a slap on the wrist. This is really wrong.
Why only $1M? Why not all of it — by firing him, before litigation even starts?
Now the question is: will mainstream media pick this up? (So far, only USAToday)
Meanwhile, from FAF’s own website:
Imagine the possibilities of what you can build with First American property-centric data.
Yes, just imagine… yikes!
What a Shame!!!This is what happens when you throw out Smart People in lieu of saving some Pennies in the name of OPEX.
You have all the Nuts on TOP (CISO,CIO,EA and all the C-level) execs who do not understand how Technology in IT works. They don’t have even the slightest CLUE..what it takes to run a Tech Shop for the Business. People First is a Sham!!
Let the real people handle these jobs and throw out the quacks instead of the Smart People. All the claims on Security is just a Eye Wash.
This is Web-Application 101 – There is something called as URL Obfuscation or rather just do parameter encryption especially on Public Facing websites. This is really embarrassing and you have jeopardized Security information for Millions of your customer.
Also your IT InfoSec and C-Level’s NEED A OVERHAUL.
God save those poor souls whose information is Compromised. I am sure the Company is not competent to even figure out how much data is compromised or where to even start ?
Agree on C-level but you ask anyone in security if they know things wrong like this and I bet you most will say yes but not given resources to fix it. As long they documented it in risk register not much more they can do.
from NBC News (emphasis mine):
U.S. real estate title insurance company First American Financial Corp said on Friday it had learned of a DESIGN DEFECT in one of its production applications that had made possible unauthorized access to customer data.
A design defect???
Sequential numbers in URLs, probably. Not bad by itself and possibly state-of-the-art. But add any additional bug to it and you’re in deep trouble.
“Not bad by itself…”? are you kidding? the only security was obscuring the URL and that’s not bad? what would it take to be “bad”? indexing by name in plaintext and allowing searches that way from a landing page that advertises “find out everything you want to know about all of our customers’ private ID and financial information?
It couldn’t pass as a feature, certainly….
Its programmers fault, its security’s fault, its audits fault.
Listen the root issue is generally up top. Security normally has a long list of security issue but no $ or no people to implement the fix are top 2 reasons it does not get fixed.
Programmer are taught to code to make something work in a Mister Rogers world and not taught secure coding. Most run DevOps not SecDevOps and security is only involved after it is ready for production instead of through out the entire Dev process. Programmers time lines are laughable, you try write a novel under a time crunch.
Security or well IT to uppers it just a cost, it doesnt make money. Until the people with the $ start putting more into IT and Security this issue will never go away.
I had a friend who was taken for one of the BEC scams and I couldn’t figure out how the scammer was able to get all the details of the loan correct – this explains it perfectly.
I wonder if people who are scammed and can’t recover their funds can go after First American…
I see where you’re going but there are some practical limitations here. First American is involved in such a high percentage of overall real estate closing deals in the U.S. today that it would seem a bit like trying to prove that a company the size of WalMart had a credit card breach just by looking at common point of purchase (CPP) data from a few small banks.
The PCI DSS is a voluntary payment card security framework that isn’t legally enforced, but heavily recommended by the payment card industry (and it includes regular scheduled vulnerability scans). I wish they would pass legislation that would legally enforce PCI DSS not only to the payment card industry, but to all organizations/industries/etc… that hold extremely sensitive data. Good chance this would not have happened then.
Would also be nice if CISOs were required for these industries AND that CISOs were required to have IT security training to be given that title. I’m afraid what we are seeing are IT managers given the title just to satisfy some corporate requirement on paper.
I completely agree Managers are CLUELESS. Most CISO’s and upper Management are more focused just on the management track than being equally focused on the Technical track they lead.
A blind cannot lead an Army! Cannot rely anymore on FAF handling our Data Securely.
You need to know your stuff better and only then can you qualify to really lead that team from the top. This mainly goes to the CISO and CIO’s along with their Directs who are just Managers but very much INCOMPETENT on the Tech front.
Also surprising part was inspite of repeated attempts by Ben to notify about this issue nothing was done by FA Exec’s which shows lack of scruples and possible attempt to keep such a thing under covers than addressing the same on priority .
BOTTOM LINE – CIO, CISO barely show any Technical Prowess in their Profiles as they themselves don’t know much about Tech. Same goes with a lot of VP’s and Directors @ FAF(with what I understood from a friend).
FAF better be prepared for paying compensation for your negligence towards your duties and commitments.
To hack the loan data first you need to have the loan document number. Remember most people have zero need to view their online doc as they have hard copies at time of sale. Hackers are few although their deeds are done to many. I would be surprised if the site was ever hacked. The sale would have been on the dark web. Plus, it would have taken a unique situation where a hacker had a First Am loan doc and decided to audit the security of said site.
another misconfigured bucket? anyone with a leaked record snapshot this for the lawsuit
who posts a req like this – with this much detail? This is why the US needs GDPR. There’s no privacy without protection.
https://careers.firstam.com/job/9057078/cloud-solutions-architect-santa-ana-ca/
A problem well-known by insiders that has been neglected for years, protected and enabled by confidentiality and nondisparagement agreements, as well as by certain laws and fiduciary duty.
I am sincerely surprised that no one has already taken advantage of this. At least, as far as we know. But I suppose that will now change.
BTW, lawyers are really, really bad at this kind of stuff. Still.
^^^This !!!
” I would be surprised if the site was ever hacked.”
Within two months of a real estate closing handled by First American my identity was stolen and I found out about a corporate credit card being issued based on my credit. fortunately the address on my real estate purchase was included in the card application and I received a piece on mail that caused me to look into what was going on. My credit is frozen now!
I keep wondering, as Brian keeps diligently reporting & exposing this stuff, is this example of FAF just truly the tip of the iceberg?
I thought that when the US Gov’t OPM and Equifax (and others) breaches/failures occurred over the past 3-4 years, that all companies (small up to big, especially the bigs) would have been so freaked out that they set aside $$$ funds to make sure that they are, at the very least, taking care of the simple security-related stuff like this FAF incident.
I mean, just substituting numbers in a link and you were IN LIKE FLYNN at FAF? This qualifies as a major wowzer to me, like I would have absolutely lost $100 betting someone that there’s no way in heck something like this exists in 2019 at any major company. At least not for a company the size of FAF!
Is all of this stuff coming to light, is it truly an honest case where these companies simply have no idea of what and/or how they are exposed www-wise?
I am more than half-afraid of the answer…..i.e. I wonder if Brian is getting any info on the haphazard agglomerations of huge hospital alliances & consolidations that formed during the last 20 years, where their back-end web systems still today are rumored to be held together by hope, an ostrich-like posture (lack of knowledge about what was acquired), and copious amount of duct tape (read: marketing platitudes) to keep it all together. But I tell myself, that, no, you are making stuff up in my head.
Then I come here and read something like FAF, and I think……oh no.
What best way to secure my account from being accessed
Have you done any investigations involving our voting machines? Their vulnerabilities? Please, for the sake of our Democracy look into this. Thank you.