Nearly every time I write about a small- to mid-sized business that has lost hundreds of thousands of dollars after falling victim to a malicious software attack, readers want to know how the perpetrators broke through the victim organization’s defenses, and which type of malware paved the way. Normally, victim companies don’t know or disclose that information, so to get a better idea, I’ve put together a profile of the top email-based malware attacks for each day over the past month.
This data draws from daily reports compiled by the computer forensics and security management students at the University of Alabama at Birmingham, a school I visited last week to give a guest lecture and to gather reporting for a bigger project I’m chasing. The UAB reports track the top email-based threats from each day, and include information about the spoofed brand or lure, the method of delivering the malware, and links to Virustotal.com, which show the percentage of antivirus products that detected the malware as hostile.
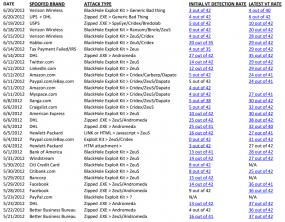
As the chart I compiled above indicates, attackers are switching the lure or spoofed brand quite often, but popular choices include Amazon.com, the Better Business Bureau, DHL, Facebook, LinkedIn, PayPal, Twitter and Verizon Wireless.
Also noticeable is the lack of antivirus detection on most of these password stealing and remote control Trojans. The average detection rate for these samples was 24.47 percent, while the median detection rate was just 19 percent. This means that if you click a malicious link or open an attachment in one of these emails, there is less than a one-in-five chance your antivirus software will detect it as bad.
According to UAB, about two-thirds of the top email-based malware attacks in the past month have used exploit kits, and most frequently that kit was BlackHole. Exploit kits are made to be sewn into the fabric of hacked or malicious sites, so that visiting Web browsers are checked for close to a dozen outdated plugins; any insecure plugins found can be used to silently install malicious software on the vulnerable machine.
It’s not hard to see why so many small to mid-sized organizations get hit with these attacks. When the malware slips past their antivirus, it is often just a question of whether the organization has someone or something in place that is vigilant about applying security updates for things like Flash, Java, and Adobe Reader and a host of other programs that hook into the browser.
This is why I continuously implore small business owners to bank online using only a dedicated system that is carefully maintained and not used for anything other than transacting with the bank’s Web site. For those who don’t have a spare computer handy, a Live CD version of Linux may be the best way to go.
If anyone wants to view the spreadsheet above in a downloadable format, here are Microsoft Excel and PDF versions of it.




A lot of these campaigns don’t have malicious payloads per se; the malware vector is through a drive-by download initiated by a call-to-action link in the messages that have been socially engineered to entice clicks–say to challenge a bogus charge on a credit card for example.
They can contain malicious attachments at times too, but the spammers mix the methods even within a single campaign run. The three common techniques seem to be: malicious url, malicious compressed binary, malicious javascript either attached or placed in an html inline part.
So, for these messages without the malicious binary attached, there’s little benefit from AV software, at least as far as receiving malicious email goes.
However, I suspect a lot of these campaigns are successful for several reasons:
Many of the spoofed brands commonly show up on user whitelists. Many of the spoofed emails look legit to non-techie folks and might fish the spoofs out of quarantine thinking they are legit messages errantly blocked by anti-spam software. Some AS vendors might have a difficult time discerning between a spoofed brand and a real message as many traits are common; sometimes only a link has been changed.
When filtering technology is less than perfect, people learn to distrust their AS solution and ignore its warnings, or override its ability to block commonly spoofed brands by blanket whitelisting domains. It’s a sad fact I’ve seen many times and is just one reason I am adamantly against whitelists, but that’s another topic…
Great content. Lovin’ the blog, as always, providing much needed technical insight on the bad guys.
One thing that would be helpful – is the CVE(s) each attack is using.
For Exploit pack CVE information, see http://contagiodump.blogspot.com/2010/06/overview-of-exploit-packs-update.html
I goes to show that education, education, education of the users is so important. SW protection only goes so far, the rest is in their head 🙂
Yes you are absolutely right. Technology is incidental, it is the human mind that is the ultimate target of a malicious hacker. As long as the user is sensitized to the dangers, the problems are greatly reduced.
I definatly agree – education is very important – but I’ve seen alot of training developed by corporate/government IT people and it is horrid. Too much focus on policy and procedure – referencing obscure documents or laws – and not enough focus on how to recognise a bogus email and how to respond to it.
That USPS/UPS/DHL *bredolab/generic bad thing made me smile… (they’re loading new IPs to DDoS your site I guess ;-))
Truely those malware email attacks are the source for many bad things around but keep in mind that this kind of attack has been out there for nearly a decade and careless companies do use their email address since years. Consequently those targets PCs must have been filled up with malware if they’ve openend all and every attachment and followed every link over the years.
As I’ve learned from your reports those victims seem to have some things in common, making me think of well-planed and targeted attacks. And maybe attackers didn’t even need to send them attachments via email:
1st victims are curiously customers of careless banks not stopping suspicious transactions for whatever reasons. 2nd they lose quite a king’s ransom. 3rd victims are some kind of happy-go-lucky about cybercrime, most likely because they’ve never had any problems and feel secure and well informed. I bet my 2 cents those attackers first visited the banks, then found the victims and tricked them into installing the backdoor.
