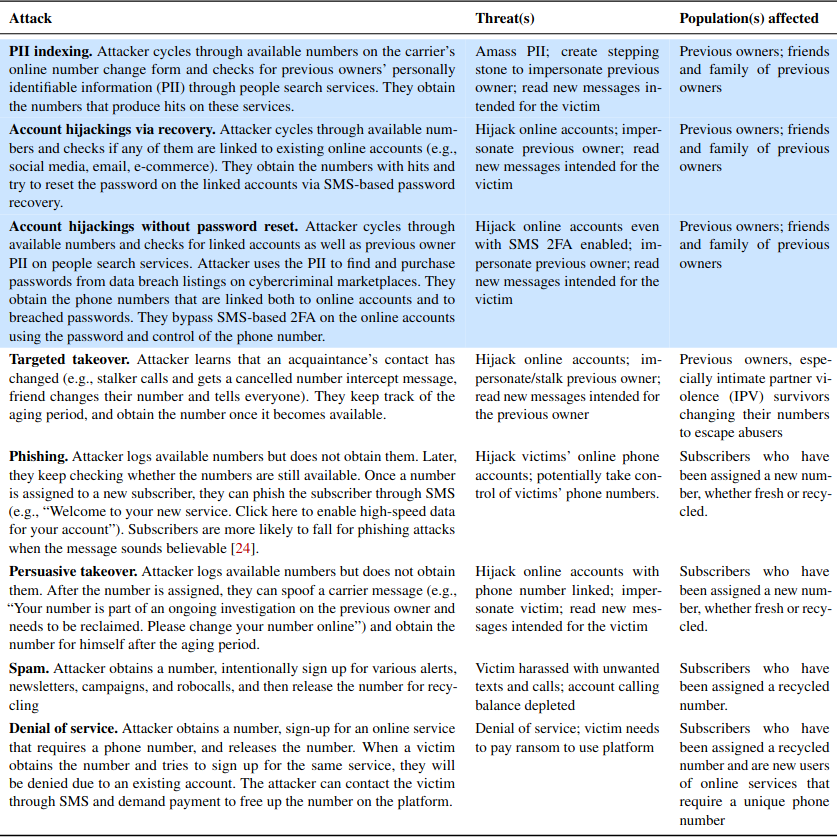
In May 2019, KrebsOnSecurity broke the news that the website of mortgage settlement giant First American Financial Corp. [NYSE:FAF] was leaking more than 800 million documents — many containing sensitive financial data — related to real estate transactions dating back 16 years. This week, the U.S. Securities and Exchange Commission settled its investigation into the matter after the Fortune 500 company agreed to pay a paltry penalty of less than $500,000.

First American Financial Corp.
If you bought or sold a property in the last two decades or so, chances are decent that you also gave loads of personal and financial documents to First American. According to data from the American Land Title Association, First American is the second largest mortgage title and settlement company in the United States, handling nearly a quarter of all closings each year.
The SEC says First American derives nearly 92 percent of its revenue from its title insurance segment, earning $7.1 billion last year.
Title insurance protects homebuyers from the prospect of someone contesting their legitimacy as the new homeowner. According to SimpleShowing.com, there are actually two title insurance policies in each transaction — one for the buyer and one for the lender (the latter also needs protection as they’re providing the mortgage to purchase the home).
Title insurance is not mandated by law, but most lenders require it as part of any mortgage transaction. In other words, if you wish to take out a mortgage on a home you will not be able to do so without giving companies like First American gobs of documents about your income, assets and liabilities — including quite a bit of sensitive financial data.
Aside from its core business competency — checking to make sure the property at issue in any real estate transaction is unencumbered by any liens or other legal claims against it — First American basically has one job: Protect the privacy and security of all these documents.
