Two of the most disruptive and widely-received spam email campaigns over the past few months — including an ongoing sextortion email scam and a bomb threat hoax that shut down dozens of schools, businesses and government buildings late last year — were made possible thanks to an authentication weakness at GoDaddy.com, the world’s largest domain name registrar, KrebsOnSecurity has learned.
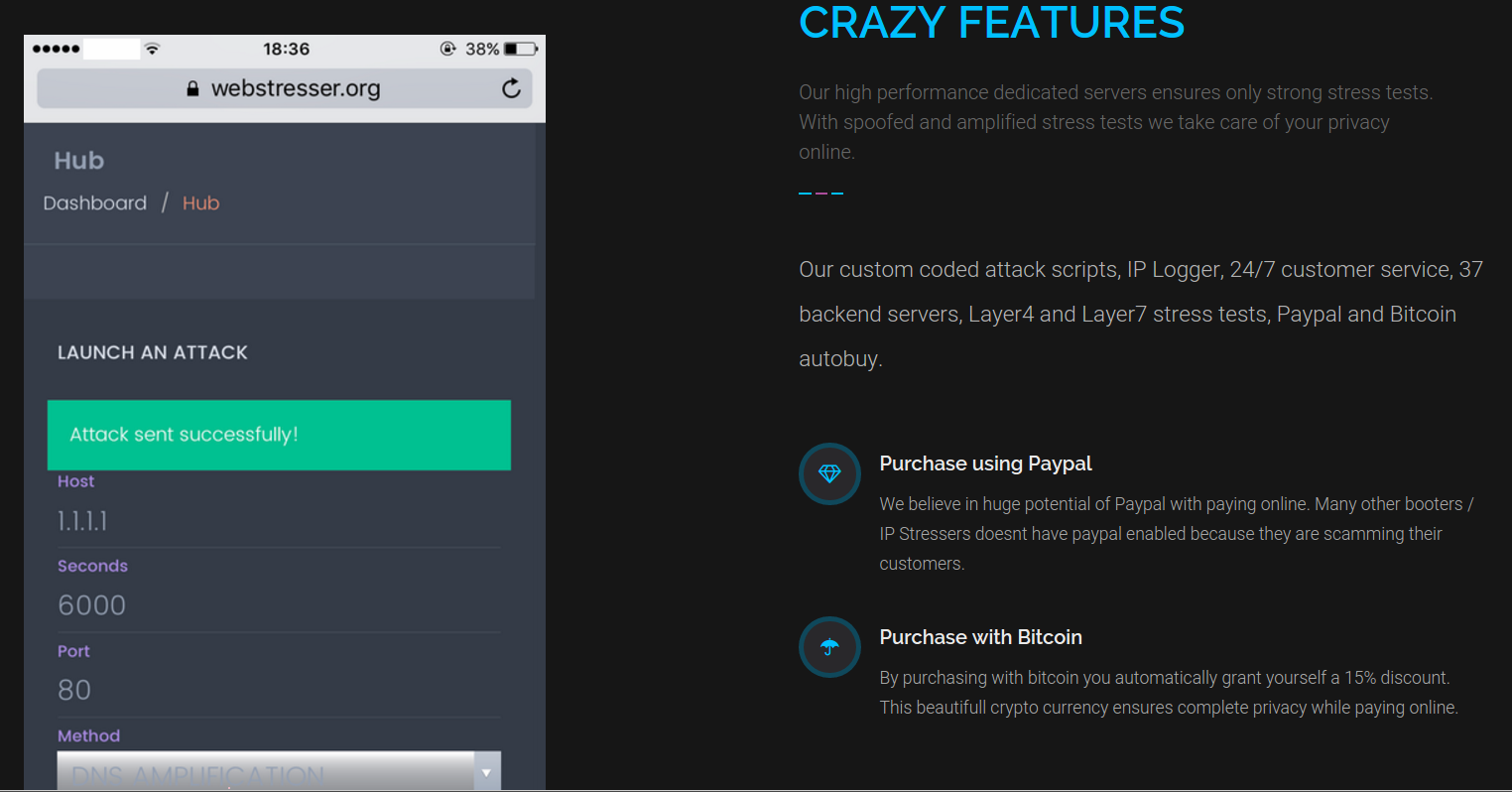
Perhaps more worryingly, experts warn this same weakness that let spammers hijack domains tied to GoDaddy also affects a great many other major Internet service providers, and is actively being abused to launch phishing and malware attacks which leverage dormant Web site names currently owned and controlled by some of the world’s most trusted corporate names and brands.

