Security researchers who rely on data included in Web site domain name records to combat spammers and scammers will likely lose access to that information for at least six months starting at the end of May 2018, under a new proposal that seeks to bring the system in line with new European privacy laws. The result, some experts warn, will likely mean more spams and scams landing in your inbox.

On May 25, the General Data Protection Regulation (GDPR) takes effect. The law, enacted by the European Parliament, requires companies to get affirmative consent for any personal information they collect on people within the European Union. Organizations that violate the GDPR could face fines of up to four percent of global annual revenues.
In response, the Internet Corporation for Assigned Names and Numbers (ICANN) — the nonprofit entity that manages the global domain name system — has proposed redacting key bits of personal data from WHOIS, the system for querying databases that store the registered users of domain names and blocks of Internet address ranges (IP addresses).
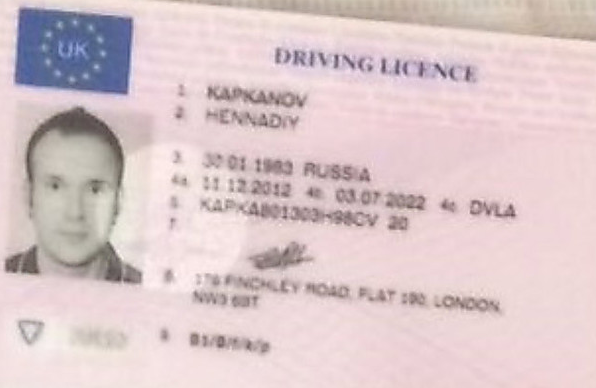
Under current ICANN rules, domain name registrars should collect and display a variety of data points when someone performs a WHOIS lookup on a given domain, such as the registrant’s name, address, email address and phone number. Most registrars offer a privacy protection service that shields this information from public WHOIS lookups; some registrars charge a nominal fee for this service, while others offer it for free.
But in a bid to help registrars comply with the GDPR, ICANN is moving forward on a plan to remove critical data elements from all public WHOIS records. Under the new system, registrars would collect all the same data points about their customers, yet limit how much of that information is made available via public WHOIS lookups.
The data to be redacted includes the name of the person who registered the domain, as well as their phone number, physical address and email address. The new rules would apply to all domain name registrars globally.
ICANN has proposed creating an “accreditation system” that would vet access to personal data in WHOIS records for several groups, including journalists, security researchers, and law enforcement officials, as well as intellectual property rights holders who routinely use WHOIS records to combat piracy and trademark abuse.
But at an ICANN meeting in San Juan, Puerto Rico on Thursday, ICANN representatives conceded that a proposal for how such a vetting system might work probably would not be ready until December 2018. Assuming ICANN meets that deadline, it could be many months after that before the hundreds of domain registrars around the world take steps to adopt the new measures.
Gregory Mounier, head of outreach at EUROPOL‘s European Cybercrime Center and member of ICANN’s Public Safety Working Group, said the new WHOIS plan could leave security researchers in the lurch — at least in the short run.