Maybe I’m wrong and those victims PCs are fully loaded up with malware and the attackers are just lucky (addressing a naive victim with access to and enough money in an account at a overstrained bank), but I hardly believe those attackers are patiently waiting for Lady Luck to stop by. (At least I can’t believe feds wouldn’t force banks to audit customers about email threats but could imagine they don’t announce manhunt on someone asking general questions about online banking?)
Brian, Thank you so much for this article and sharing your spreadsheet. I use ESET on my Mac and so far so good. 😉
Great – data! I’ll have another go at getting our payroll boss to use secured VM’s for handling anything involving money.
BTW: looks like you have an open somewhere above. Or maybe it’s just my Firefox acting up.
That should’ve been “an open somewhere” – I should have seen that coming.
Egg-on-face – “less-than b greater-than” then? Preview would be helpful here…
LOL. Thanks, fixed.
I would put in a word of caution about using a VM for sensitive transactions. A key logger installed on the host OS would still catch any data entered in the VM (Please correct me if I am wrong on this). I would go with Brian’s suggestion to use a Live CD.
Good question. I know when USB devices are attached and tied to the VM, the host OS sees them as disconnected/removed. The mouse, however, is not that way, so it stands to reason you’re correct about the keyboard too.
Someone’s surely done the testing on this.. right?
I keep wondering about keyloggers interacting with a vm too. Who would have a good answer on that?
If your underlying host machine is infected with a keystroke logger and/or a rootkit, it’s most likely going to have the ability to capture keystrokes whether those are keypresses in the host machine or in the guest/virtual operating system. Furthermore, most of these “keyloggers” are in fact better described as “form grabbers,” in that they hijack the TCP/IP stack on the host operating system and intercept data that is entered into Web page forms, such as usernames and passwords.
We thought about this system. We decided it would be best to force the use of the system, and require it to be separate from the PC. Sooooo, a half a dozen KVM’s, thin clients, and an RDP server on its own VLAN later we are forcing the user to bank through the “secure” (read restricted) server. The server can only go to the banks that are needed, no other services, especially email is not allowed on the server. The PC cannot go to the banks that are needed (this was trickier to implement than I originally thought).
Now what did I forget???
You probably should be archiving your bank machines and re-imaging them regularly. The archived instance will let you perform forensics. The images will help avoid successful attacks persisting.
It’s been a while since I heavily used RDP, but you probably should disable mounting drives over RDP, and if you haven’t disabled SMB, I would. Each machine in your pool should be isolated from all other machines in your pool.
Your chosen technique isn’t immune from old fashioned key loggers, but my impression is that most attacks are really closer to browser form logging.
Personally, I’d want to spend some time working with my bank on ACH restrictions and actually testing my bank by violating them to see how they behave.
Brian, thanks for the answer! That makes sense that the internet communication can be captured with the logging malware, regardless of what VM container is sending or receiving it. I guess a dedicated machine is the best answer to all of this.
@andy1: “I guess a dedicated machine is the best answer to all of this.”
Any particular session is unlikely to encounter malware. So malware is a problem specifically because it infects the hard drive to become active on every new session. A dedicated machine can be infected just like any other.
Every operator does bad things sometimes, by ignorance or human error. All it takes is one error to get infected, and later antivirus scans probably will not detect it. Without some clear indication, the infection will continue essentially forever, even on a dedicated machine. And without reliable detection, we simply cannot know how common it is for dedicated machines to be infected.
Your blog should be required reading for all who oversee or manage IT. It is a valuable resource for me which I visit at least once each day.
Those who ignore your insights are verging on criminal recklessness if they have responsibilities for corporate IT systems. I am thinking of Dilbert’s ludicrous Pointy Haired Boss of which there are far too many. Have they no idea what their unfortunate subordinates really think of them?
I am just an old-timer who looks after systems of friends who you now help keep safe. Thanks for your hard work and expertise.
The paragraph with 24.47 detection rate is wrong. You’re mixing two things together – while it is true, that static detection of the samples may be that bad, it’s wrong to assert that this is the overall performance of AV products. VT guys (hi, julio) said it many times that VT is a multiscanner and drawing conclusions from their results is wrong. The installed AV product on the machine has many other options to protect user – email heuristics, website reputation, file reputation, sandboxing, extended heuristics taking in account all the stuff I mentioned.
I don’t disagree with you in principle, Jindrich. However, we have no other metric aside from the useless and frankly staged tests that antivirus firms pay to have done on their software. If we believe the antivirus industry’s stats, most AV has like a 80-90 percent detection rate, and I doubt even the industry itself believes those stats anymore.
The truth is probably somewhere in the middle: About 50 percent of the time. Might as well flip a coin to decide whether you should open a file or not.
I’m not saying AV is completely useless, just that users should behave as though it is.
Brian, even if you believe in the ‘staged tests’ and whatnot, it still does not make that paragraph closer to truth. Static detection of samples obtained in this run on VT is not ‘metric’, it’s just some random numbers which can, in worst cases, be interpreted as lowest possible score, but in fact it does not mean anything. And running median on nonsense gives you median of nonsense. 😉
Don’t get me wrong – I know what AVs can and what they can’t do. But this kind of bashing (wrong numbers, wrong ‘methodology’ etc) is not exactly what I consider useful for anyone.
