Joker’s Stash, by some accounts the largest underground shop for selling stolen credit card and identity data, says it’s closing up shop effective mid-February 2021. The announcement came on the heels of a turbulent year for the major cybercrime store, and just weeks after U.S. and European authorities seized a number of its servers.
A farewell message posted by Joker’s Stash admin on Jan. 15, 2021.
The Russian and English language carding store first opened in October 2014, and quickly became a major source of “dumps” — information stolen from compromised payment cards that thieves can buy and use to create physical counterfeit copies of the cards.
But 2020 turned out to be a tough year for Joker’s Stash. As cyber intelligence firm Intel 471 notes, the curator of the store announced in October that he’d contracted COVID-19, spending a week in the hospital. Around that time, Intel 471 says many of Joker’s loyal customers started complaining that the shop’s payment card data quality was increasingly poor.
“The condition impacted the site’s forums, inventory replenishments and other operations,” Intel 471 said.
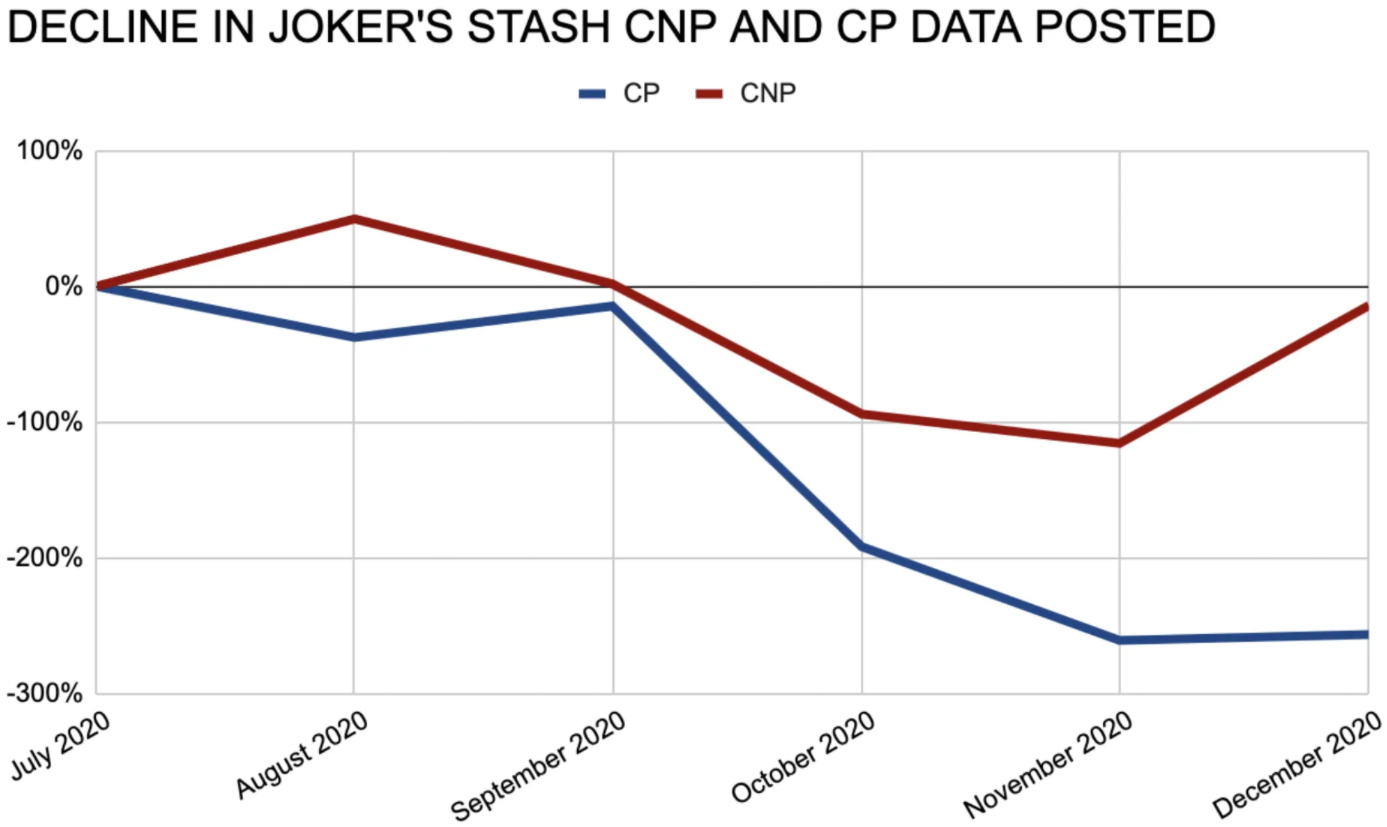
That COVID diagnosis may have affected the shop owner’s ability to maintain fresh and valid inventory on his site. Gemini Advisory, a New York City-based company that monitors underground carding shops, tracked a “severe decline” in the volume of compromised payment card accounts for sale on Joker’s Stash over the past six months.
“Joker’s Stash has received numerous user complaints alleging that card data validity is low, which even prompted the administrator to upload proof of validity through a card-testing service,” Gemini wrote in a blog post about the planned shutdown.