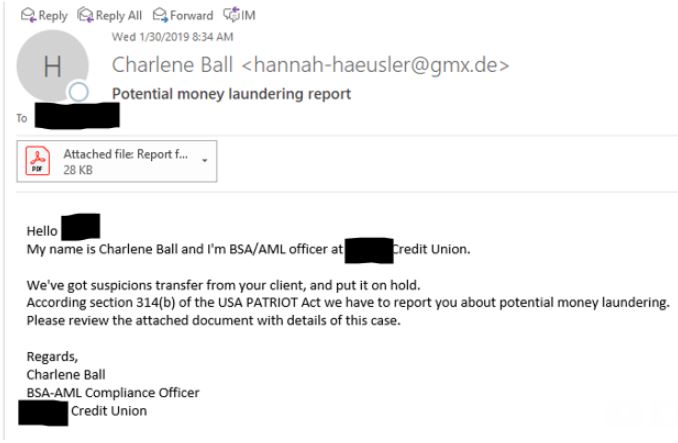
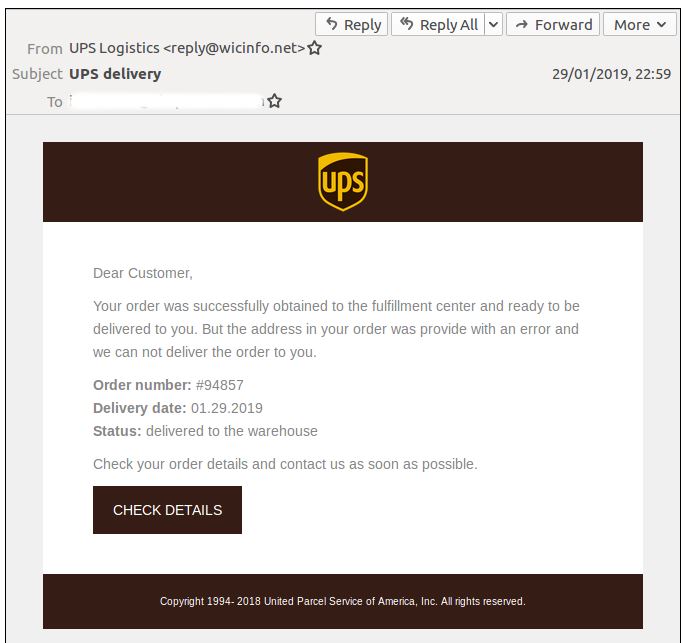
In July 2018, email users around the world began complaining of receiving spam which began with a password the recipient used at some point in the past and threatened to release embarrassing videos of the recipient unless a bitcoin ransom was paid. On December 13, 2018, a similarly large spam campaign was blasted out, threatening that someone had planted bombs within the recipient’s building that would be detonated unless a hefty bitcoin ransom was paid by the end of the business day.
Experts at Cisco Talos and other security firms quickly drew parallels between the two mass spam campaigns, pointing to a significant overlap in Russia-based Internet addresses used to send the junk emails. Yet one aspect of these seemingly related campaigns that has been largely overlooked is the degree to which each achieved an unusually high rate of delivery to recipients.
Large-scale spam campaigns often are conducted using newly-registered or hacked email addresses, and/or throwaway domains. The trouble is, spam sent from these assets is trivial to block because anti-spam and security systems tend to discard or mark as spam any messages that appear to come from addresses which have no known history or reputation attached to them.
However, in both the sextortion and bomb threat spam campaigns, the vast majority of the email was being sent through Web site names that had already existed for some time, and indeed even had a trusted reputation. Not only that, new research shows many of these domains were registered long ago and are still owned by dozens of Fortune 500 and Fortune 1000 companies.