I guess we can agree to disagree. Show me a better metric. You’re saying the VT numbers are useless. I would disagree, because the alternatives are “trust us, it’s working fine,” or, “here, look how well our products fared in a re-enacted battle.
But again, I think we’re talking about two different things here, and there is no “wrong” in this analysis. It’s one view of the performance of the industry, from AVG on down the line. My point is that antivirus has become unreliable. I haven’t heard you argue with me on that point.
In re: the topic of this post, every single victim organization I’ve written about was running up to date and licensed antivirus software. How many of them do you think had detections before the money was stolen? This is not an exception but the rule: If you’re unfortunate enough to click a bad link or open a bad attachment in the first 24 hours of the attack, there is not a very good chance that your AV product is going to save you, IMHO.
There are at least three ‘staged tests’ – AVC, AV-Test, Dennis Labs – all of them running some kind of realtime tests. Their results are nowhere near 20% or 50%, they’re usually in 80%+.
Any cloud AV can (and does) check the cloud for the existence of unknown, unsigned binary even before running it. Also, if there is any multi-stage, or exploits involved, there’s quite high probability, that there are network blocks in effect, or that the combination of the vulnerabilities on your computer is not high enough to get exploited.
The numbers 20%-50% on a computer with updated av are definitely not closer to truth than ‘staged’ 99.65% 😉
You operate only with (dis)belief and static detections and from that, you draw wrong conclusions.
Set-up N computers each with updated AV installed and click on every single link in such emails, and count, that’s the only way how correctly argue about this.
“Set-up N computers each with updated AV installed and click on every single link in such emails, and count, that’s the only way how correctly argue about this.”
Great! Let’s do that. Come to think of it, why isn’t VT doing that? Oh wait, I know, it’s expensive and requires real people to maintain.
That’s not a dig at VT guys, I love their work. It’s more just me voicing my frustration at truly useful projects that could add some very meaningful “ground truth” data to some of the security voodoo that passes for wisdom in this industry. For example, the UCSD guys used to run a botfarm, where they’d run and maintain samples of the latest spam bots, just to record what they were spamming, which sites were benefiting, etc. This information can hugely useful down the road for a variety of reasons, yet there is virtually no way to get it after the opportunity is gone. IMHO, it’s vital intelligence that needs to be captured, but it’s tedious and boring to do it. I smell an NSF grant, or three!
But AVC/AV-Test and Dennis are doing exactly these tests. But you pre-dismissed them as ‘staged’ (paid for by av companies, I suppose).
But still, the point of my original comment remains valid. You draw wrong conclusions from wrong numbers.
Sorry, but for credibility’s sake, it matters a lot who pays for the testing. If it’s a third party, independent and hopefully academic endeavor, it will be more transparent and believable.
Best test they could do is get 20 13 year old boys and girls in a room and let them surf the web all day long – any AV that can keep those machines clean at the end is far better than anything I have ever come across.
Worst infection I ever saw was a 14 year old girl’s computer with 40 toolbars, redirects, popups, and every thing else. I ended up almost having to wipe the OS to get it usable, and if I had more time and it was my computer I probably would have.
Ron, sounds like you have seen my son’s computers. I use USGCB policies on them, I limit their connectivity, I do content filtering on each box, everything automatically patches, but give them 10 minutes playing games and surfing the sites they like and the box is infected.
Brian,
Help us find a funding source and my lab will be happy to do that experiment!
The “black hole exploit kit” version of these attacks is working REMARKABLY WELL and they are by-passing AV on all fronts. First, the malware is freshly packed – the version spammed this morning would have no reputation or known signature. Second, the machines hosting the malware redirectors are freshly compromised. The attack starts early this morning. Yesterday all of these sites were existing websites that had never been seen before as being “negative”, so site reputation has not yet been applied to them. Third, the spamming IPs are fresh. When we check spam history for the sending IPs, the ones used very very rarely have ever been seen before by the UAB Spam Data Mine.
The other features of the AV suites would certainly stop some of the older and less sophisticated malware, such as the Bredolab crap mentioned above, but those aren’t the biggest threats.
As you said though, research takes funding. If someone would like to step forward to pay for the AV licenses, and most importantly, the graduate students, we’ll get to work on this suggested project right away!
Rather than just sending infected spam at the computers why not install something like wireshark and have someone use the computers for say a month – see what attacks got thwarted and by what – updated software – non-admin accounts or the AV/IS software. The packet logging should reveal what attacks occour when, or if. I think the packet capture would be especially helpful in any real research since alot of security softwares are tending to be more quiet about what they’re stopping – the idea being to keep the end user from being overloaded with messages.
Static detection of samples obtained in this run on VT is not ‘metric’, it’s just some random numbers which can, in worst cases, be interpreted as lowest possible score, but in fact it does not mean anything. And running median on nonsense gives you median of nonsense.
Your statement is nonsense. These results are valid detection rates. How many attacks are there? How many were detected? Dividing #detected by #attacks gives the probability detection, pure and simple. There may be later detection stages that improve the probability of detection, but the reported numbers are highly meaningful as the odds that VT will catch the this stage of a malware attack.
Nope. Static detections are just subset of the functionality of AVs nowadays. Because you don’t know how much they contribute to overall protection score of the product, talking static detections is almost worthless.