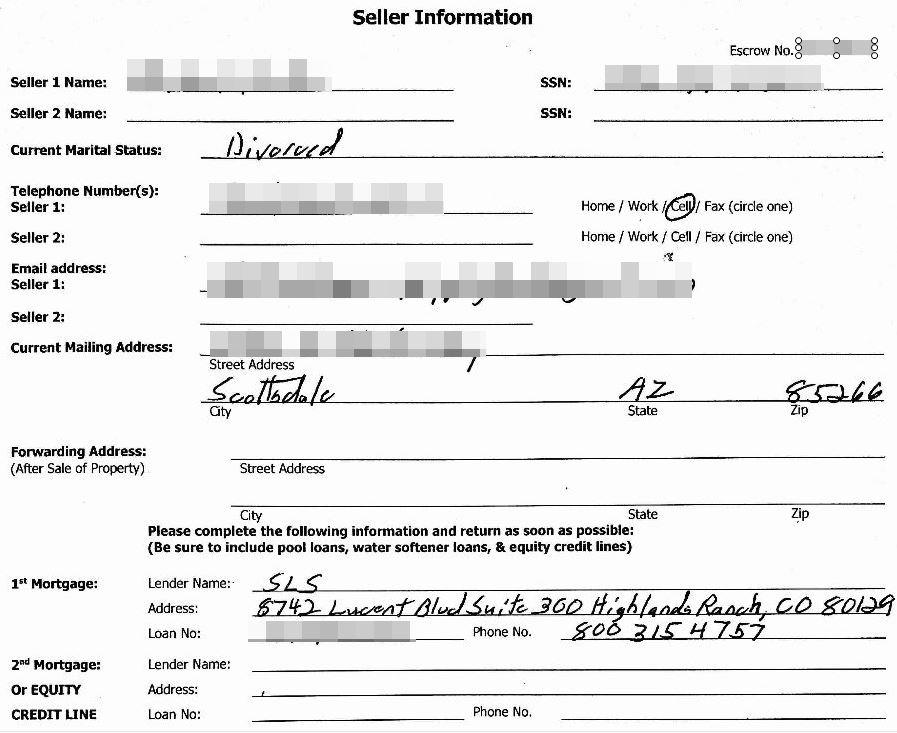
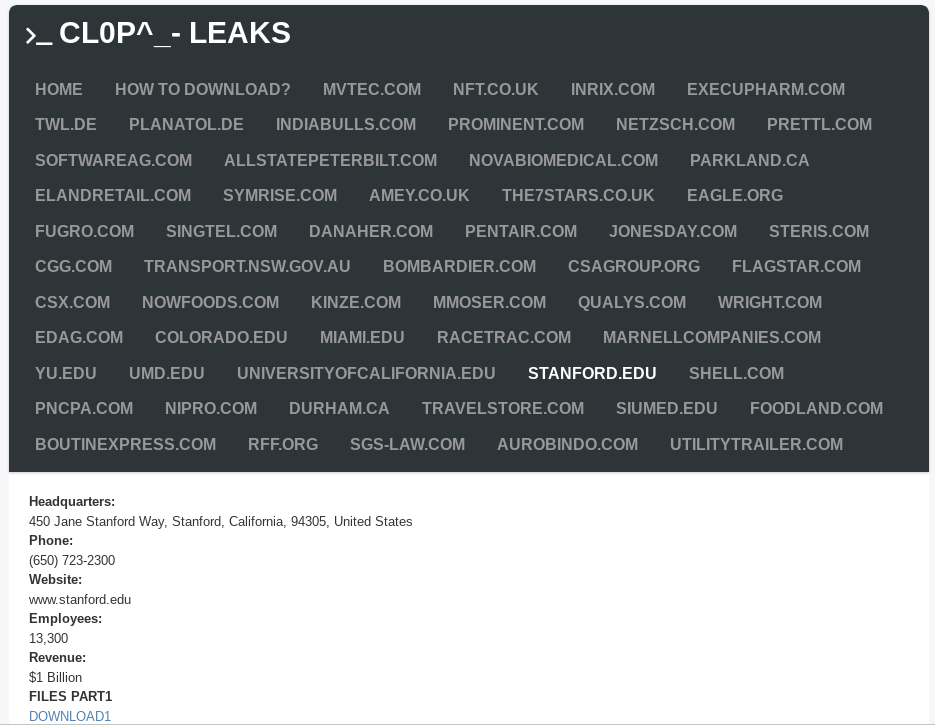
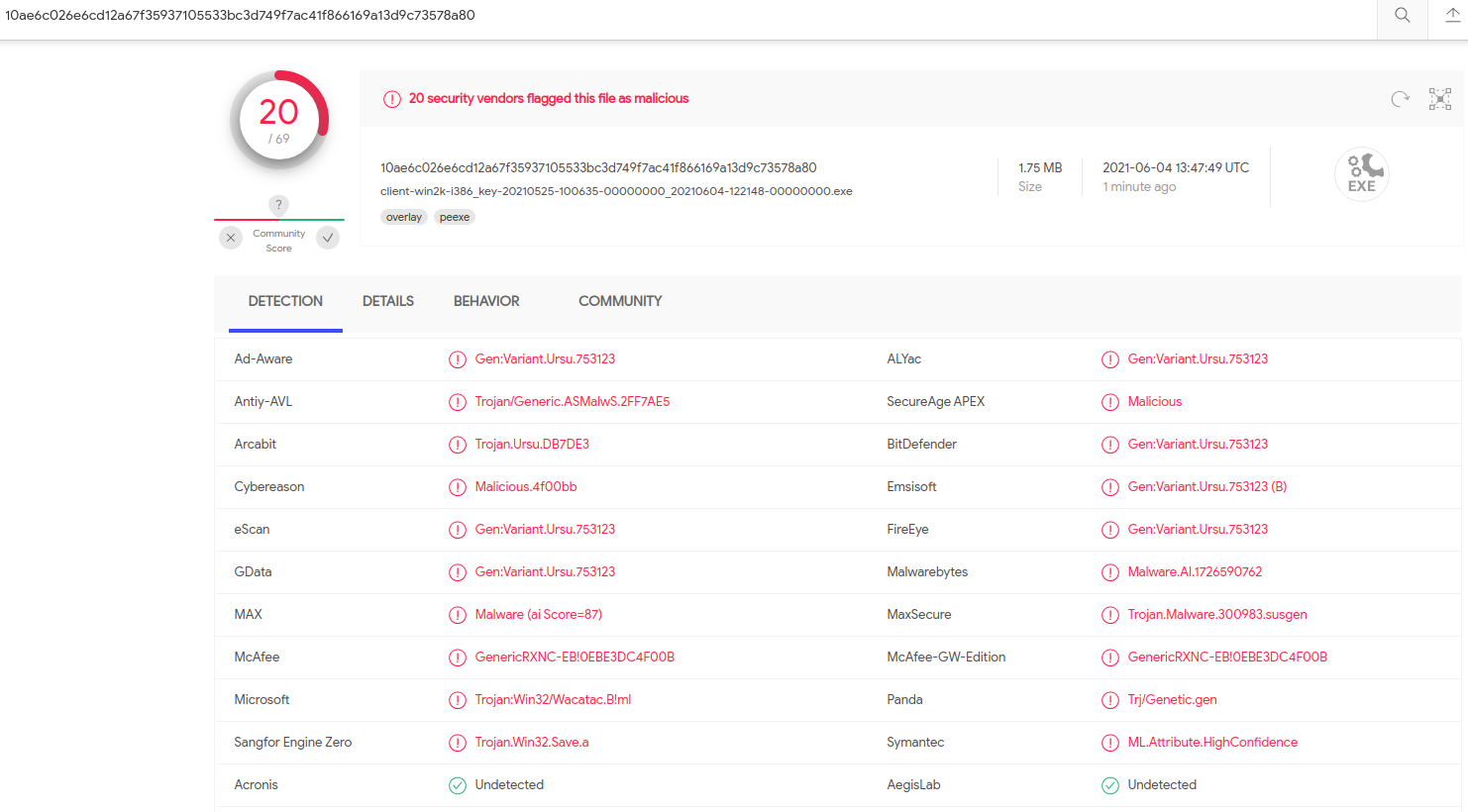
A redacted screenshot of one of many millions of sensitive records exposed by First American’s Web site.
It’s easy to see why companies like First American might not view protecting this data as sacrosanct, as the entire industry’s incentive for safeguarding all those sensitive documents is somewhat misaligned.
That is to say, in the title insurance industry the parties to a real estate transaction aren’t customers, but rather they are are the product. The actual customers of the title insurance companies are principally the banks which back these mortgage transactions.
We see a similar dynamic with social media platforms, where the “user” is not the customer at all but the product whose data is being bought and sold by these platforms.
Roughly five months before KrebsOnSecurity notified First American that anyone with a web browser could view sensitive document in its “Eagle Pro” database online just by changing some characters at the end of a link, an internal security audit at First American flagged the exact same vulnerability.
But the company never acted to fix it until the news media came calling. Continue reading