Google this week made it easier for Android users to enable strong 2-factor authentication (2FA) when logging into Google’s various services. The company announced that all phones running Android 7.0 and higher can now be used as Security Keys, an additional authentication layer that helps thwart phishing sites and password theft.
As first disclosed by KrebsOnSecurity last summer, Google maintains it has not had any of its 85,000+ employees successfully phished on their work-related accounts since early 2017, when it began requiring all employees to use physical Security Keys in place of passwords and one-time codes.
The most commonly used Security Keys are inexpensive USB-based devices that offer an alternative approach to 2FA, which requires the user to log in to a Web site using something they know (the password) and something they have (e.g. a one-time token, key fob or mobile device).
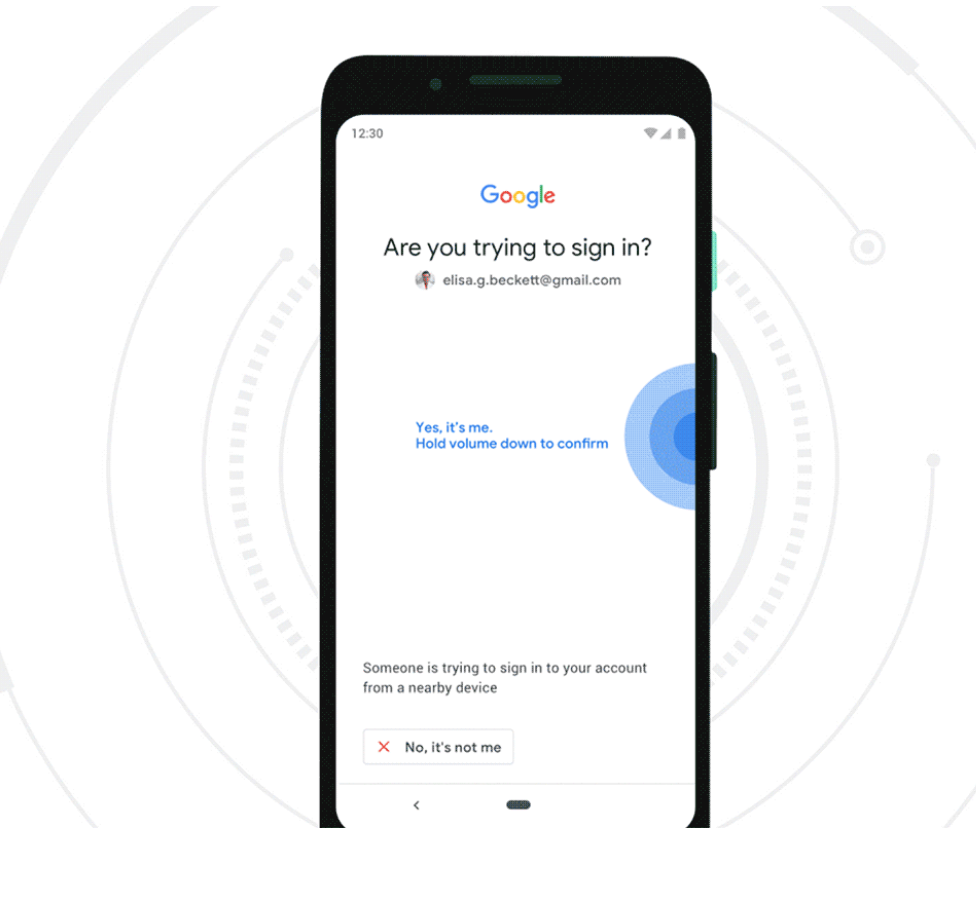
But Google said starting this week, any mobile phone running Android 7.0+ (Nougat) can serve the same function as a USB-based security key. Once a user has enrolled their Android phone as a Security Key, the user will need to approve logins via a prompt sent to their phone after submitting their username and password at a Google login page.
Many readers have expressed confusion or skepticism about how Security Keys can prevent users from getting hooked by phishing sites or clever man-in-the-middle attacks. This capability was described in far greater visual detail in this video last year by Christiaan Brand, product manager at Google Cloud.
But the short version is that even if a user who has enrolled a Security Key for authentication tries to log in at a site pretending to be Google, the company’s systems simply refuse to request the Security Key if the user isn’t on an official Google site, and the login attempt fails.
“It puts you in this mode….[in] which is there is no other way to log in apart from the Security Key,” Brand said. “No one can trick you into a downgrade attack, no one can trick you into anything different. You need to provide a security key or you don’t get into your account.”
Google says built-in security keys are available on phones running Android 7.0+ (Nougat) with Google Play Services, enabling existing phones to act as users’ primary 2FA method for work (G Suite, Cloud Identity, and GCP) and personal Google accounts to sign in on a Bluetooth-enabled Chrome OS, macOS X, or Windows 10 device with a Chrome browser. Continue reading




 According to security firm
According to security firm  Adobe’s Patch Tuesday includes security updates for its
Adobe’s Patch Tuesday includes security updates for its