It’s a terminology problem (on your side). What you see on the VT is “detected by statical detections”, not “detected”. That’s the point of my original comment.
Brian said:
“I’m not saying AV is completely useless, just that users should behave as though it is.”
Best summary ever.
But so long as ignorance goes unpunished, we as security and I.T. will be forced to continue to try and “fix stupid” with technology, and that just doesn’t work.
It’s not that AV is useless, but that clients depend on it 100%. To the point that you can tell someone their machine is infected and visiting a malware command and control server and they will say “but I scanned it and the AV didn’t find anything, so it’s not infected.”.
It doesn’t matter if AV is right 10 out of 50 times or 99 out of 100 times. It just takes that 1 time!
It’s best if secured activities are kept completely separate from casual surfing machines.
“It’s not that AV is useless, but that clients depend on it 100%.”
I think it’s fair say that client expectations are being set by the AV vendors themselves, not the other way around.
For example, it seems quite reasonable to me that a non-technical “paying” customer would/should expect relative perfection given the below marketing spin (in this case Norton™ Internet Security):
Stop viruses, spyware, and online identity theft
*Offers advanced protection from online threats.
*Four different layers of smart protection proactively detect and eliminate threats before they reach your computer.
*Identifies and stops new threats fast.
Browse, shop, bank, and socialize online without worry
*Scans email and instant messages for viruses, suspicious links, infected attachments, and other dangers before you open them.
*Identifies safe websites, proactively blocks unsafe sites, and stops online threats before your browser even loads.
*Prevents cybercriminals from hacking into your PC and swiping your information when you use wireless networks.
I’m curious.
I’ve been running a “banking-only” virtual machine running Linux off an ISO (no virtual HDD) , but also my daily desktop sits inside a different virtual machine, also running Linux.
The VM hostOS, Win7, only goes on the internet to get patches. It only has 20 well known programs on it, but those really aren’t used besides VirtualBox and MS-Office (ppt, visio, word, never IE or outlook.
Is this technique likely to be safe enough for our small business banking?
Wow. From top down, you’re running Linux Live CD, inside of a separate Linux VM, on top of a Win7 box? Or did I get that backwards?
You got it right. I’ve also used a LiveCD ISO file + [carefully config.ed] virtual machine on both Windows & Linux for similar reasons. He should be safe so long as nobody targets him specifically or does some attack within the browser. That’s what things like NoScript are for, though. 😉
The hostOS is Win7, but that is barely used.
There are 2 virtual machines (actually about 20, but that doesn’t matter here), both run Linux.
a) Linux ISO only – for banking. No HDD even connected to the VM. It is a liveCD. Booting a liveCD ISO inside a VM is fast. Using a small distro like TinyCoreLinux means hardly any resources are used. 128MB of RAM is overkill for it. DSL/Puppy or other small distros work for banking needs too, if you want a few more apps, but why?
b) Linux Desktop – in this case LXDE loaded on Ubuntu Server to avoid bloat. I’m using all the normal firefox plugins like NoScript and blocking thousands of ad/spam networks at the network layer. Almost all MS-Docs are edited inside this VM using LibreOffice – it really is an excellent tool. Best of all, no Ribbon! Only when I’m embedding Visio do I use the Win7, hostOS, MS-Office install. There’s no competition to Visio for my requirements. No Adobe tools either (besides – cough – Flash), so the PDF issues are gone. Why do people have Adobe software loaded unless they earn a living with it? The risks seem to great.
I don’t think any real possibility of virus contamination between VMs is possible this way.
I’m afraid to have Linux as the hostOS – need one copy of Windows somewhere and Microsoft has been successful in scaring even me into believing there will be software or drivers that only work on Windows. It isn’t true, but that is the fear.
I like you set up, but I still wonder if it would be better to have Linux as the host OS; but then maybe you like the MS virtual machines better. I assume your “LiveCD” is very small and has a low vulnerability profile.
Perhaps you could go further and use something similar to steady state to lock down the drive to your Win7 OS?
Never mind my LiveCD question, I must have posted before reading your description; but my last question still stands.
I’ll make up some day! :p
SteadyState is discontinued. The immutable hard disk feature was on numerous products before it. The inexpensive & effective SandboxIE tool emulates this kind of functionality by default. I’ve also recommended RAM-based distro’s or putting temporary stuff on a RAM disk. With enough RAM, most of what you’re doing can fit in the RAM disk. Anything not explicitly saved is lost upon shutdown.
(Well, after a certain period of time… 😉
Steady State was inferior to new solutions anyway.
Puppy Linux LiveCD fits in RAM very nicely.
Some folks on Wilder’s like to run other browsers inside Sanboxie for regular surfing, and then switch to IE with Prevx Safe-On-Line when they do banking. One can’t do both.
I was surprised to find that you can now run Rapport and SOL concurrently, although Trusteer still complains upon installation. Apparently SOL auto adjusts to medium protection when the presence of Rapport is detected.
I have no idea if trying to use IE with Rapport inside Sanboxie is advisable or not. You may think I’m crazy, but my clients are on strict budgets, and free is king.
I kind of do the same thing, only my base OS is Linux.
Then I have a Win7 VM for Office type work and another Linux VM with a non-persistent disk for internet browsing.
