The U.S. Department of Justice (DOJ) last week announced the arrest of a 55-year-old Latvian woman who’s alleged to have worked as a programmer for Trickbot, a malware-as-a-service platform responsible for infecting millions of computers and seeding many of those systems with ransomware.
Just how did a self-employed web site designer and mother of two come to work for one of the world’s most rapacious cybercriminal groups and then leave such an obvious trail of clues indicating her involvement with the gang? This post explores answers to those questions, as well as some of the ways Trickbot and other organized cybercrime gangs gradually recruit, groom and trust new programmers.

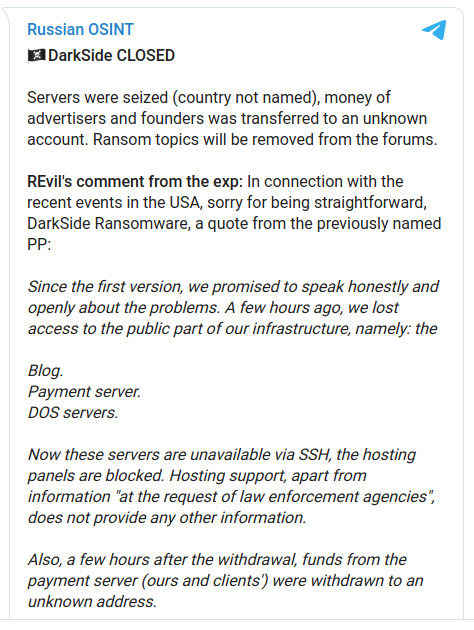
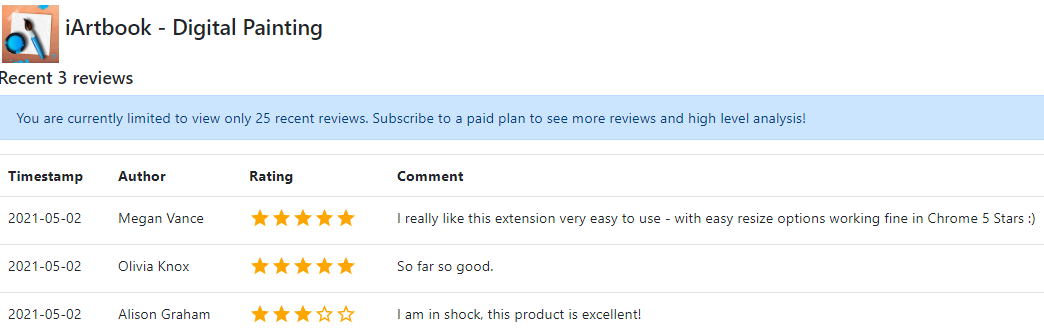
Alla Witte’s personal website — allawitte[.]nl — circa October 2018.
The indictment released by the DOJ (PDF) is heavily redacted, and only one of the defendants is named: Alla “Max” Witte, a 55-year-old Latvian national who was arrested Feb. 6 in Miami, Fla.
The DOJ alleges Witte was responsible for “overseeing the creation of code related to the monitoring and tracking of authorized users of the Trickbot malware, the control and deployment of ransomware, obtaining payments from ransomware victims, and developing tools and protocols for the storage of credentials stolen and exfiltrated from victims infected by Trickbot.”
The indictment also says Witte provided code to the Trickbot Group for a web panel used to access victim data stored in a database. According to the government, that database contained a large number of credit card numbers and stolen credentials from the Trickbot botnet, as well as information about infected machines available as bots.
“Witte provided code to this repository that showed an infected computer or ‘bot’ status in different colors based on the colors of a traffic light and allowed other Trickbot Group members to know when their co-conspirators were working on a particular infected machine,” the indictment alleges.
While any law enforcement action against a crime group that has targeted hospitals, schools, public utilities and governments is good news, Witte’s indictment and arrest were probably inevitable: It is hard to think of an accused cybercriminal who has made more stunningly poor and rookie operational security mistakes than this Latvian senior citizen.
