The Dark Nexus Between Harm Groups and ‘The Com’
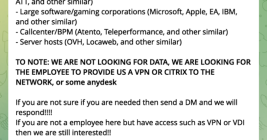
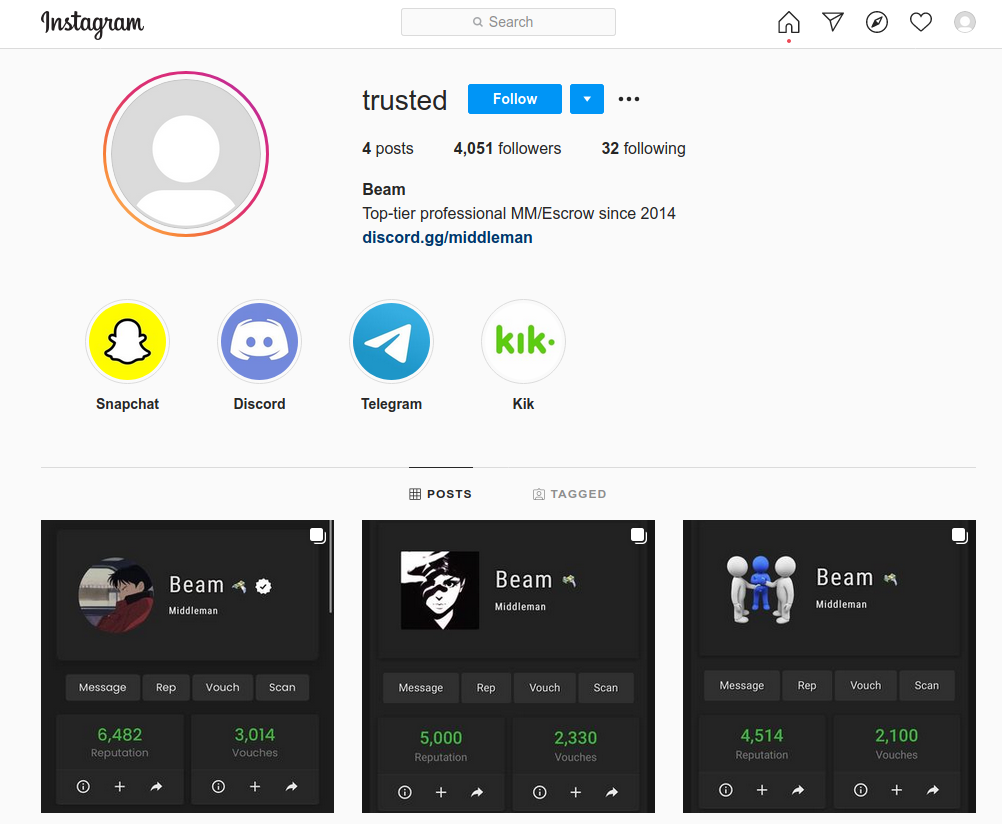
A cyberattack that shut down some of the top casinos in Las Vegas last year quickly became one of the most riveting security stories of 2023: It was the first known case of native English-speaking hackers in the United States and Britain teaming up with ransomware gangs based in Russia. But that made-for-Hollywood narrative has eclipsed a far more hideous trend: Many of these young, Western cybercriminals are also members of fast-growing online groups that exist solely to bully, stalk, harass and extort vulnerable teens into physically harming themselves and others.