My Host sys is Win 7 Prof 64bit with all current updates and webroot av. I use Oracle’s VirtualBox and XP Prof sp3 virtual machine with all current updates along with MS Security essentials. XP is needed for legacy app. I do NOT casually surf, but visit only specific and currently known safe websites. I carefully scrutinize any email and only open email from known senders.
Is this a good defense against these attacks?
Qubes OS takes this to an extreme level, but effective. The host OS is linux with no network connectivity. Most functions are accomplished with different VMs that ranked by level of trustworthiness. For instance, untrusted browsing can only make external connections and has no host disk access. Trusted browsing, like for banking, occur in another VM with a different level of internal banking. You can create VMs to do whatever you need and assign it a default level of access to the internal network, etc. They should be supporting Windows VMs soon, but do not right now. Bromium is taking a little bit different approach and looks to be very interesting as well.
They’re not so extreme. They’re kind of reinventing the Compartmented Mode Workstations and Trusted GUI’s of the past using a mainstream, low assurance platform. More robust examples include Dell Secure Consolidated Client on INTEGRITY RTOS, LynxSecure, open source Perseus Security Architecture (in Turaya Desktop), BAE’s XTS-400, and Aesec’s GEMSOS designs.
I also have a scheme that uses a master node, low cost worker nodes, KVM switch, and other details to make it a physical separation & controlled interfaces issue. (Easier to deal with than security on hardware shared by trusted & untrusted processes, imho.) Software and system security levels can be increased or decreased based on need.
This all looks much better – and of course any VM used to check email should be shutdown and/or used independently of any other action. Using email at all makes me nervous, no matter what the host OS or virtual component.
It would be nice if I would get cracking and get caught up on high assurance hardware switch schemes; I just don’t seem to have enough time in the day to find out for myself.
Yeah, but you’d fail: I’m kind of the first guy trying to do COTS high assurance switch schemes. Only things on the market are some Data Diodes, Network Pump, and a EAL5 KVM. You can easily get some of the benefits, though, with a very simple set-up.
Essentially, you separate what you do among PC’s based on risk. One PC will almost surely be a Windows PC due to app compatibility. You might have others for various reasons. You keep them separate, even on the networking level, and have them connected to a KVM switch. Then, you can do your main stuff on one PC & effortlessly switch to another to do sensitive or dangerous stuff. They can all be little, low-energy, low-price VIA ARTIGO-like boxes if you want.
The next step is protection at the software layer. The easiest method is virtualization. You can have a good virt. platform that run’s VM’s representing different things you have to do. High risk stuff NEVER goes on a physical box that does important stuff (main assets). From that point, you can use the VM’s to further isolate things on the box, make management of the physical box’s function easier, etc.
It’s honestly similar to how some advanced firms do networking. They try to make it where they turn all the networked servers and applications into either virtual appliances or software appliances. Things are sent, retrieved, migrated, started, stopped, etc. with simple commands and automated processes. Any output on any box is routed to admin’s console.
Now, just imagine master/slave architecture that’s heterogenous b/c some jobs require specialized hardware. The nodes have onboard security mechanisms running directly on a robust med-to-high assurance OS, from access control to IPSec comms to recovery. The virtual machine, probably paravirtualized for extra security, contains the functionality. Anything breaking out of the virtual machine will have too limited privileges to accomplish anything major on the network, whereas the admin or user can be sure he has a working trusted path network-wide & sensitive stuff remains sensitive.
Most stuff like this can be done cost-effectively using COTS components with minimal specialized hardware. The trick is that there’s too much complexity and shared state inside the monster servers that modern IT shops use. So, I’ve been advocating going smaller & using lots of cheap boards with low-watt processors & maybe onboard security options. (VIA’s x86 & some Freescale PPC fit the bill) At least for the security-critical core stuff, that is. This let’s us use a mix of COTS legacy approaches & more robust/secure components.
Great post Nick, and thanks! This discussion reminds me of being back in CNA school about VLAN setups. I hear even those can be pwned – don’t know how the control consol gets comprimised.
Hopefully one can avoid doped chips in anything purchased or scavenged. Sometimes I wonder if I should go back to old junk just to assure that wouldn’t happen; but I suspect even equipment sold clear back to when IC manufacture switched from Japan and the Pacific Rim, to China. Not that Japan is any less suspect, but I think the oversight was more stringent then.
You’re welcome. Glad you enjoyed, it. Yeah, some of it’s similar to the VLAN’s. I remember hearing about them and totally not trusting them. My stuff is actually more inspired by security kernel work in the Orange Book days. Add secure coding, hardware problems, hardware solutions, separation kernels, etc. & here we are today. If you want, here’s a really nice presentation giving the basics from the old days.
Security Kernels
http://www.cse.psu.edu/~tjaeger/cse544…/cse544-lec9-10-security-kernel.ppt
Trusted Operating Systems
http://discovery.csc.ncsu.edu/Courses/csc405-F06/T05_TrustedOS-2.pps
Perseus (modern version)
http://www.perseus-os.org/content/pages/Architecture.htm
Link below is my transaction appliance. It uses some principles from above. It was for mediating ACH fraud, but is general enough to be trusted part of all kinds of stuff. The design & hardware is done to allow gradual increase of system assurance as it sells more units. More details to this use case are worked out in comments by me, tommy, mark currie and clive robinson.
http://www.schneier.com/blog/archives/2011/06/court_ruling_on.html#c552667
Enjoy bringing your mind into the world of *real* computer security. 😉
Ed, one flaw in your logic is that email can appear to come from someone you know, when it actually didn’t. This happens all the time.