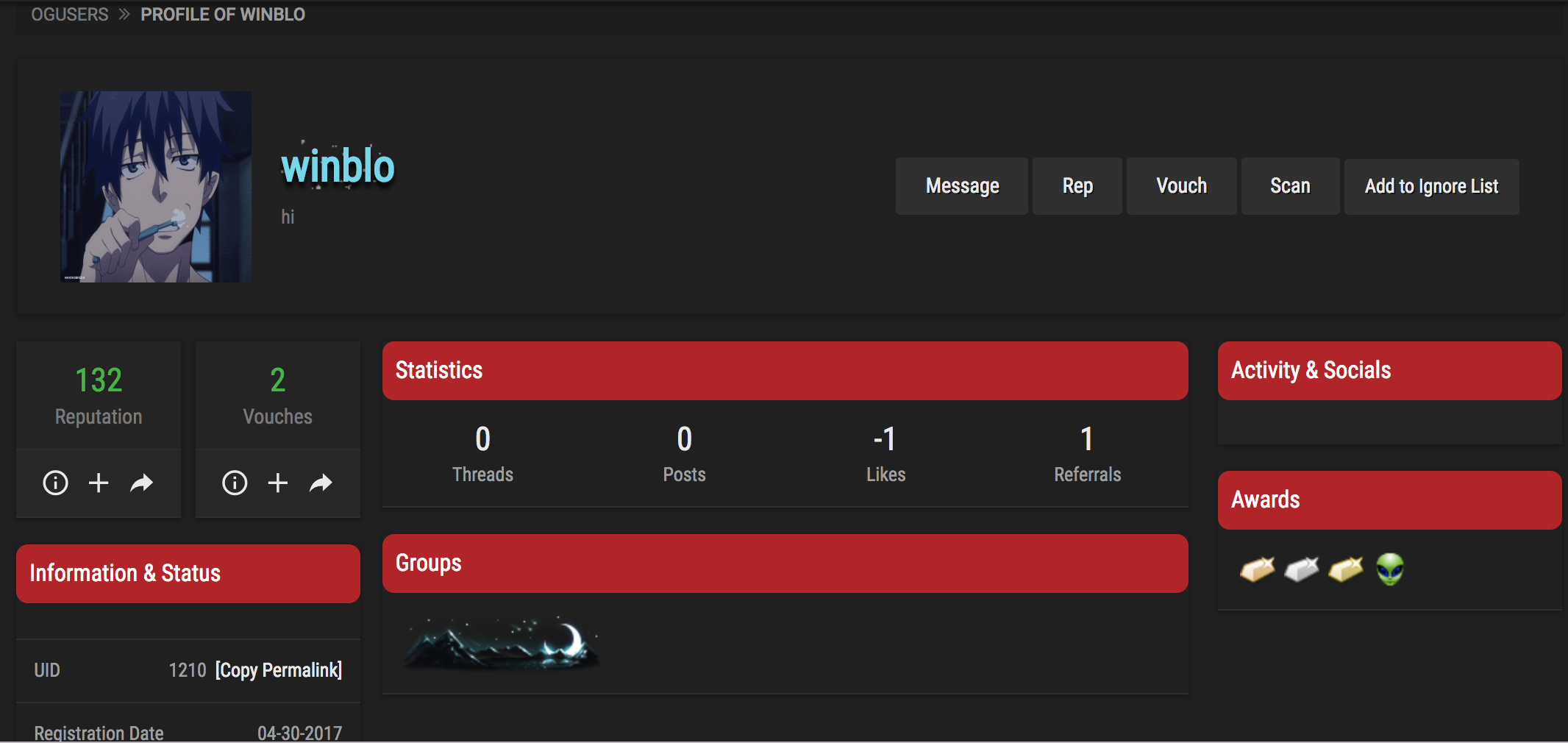
That’s according to Ron Guilmette, a dogged anti-spam researcher. Researching the history and reputation of thousands of Web site names used in each of the extortionist spam campaigns, Guilmette made a startling discovery: Virtually all of them had at one time received service from GoDaddy.com, a Scottsdale, Ariz. based domain name registrar and hosting provider.
Guilmette told KrebsOnSecurity he initially considered the possibility that GoDaddy had been hacked, or that thousands of the registrar’s customers perhaps had their GoDaddy usernames and passwords stolen.
But as he began digging deeper, Guilmette came to the conclusion that the spammers were exploiting an obscure — albeit widespread — weakness among hosting companies, cloud providers and domain registrars that was first publicly detailed in 2016.
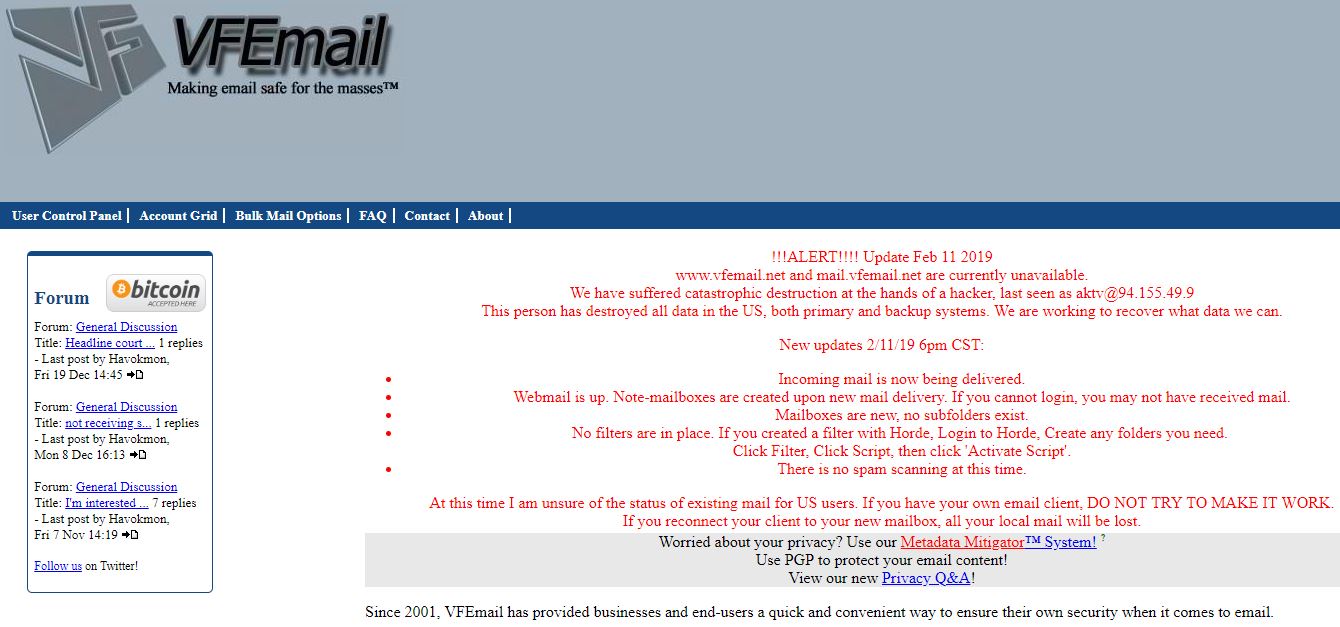
EARLY WARNING SIGNS
In August 2016, security researcher Matthew Bryant wrote about a weakness that could be used to hijack email service for 20,000 established domain names at a U.S. based hosting provider. A few months later, Bryant warned that the same technique could be leveraged to send spam from more than 120,000 trusted domains across multiple providers. And Guilmette says he now believes the attack method detailed by Bryant also explains what’s going on in the more recent sextortion and bomb threat spams.
Grasping the true breadth of Bryant’s prescient discovery requires a brief and simplified primer on how Web sites work. Your Web browser knows how to find a Web site name like example.com thanks to the global Domain Name System (DNS), which serves as a kind of phone book for the Internet by translating human-friendly Web site names (example.com) into numeric Internet address that are easier for computers to manage.
