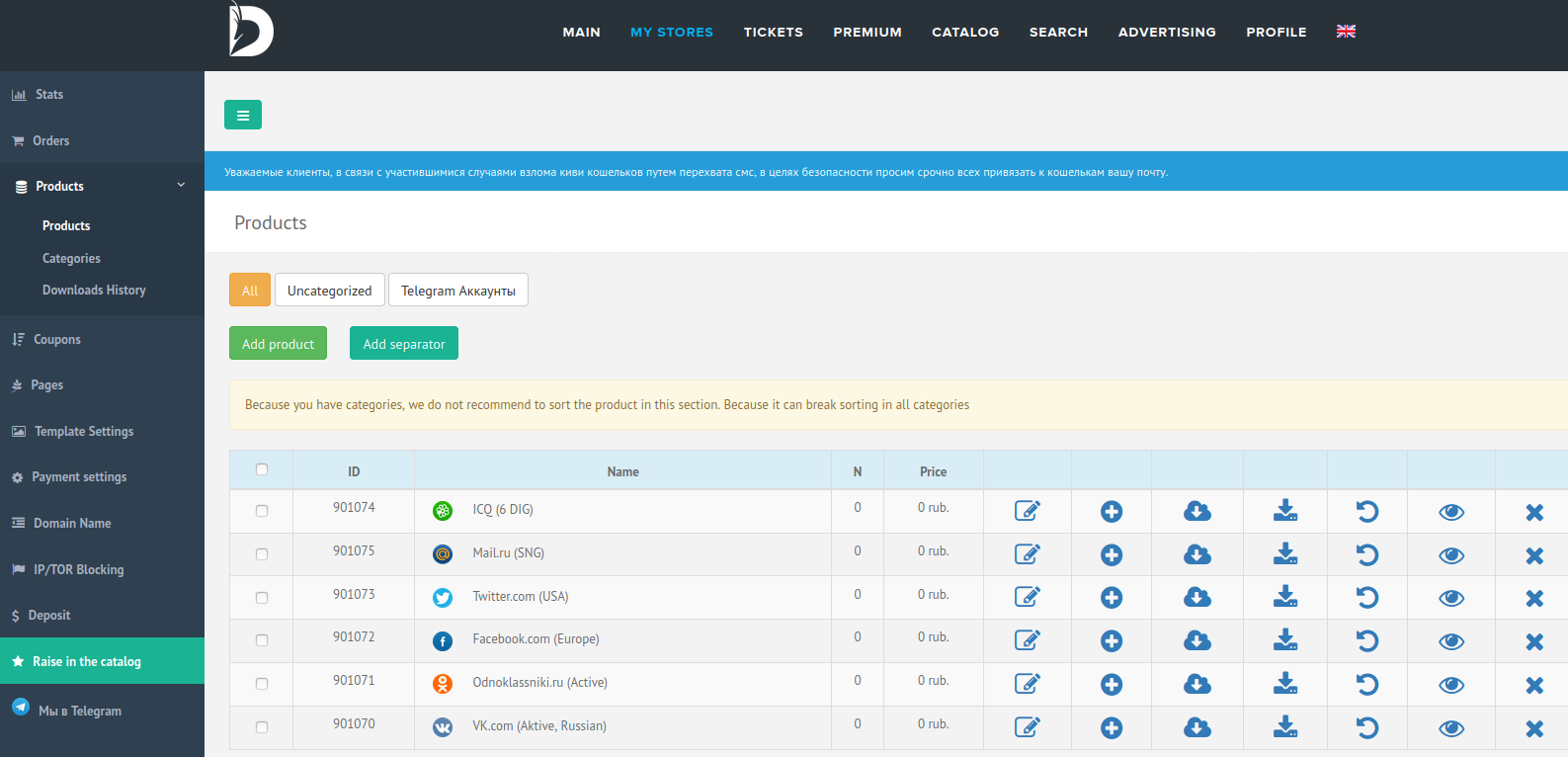
In December 2018, KrebsOnSecurity looked at how dozens of U.S. political campaigns, cities and towns had paid a shady company called Web Listings Inc. after receiving what looked like a bill for search engine optimization (SEO) services rendered on behalf of their domain names. The story concluded that this dubious service had been scamming people and companies for more than a decade, and promised a Part II to explore who was behind Web Listings. What follows are some clues that point to a very convincing answer to that question.