Then on Dec. 16, 2020, several of Joker’s long-held domains began displaying notices that the sites had been seized by the U.S. Department of Justice and Interpol. The crime shop quickly recovered, moving to new infrastructure and assuring the underground community that it would continue to operate normally.
Gemini estimates that Joker’s Stash generated more than a billion dollars in revenue over the past several years. Much of that revenue came from high-profile breaches, including tens of millions of payment card records stolen from major merchants including Saks Fifth Avenue, Lord and Taylor, Bebe Stores, Hilton Hotels, Jason’s Deli, Whole Foods, Chipotle, Wawa, Sonic Drive-In, the Hy-Vee supermarket chain, Buca Di Beppo, and Dickey’s BBQ.
Joker’s Stash routinely teased big breaches days or weeks in advance of selling payment card records stolen from those companies, and periodically linked to this site and other media outlets as proof of his shop’s prowess and authenticity.
Like many other top cybercrime bazaars, Joker’s Stash was a frequent target of phishers looking to rip off unwary or unsophisticated thieves. In 2018, KrebsOnSecurity detailed a vast network of fake Joker’s Stash sites set up to steal login credentials and bitcoin. The phony sites all traced back to the owners of a Pakistani web site design firm. Many of those fake sites are still active (e.g. jokersstash[.]su). Continue reading







 Like so many Q drops, Queequeg’s tattoos tell a mysterious tale, but we never quite learn what that full story is. Indeed, the artist who etched them into Queequeg’s body is long dead, and the cannibal himself can’t seem to explain what it all means.
Like so many Q drops, Queequeg’s tattoos tell a mysterious tale, but we never quite learn what that full story is. Indeed, the artist who etched them into Queequeg’s body is long dead, and the cannibal himself can’t seem to explain what it all means.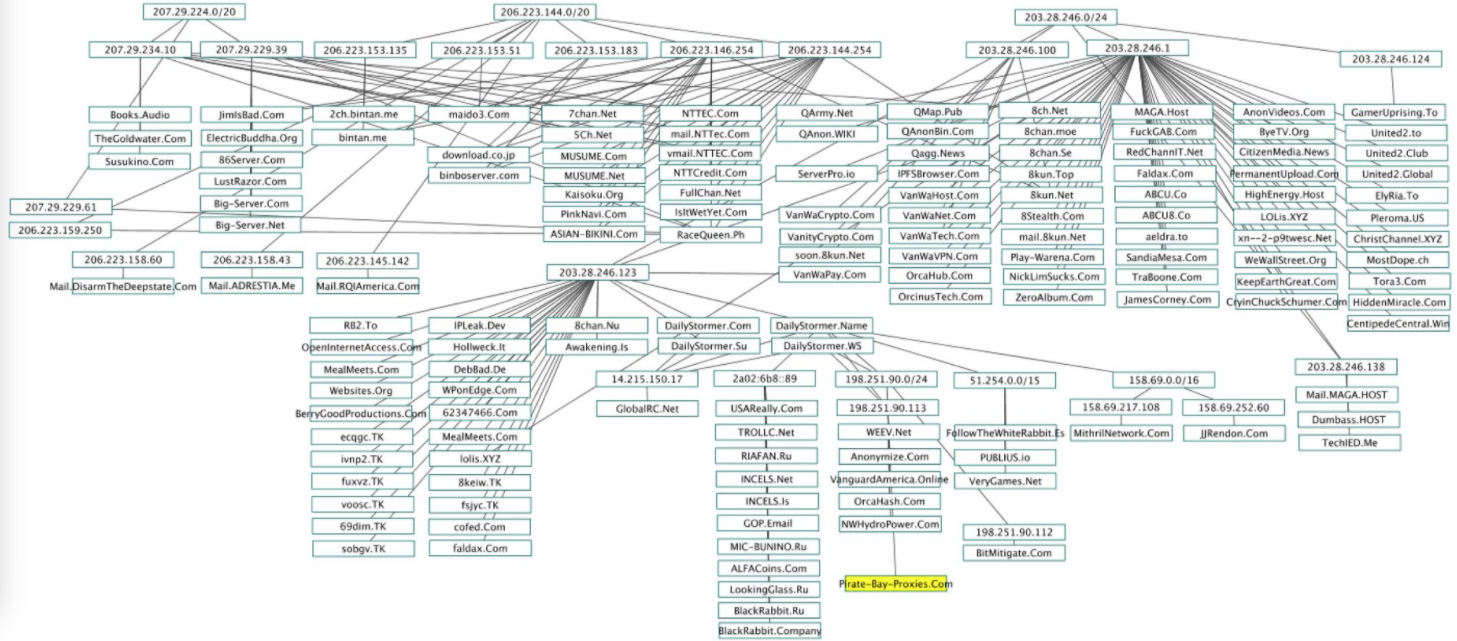
 With the ongoing disruption to life and livelihood wrought by the Covid-19 pandemic, 2020 has been a fairly horrid year by most accounts. And it’s perhaps fitting that this was also a leap year, piling on an extra day to a solar rotation that most of us probably can’t wait to see in the rearview mirror.
With the ongoing disruption to life and livelihood wrought by the Covid-19 pandemic, 2020 has been a fairly horrid year by most accounts. And it’s perhaps fitting that this was also a leap year, piling on an extra day to a solar rotation that most of us probably can’t wait to see in the rearview mirror.