Last week we looked at reports from China and Israel about a new “Internet of Things” malware strain called “Reaper” that researchers said infected more than a million organizations by targeting newfound security weaknesses in countless Internet routers, security cameras and digital video recorders (DVRs). Now some botnet experts are calling on people to stop the “Reaper Madness,” saying the actual number of IoT devices infected with Reaper right now is much smaller.
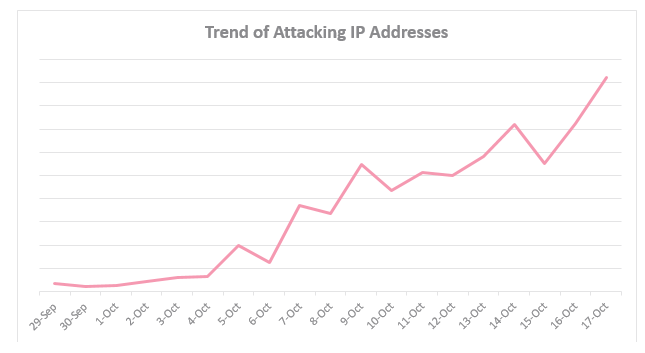
 Arbor Networks said it believes the size of the Reaper botnet currently fluctuates between 10,000 and 20,000 bots total. Arbor notes that this can change any time.
Arbor Networks said it believes the size of the Reaper botnet currently fluctuates between 10,000 and 20,000 bots total. Arbor notes that this can change any time.
Reaper was based in part on “Mirai,” IoT malware code designed to knock Web sites offline in high-powered data floods, and an IoT malware strain that powered most of the largest cyberattacks of the past year. So it’s worrisome to think someone may have just built an army of a million IoT drones that could be used in crippling, coordinated assaults capable of wiping most networks offline.
If criminals haven’t yet built a million-strong botnet using the current pool of vulnerable devices, they certainly have the capacity to do so.
“An additional 2 million hosts have been identified by the botnet scanners as potential Reaper nodes, but have not been subsumed into the botnet,” Arbor’s ASERT team wrote, explaining that the coders may have intentionally slowed the how quickly the malware can spread to keep it quiet and under the radar.
Arbor says Reaper is likely being built to serve as the machine powering a giant attack-for-hire service known as a “booter” or “stresser” service.
“Our current assessment of Reaper is that it is likely intended for use as a booter/stresser service primarily serving the intra-China DDoS-for-hire market,” Arbor wrote. “Reaper appears to be a product of the Chinese criminal underground; some of the general Reaper code is based on the Mirai IoT malware, but it is not an outright Mirai clone.” Continue reading








 Hyatt said its cyber security team discovered signs of unauthorized access to payment card information from cards manually entered or swiped at the front desk of certain Hyatt-managed locations between March 18, 2017 and July 2, 2017.
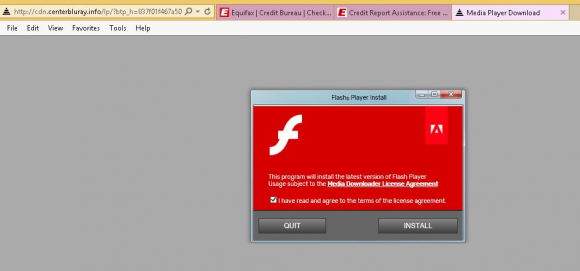
Hyatt said its cyber security team discovered signs of unauthorized access to payment card information from cards manually entered or swiped at the front desk of certain Hyatt-managed locations between March 18, 2017 and July 2, 2017. Roughly half of the flaws Microsoft addressed this week are in the code that makes up various versions of Windows, and 28 of them were labeled “critical” — meaning malware or malicious attackers could use the weaknesses to break into Windows computers remotely with no help from users.
Roughly half of the flaws Microsoft addressed this week are in the code that makes up various versions of Windows, and 28 of them were labeled “critical” — meaning malware or malicious attackers could use the weaknesses to break into Windows computers remotely with no help from users. Previously, Equifax said the breach impacted approximately 400,000 U.K. residents. But in a statement released Tuesday, Equifax said it would notify 693,665 U.K. consumers by mail that their personal information was jeopardized in the breach. This includes:
Previously, Equifax said the breach impacted approximately 400,000 U.K. residents. But in a statement released Tuesday, Equifax said it would notify 693,665 U.K. consumers by mail that their personal information was jeopardized in the breach. This includes: