On Monday, KrebsOnSecurity notified MBIA Inc. — the nation’s largest bond insurer — that a misconfiguration in a company Web server had exposed countless customer account numbers, balances and other sensitive data. Much of the information had been indexed by search engines, including a page listing administrative credentials that attackers could use to access data that wasn’t already accessible via a simple Web search.
MBIA Inc., based in Purchase, N.Y., is a public holding company that offers municipal bond insurance and investment management products. According to the firm’s Wiki page, MBIA, formerly known as the Municipal Bond Insurance Association, was formed in 1973 to diversify the holdings of several insurance companies, including Aetna, Fireman’s Fund, Travelers, Cigna and Continental.
Notified about the breach, the company quickly disabled the vulnerable site — mbiaweb.com. This Web property contained customer data from Cutwater Asset Management, a fixed-income unit of MBIA that is slated to be acquired by BNY Mellon Corp.
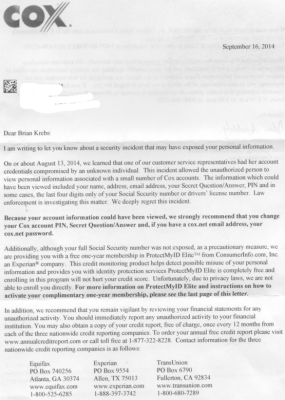
“We have been notified that certain information related to clients of MBIA’s asset management subsidiary, Cutwater Asset Management, may have been illegally accessed,” said MBIA spokesman Kevin Brown. “We are conducting a thorough investigation and will take all measures necessary to protect our customers’ data, secure our systems, and preserve evidence for law enforcement.”
Brown said MBIA notified all current customers about the incident Monday evening, and that it planned to notify former customers today.
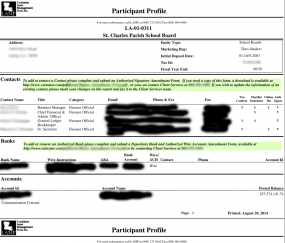
Some 230 pages of account statements from Cutwater had been indexed by Google, including account and routing numbers, balances, dividends and account holder names for the Texas CLASS (a local government investment pool) ; the Louisiana Asset Management Pool; the New Hampshire Public Deposit Investment Pool; Connecticut CLASS Plus; and the Town of Richmond, NH.
In some cases, the documents indexed by search engines featured detailed instructions on how to authorize new bank accounts for deposits, including the forms and fax numbers needed to submit the account information.
Bryan Seely, an independent security expert with Seely Security, discovered the exposed data using a search engine. Seely said the data was exposed thanks to a poorly configured Oracle Reports database server. Normally, Seely said, this type of database server is configured to serve information only to authorized users who are accessing the data from within a trusted, private network — and certainly not open to the Web.