Since at least 2007, Web Listings Inc. has been sending snail mail letters to domain registrants around the world. The missives appear to be an $85 bill for an “annual search engine listing” service. The notice does disclose that it is in fact a solicitation and not a bill, but wording of the notice asserts the recipient has already received the services in question.
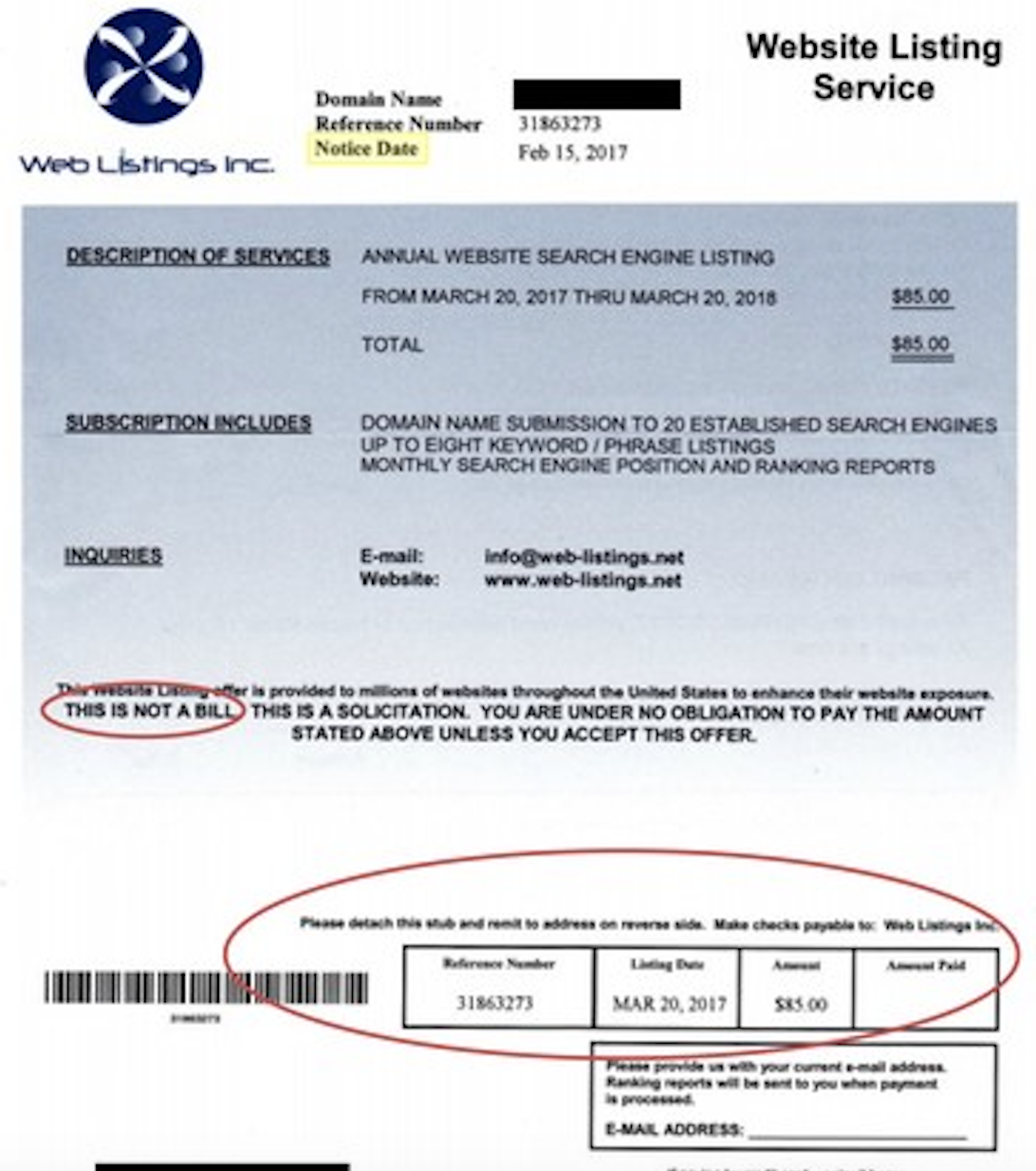
Image: Better Business Bureau.
The mailer references the domain name web-listings.net, one of several similarly-named domains registered sometime in 2007 or later to a “James Madison,” who lists his address variously as a university in New Britain, Connecticut or a UPS Store mailbox in Niagara Falls, New York.