I’ve got some other steps listed at mechbgon.com/security you might want to look into, which are geared towards reducing attack surface, reducing impact of a successful attack, making it more difficult to attack successfully, and making even successful attacks ultimately futile.
On the last note there, I’m referring to using a non-Administrator user account (“Limited” or “Standard” on WinXP or Vista/7 respectively) with a disallowed-by-default Software Restriction Policy, which will arbitrarily stop execution of, for example, a malicious .EXE that an exploit is trying to launch from your user profile’s Temp directory.
SRP can be applied to all files, or you can make an exception for libraries. Currently, Adobe Flash Player 11.3 will hang the browser if library enforcement is in effect, but you can use the “all files except libraries” option. I’ve reported the bug to Adobe twice now, maybe they’ll fix it in a future release.
Rather than continue the current security architecture model of believing in the universal desktop and relying on compliance and security tools to protect against everything, why not think a little outside of that model?
Brian’s suggestion is one I have seen before and sparked a new line of thought.
Email and web browsing should be considered public facing services, like email and web servers, and we should look at segmenting them off like we do other public facing services into DMZ or other protected enclaves.
Even if AV is detecting 1 in 2 versus 1 in 5, that still is bad news.
Projects like http://www.qubes-os.com and http://www.bromium.com are examples of great work to isolate inherently untrusted functions.
You can even begin to leverage application virtualization and network segmentation as well.
Rathter than patch, configure, and update, look at the problem from the perspective of malware is going to run no matter what you do. Look at how it gets there. Then start really looking at what the options are for moving the risk somewhere else or otherwise limiting it that doesn’t include IDS,AV,patches, or compliance. There are ways you can keep the user experience the same and at the same time make it very easy as a defender to spot the anomalies. We need IDS, spam filtering, AV, and compliance, but we can do more to enhance and improve their effectiveness if we stop expecting them to make us invulnerable. It is also a fallacy that all malware exploits some service or software. There may not be a CVE involved. If I can get software to run on a system, and I just need to collect user accessible data, then do I really need an exploit to do that, or can I just use valid system tools to collect and exfiltrate that data?
Brian,
Thank you for compiling these sobering statistics.
Aside from the recommended dedicated VM machines, other preventative options exist such as Trusteer Rapport (Zeus detection/removal) and Ironkey Trusted Access (secured browsing and online banking).
Chas
As to Braden above…the thing about Blackhole is that it looks at your machine and reports back to the controller the versions of the various software that you are running. From that information, it can load software to exploit up to several different vulnerabilities that may exist on your configuration. There is a long list of CVEs that it can exploit, including some from 2012 but going back to 2008. So, patching is critical, and as Krebs has reminded us before, that even goes for programs like Java that you may not think to patch or that maybe should just be disabled.
As to Ed and Mike above, opening email shouldn’t hurt you, but a key thought should be not to click on links in the email or download/open attachments. The lures for these exploits are VERY convincing; so to say that you only open email from known, trusted senders wouldn’t save you here, e.g. the Verizon messages are quite legit looking, and even though the dollar amount of the bill may seem higher than most people run up for their cell phone, the amount is in the ballpark for some small businesses.
Another caveat would be to watch for more targeted attacks delivering these lures that take you to Blackhole infected sites. We have already seen CPAs receiving (fake) notices from their professional association and small businesses being urged to check out bad reports on them from the BBB.
Just don’t click on the links!
Thanks, Heather. Just a note about opening email…at least one of the attacks in that chart above (I forget which one) included javascript in the HTML that was inside of the email, so that if you just opened the email in a client that allowed HTML, it would render the javascript and try a series of redirects to a blackhole exploit. People poo-poo my advice about reading email in plain text, saying nobody does these attacks, but the examples above prove otherwise.
True, true. I forgot that people still do that! And, some folks cannot easily control their email configuration at work.
Mozilla email readers (Seamonkey or Thunderbird) allow you to view html without enabling javascript. What are the other risks we need to worry about in email if we don’t open attachments or follow links?
While I usually view in plain text, there are many emails that are pretty incomprehensible that way.
Add: They also can be set to not download remote images unless you specifically allow it for each email.
Hotmail is pretty good about that from sources not on your trusted list; but then you could still get pwned from a trusted source, if you don’t set it to plain text. Too bad most business exchange systems don’t filtering that fine; or the excellent spam blocking I get there. I never get these fake Verizon or any other messages. I did get some cleverly constructed Paypal fakes last year, but they’ve disappeared too.
Of course the fake ones won’t show HTML, because MS blocks them. I do get some legitimate email where images are blocked too, but then that is fine as long as I don’t need the information, I just leave it that way. So far, anything that exhibits keyboard or screen capture or anyother manipulative behavior in my honeypot is blocked by Emisoft’s Mamutu. I do not work for any security software vendor or anyone else for money anyway; so no axe to grind there.
I have one old XP machine I run my server based email from – I shutdown all networked machines when running it, and shut it down when I’m finished. Despite having excellent software firewalls behind my perimeter appliance, I just don’t trust software firewalls.