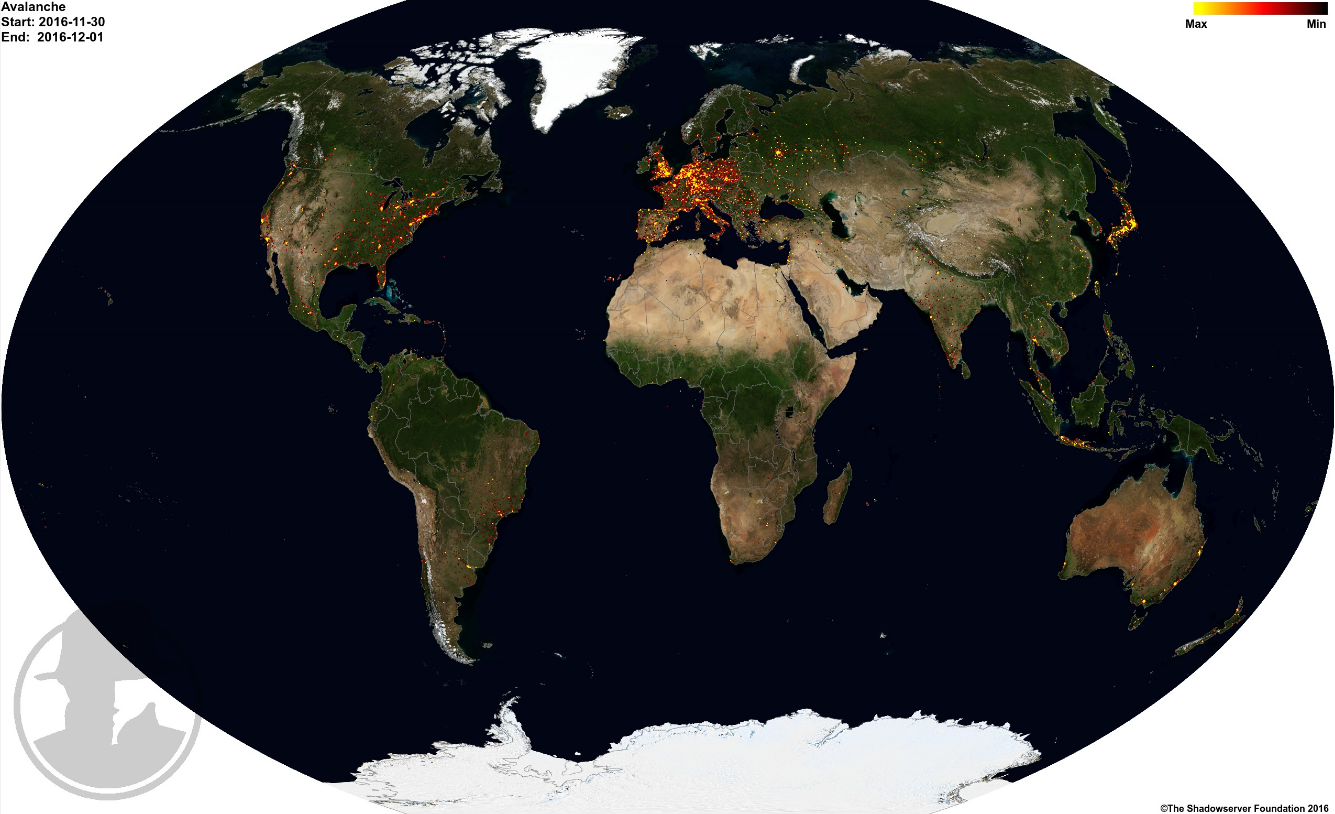
“If you don’t have an accreditation system by 25 May then there’s no means for cybersecurity folks to get access to this information,” Mounier told KrebsOnSecurity. “Let’s say you’re monitoring a botnet and have 10.000 domains connected to that and you want to find information about them in the WHOIS records, you won’t be able to do that anymore. It probably won’t be implemented before December 2018 or January 2019, and that may mean security gaps for many months.”
Rod Rasmussen, chair of ICANN’s Security and Stability Advisory Committee, said ICANN does not have a history of getting things done before or on set deadlines, meaning it may be well more than six months before researchers and others can get vetted to access personal information in WHOIS data.
Asked for his take on the chances that ICANN and the registrar community might still be designing the vetting system this time next year, Rasmussen said “100 percent.”
“A lot of people who are using this data won’t be able to get access to it, and it’s not going to be pretty,” Rasmussen said. “Once things start going dark it will have a cascading effect. Email deliverability is going to be one issue, and the amount of spam that shows up in peoples’ inboxes will be climbing rapidly because a lot of anti-spam technologies rely on WHOIS for their algorithms.”
As I noted in last month’s story on this topic, WHOIS is probably the single most useful tool we have right now for tracking down cybercrooks and/or for disrupting their operations. On any given day I probably perform 20-30 different WHOIS queries; on days I’ve set aside for deep-dive research, I may run hundreds of WHOIS searches. Continue reading




 The Microsoft updates affect all supported Windows operating systems, as well as all supported versions of Internet Explorer/Edge, Office, Sharepoint and Exchange Server.
The Microsoft updates affect all supported Windows operating systems, as well as all supported versions of Internet Explorer/Edge, Office, Sharepoint and Exchange Server.