When someone wants to register a domain at a registrar like GoDaddy, the registrar will typically provide two sets of DNS records that the customer then needs to assign to his domain. Those records are crucial because they allow Web browsers to figure out the Internet address of the hosting provider that’s serving that Web site domain. Like many other registrars, GoDaddy lets new customers use their managed DNS services for free for a period of time (in GoDaddy’s case it’s 30 days), after which time customers must pay for the service.
The crux of Bryant’s discovery was that the spammers in those 2016 campaigns learned that countless hosting firms and registrars would allow anyone to add a domain to their account without ever validating that the person requesting the change actually owned the domain. Here’s what Bryant wrote about the threat back in 2016:
“In addition to the hijacked domains often having past history and a long age, they also have WHOIS information which points to real people unrelated to the person carrying out the attack. Now if an attacker launches a malware campaign using these domains, it will be harder to pinpoint who/what is carrying out the attack since the domains would all appear to be just regular domains with no observable pattern other than the fact that they all use cloud DNS. It’s an attacker’s dream, troublesome attribution and an endless number of names to use for malicious campaigns.”
SAY WHAT?
For a more concrete example of what’s going on here, we’ll look at just one of the 4,000+ domains that Guilmette found were used in the Dec. 13, 2018 bomb threat hoax. Virtualfirefox.com is a domain registered via GoDaddy in 2013 and currently owned by The Mozilla Corporation, a wholly owned subsidiary of the Mozilla Foundation — the makers of the popular Firefox Web browser.
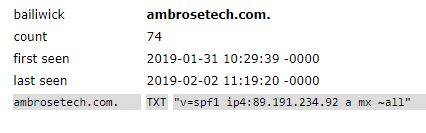
The domain’s registration has been renewed each year since its inception, but the domain itself has sat dormant for some time. When it was initially set up, it took advantage of two managed DNS servers assigned to it by GoDaddy — ns17.domaincontrol.com, and ns18.domaincontrol.com.
GoDaddy is a massive hosting provider, and it has more than 100 such DNS servers to serve the needs of its clients. To hijack this domain, the attackers in the December 2018 spam campaign needed only to have created a free account at GoDaddy that was assigned the exact same DNS servers handed out to Virtualfirefox.com (ns17.domaincontrol.com and ns18.domaincontrol.com). After that, the attackers simply claim ownership over the domain, and tell GoDaddy to allow the sending of email with that domain from an Internet address they control.
Mozilla spokesperson Ellen Canale said Mozilla took ownership of virtualfirefox.com in September 2017 after a trademark dispute, but that the DNS nameserver for the record was not reset until January of 2019.
“This oversight created a state where the DNS pointed to a server controlled by a third party, leaving it vulnerable to misuse,” Canale said. “We’ve reviewed the configuration of both our registrar and nameservers and have found no indication of misuse. In addition to addressing the immediate problem, we have reviewed the entire catalog of properties we own to ensure they are properly configured.”
According to both Guilmette and Bryant, this type of hijack is possible because GoDaddy — like many other managed DNS providers — does little to check whether someone with an existing account (free or otherwise) who is claiming ownership over a given domain actually controls that domain name.
Contacted by KrebsOnSecurity, GoDaddy acknowledged the authentication weakness documented by Guilmette.
“After investigating the matter, our team confirmed that a threat actor(s) abused our DNS setup process,” the company said in an emailed statement.
“We’ve identified a fix and are taking corrective action immediately,” the statement continued. “While those responsible were able to create DNS entries on dormant domains, at no time did account ownership change nor was customer information exposed.” Continue reading →
 Some 20 of the flaws addressed in February’s update bundle are weaknesses labeled “critical,” meaning Microsoft believes that attackers or malware could exploit them to fully compromise systems through little or no help from users — save from convincing a user to visit a malicious or hacked Web site.
Some 20 of the flaws addressed in February’s update bundle are weaknesses labeled “critical,” meaning Microsoft believes that attackers or malware could exploit them to fully compromise systems through little or no help from users — save from convincing a user to visit a malicious or hacked Web site.