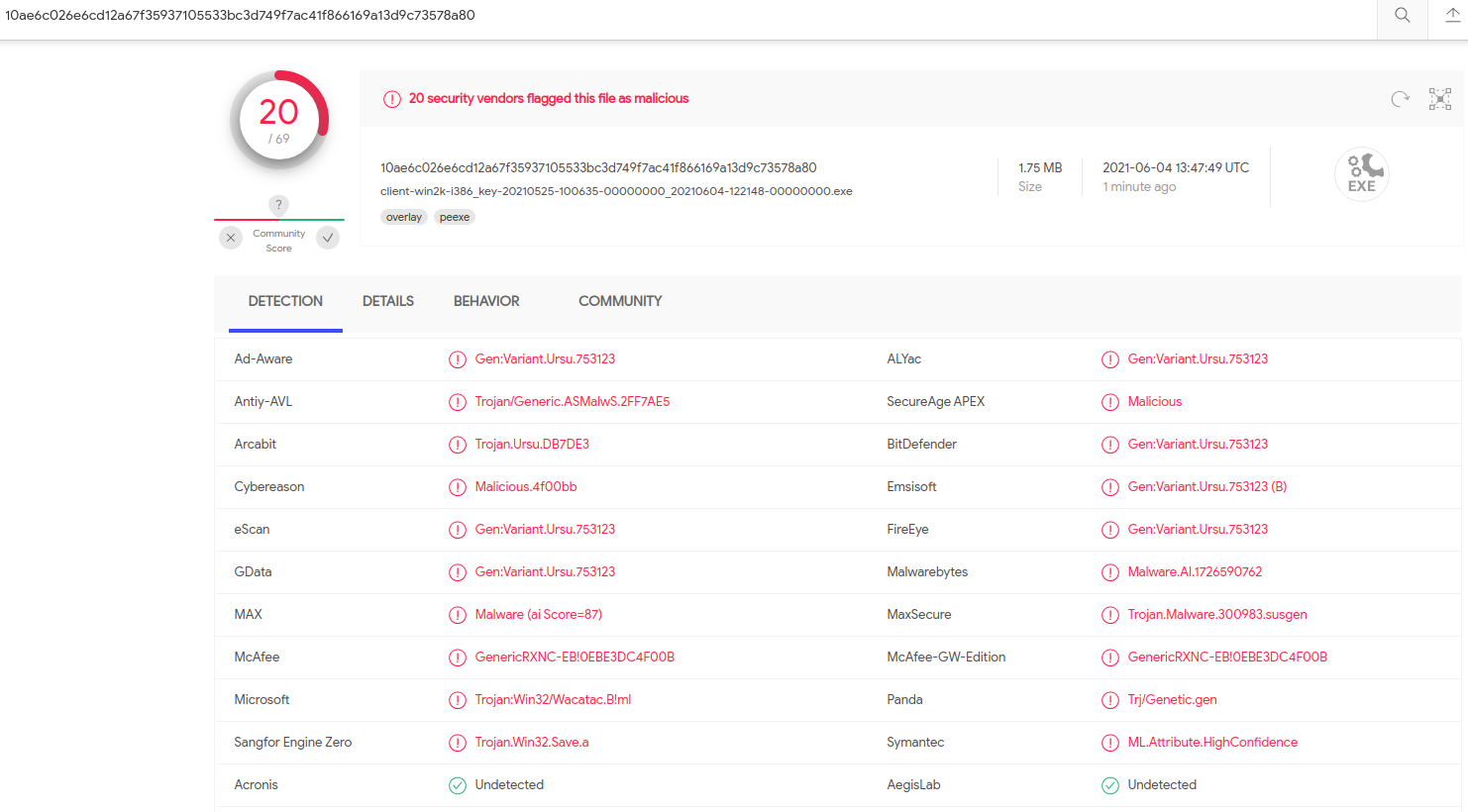
For starters, it appears at one point in 2020 Witte actually hosted Trickbot malware on a vanity website registered in her name — allawitte[.]nl.
While it is generally a bad idea for cybercriminals to mix their personal life with work, Witte’s social media accounts mention a close family member (perhaps her son or husband) had the first name “Max,” which allegedly was her hacker handle.
Unlike many accused cybercriminals who hail from Russia or former Soviet countries, Witte did not feel obligated to avoid traveling to areas where she might be within reach of U.S. law enforcement agencies. According to her indictment, Witte was living in the South American nation of Suriname and she was arrested in Miami while flying from Suriname. It is not clear where her intended destination was.
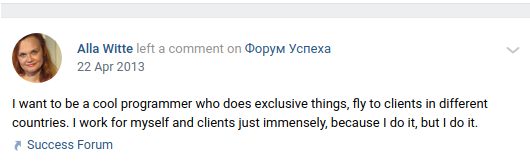
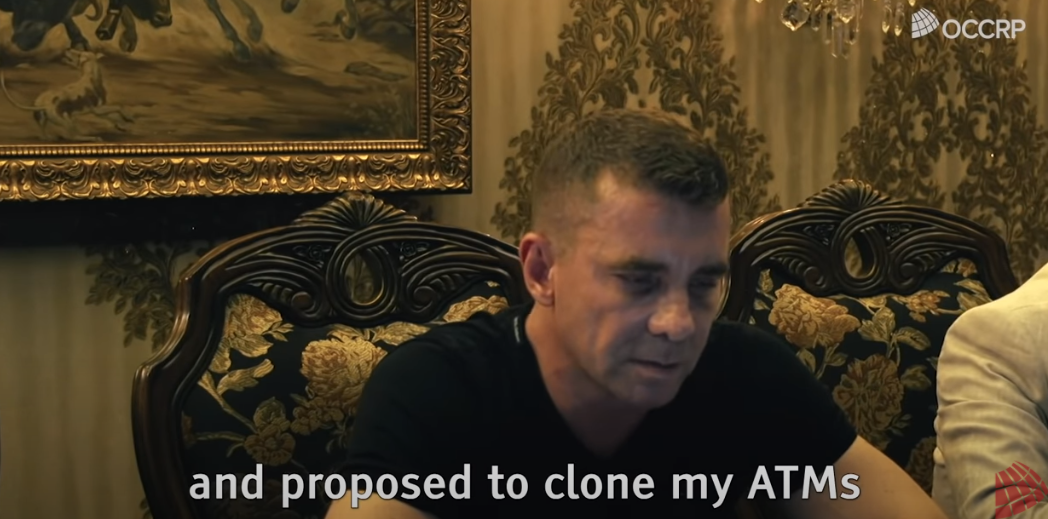
A Google-translated post Witte made to her Vkontakte page, five years before allegedly joining the Trickbot group.
Alex Holden, founder of the cybersecurity intelligence firm Hold Security, said Witte’s greatest lapse in judgment came around Christmas time in 2019, when she infected one of her own computers with the Trickbot malware — allowing it to steal and log her data within the botnet interface.
“On top of the password re-use, the data shows a great insight into her professional and personal Internet usage,” Holden wrote in a blog post on Witte’s arrest.
“Many in the gang not only knew her gender but her name too,” Holden wrote. “Several group members had AllaWitte folders with data. They refer to Alla almost like they would address their mothers.”
So how did this hacker mom with apparently zero sense of self-preservation come to work for one of the world’s most predatory cybercriminal gangs? Continue reading