To make matters worse I recall an exploit a few years ago that leveraged a flaw in how the subject line was processed. – no need to open the email – javascript/HTML processing didn’t matter and your preview pane could even be turned off.
That is the primary reason I only run my Outlook PC alone on the LAN. I never run any other machine until it is shutdown; and I keep PXE disabled.
As mentioned in the previous comment, just reading an HTML email could give the nasties a foothold therefore rule number should be ALWAYS use plain-text for emails.
I never (and I mean NEVER) view html emails. If someone sends one that doesn’t have text equivalent I reply that I never read html-only emails and insist (politely) they use plain-text only.
BTW – There are still a lot of people who either can’t afford or don’t want the latest Office products who won’t be able to open a .xlsx file. Since that format doesn’t offer any advantages, please offer a previous one for download? Thanks.
There is also a link to a PDF version in the story above. I can post a .csv or .html version as well, but some of the formatting does not carry though (like the links in the second column of VT results).
Earlier this year, I switched browsers and e-mail clients and actually began to pay attention to the stuff that previously just went into a spam folder, as I discovered a few important e-mails had accrued there which actually weren’t spam. So, I turned off the spam filter completely — now I get perhaps 20-30 per day, some so obvious and malformed they’re actually humorous but some are really well-crafted. I look at the source code to determine whether the “removed link” URLs actually point to the purported sender or somewhere else entirely, which is a dead giveaway. The process can sometimes be a bit tedious but now that it’s become routine it enables me to forward them to the companies which are being phished or impersonated.
There’s an e-mail address to be found somewhere on the website of almost all major companies (PayPal, eBay, UPS, Chase, BankOne, Wells Fargo, USPS, etc.) that is where anyone is requested to send them for their internal security/fraud department to address. Once you actually find that specific e-mail address (sometimes it isn’t so easy or obvious, and you’ve got to dig), there’s very little additional time required in the forwarding process with each new receipt from there onward. and while I don’t know that my efforts actually do that much good in fighting the scourge, it can’t hurt. If my forwarding a bit of phishing badware to the company being impersonated helps shut down that particular scam a littler earlier than it otherwise might be, so much the better. I seriously doubt it will help catch the miscreants or shut them down, but the more quickly any of their individual efforts are blocked the less successful at stealing they’ll be.
However, if Brian might have a different viewpoint or additional thoughts on whether this is worthwhile for users to do, I’d certainly be interested in hearing his reaction(s). As always, this was another interesting and educational posting.
I’m always surprised at how many of them personally answer these forwards! Paypal is the best. I wouldn’t be surprised if they use the data to help prosecute phishers once they’ve been apprehended.
We tell people not to click on links in emails – period. “You are not qualified to determine if an email link is malicious or not, and you should not put yourself in the position of trying to do so.”
BTW, Brian, if you’re looking into email based threats, shoot me a line.
thx 4 removin my post. so lame.
Always love reading your blog posts Krebs!
Brian:
Two problems with Live CD.:
1. Can’t accept cookies
2. Can’t accept Security Certificates.
2a. Can’t accept NEW Certificates.
This can cause problems with banking accounts — No???
Oh, yes maybe the IT dept. is so good they installed a RAM Disk as part of Live CD boot! Really?
@Dan Ells: “Two problems with Live CD.:
1. Can’t accept cookies
2. Can’t accept Security Certificates.
2a. Can’t accept NEW Certificates.
This can cause problems with banking accounts — No???”
No, not really. I use Puppy Linux, loaded from DVD, in a system without a hard drive, all day, every day (including now). I do online banking immediately after a reboot.
A cookie resides in a single machine. So if I use a different machine, I will not have the current cookie anyway. Normally I have the browser remove all cookies before quitting.
I do as much as possible in SSL (like GMail and Google Docs), and do see certificates exposed by the Firefox add-on “Certificate Patrol.” SSL authentication also occurs in the “Perspectives” add-on. When delay for certificate updates becomes an issue, I save the changes to the DVD.
The Puppy Linux system is best described as “DVD Load” instead of “Live DVD”: The OS loads completely into RAM and the DVD can be removed. As add-on and browser updates and other new files are needed, they can be saved to a new “session” on the same “multi-session” DVD. At startup, only the latest files are loaded. The idea is to reboot, get only the needed things, then save.
I’m using Puppy Linux LiveCD version 5.25; which version do you use?
@JCitizen: “I’m using Puppy Linux LiveCD version 5.25; which version do you use?”
For the past 6 months or so, I have been using Lighthouse 64 5.14 B4, which now may never come out of beta. The guy who made it appears to have succumbed to some serious malady, so it is now unsupported. Usually I rely on the maintainer to post up-to-date browser and driver code, which now will not happen. Nevertheless, it works.
For me, on my 2-year-old desktop, Lighthouse 64 has been less awkward than any other Puppy version I have tried, and I like the graphic screen savers. The wife, however, moved back to Puppy 5.2.5 (which I am expecting to update, someday). Releases I have tried since have disappointed. It was particularly nice for Lighthouse to download a somewhat modern video driver to handle an AMD 6xxx-series video card.