Some others include: weblistingservices.com, webservicescorp.net, websiteservicescorp.com, web-listingsinc.com, weblistingsinc.net, and weblistingsreports.net. At some point, each of these domains changes the owner’s name from James Madison to “Mark Carter.” As we’ll see, Mark is a name that comes up quite a bit in this investigation.
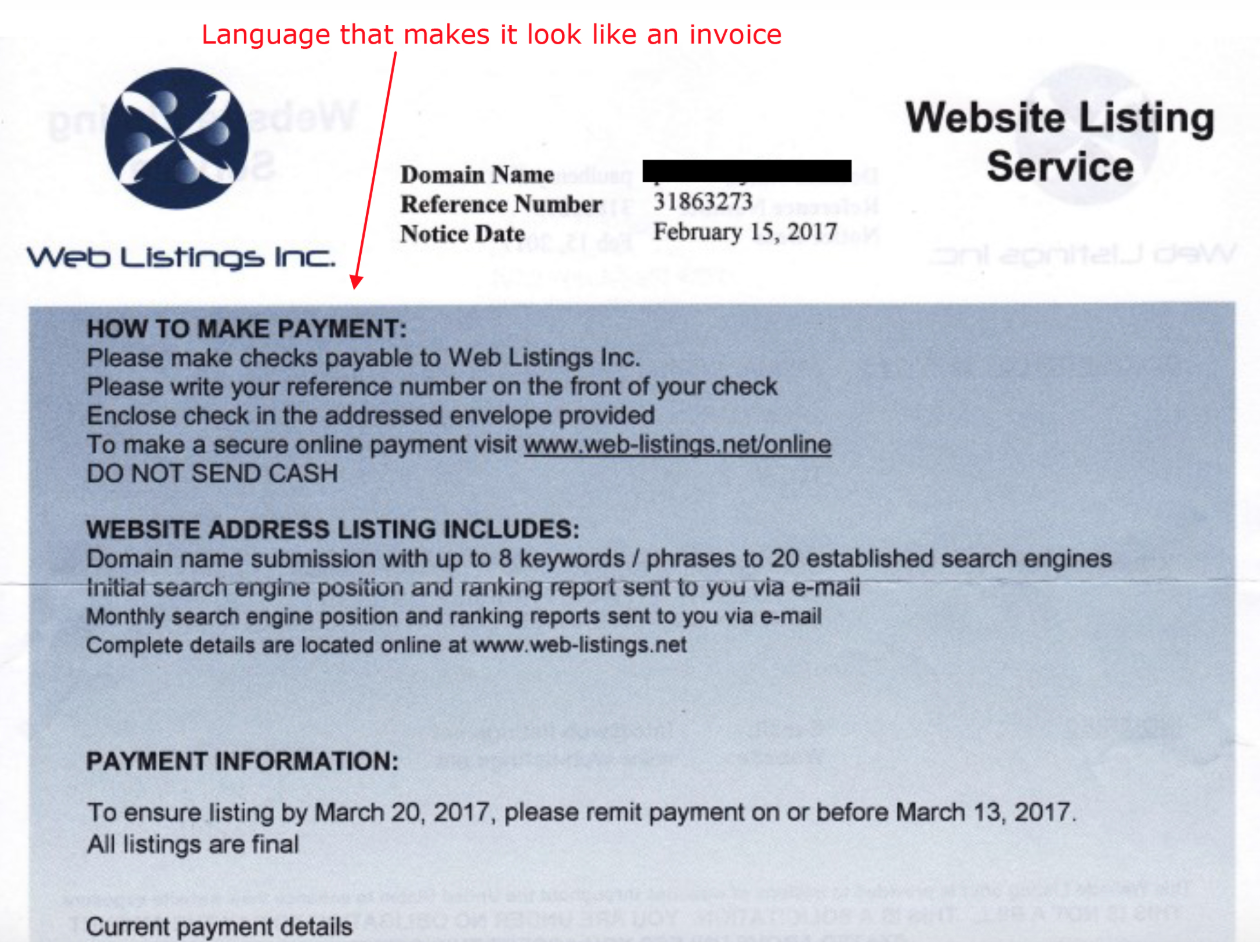
Image: Better Business Bureau.
