In early October, news leaked out of Russia that authorities there had arrested and charged the malware kingpin known as “Paunch,” the alleged creator and distributor of the Blackhole exploit kit. Today, Russian police and computer security experts released additional details about this individual, revealing a much more vivid picture of the cybercrime underworld today.
A statement released by the Russian Interior Ministry (MVD) — the entity which runs the police departments in each Russian city — doesn’t include Paunch’s real name, but it says the Blackhole exploit kit creator was arrested in October along with a dozen other individuals who allegedly worked to sell, develop and profit from the crimeware package.
Russian security and forensics firm Group-IB, which assisted in the investigation, released additional details, including several pictures of the 27-year-old accused malware author. According to Group-IB, Paunch had more than 1,000 customers and was earning $50,000 per month from his illegal activity. The image at right shows Paunch standing in front of his personal car, a Porsche Cayenne.
First spotted in 2010, BlackHole is commercial crimeware designed to be stitched into hacked or malicious sites and exploit a variety of Web-browser vulnerabilities for the purposes of installing malware of the customer’s choosing. The price of renting the kit ran from $500 to $700 each month. For an extra $50 a month, Paunch also rented customers “crypting” services; cryptors are designed to obfuscate malicious software so that it remains undetectable by antivirus software.
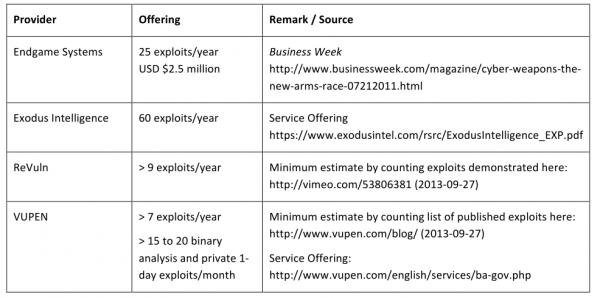
Paunch worked with several other cybercriminals to purchase new exploits and security vulnerabilities that could be rolled into Blackhole and help increase the success of the software. Paunch bought the exploits to fund a pricier ($10,000/month) and more exclusive exploit pack called “Cool Exploit Kit.”
As documented on this blog in January 2013 (see Crimeware Author Funds Exploit Buying Spree), Paunch contracted with a third-party exploit broker who announced that he had a $100,000 budget for buying new, previously undocumented “zero-day” vulnerabilities.
Not long after that story, the individual with whom Paunch worked to purchase those exclusive exploits — a miscreant who uses the nickname “J.P. Morgan” — posted a message to the Darkode[dot]com crime forum, stating that he was doubling his exploit-buying budget to $200,000.
In October, shortly after news of Paunch’s arrest leaked to the media, J.P. Morgan posted to Darkode again, this time more than doubling his previous budget — to $450,000.
“Dear ladies and gentlemen! In light of recent events, we look to build a new exploit kit framework. We have budgeted $450,000 to buy vulnerabilities of a browser and its plugins, which will be used only by us afterwards! ”







![fraudcheck[dot]cc resells bundles of anti-fraud services from legitimate providers like MaxMind.](https://krebsonsecurity.com/wp-content/uploads/2013/11/fchistory-copy-600x312.png)