My main reason for using a 64-bit version is to allow space for substantial downloads. (File system size limitations may not be on the radar to someone moving from a hard-drive system to a thin-client system, but it should be, and big RAM is cheap now.) Some of the 32-bit Puppy versions may have a huge file system, but I have not been able to live with them.
Here’s some short descriptions of my version from On-Disc:
Lucid 5.25 is the most leading-edge Lucid ever and a Five Digit Update from Lucid 5.2. It has Bash 4.1.0, an upgrade from Bash 3, Syslinux 4.03, an upgrade from Syslinux 3, and e2fsprogs 1.41.14, the latest from Ubuntu Natty. It now has JWM 500, up from 493. Gnumeric 1.10.13 (up from 1.10.12 in 5.2) is a necessity because our very own yarddog had posted a bug to Gnumeric that is corrected in 1.0.13. Lucid 5.2.1 uses the Woof of FEB 28 replacing the Woof of NOV 28 for 3 months of progress in Woof development.
64 bit, x86_64, and AMD64 designations refer to a 64-bit extension to the existing x86 architecture. A 64 Bit Intel, or Intel Compatible, computer can run either a standard 32 bit operating system, or a 64 bit optimized version.
Thanks for your reply, that is very interesting! 🙂
Hi Brian- appreciate your work and research, and check in on you via twitter daily. I’m interested in real-time updates to the table of phishing scams above. do you know of a link that keeps that information up to date?
thanks,
-dave
No, I don’t. But I will probably make this a monthly blog post, just to keep these reminders at the forefront of everyone’s attention.
Brian,
Can a key stroke logger detect the strokes on an on-screen keyboard, in my case the one that comes with Vista?
just wondering, though so far I havent had a problem.
Thanks Brian
Peter in Sydney New South Wales
An increasing number of malware families today seem to have the capability to do some type of screen grab and/or record video of the victim’s screen. I discussed this feature being added to the Citadel Trojan (a very popular offshoot of Zeus):
http://krebsonsecurity.com/2012/02/collaboration-feuls-rapdid-growth-of-citadel-trojan/
The Brazilian banking Trojans have had this for years, but they typically stick to attacking their own banks.
Hi Brian
I recently downloaded a copy of WaryPuppy Linux and then used ISO to USB to pop it on a USB.
An investment of less than $10 and 10 minutes is all it takes to have a dedicated USB for banking.
@emv x man: “I recently downloaded a copy of WaryPuppy Linux and then used ISO to USB to pop it on a USB.”
Just using Linux is a big, big advantage in avoiding malware. But USB flash drives can be infected by malware just like a hard drive. Even flash drives with write-protect switches become vulnerable as soon as the switch is flipped to allow updates.
One of the advantages of Puppy Linux always has been the ability to periodically save “sessions” of new files to the “multi-session” boot DVD. By rebooting, then updating and immediately saving, malware has a difficult time being present when saving, so the DVD stays clean. This advantage is not available with flash drives, since they are updated continuously, like a hard drive.
There are several reputable distro sites that sell linux preinstalled on USB sticks. They have very reasonable prices. These are bootable just like the liveCDs.
Brian…even tho I’m really an amateur compared to the other readers, I read ur column regularly. Long ago I took your advice and now surf the web as a limited user. Doesn’t that limiting limit the amount of damage these spammers can inflict? I do read my email in HTML and have had not problems. I’m a bit paranoid and I suppose that helps.
EB
These kind of threats can run in a limited environment because they don’t need special permissions from the operating system, can run without installation, and can survive by injecting into the startup folder. Running in a 64 bit environment with IE9 or fully updated open source browsers like FireFox with No Script and AdBlock Plus can also help, but less so for email threats pointed to in this article.
But running CCleaner can lower your threat profile, if you run it at the right settings before any log off, reboot, or shutdown. Running it often during web sessions can keep the crud out of the temporary folders and easily defeat threats like fake virus alerts. Some folks think that Winpatrol could detect some of this behavior, but I’ve seen some malware that can turn it off. I haven’t tested it yet, but maybe Comodo’s Defense + may add another layer of protection in an infected environment. Look for solutions that run at or near the kernel layer to avoid malware manipulation. CNET is a good place to start, to read the editor and especially the user reviews on the most popular downloads.
Be careful running more than one kernel space solution at a time, as they can conflict with bad results like BSODs and boot loops. I’ve always been able to boot to safemode to reverse this. Lately I’ve been able to run several concurrently, so the science is catching up rapidly.
AdAware used to test very well for a signature based product, and even had pretty good heuristics for behavioral based detection, and the real time protection even worked on a limited account; but unfortunately Lavasoft has been bought out literally by a bunch of crooks; so I wouldn’t touch them with a ten foot pole now! An article in the Register exposed this latest development.
An increasing number of malware families today seem to have the capability to do some type of screen grab and/or record video of the victim’s screen. I discussed this feature being added to the Citadel Trojan (a very popular offshoot of Zeus):
http://krebsonsecurity.com/2012/02/collaboration-feuls-rapdid-growth-of-citadel-trojan/
The Brazilian banking Trojans have had this for years, but they typically stick to attacking their own banks.
Similar with the increasing usage of mobile and social applications, the usage of e-mail opens up a can of security concerns. Malware attacks are just one of the biggest problems that may occur. In the following article, we try to better understand the behavior and unknown vulnerabilities that may occur in the mobile and social environments