A Twitter account for Web Listings Inc. has posts dating back to 2010, and points to even more Web Listings domains, including weblistingsinc.org. Cached versions of weblistingsinc.org at archive.org show logos similar to the one featured on the Web Listings mailer, and early versions of the site reference a number of “business partners” in India that also perform SEO services.
Searching the Internet for some of these Web listing domains mentioned in the company’s Twitter account brings up a series of press releases once issued on behalf of the company. One from May 2011 at onlineprnews.com sings the praises of Weblistingsinc.info, weblistingsinc.org and web-listings.net in the same release, and lists the point of contact simply as “Mark.”
Historic WHOIS registration records from Domaintools [an advertiser on this blog] say Weblistingsinc.org was registered in Nov. 2010 to a Mark Scott in Blairgowrie, Scotland, using the email address clientnews@reputationmanagementfor.com.
Reputationmanagementfor.com bills itself as an online service for “fighting negative and incorrect content on the internet,” which is especially interesting for reasons that should become clearer in a few paragraphs. The site says Mark Scott, 46, is an employee of Reputationmanagementfor.com, and that he is also involved with two other companies:
-GoBananas, a business that sets up group outings, with a focus on bachelor and bachelorette parties;
-HelpMeGo.to, an entity in Scotland that did online marketing and travel tourism both in Scotland (via sites like Scotland.org.uk and marketinghotelsonline.co.uk) and on India’s coastal Kerala state where HelpMeGo.to employed a number of people involved in the SEO business. Helpmego.to now simply redirects to GoBananas.
According to Farsight Security, a company that keeps historic records of which Web sites were hosted at which Internet addresses, Weblistingsinc.org was for a while hosted at the IP address 68.169.45.65 with just six other domains, including travelingalberta.com, which was a blog about traveling and living in Alberta, Canada registered to Mark Scott and the email address management@helpmego.to. Cached versions of this site from 2011 show it naming Web Listings Inc. as a business partner.
That same management@helpmego.to email address is tied to the WHOIS records for markscottblog.com, gobananas.co.uk, gobananas.com. Cached copies of markscottblog.com from 2010 at Archive.org show his profile page on blogger.com links to another blog with much the same content, images and links called internetmadness.blogspot.com.
Among the 2011 entries from the Internetmadness blog is a post promoting the wonders of benefits of Web Listings Inc.
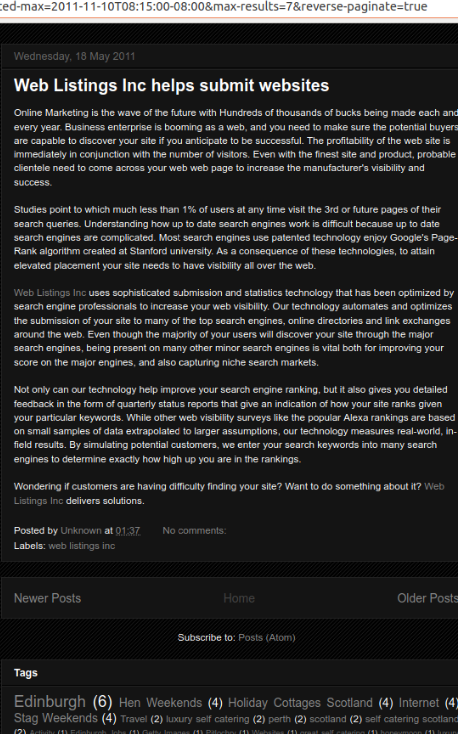
A cached copy of Mark Scott’s blog Internet Madness from 2011 promotes Web Listings Inc.



 London-based Finastra has offices in 42 countries and reported more than $2 billion in revenues last year. The company employs more than 10,000 people and has over 9,000 customers across 130 countries — including nearly all of the top 50 banks globally.
London-based Finastra has offices in 42 countries and reported more than $2 billion in revenues last year. The company employs more than 10,000 people and has over 9,000 customers across 130 countries — including nearly all of the top 50 banks globally.
 , this patch batch addresses at least 115 security flaws. Twenty-six of those earned Microsoft’s most-dire “critical” rating, meaning malware or miscreants could exploit them to gain complete, remote control over vulnerable computers without any help from users.
, this patch batch addresses at least 115 security flaws. Twenty-six of those earned Microsoft’s most-dire “critical” rating, meaning malware or miscreants could exploit them to gain complete, remote control over vulnerable computers without any help from users.